If you’re thinking about checking out the website owned by the restaurant that asked White House press secretary Sarah Huckabee Sanders to leave the premises, you might want to hold off. There’s some site compromise action afoot.
Although the homepage appears to be acting in a perfectly normal manner, turning off scripts so you can see what’s happening under the hood provides a rather stark visual discrepancy.
Visiting as normal:
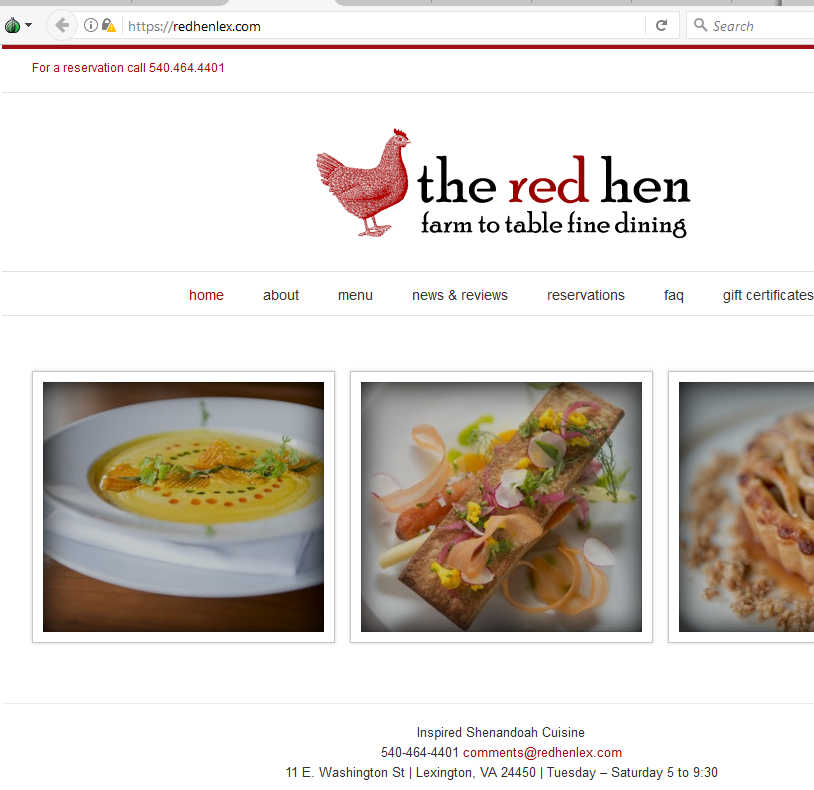
Click to enlarge
Visiting with scripts turned off:
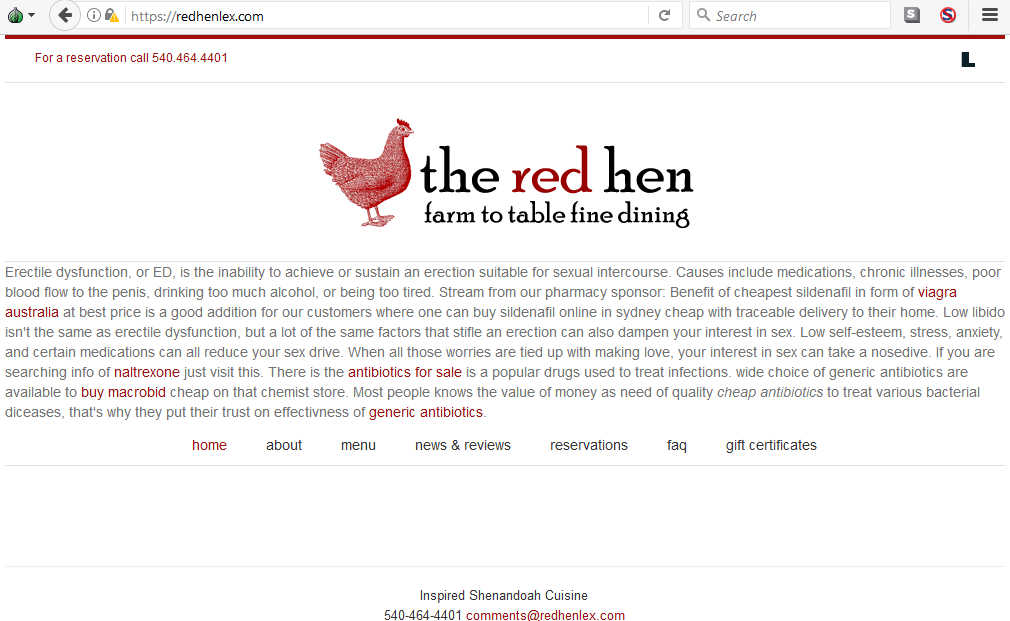
Click to enlarge
Why yes, that’s a collection of Viagra spam text injected into the website with the aim of giving a search engine boost to the sites linked. What you’re seeing here is the otherwise “hidden” code leaking through onto the page; it actually resides in the HTML source like so:
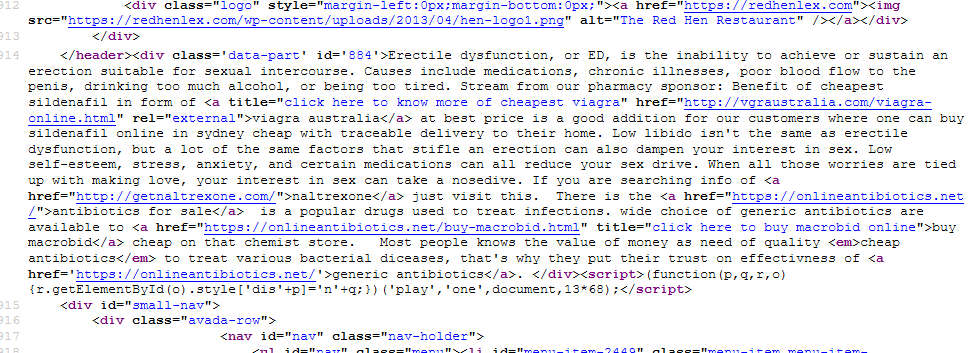
Click to enlarge
The sites hoping to get a search engine boost from the compromised restaurant page are pushing pharmaceuticals. Here’s the first example, a shopping portal for Generic Viagra:
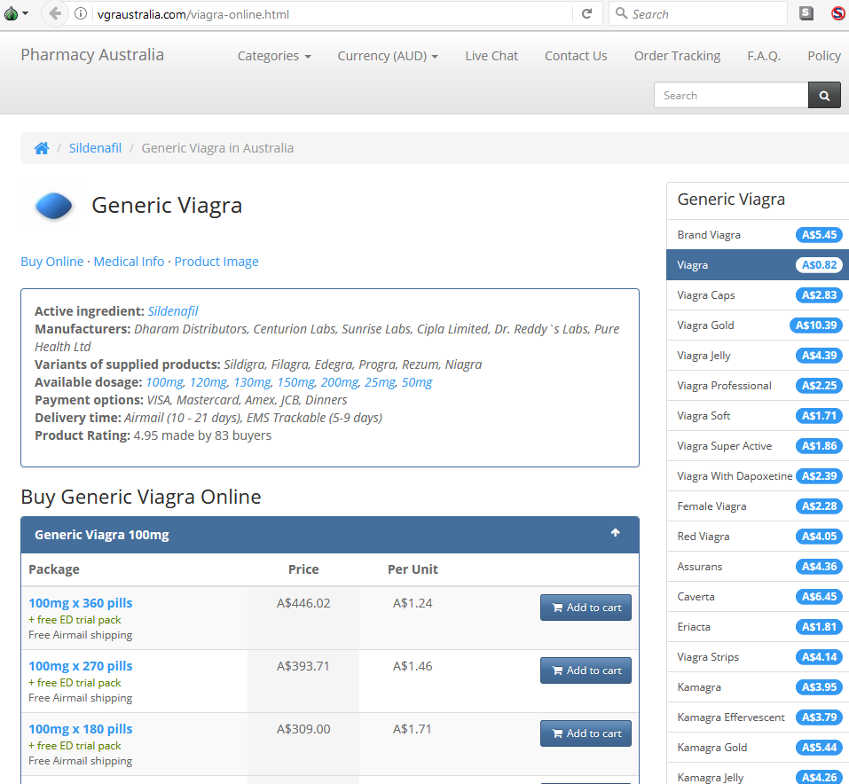
Click to enlarge
The second is for a prescription drug I’m not even going to attempt to pronounce:
Click to enlarge
Old hat
This is an absolutely ancient black hat tactic, most typically referred to as a form of SEO (Search Engine Optimisation) spam, or “Spamdexing.” Threat actors either use dirty SEO tactics to drive high traffic to their pages or they capitalize on already highly-trafficked targets by hiding their links in subtext. The most common forms down the years have tended to be one of the following:
- Keyword stuffing, where lots of content-specific words are jammed into the text of an article to artificially drive traffic in ways that would otherwise make little sense.
- Scraper sites, which pillage content from other places and occasionally remove things like the author or company name, hoping to make some ad-based revenue from the multitude of flashing banners hosted on their own website.
- Hidden text, where a website is filled with content the same colour as the background and placed across multiple pages in an effort to boost links/ranking for the linked sites in question. This can be content added deliberately by the webmaster, but it can also come about as a result of a hacked website.
A fourth variant of SEO poisoning would be where a hacker added malicious files to a site and drew visitors there through bogus search results, but services such as Google have been cracking down on this for years.
The fallout
While compromises of this kind may give a slight, fleeting edge to the scammers pushing their wares, it can do significant damage to the webmaster’s online business. Everything from page rank to general trustworthiness all take a nose dive in the eyes of Google, and it can be hard to get things back on track.
In this case, the Red Hen site is running on WordPress, so it’s possible an exploit targeting the popular platform or one of its plugins was used. It could even be down to something as basic as gaining access using default admin credentials, or a webmaster being caught up in a phishing scam. We couldn’t say for sure, though attacks on content management systems have been ramping up over the last quarter. Regardless of the break-in method, the site owners definitely have some cleaning up to do.
If you’d like to delve deeper into the art of SEO, we have a couple of links you can browse.
SEO poisoning: is it worth it?
Google’s featured snippets abused by SEO scammers
Otherwise, pay attention to search results when hunting around online. If you’re expecting to see a result for an eatery located in Lexington but instead find a webpage related to cars and written in Japanese—someone is likely giving Google the slip by abusing its algorithms in order to boost phony results.

Click to enlarge
And if you do find your favorite restaurant is serving up Viagra instead of farm-to-table, you might want to do things the old fashioned way: Grab a leaflet and order takeout.










