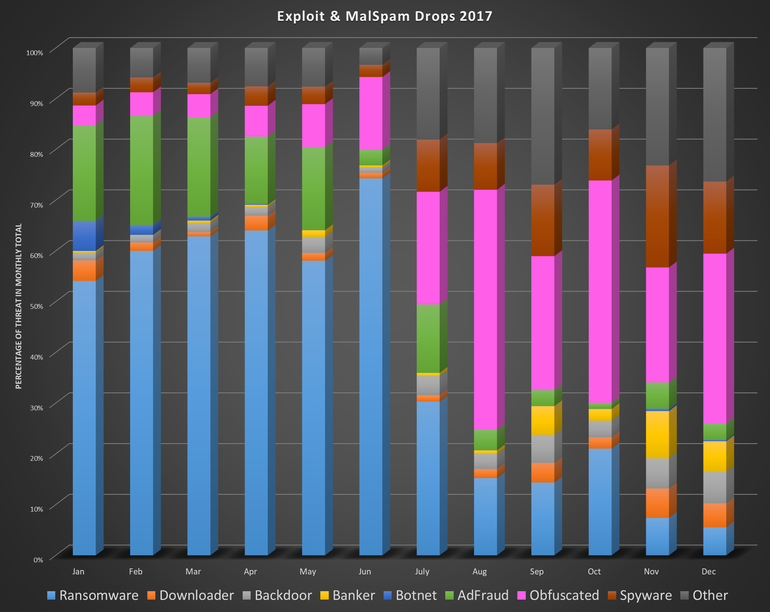
The last year has seen all manner of cybercrime, from scams and social engineering to malvertising and malspam. What’s interesting is that so many “next-gen,” sophisticated malware mainstays like exploits have dropped in popularity, while other more traditional types such as spyware have shot up dramatically —to the tune of an 882 percent increase in UK detections.
Meanwhile, here’s ransomware pretty much falling off a cliff, dropping as low as a 10 percent infection rate in December 2017:
Click to enlarge
Why is everyone jumping on the “I used spyware perfectly fine in 2007, and now I will again” bandwagon? Why is ransomware stagnating and tailing off? What omnipresent entity is dancing away behind the scenes, tying connections together and ensuring today’s attack news is yesterday’s old newspapers?
One of the answers, for me anyway, is Bitcoin.
(Digital) money makes the world go round
For many people in security circles (both victims and researchers), the first time coming across any mention of Bitcoin was through the payment demanded by ransomware authors. I have far too many memories of victims asking me what on Earth a Bitcoin was as they stared at the ransom screen blinking out from their computers. Bitcoin quickly became the payment method of choice over and above the formerly more common “send us an iTunes card code or wire us some money” demands.
From there, the professional criminal community fully embraced Bitcoin as the payment method of choice. They started utilizing TOR onion links to further anonymize the transaction, and layered on lots of other tactics that frankly required scammers to include FAQs in multiple languages just to ensure victims knew what they had to do next.
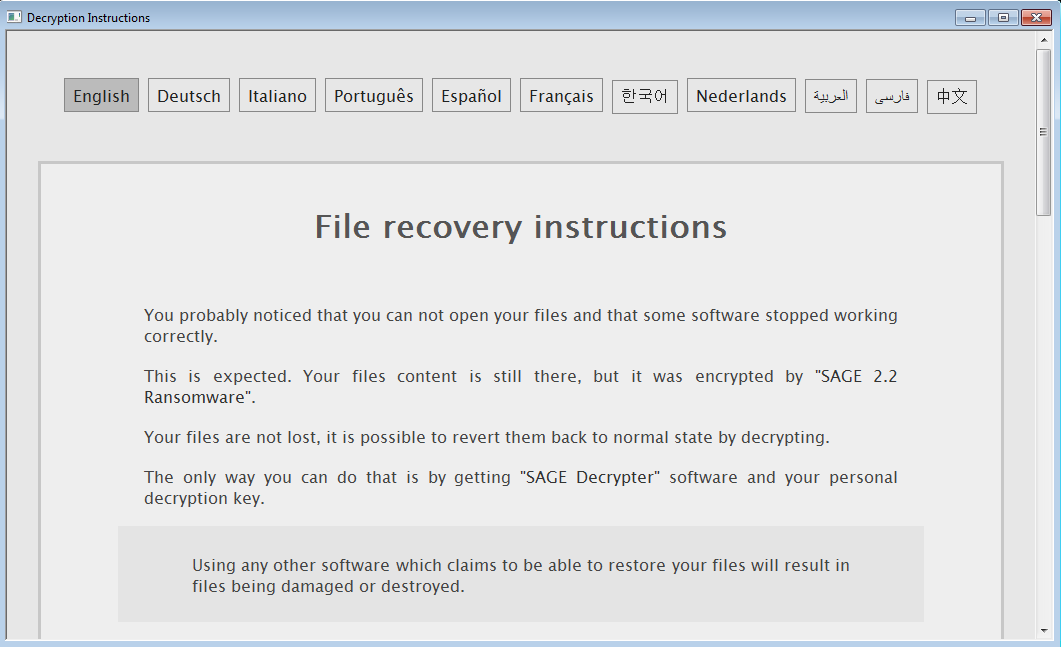
Click to enlarge
Once the script kiddies and amateur hour developers saw the big players raking in Bitcoin cash, they decided they wanted some of the same. We then had lots of pieces of poorly designed, DIY ransomware. You couldn’t always guarantee files would be decrypted after payment, and often it was impossible to tell if this was done intentionally or by accident. Even some of the big names didn’t always do what they were supposed to do.
The weird thing about ransomware is that it relies on dishonest developers being, well, honest. If people are coughing up lots of money to get their files back and it isn’t happening, word of mouth and a rapid press response will ensure the law of diminishing returns kicks in. People will either get smart and back up their files or simply resign themselves to losing them. A nice little earner suddenly becomes a big pile of nothing. Or, to put it another way:

For those wanting to ply their trade over a long time, this is, of course, not a good result.
The great ransomware fightback of 2017
Alongside bad developers and increased public visibility after some huge outbreaks 2017, advances in security tools have become better equipped to deal with ransomware threats. In addition, lots of standalone programs have been made by independent researchers to decrypt files. This increased awareness of ransomware prevention (backing up files, using security tools) alongside decreasing prices for file storage has really helped to defang the ransomware menace to some degree. It’s no longer the killer app it once was for scammers, and with a few precautions in place, it loses much of its power.
And then, at last, we come to the Bitcoins themselves. You don’t need me to tell you the price is simultaneously through the roof and in the toilet, on the kind of crazy rollercoaster ride you just can’t predict. Back in the days when they weren’t quite so highly valued, ransomware authors could afford to get away with asking for the odd coin or two. Now? Frankly, they’re taking a huge leap of faith that someone can summon up the cryptocash to get their files back.
There are many pieces of ransomware out there that can be controlled by Command & Control servers; new files can be downloaded as required, and, if needed, criminals can tweak values to more manageable figures. Trouble is, there’s no guarantee our malware-developing friend is sitting there monitoring the rise and fall and rise and rise and fall of Bitcoin. It’s also entirely possible they don’t really care if the coin value on display is a bit too much to pay, because another victim will be along in a minute.
As for the DIY/home-brew contingent? Everything may well be hardcoded into the file, with no way to alter it once it lurches into the wild. At that point, if they’re asking for four Bitcoins and the price triples overnight, there’s a good chance they won’t be getting any money out of it.
There are many other factors at play of course, but “we’re slowly strangling ourselves out of the market by asking for ridiculous amounts of money” is certainly a rather large warning sign.
Swings, roundabouts, and the path of least resistance
There is a cyclical nature to attacks. They tend to swing from stealth being the “in” thing, to overt displays of fireworks on your desktop, to covert action becoming the new (old) hotness, and so on. Back in the day, old-school adware vendors had their programs bundled alongside other spyware, and the desktop would be ablaze with pop-ups, pop-unders, sliders, extensions—you name it. The idea was to generate as many ad impressions as possible before the affiliate networks were shut down. A quick apology, “It’ll never happen again,” and sure enough, they’d be right back at it a few days later.
Once security tools and public awareness had reached a tipping point and big legal things started to happen, many vendors went broke or moved onto pastures new. Those that remained knew they had to go dark, and from about 2008 onward you started to see a lot less fireworks and a lot more invisible assassins. (Well, not see them, exactly, given they were invisible, but anyway.)
Stealthy malware and silent botnets clinging onto a PC as covertly as possible for as long as they could was the order of the day. Eventually, these methods, too, fell out of favour, and cybercriminals started to ramp up more visible scams in the form of the evergreen fake antivirus/tech support scams, and social engineering on social media portals.
We’re seeing a similar pattern now with ransomware. Ransomware catches plenty of victims out the gate, but not so much once everyone has wised up a little. If ransomware groups can’t even get their hands on Bitcoins by wandering into a victim’s home at 2am and loudly announcing the takeover of their PC, it’s surely a lot easier to jump on the cryptomining craze and return to the digital shadows.
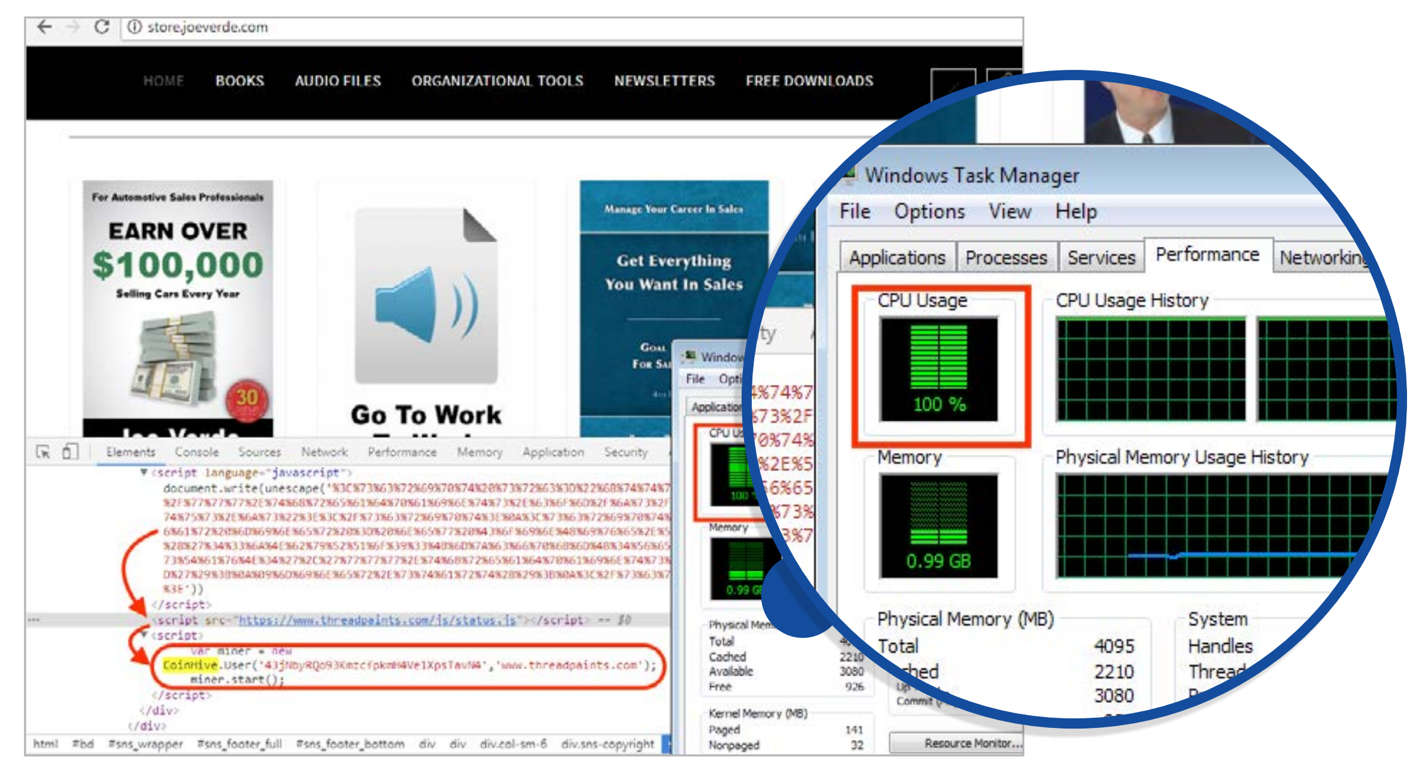
Click to enlarge
The advantages to moving into stealth mode are obvious. First, there are no more splashy takeovers. Splashy takeovers don’t last long on PCs these days. Second, the movement to covertly mine for coins using the victim’s GPU horsepower—without them knowing about it—has potential for longer-term gains. That’s the theory, at least; in reality, many people will notice fans spinning up, or computers under higher load or just plain old not responding. Even so, a lot of those people may just pass it off as “one of those things my computer does.” It’s a trade off, and not likely to make more money than kicking the door in and screaming for free coins, but it’s definitely a lot sneakier.
Finally, it’s a lot less hassle to just throw some script on a website, as opposed build the ransomware, pay some developers, mess around with onion sites, write up long FAQs for the victims, maintain C&C servers, ensure the decryption of hijacked files actually works, and so on. And cybercriminals delivering any kind of attack have noticed.
As we said in our blog on the 2017 State of Malware report:
Alongside a sudden cryptocurrency craze, bad actors have started utilizing cryptomining tools for their own profit, using victim system resources in the process. This includes compromised websites serving drive-by mining code, a significant increase of miners through malicious spam and exploit kit drops, and adware bundlers pushing miners instead of toolbars. By the end of 2017, basically anyone doing any kind of cybercrime was also likely dabbling in cryptomining.
It isn’t just scripts mining for coins in the background of low traffic, unknown websites, either. In the last few days, we’ve also seen signs of Google’s DoubleClick ads on Youtube serving as the launchpad for Coinhive mining scripts. If you’re hunting around for websites for your kids, you may well run into mining scripts there, too. This kind of furtive mining is a bit of a fast moving plague, and throws the old arguments over blocking ads while hurting publishers to the foreground once more.
And while we’re talking about paths of least resistance, there are many other types of scams taking aim at digital coins; the sky is the limit, and bad actors don’t seem worried about locking themselves into the same old tried and tested methods.
Everywhere you look, digital currency is causing headaches across the board. Malware miners. Fake wallets in official mobile stores. Covert scripts quietly gobbling up power cycles in the background. Gamers unable to buy graphics cards due to miners hogging stock, resulting in shops selling them at a discount with gaming components. Even fake fonts are in on the act.

Click to enlarge
Ransomware: not dead yet
Ransomware may be losing its cool factor, but it’s definitely not dead and buried—not by a long shot. Many ransomware authors appear to be in bit of a self-imposed time out. Except these guys aren’t feeling guilty. It’s more like “let’s see what horrible new thing we can come up with next.”
There are already a few signs of desperate, scorched-earth ransomware attack methods, with the so-called “SpriteCoin” hurling malware at victims once they’ve paid to recover their files. Elsewhere, we have ransomware effectively trying to cannibalize each other’s payments. This infighting certainly isn’t a good thing for the victims, especially when their payments are ending up with the wrong malware groups—nobody is getting their files back in that scenario. Stack that alongside the “bad” ransomware not decrypting files, and you have yet another reason why people will, eventually, choose not to pay.
The future may or may not be Bitcoin, but for now, it almost certainly isn’t ransomware. Give it time while the battle to establish exactly what ransomware is about plays out behind the scenes, though. Eventually, the pendulum always swings back.