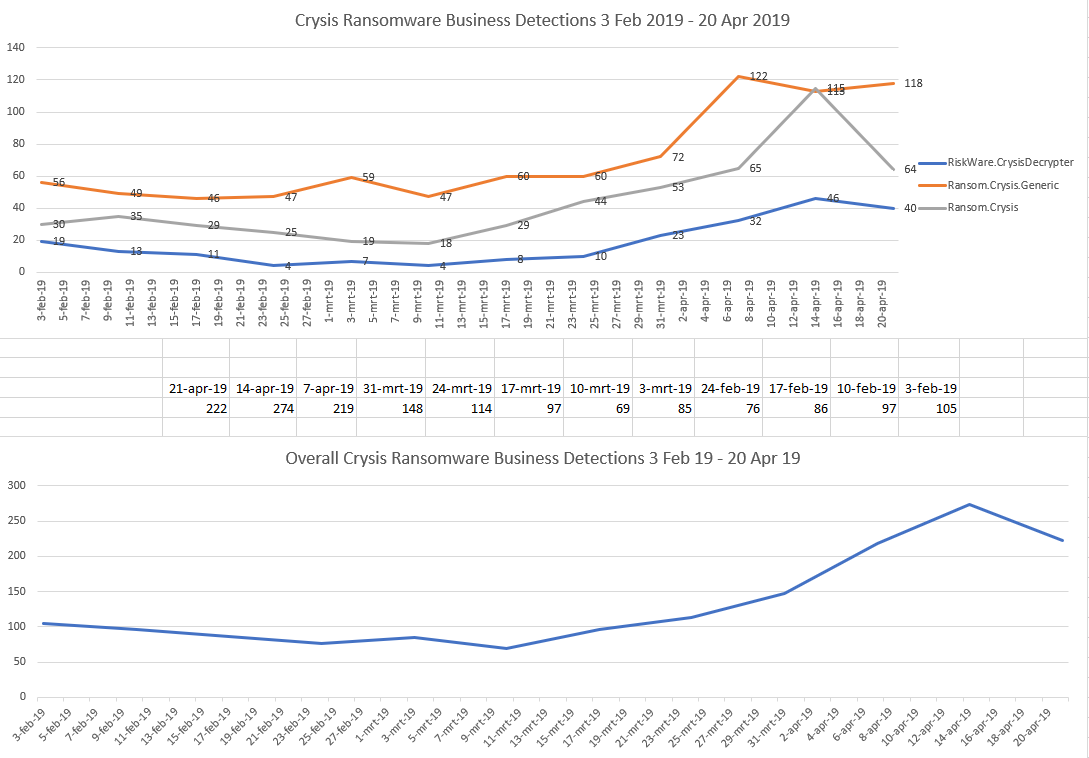
CrySIS, aka Dharma, is a family of ransomware that has been evolving since 2016. We have noticed that this ransomware has become increasingly active lately, increasing by a margin of 148 percent from February until April 2019. The uptick in detections may be due to CrySIS’ effective use of multiple attack vectors.
Profile of the CrySIS ransomware
CrySIS/Dharma, which Malwarebytes detects as Ransom.Crysis, targets Windows systems, and this family primarily targets businesses. It uses several methods of distribution:
- CrySIS is distributed as malicious attachments in spam emails. Specific to this family is the use of malicious attachments that use double file extensions, which under default Windows settings may appear to be non-executable, when in reality they are.
- CrySIS can also arrive disguised as installation files for legitimate software, including AV vendors. CrySIS operators will offer up these harmless looking installers for various legitimate applications as downloadable executables, which they have been distributing through various online locations and shared networks.
- Most of the time, CrySIS/Dharma is delivered manually in targeted attacks by exploiting leaked or weak RDP credentials. This means a human attacker is accessing the victim machines prior to the infection by brute-forcing the Windows RDP protocol on port 3389.
In a recent attack, CrySIS was delivered as a download link in a spam email. The link pointed to a password-protected, self-extracting bundle installer. The password was given to the potential victims in the email and, besides the CrySIS/Dharma executable, the installer contained an outdated removal tool issued by a well-known security vendor.
This social engineering strategy worked to bring down user defenses. Seeing a familiar security solution in the installation package tricked users into believing the downloadable was safe, and the attack was successful.
The infection
Once CrySIS has infected a system, it creates registry entries to maintain persistence and encrypts practically every file type, while skipping system and malware files. It performs the encryption routine using a strong encryption algorithm (AES-256 combined with RSA-1024 asymmetric encryption), which is applied to fixed, removable, and network drives.
Before the encryption routine, CrySIS deletes all the Windows Restore Points by running the vssadmin delete shadows /all /quiet command.
The Trojan that drops the ransomware collects the computer’s name and a number of encrypted files by certain formats, sending them to a remote C2 server controlled by the threat actor. On some Windows versions, it also attempts to run itself with administrator privileges, thus extending the list of files that can be encrypted.
After a successful RDP-based attack, it has been observed that before executing the ransomware payload, CrySIS uninstalls security software installed on the system.
The ransom
When CrySIS has completed the encryption routine, it drops a ransom note on the desktop for the victim, providing two email addresses the victim can use to contact the attackers and pay the ransom. Some variants include one of the contact email addresses in the encrypted file names.
The ransom demand is usually around 1 Bitcoin, but there have been cases where pricing seems to have been adapted to match the revenue of the affected company. Financially sound companies often have to pay a larger ransomware sum.

Some of the older variants of CrySIS can be decrypted using free tools that have been made available through the NoMoreRansom project.
Countermeasures
While you do have a choice to deploy other software to remotely operate your work computers, RDP is essentially a safe and easy-to-use protocol with a client that comes pre-installed on Windows systems, as well as clients available for other operating systems. There are a few measures you can take to make it a lot harder to gain access to your network over unauthorized RDP connections:
- To make it harder for a brute force attack to succeed, it helps to use strong passwords.
- Do not disable Network Level Authentication (NLA) as it offers an extra authentication level. Enable it if it wasn’t already.

- Change the RDP port so port-scanners looking for open RDP ports will miss yours. By default, the server listens on port 3389 for both TCP and UDP.
- Or use a Remote Desktop Gateway Server, which also gives you some additional security and operational benefits like 2FA. The logs of the RDP sessions can prove especially useful when you are trying to figure out what might have happened. As these logs are not on the compromised machine, they are harder to falsify by intruders.
- Limit access to specific IPs, if possible. There should be no need for a whole lot of IPs that need RDP access.
- There are several possibilities to elevate user privileges on Windows computers, even when using RDP, but all of the known methods have been patched. So, as always, make sure your systems are fully up-to-date and patched to prevent privilege elevation and other exploits from being used.
- Use an effective and easy-to-deploy backup strategy. Relying on Restore Points doesn’t qualify as such and is utterly useless when the ransomware first deletes the restore points, as is the case with CrySIS.
- Train your staff on the dangers of email attachments and downloading files from unofficial sources.
- Finally, use a multi-layered, advanced security solution to protect your machines against ransomware attacks.
IOCs
Ransom.Crysis has been known to append these extensions for encrypted files:
.crysis, .dharma, wallet, .java, .adobe, .viper1, .write, .bip, .zzzzz, .viper2, .arrow, .gif, .xtbl, .onion, .bip, .cezar, .combo, .cesar, .cmb, .AUF, .arena, .brrr, .btc, .cobra, .gamma, .heets, .java, .monro, .USA, .bkp, .xwx, .btc, .best, .bgtx, .boost, .heets, .waifu, .qwe, .gamma, .ETH, .bet, ta, .air, .vanss, . 888, .FUNNY, .amber, .gdb, .frend, .like, .KARLS, .xxxxx, .aqva, .lock, .korea, .plomb, .tron, .NWA, .AUDIT, .com, .cccmn, .azero, .Bear, .bk666, .fire, .stun, .myjob, .ms13, .war, .carcn, .risk, .btix, .bkpx, .he, .ets, .santa, .gate, .bizer, .LOVE, .LDPR, .MERS, .bat, .qbix, .aa1, and .wal
The following ransom note names have been found:
- README.txt
- HOW TO DECRYPT YOUR DATA.txt
- Readme to restore your files.txt
- Decryption instructions.txt
- FILES ENCRYPTED.txt
- Files encrypted!!.txt
- Info.hta
Common file hashes:
- 0aaad9fd6d9de6a189e89709e052f06b
- bd3e58a09341d6f40bf9178940ef6603
- 38dd369ddf045d1b9e1bfbb15a463d4c











