Here’s a scary thought: Mobile devices may soon come with pre-installed malware on required system apps. While it might sound like a grim foretelling, pre-installed mobile malware is an unfortunate reality of the future.
In the past, we’ve seen pre-installed malware with the notorious Adups threat, among others. “Pre-installed” means the malware comes already installed on a device at the system level, thus, it cannot be removed; only disabled. However, remediating these iterations of pre-installed malware is possible by using a work-around to uninstall apps for the current user. This method involves connecting the mobile device to a PC and using the ADB command line tool. Follow our guide, removal instructions for Adups, to find out more.
Although this method is a bit tedious, it works to remediate the malware. In contrast, remediating newer versions of pre-installed malware has become much more difficult. We are now seeing malware authors target system apps that are required for the device to function properly. By injecting malicious code within these necessary apps, threat actors have reshaped the landscape of pre-installed malware for the worse.
Types of pre-installed apps
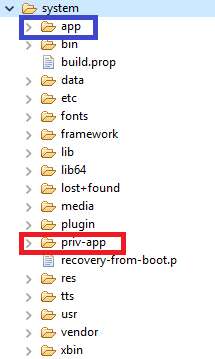
There are two types of preinstalled apps, based on the apps’ location on the device. This location also determines the importance of the app.
The first location is /system/app/. Apps in this location are typically something you want to have, but not critical for the device to run. For example, apps that contain functionally for the camera, Bluetooth, FM radio on the device, or photo viewing are stored in this location. This location is also where device manufactures cache what some may consider bloatware. Uninstalling some of these apps may degrade the user experience, but it isn’t going to stop the device from functioning.
The other location is /system/priv-app/. This is where significantly important apps reside. For instance, apps like settings and system UI, which include the functionality for the back/home buttons on Android devices, are stored here. In other words, apps you absolutely cannot uninstall these without essentially breaking the phone. Sadly, the latest pre-installed malware is targeting this location.
The evidence
In the light of this new, frightening pre-installed malware, let’s look at two case studies.Case study 1: Riskware auto installer within System UI
The device is a THL T9 Pro. The infection is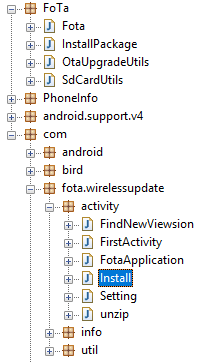
Case Study 2: Monitor within settings
This time, the device is a UTOK Q55. The infection is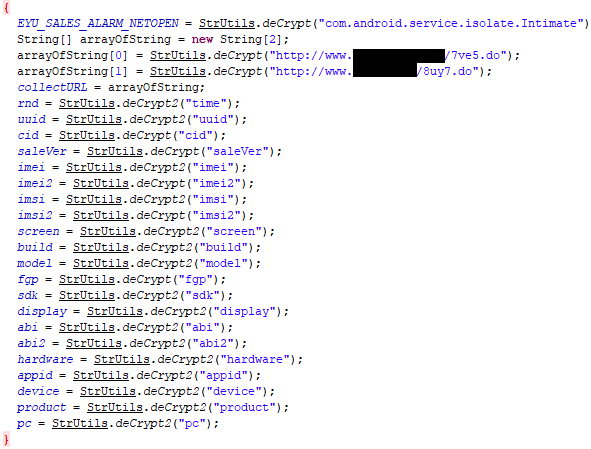
Attempting to remediate
Here lays the biggest problem with these infections—there is currently no good way to remediate. I have worked with several customers with these infections, but despite my attempts, I have yet to find a good work around. However, I can offer some guidance. If a clean version of the system app can be found to replace the malicious version, you might be able to replace it. You will want to look for system apps that match the current Android OS version of the device. If found, you can try using the following method:- You can use the popular site VirusTotal to determine if it’s clean or not.
- adb push
/sdcard/Download/
- adb shell pm uninstall -k –user 0
- adb shell pm install -r –user 0 /sdcard/Download/
- Common failure errors:
- [INSTALL_FAILED_VERSION_DOWNGRADE]
- [INSTALL_FAILED_UPDATE_INCOMPATIBLE]
- [INSTALL_FAILED_OLDER_SDK]
- If the new version fails to install, you can revert to the old system app.
- adb shell pm install -r –user 0
- adb shell pm install -r –user 0
As noted above, I have yet to find a version of any of the infections encountered that successfully installs. If you need assistance, feel free to post on our forum Mobile Malware Removal Help & Support.
What really can be done?
Currently, the best method to deal with these infections is to:
- Stay away from devices with these infections. Here are the manufacturers/models we have seen so far that have been impacted:
- THL T9 Pro
- UTOK Q55
- BLU Studio G2 HD
- If you already bought one, return the device.
- If you already bought the device and can’t return it, contact the manufacturer.
Extreme frustration
As a mobile malware researcher, it pains me to no end to write about malware we can’t currently remediate. However, the public needs to know that these types of infections exist in the wild. No one should have to tolerate such infections on any mobile device regardless of its price point and/or notoriety. I will continue to look for methods to deal with these infections. In the meantime, stay safe out there.
APK samples
Detection: Android/PUP.Riskware.Autoins.Fota.INS MD5: 9E0BBF6D26B843FB8FE95FDAD582BB70 Package Name: com.android.systemui”>
Detection: Android/Monitor.Pipe.Settings MD5: DC267F396FA6F06FC7F70CFE845B39D7 Package Name: com.android.settings










