Traffic monetization and ad fraud
While we encountered some desktop traffic, we believe the primary goal of the fake jquery campaign is to monetize from mobile users. This would explain the level of filtering involved to hide non-qualified traffic.
We weren’t able to get an idea of the scale at play, especially considering that the domain initiating the redirects really only became active in late May. However, given the number of websites that have been compromised, this campaign is quite likely funneling a significant amount of traffic leading to ad fraud.
Malwarebytes users are protected against this campaign both on desktop and mobile.
Indicators of Compromise
Fake jquery domains:
12js[.]org
16js[.]org
22js[.]org
lib0[.]org
16lib[.]org
12lib[.]org
wp11[.]org
Redirects:
financeleader[.]co
afflink[.]org
Malicious APKs:
0e67fd9fc535e0f9cf955444d81b0e84882aa73a317d7c8b79af48d91b79ef19 a210c9960edc5362b23e0a73b92b4ce4597911b00e91e7d3ca82632485c5e68d
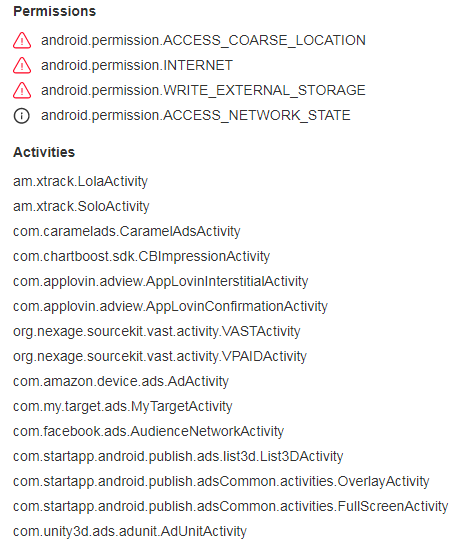
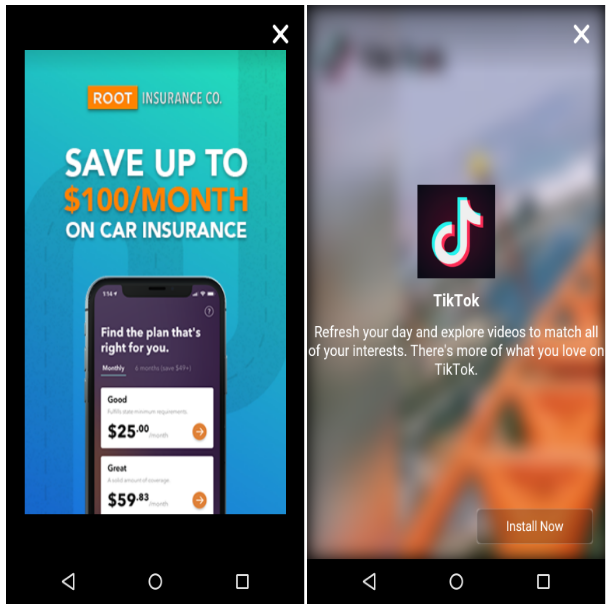
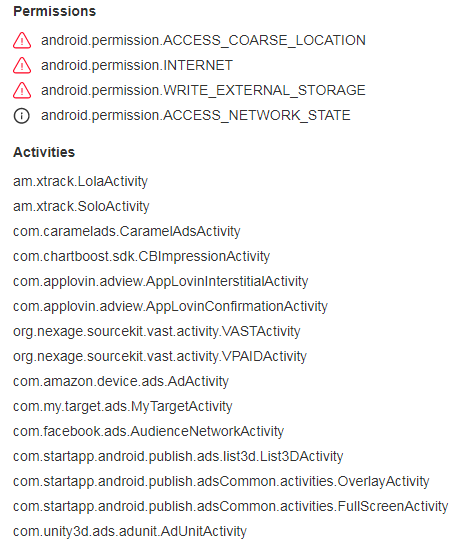
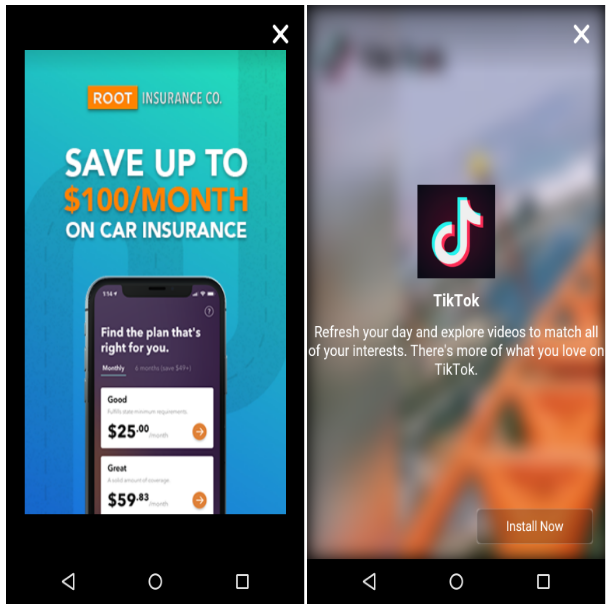
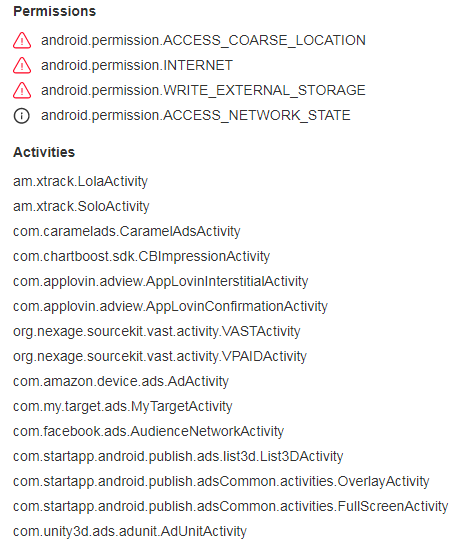
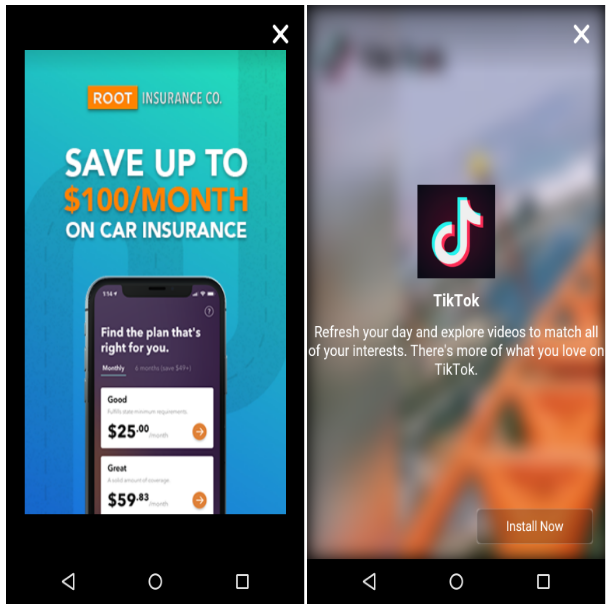
This app is malicious (detected as Android/Trojan.HiddenAds.xt by Malwarebytes) and will generate full screen ads at regular intervals.
Traffic monetization and ad fraud
While we encountered some desktop traffic, we believe the primary goal of the fake jquery campaign is to monetize from mobile users. This would explain the level of filtering involved to hide non-qualified traffic.
We weren’t able to get an idea of the scale at play, especially considering that the domain initiating the redirects really only became active in late May. However, given the number of websites that have been compromised, this campaign is quite likely funneling a significant amount of traffic leading to ad fraud.
Malwarebytes users are protected against this campaign both on desktop and mobile.
Indicators of Compromise
Fake jquery domains:
12js[.]org
16js[.]org
22js[.]org
lib0[.]org
16lib[.]org
12lib[.]org
wp11[.]org
Redirects:
financeleader[.]co
afflink[.]org
Malicious APKs:
0e67fd9fc535e0f9cf955444d81b0e84882aa73a317d7c8b79af48d91b79ef19 a210c9960edc5362b23e0a73b92b4ce4597911b00e91e7d3ca82632485c5e68d
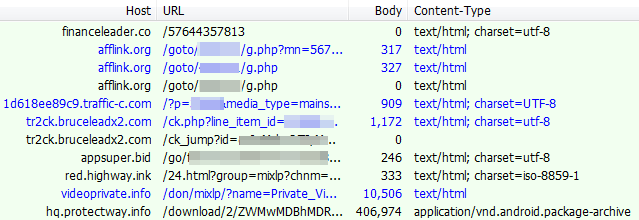
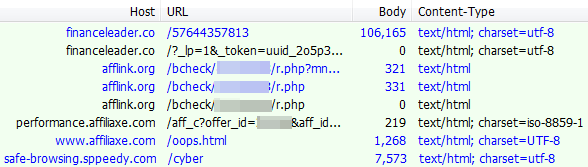
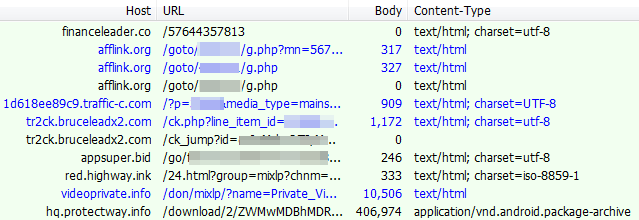
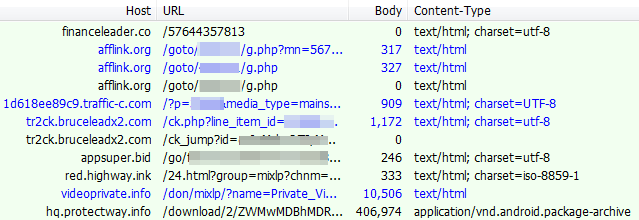
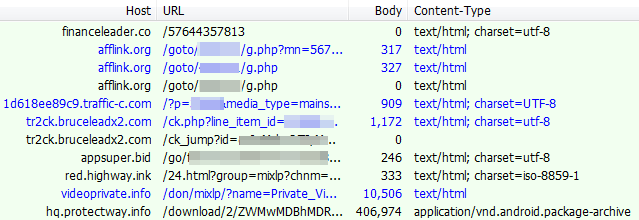
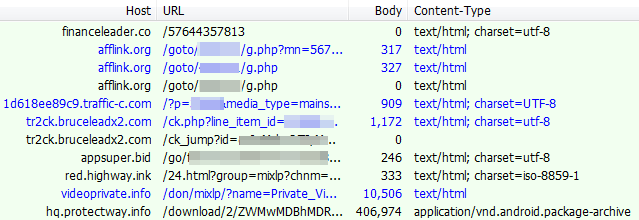
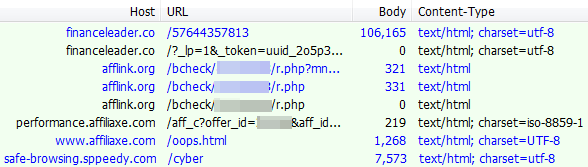
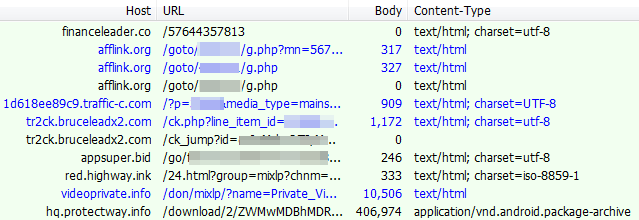
Associated web traffic:
This app is malicious (detected as Android/Trojan.HiddenAds.xt by Malwarebytes) and will generate full screen ads at regular intervals.
Traffic monetization and ad fraud
While we encountered some desktop traffic, we believe the primary goal of the fake jquery campaign is to monetize from mobile users. This would explain the level of filtering involved to hide non-qualified traffic.
We weren’t able to get an idea of the scale at play, especially considering that the domain initiating the redirects really only became active in late May. However, given the number of websites that have been compromised, this campaign is quite likely funneling a significant amount of traffic leading to ad fraud.
Malwarebytes users are protected against this campaign both on desktop and mobile.
Indicators of Compromise
Fake jquery domains:
12js[.]org
16js[.]org
22js[.]org
lib0[.]org
16lib[.]org
12lib[.]org
wp11[.]org
Redirects:
financeleader[.]co
afflink[.]org
Malicious APKs:
0e67fd9fc535e0f9cf955444d81b0e84882aa73a317d7c8b79af48d91b79ef19 a210c9960edc5362b23e0a73b92b4ce4597911b00e91e7d3ca82632485c5e68d
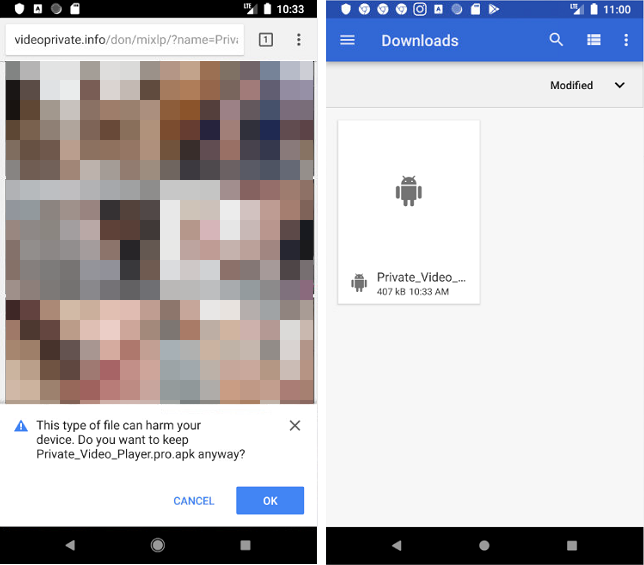
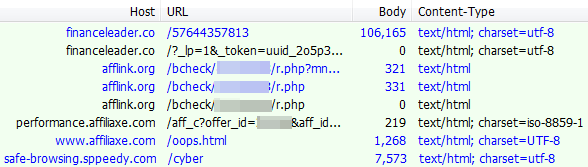
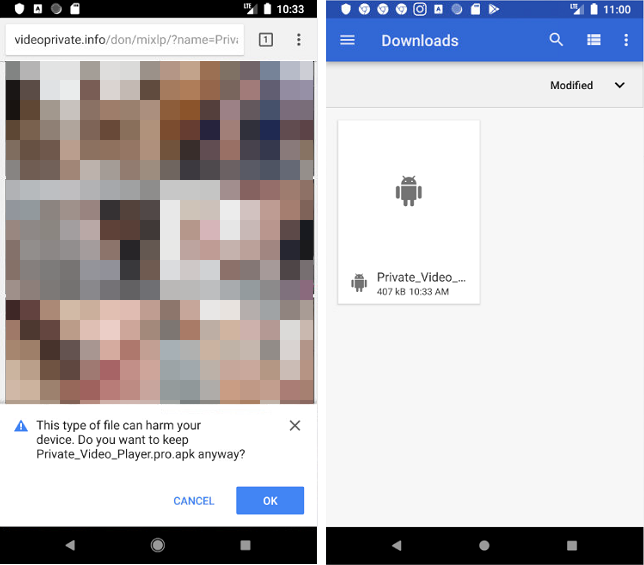
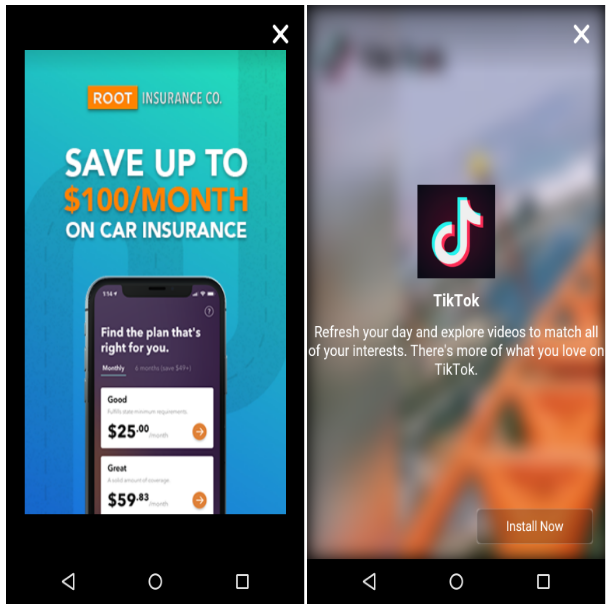
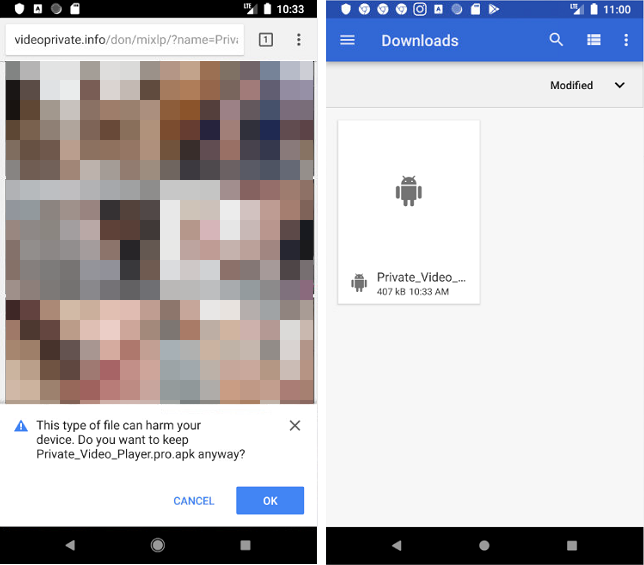
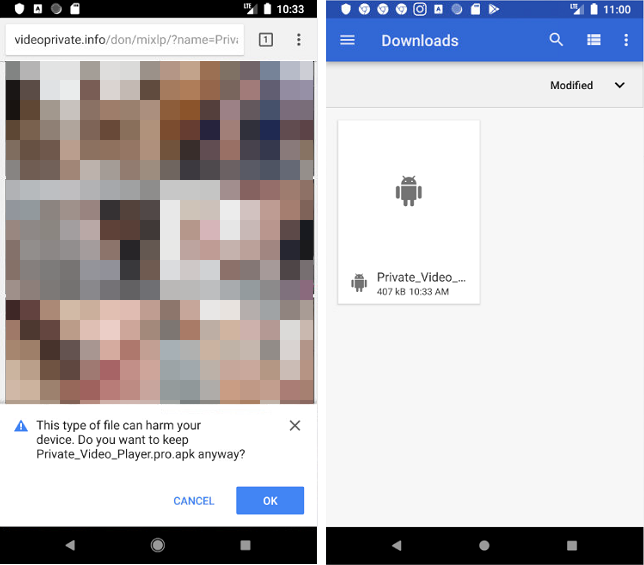
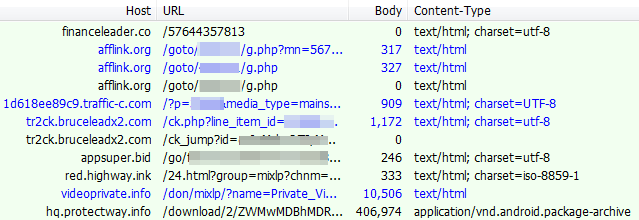
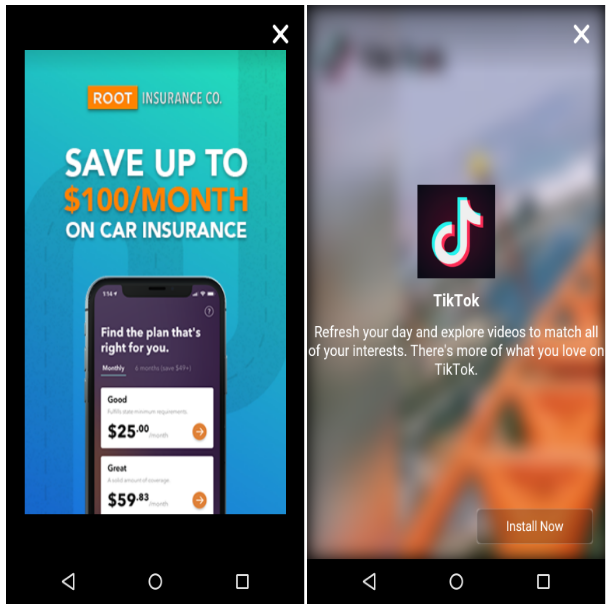
Mobile web traffic
Once we switch to a mobile User-Agent and Android in particular, we can see a lot more activity and a variety of redirects. For example in one case, we were served a bogus adult site that requires users to download an app in order to play the videos:
Associated web traffic:
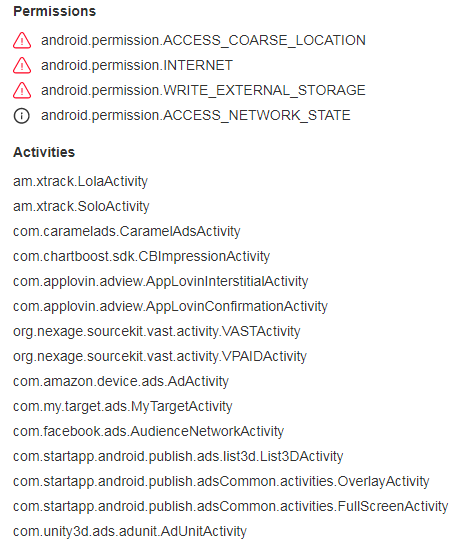
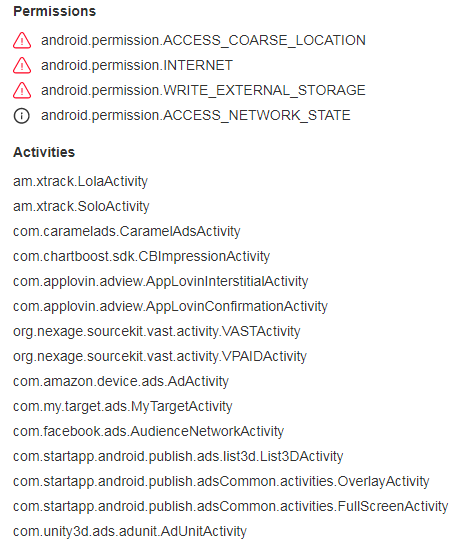
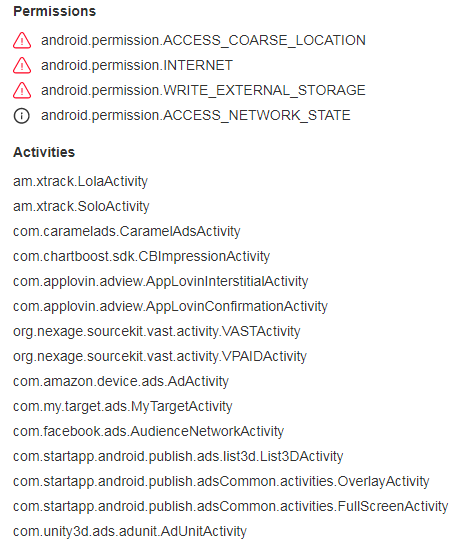
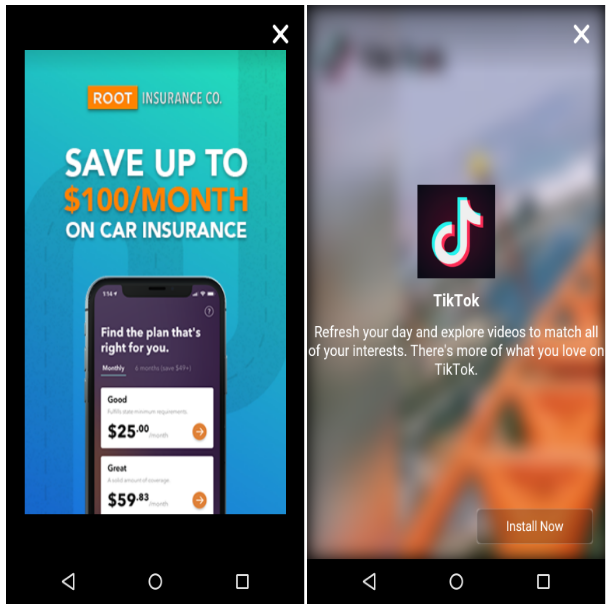
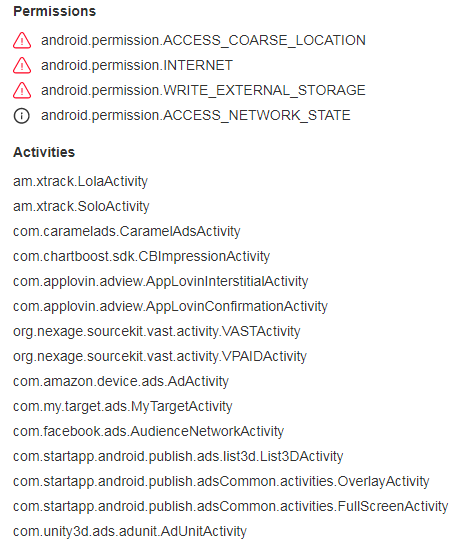
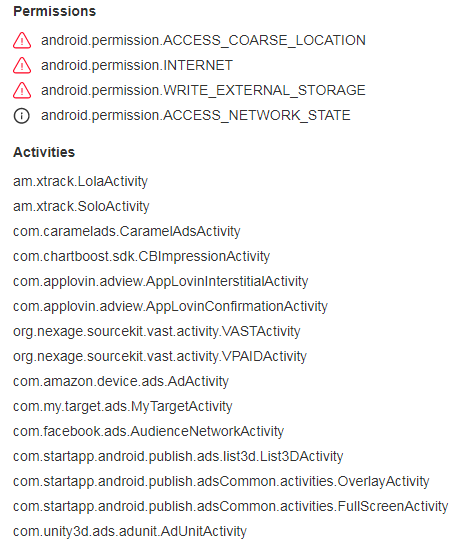
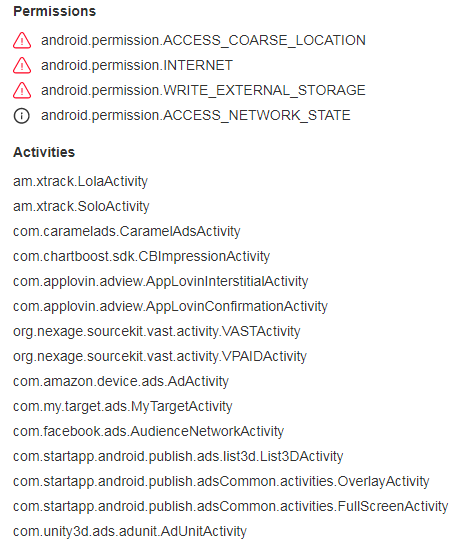
This app is malicious (detected as Android/Trojan.HiddenAds.xt by Malwarebytes) and will generate full screen ads at regular intervals.
Traffic monetization and ad fraud
While we encountered some desktop traffic, we believe the primary goal of the fake jquery campaign is to monetize from mobile users. This would explain the level of filtering involved to hide non-qualified traffic.
We weren’t able to get an idea of the scale at play, especially considering that the domain initiating the redirects really only became active in late May. However, given the number of websites that have been compromised, this campaign is quite likely funneling a significant amount of traffic leading to ad fraud.
Malwarebytes users are protected against this campaign both on desktop and mobile.
Indicators of Compromise
Fake jquery domains:
12js[.]org
16js[.]org
22js[.]org
lib0[.]org
16lib[.]org
12lib[.]org
wp11[.]org
Redirects:
financeleader[.]co
afflink[.]org
Malicious APKs:
0e67fd9fc535e0f9cf955444d81b0e84882aa73a317d7c8b79af48d91b79ef19 a210c9960edc5362b23e0a73b92b4ce4597911b00e91e7d3ca82632485c5e68d
Associated web traffic:
Mobile web traffic
Once we switch to a mobile User-Agent and Android in particular, we can see a lot more activity and a variety of redirects. For example in one case, we were served a bogus adult site that requires users to download an app in order to play the videos:
Associated web traffic:
This app is malicious (detected as Android/Trojan.HiddenAds.xt by Malwarebytes) and will generate full screen ads at regular intervals.
Traffic monetization and ad fraud
While we encountered some desktop traffic, we believe the primary goal of the fake jquery campaign is to monetize from mobile users. This would explain the level of filtering involved to hide non-qualified traffic.
We weren’t able to get an idea of the scale at play, especially considering that the domain initiating the redirects really only became active in late May. However, given the number of websites that have been compromised, this campaign is quite likely funneling a significant amount of traffic leading to ad fraud.
Malwarebytes users are protected against this campaign both on desktop and mobile.
Indicators of Compromise
Fake jquery domains:
12js[.]org
16js[.]org
22js[.]org
lib0[.]org
16lib[.]org
12lib[.]org
wp11[.]org
Redirects:
financeleader[.]co
afflink[.]org
Malicious APKs:
0e67fd9fc535e0f9cf955444d81b0e84882aa73a317d7c8b79af48d91b79ef19 a210c9960edc5362b23e0a73b92b4ce4597911b00e91e7d3ca82632485c5e68d
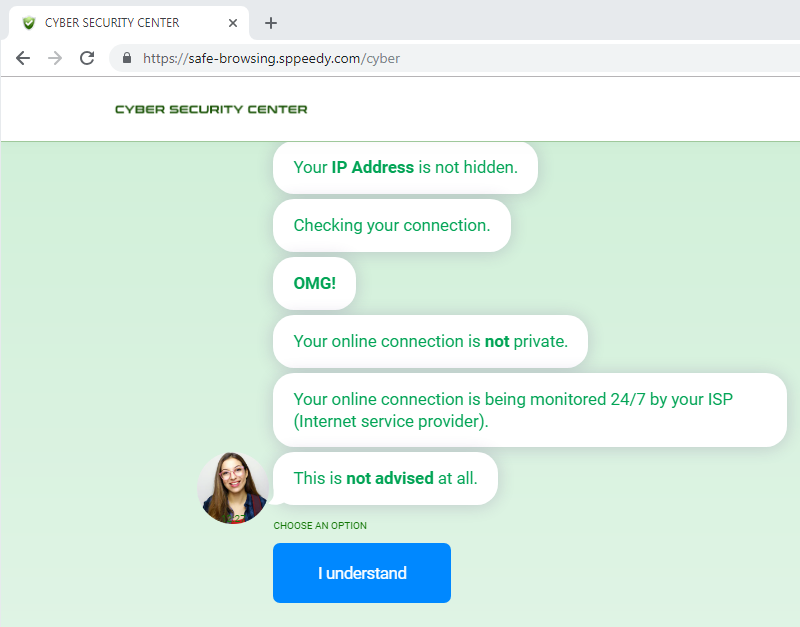
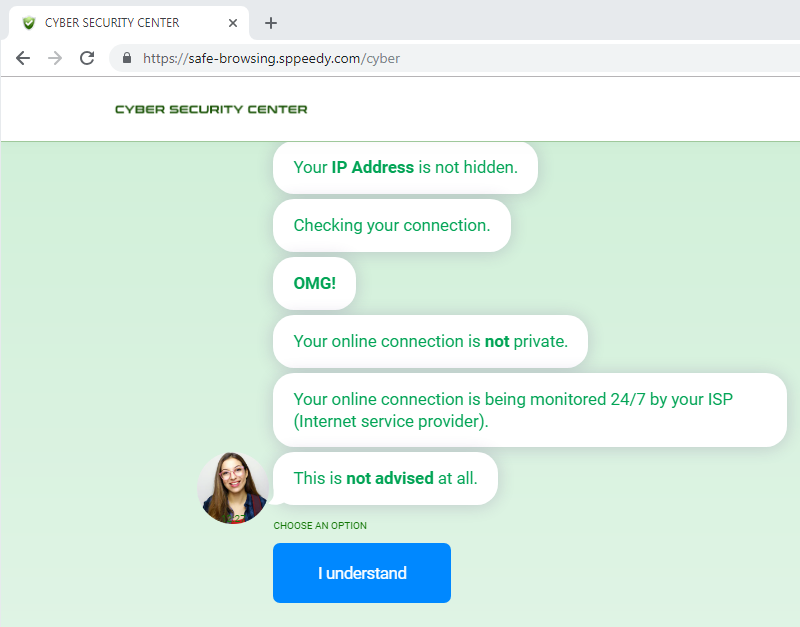
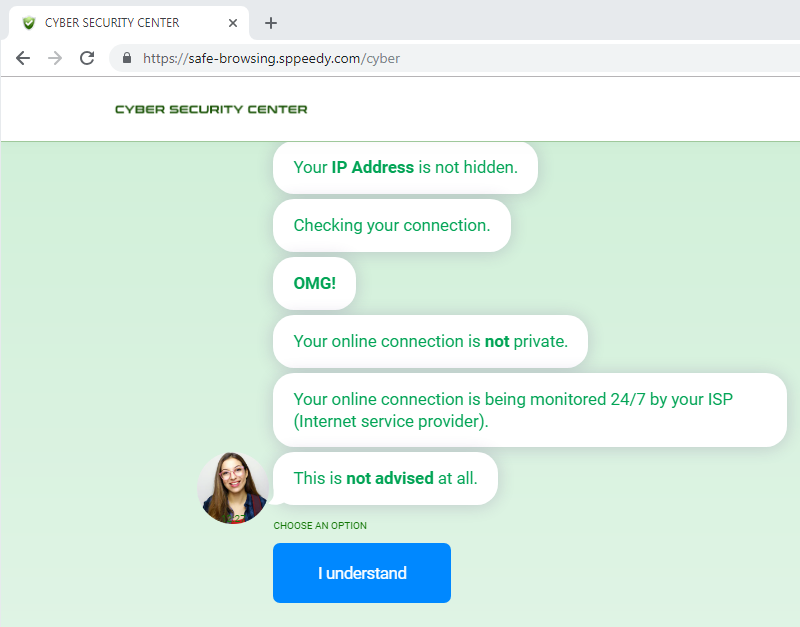
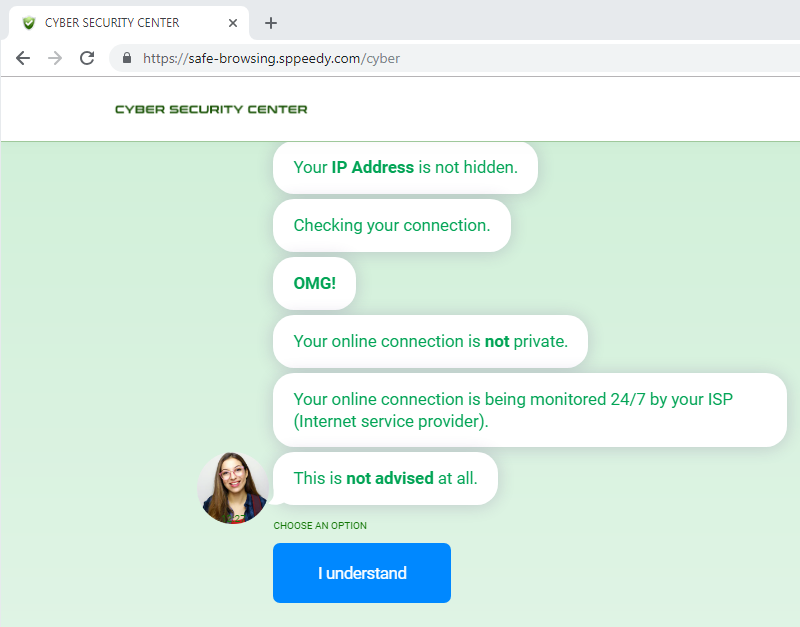
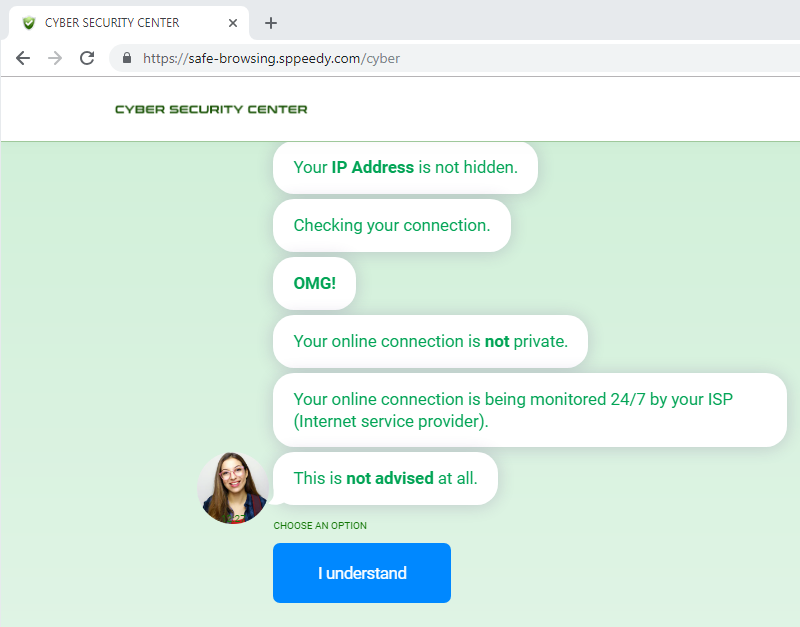
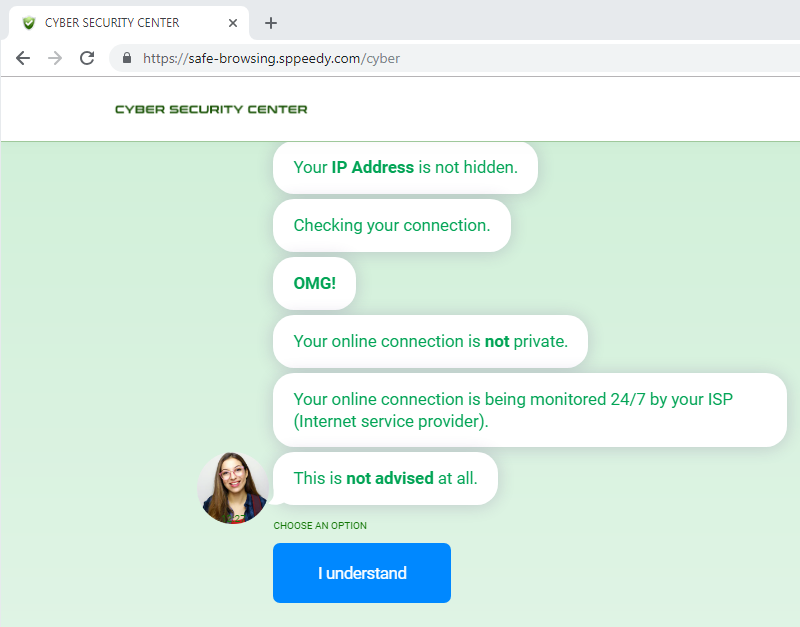
From a non US IP, you are redirected to a page that aggressively advertises VPNs:
Associated web traffic:
Mobile web traffic
Once we switch to a mobile User-Agent and Android in particular, we can see a lot more activity and a variety of redirects. For example in one case, we were served a bogus adult site that requires users to download an app in order to play the videos:
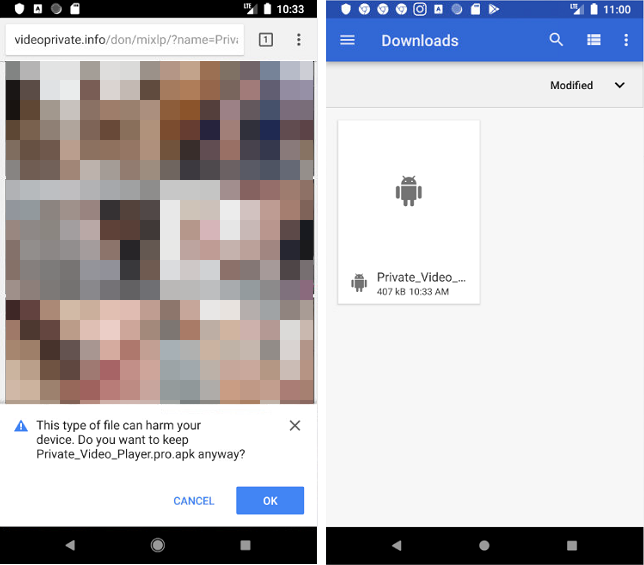
Associated web traffic:
This app is malicious (detected as Android/Trojan.HiddenAds.xt by Malwarebytes) and will generate full screen ads at regular intervals.
Traffic monetization and ad fraud
While we encountered some desktop traffic, we believe the primary goal of the fake jquery campaign is to monetize from mobile users. This would explain the level of filtering involved to hide non-qualified traffic.
We weren’t able to get an idea of the scale at play, especially considering that the domain initiating the redirects really only became active in late May. However, given the number of websites that have been compromised, this campaign is quite likely funneling a significant amount of traffic leading to ad fraud.
Malwarebytes users are protected against this campaign both on desktop and mobile.
Indicators of Compromise
Fake jquery domains:
12js[.]org
16js[.]org
22js[.]org
lib0[.]org
16lib[.]org
12lib[.]org
wp11[.]org
Redirects:
financeleader[.]co
afflink[.]org
Malicious APKs:
0e67fd9fc535e0f9cf955444d81b0e84882aa73a317d7c8b79af48d91b79ef19 a210c9960edc5362b23e0a73b92b4ce4597911b00e91e7d3ca82632485c5e68d
Associated web traffic:
From a non US IP, you are redirected to a page that aggressively advertises VPNs:
Associated web traffic:
Mobile web traffic
Once we switch to a mobile User-Agent and Android in particular, we can see a lot more activity and a variety of redirects. For example in one case, we were served a bogus adult site that requires users to download an app in order to play the videos:
Associated web traffic:
This app is malicious (detected as Android/Trojan.HiddenAds.xt by Malwarebytes) and will generate full screen ads at regular intervals.
Traffic monetization and ad fraud
While we encountered some desktop traffic, we believe the primary goal of the fake jquery campaign is to monetize from mobile users. This would explain the level of filtering involved to hide non-qualified traffic.
We weren’t able to get an idea of the scale at play, especially considering that the domain initiating the redirects really only became active in late May. However, given the number of websites that have been compromised, this campaign is quite likely funneling a significant amount of traffic leading to ad fraud.
Malwarebytes users are protected against this campaign both on desktop and mobile.
Indicators of Compromise
Fake jquery domains:
12js[.]org
16js[.]org
22js[.]org
lib0[.]org
16lib[.]org
12lib[.]org
wp11[.]org
Redirects:
financeleader[.]co
afflink[.]org
Malicious APKs:
0e67fd9fc535e0f9cf955444d81b0e84882aa73a317d7c8b79af48d91b79ef19 a210c9960edc5362b23e0a73b92b4ce4597911b00e91e7d3ca82632485c5e68d
Desktop web traffic
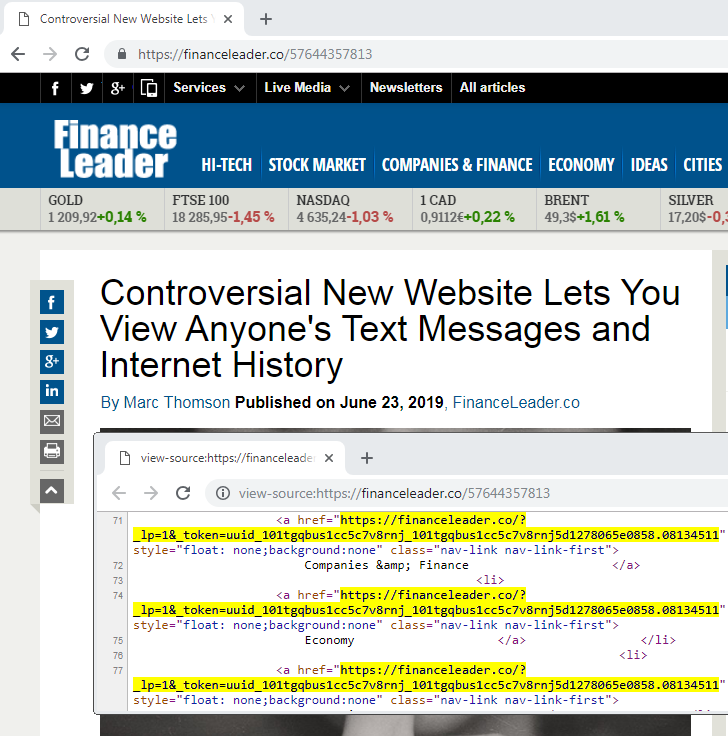
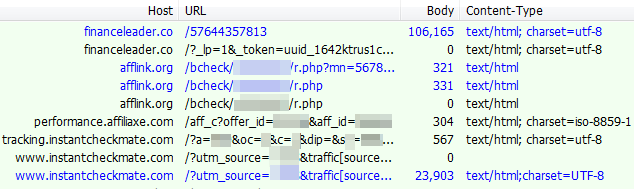
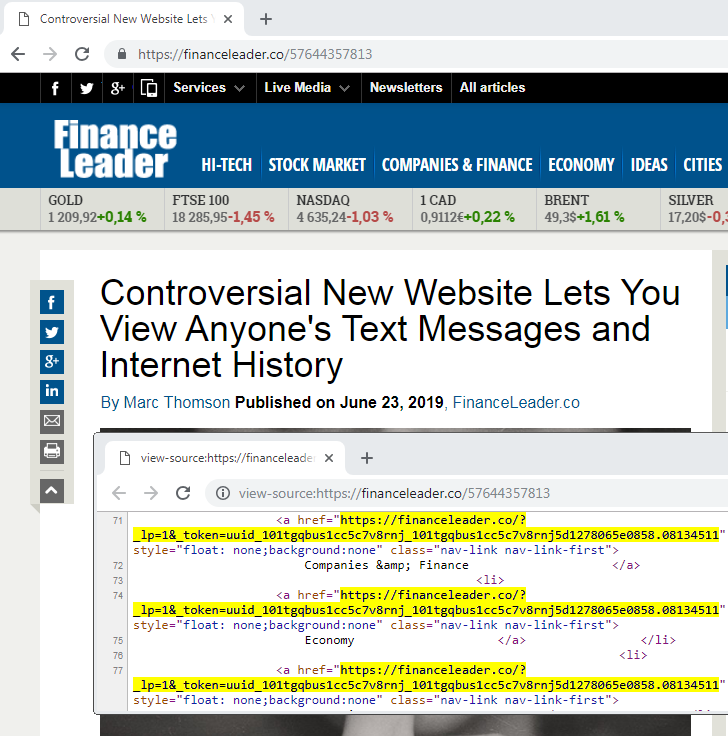
There is some geo-targeting involved for the redirections and clearly desktop users do not appear to be the primary focus here. From a US IP address, you are presented with a bogus site where all items point to the same link that redirect you to instantcheckmate[.]com.
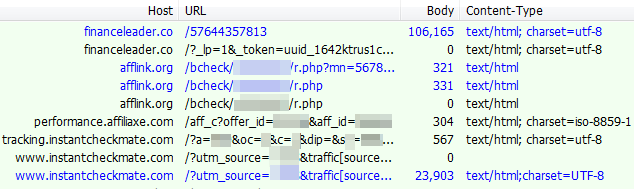
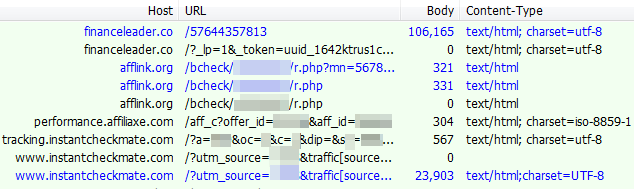
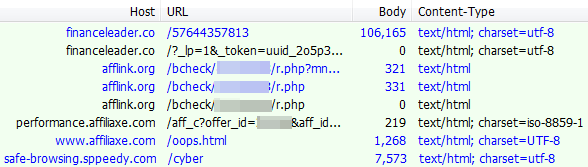
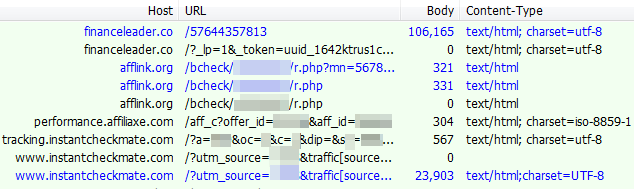
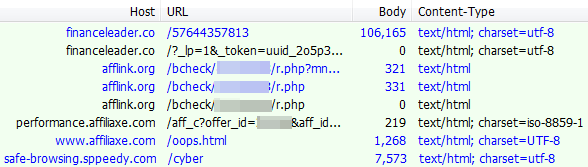
Associated web traffic:
From a non US IP, you are redirected to a page that aggressively advertises VPNs:
Associated web traffic:
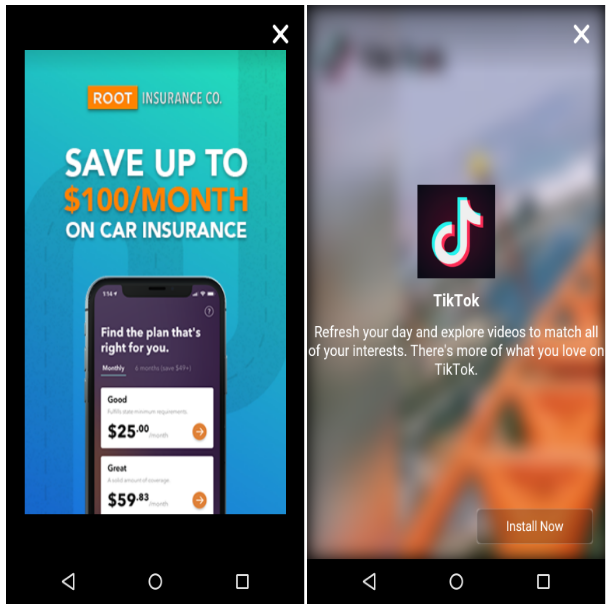
Mobile web traffic
Once we switch to a mobile User-Agent and Android in particular, we can see a lot more activity and a variety of redirects. For example in one case, we were served a bogus adult site that requires users to download an app in order to play the videos:
Associated web traffic:
This app is malicious (detected as Android/Trojan.HiddenAds.xt by Malwarebytes) and will generate full screen ads at regular intervals.
Traffic monetization and ad fraud
While we encountered some desktop traffic, we believe the primary goal of the fake jquery campaign is to monetize from mobile users. This would explain the level of filtering involved to hide non-qualified traffic.
We weren’t able to get an idea of the scale at play, especially considering that the domain initiating the redirects really only became active in late May. However, given the number of websites that have been compromised, this campaign is quite likely funneling a significant amount of traffic leading to ad fraud.
Malwarebytes users are protected against this campaign both on desktop and mobile.
Indicators of Compromise
Fake jquery domains:
12js[.]org
16js[.]org
22js[.]org
lib0[.]org
16lib[.]org
12lib[.]org
wp11[.]org
Redirects:
financeleader[.]co
afflink[.]org
Malicious APKs:
0e67fd9fc535e0f9cf955444d81b0e84882aa73a317d7c8b79af48d91b79ef19 a210c9960edc5362b23e0a73b92b4ce4597911b00e91e7d3ca82632485c5e68d
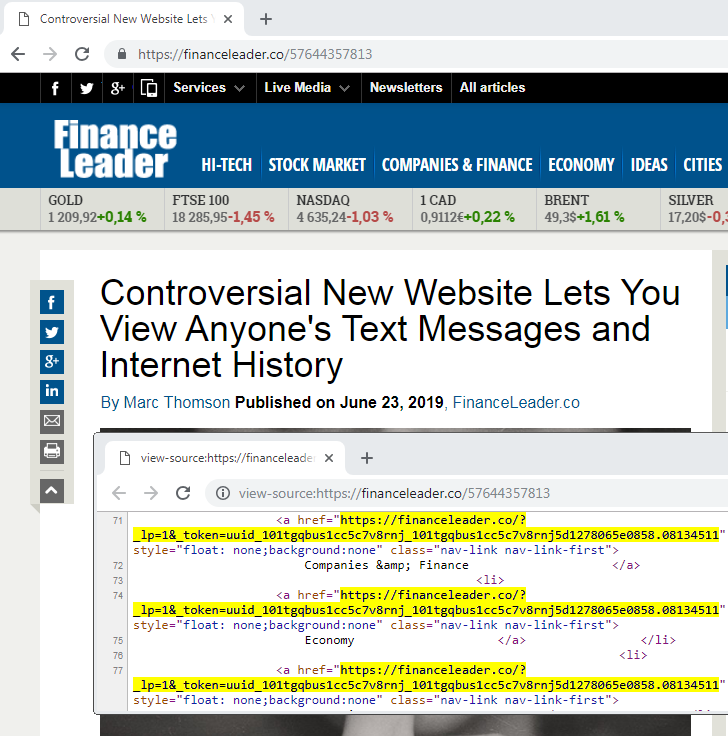
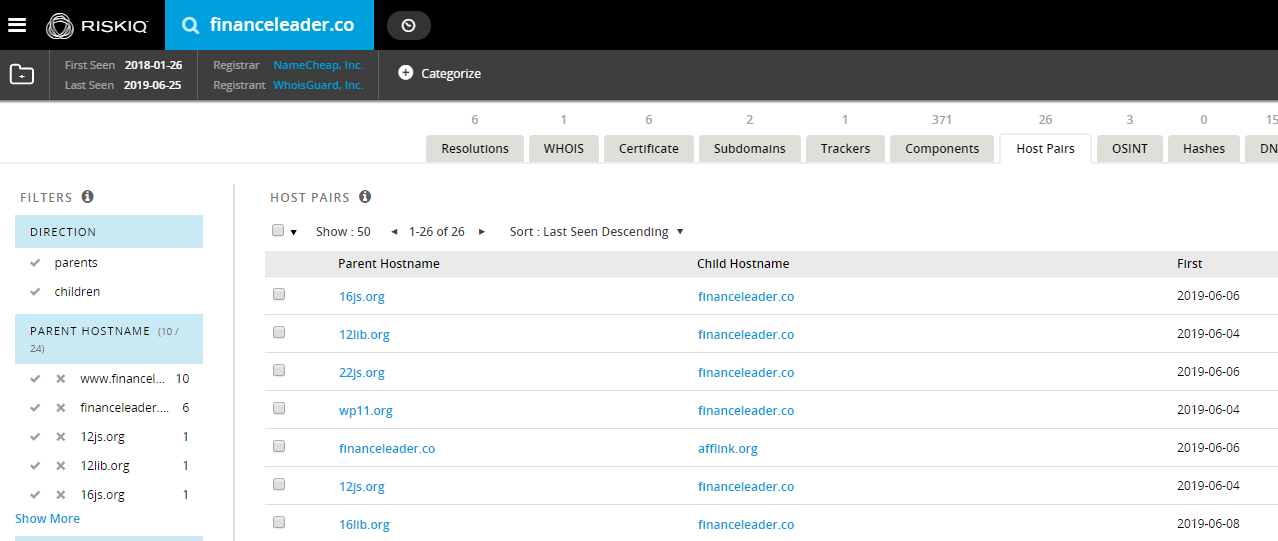
We can see that it contains a redirect to: financeleader[.]co. A cursory check on this domain confirms the host pairs corresponding to those fake jquery domains. It’s worth noting that browsing to the root domain without the special identifier will redirect to google.com.
Desktop web traffic
There is some geo-targeting involved for the redirections and clearly desktop users do not appear to be the primary focus here. From a US IP address, you are presented with a bogus site where all items point to the same link that redirect you to instantcheckmate[.]com.
Associated web traffic:
From a non US IP, you are redirected to a page that aggressively advertises VPNs:
Associated web traffic:
Mobile web traffic
Once we switch to a mobile User-Agent and Android in particular, we can see a lot more activity and a variety of redirects. For example in one case, we were served a bogus adult site that requires users to download an app in order to play the videos:
Associated web traffic:
This app is malicious (detected as Android/Trojan.HiddenAds.xt by Malwarebytes) and will generate full screen ads at regular intervals.
Traffic monetization and ad fraud
While we encountered some desktop traffic, we believe the primary goal of the fake jquery campaign is to monetize from mobile users. This would explain the level of filtering involved to hide non-qualified traffic.
We weren’t able to get an idea of the scale at play, especially considering that the domain initiating the redirects really only became active in late May. However, given the number of websites that have been compromised, this campaign is quite likely funneling a significant amount of traffic leading to ad fraud.
Malwarebytes users are protected against this campaign both on desktop and mobile.
Indicators of Compromise
Fake jquery domains:
12js[.]org
16js[.]org
22js[.]org
lib0[.]org
16lib[.]org
12lib[.]org
wp11[.]org
Redirects:
financeleader[.]co
afflink[.]org
Malicious APKs:
0e67fd9fc535e0f9cf955444d81b0e84882aa73a317d7c8b79af48d91b79ef19 a210c9960edc5362b23e0a73b92b4ce4597911b00e91e7d3ca82632485c5e68d
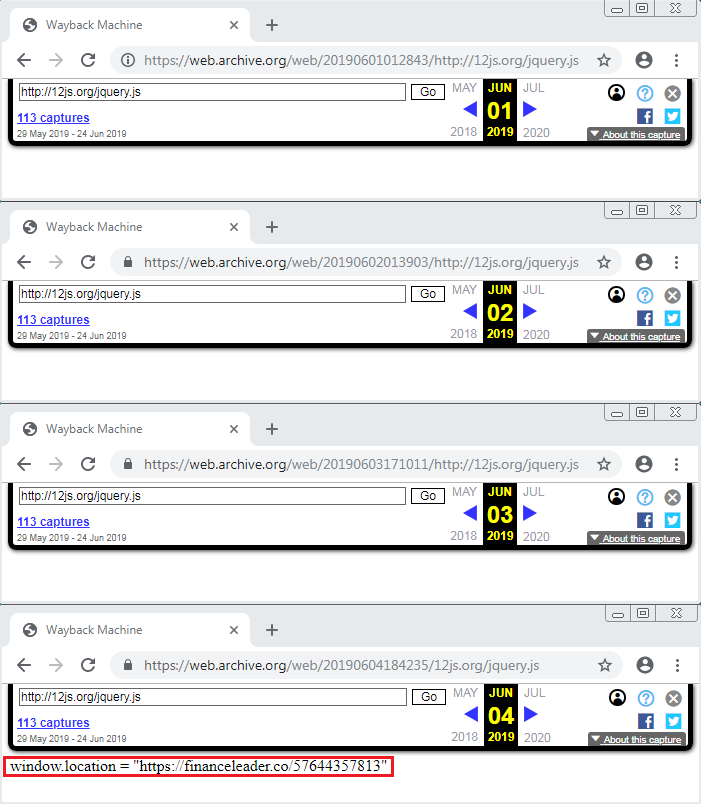
However, with some persistence and luck, we were able to find an archive of this script when it was not empty.
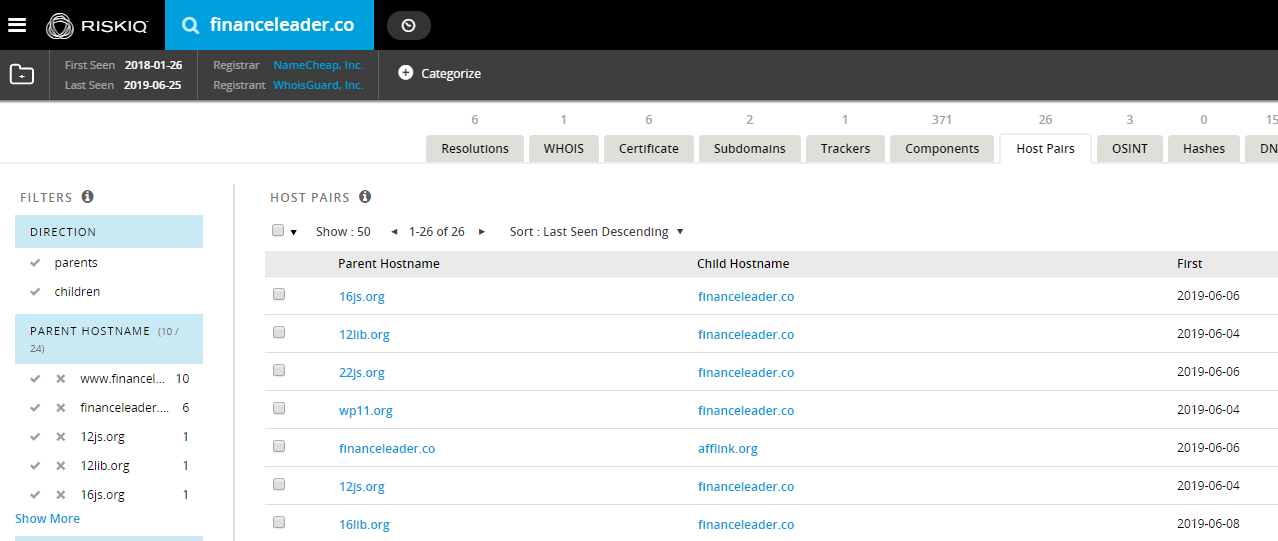
We can see that it contains a redirect to: financeleader[.]co. A cursory check on this domain confirms the host pairs corresponding to those fake jquery domains. It’s worth noting that browsing to the root domain without the special identifier will redirect to google.com.
Desktop web traffic
There is some geo-targeting involved for the redirections and clearly desktop users do not appear to be the primary focus here. From a US IP address, you are presented with a bogus site where all items point to the same link that redirect you to instantcheckmate[.]com.
Associated web traffic:
From a non US IP, you are redirected to a page that aggressively advertises VPNs:
Associated web traffic:
Mobile web traffic
Once we switch to a mobile User-Agent and Android in particular, we can see a lot more activity and a variety of redirects. For example in one case, we were served a bogus adult site that requires users to download an app in order to play the videos:
Associated web traffic:
This app is malicious (detected as Android/Trojan.HiddenAds.xt by Malwarebytes) and will generate full screen ads at regular intervals.
Traffic monetization and ad fraud
While we encountered some desktop traffic, we believe the primary goal of the fake jquery campaign is to monetize from mobile users. This would explain the level of filtering involved to hide non-qualified traffic.
We weren’t able to get an idea of the scale at play, especially considering that the domain initiating the redirects really only became active in late May. However, given the number of websites that have been compromised, this campaign is quite likely funneling a significant amount of traffic leading to ad fraud.
Malwarebytes users are protected against this campaign both on desktop and mobile.
Indicators of Compromise
Fake jquery domains:
12js[.]org
16js[.]org
22js[.]org
lib0[.]org
16lib[.]org
12lib[.]org
wp11[.]org
Redirects:
financeleader[.]co
afflink[.]org
Malicious APKs:
0e67fd9fc535e0f9cf955444d81b0e84882aa73a317d7c8b79af48d91b79ef19 a210c9960edc5362b23e0a73b92b4ce4597911b00e91e7d3ca82632485c5e68d
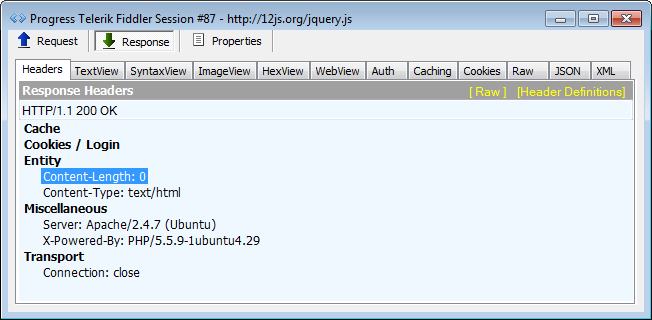
Like other researchers before, when we replayed traffic the supposedly malicious JavaScript was once again empty.
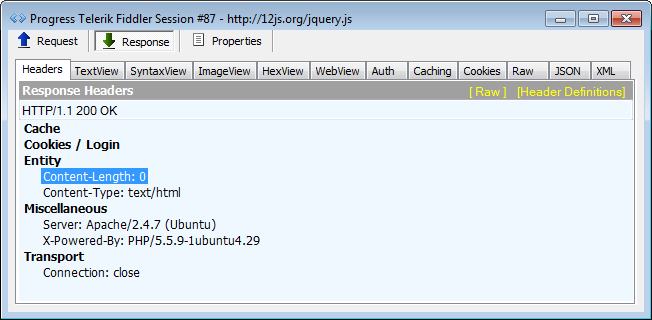
However, with some persistence and luck, we were able to find an archive of this script when it was not empty.
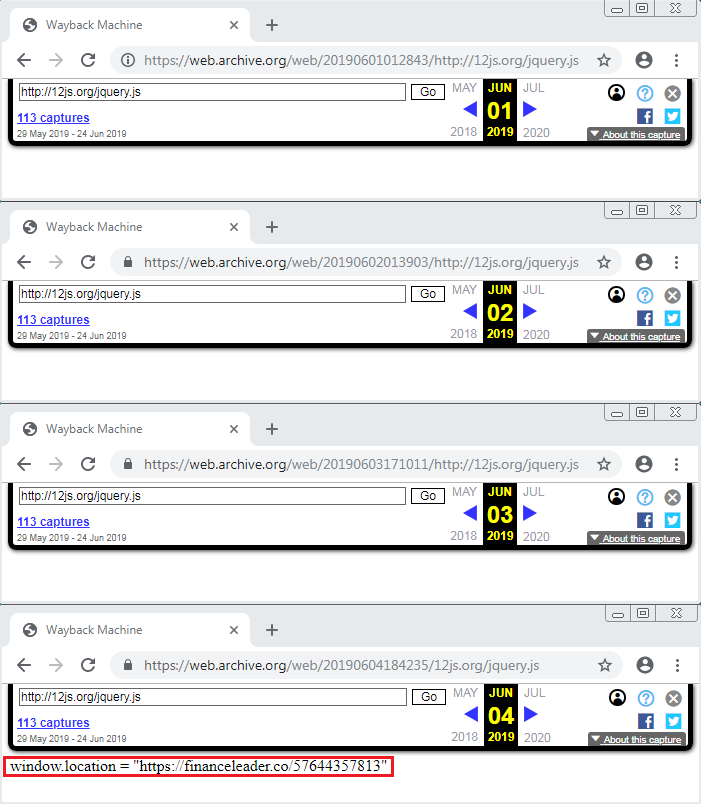
We can see that it contains a redirect to: financeleader[.]co. A cursory check on this domain confirms the host pairs corresponding to those fake jquery domains. It’s worth noting that browsing to the root domain without the special identifier will redirect to google.com.
Desktop web traffic
There is some geo-targeting involved for the redirections and clearly desktop users do not appear to be the primary focus here. From a US IP address, you are presented with a bogus site where all items point to the same link that redirect you to instantcheckmate[.]com.
Associated web traffic:
From a non US IP, you are redirected to a page that aggressively advertises VPNs:
Associated web traffic:
Mobile web traffic
Once we switch to a mobile User-Agent and Android in particular, we can see a lot more activity and a variety of redirects. For example in one case, we were served a bogus adult site that requires users to download an app in order to play the videos:
Associated web traffic:
This app is malicious (detected as Android/Trojan.HiddenAds.xt by Malwarebytes) and will generate full screen ads at regular intervals.
Traffic monetization and ad fraud
While we encountered some desktop traffic, we believe the primary goal of the fake jquery campaign is to monetize from mobile users. This would explain the level of filtering involved to hide non-qualified traffic.
We weren’t able to get an idea of the scale at play, especially considering that the domain initiating the redirects really only became active in late May. However, given the number of websites that have been compromised, this campaign is quite likely funneling a significant amount of traffic leading to ad fraud.
Malwarebytes users are protected against this campaign both on desktop and mobile.
Indicators of Compromise
Fake jquery domains:
12js[.]org
16js[.]org
22js[.]org
lib0[.]org
16lib[.]org
12lib[.]org
wp11[.]org
Redirects:
financeleader[.]co
afflink[.]org
Malicious APKs:
0e67fd9fc535e0f9cf955444d81b0e84882aa73a317d7c8b79af48d91b79ef19 a210c9960edc5362b23e0a73b92b4ce4597911b00e91e7d3ca82632485c5e68d
While we do not know the exact infection vector, many of these websites are running an outdated Content Management System (CMS).
Like other researchers before, when we replayed traffic the supposedly malicious JavaScript was once again empty.
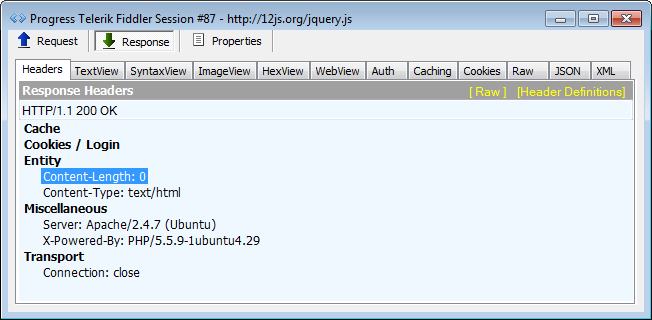
However, with some persistence and luck, we were able to find an archive of this script when it was not empty.
We can see that it contains a redirect to: financeleader[.]co. A cursory check on this domain confirms the host pairs corresponding to those fake jquery domains. It’s worth noting that browsing to the root domain without the special identifier will redirect to google.com.
Desktop web traffic
There is some geo-targeting involved for the redirections and clearly desktop users do not appear to be the primary focus here. From a US IP address, you are presented with a bogus site where all items point to the same link that redirect you to instantcheckmate[.]com.
Associated web traffic:
From a non US IP, you are redirected to a page that aggressively advertises VPNs:
Associated web traffic:
Mobile web traffic
Once we switch to a mobile User-Agent and Android in particular, we can see a lot more activity and a variety of redirects. For example in one case, we were served a bogus adult site that requires users to download an app in order to play the videos:
Associated web traffic:
This app is malicious (detected as Android/Trojan.HiddenAds.xt by Malwarebytes) and will generate full screen ads at regular intervals.
Traffic monetization and ad fraud
While we encountered some desktop traffic, we believe the primary goal of the fake jquery campaign is to monetize from mobile users. This would explain the level of filtering involved to hide non-qualified traffic.
We weren’t able to get an idea of the scale at play, especially considering that the domain initiating the redirects really only became active in late May. However, given the number of websites that have been compromised, this campaign is quite likely funneling a significant amount of traffic leading to ad fraud.
Malwarebytes users are protected against this campaign both on desktop and mobile.
Indicators of Compromise
Fake jquery domains:
12js[.]org
16js[.]org
22js[.]org
lib0[.]org
16lib[.]org
12lib[.]org
wp11[.]org
Redirects:
financeleader[.]co
afflink[.]org
Malicious APKs:
0e67fd9fc535e0f9cf955444d81b0e84882aa73a317d7c8b79af48d91b79ef19 a210c9960edc5362b23e0a73b92b4ce4597911b00e91e7d3ca82632485c5e68d
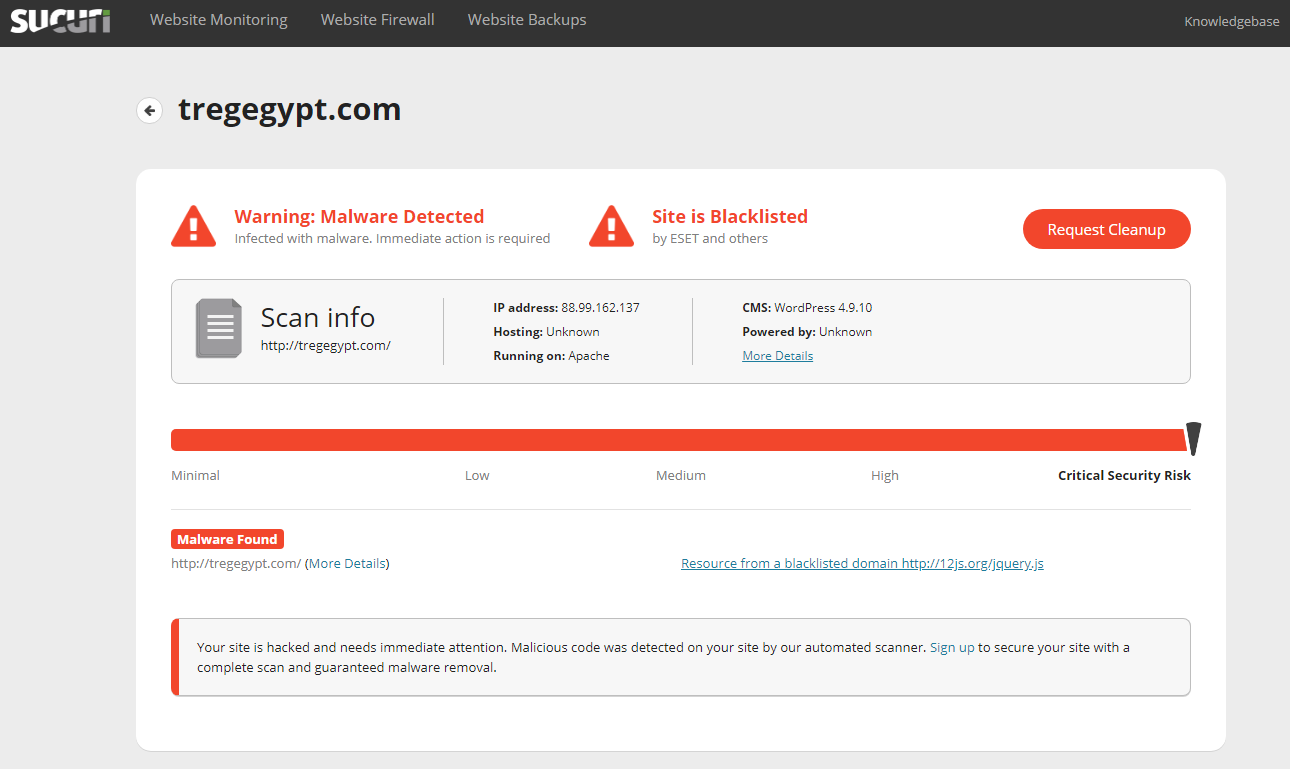
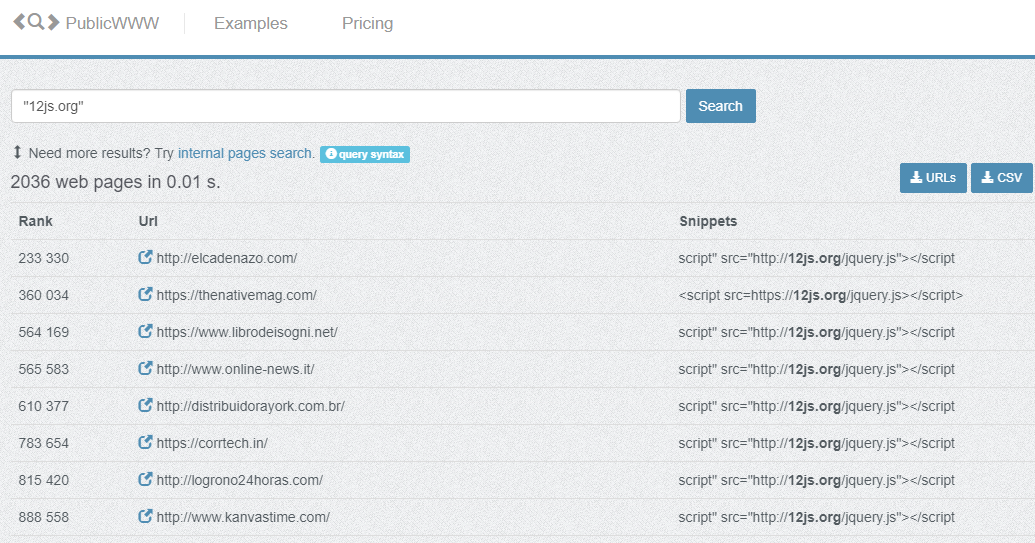
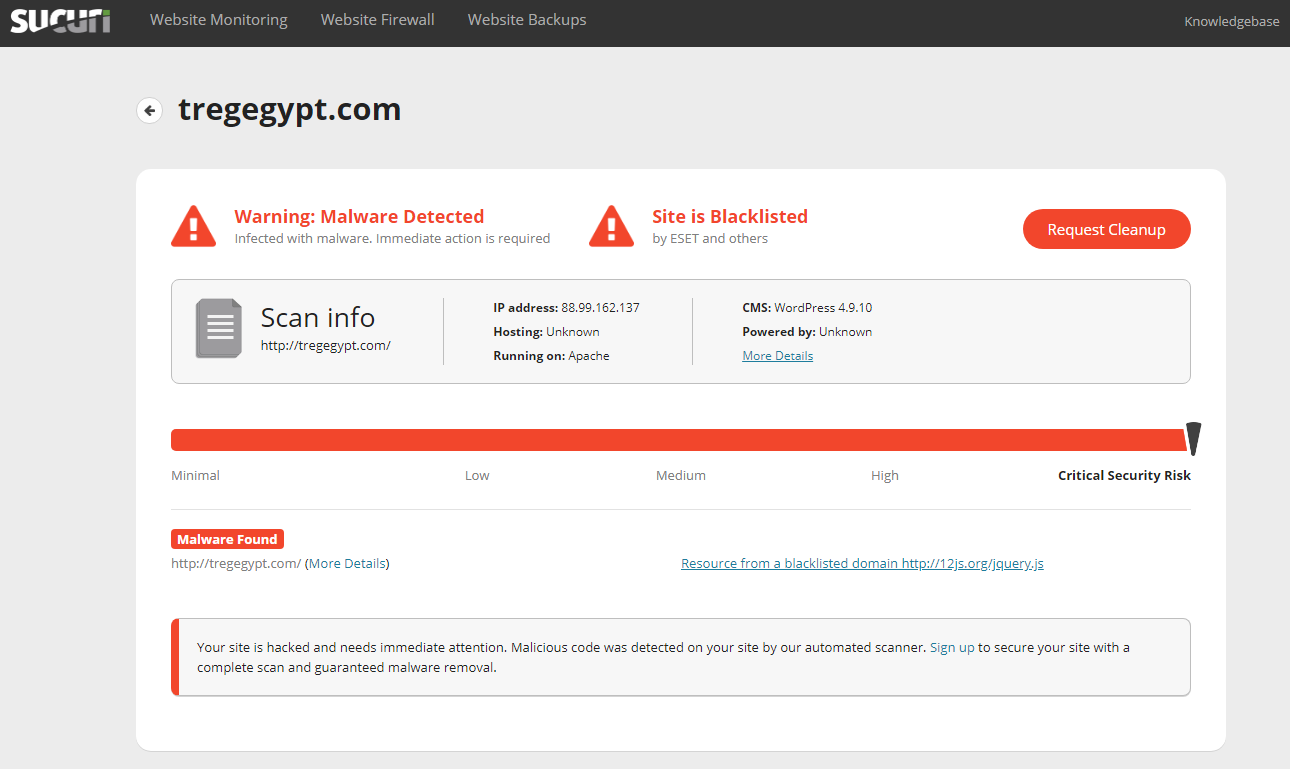
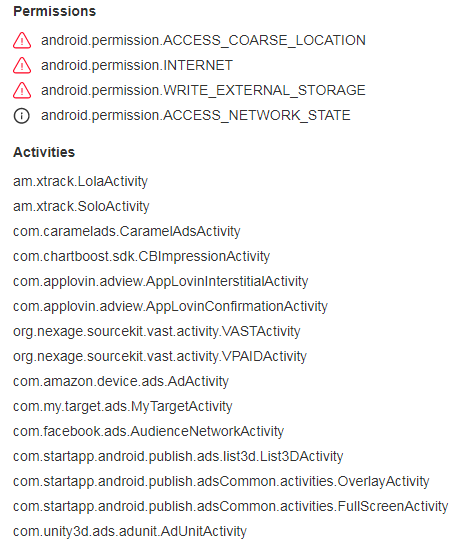
Recently we became aware of new domains used by an old malware campaign known as ‘fake jquery’, previously documented by web security firm Sucuri. Thousands of compromised websites are injected with a reference to an external JavaScript called jquery.js.
However, there is something quite elusive about this campaign with regards to its payload. Indeed, to many researchers the supposedly malicious JavaScript is always blank.
In this blog we share how we were able to identify the purpose of the fake jquery malware infection by looking for artifacts and employing a variety of User-Agent strings and geolocations.
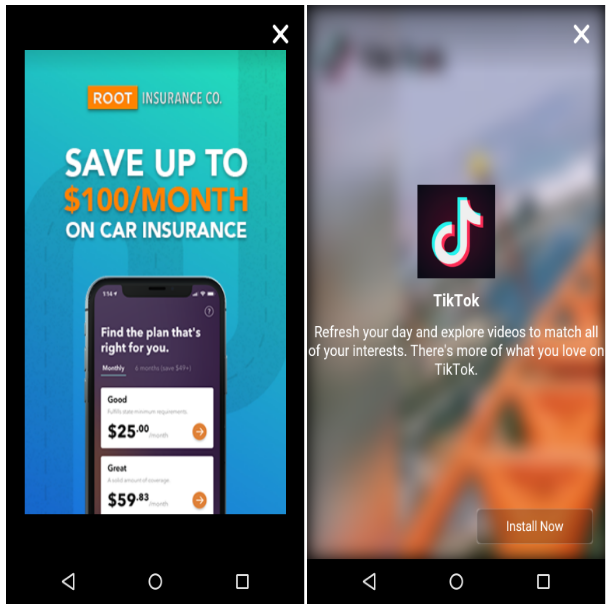
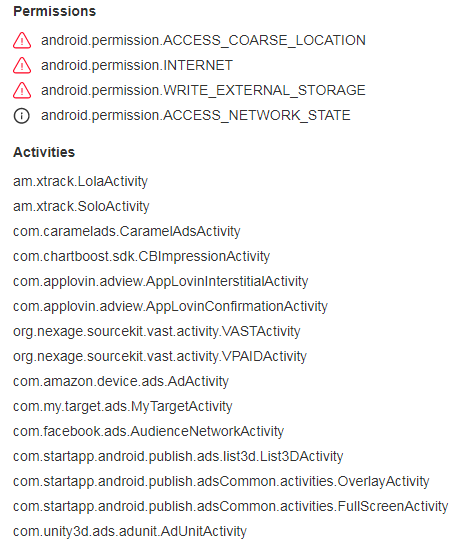
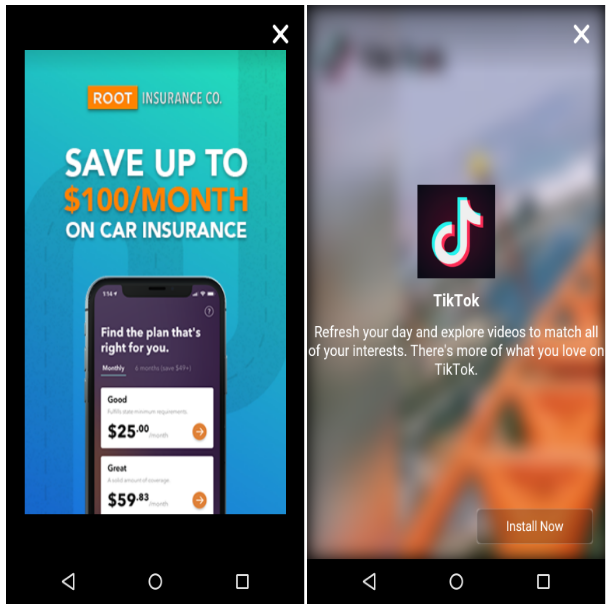
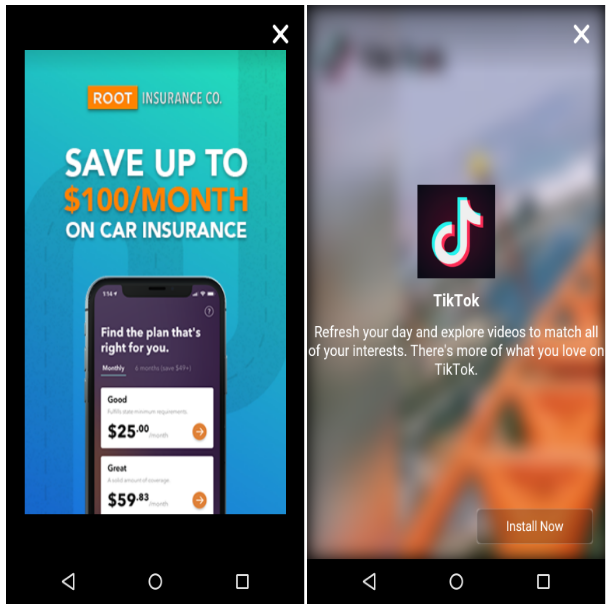
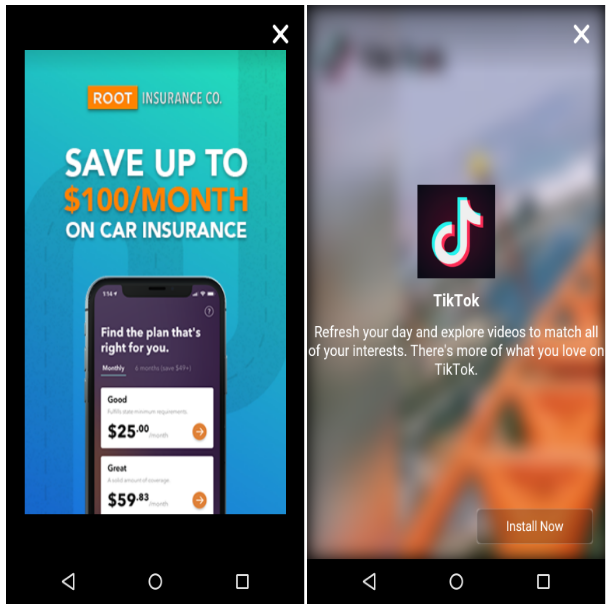
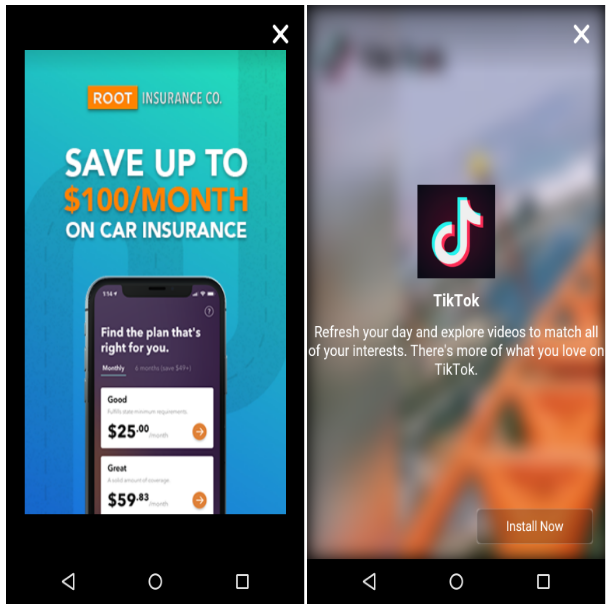
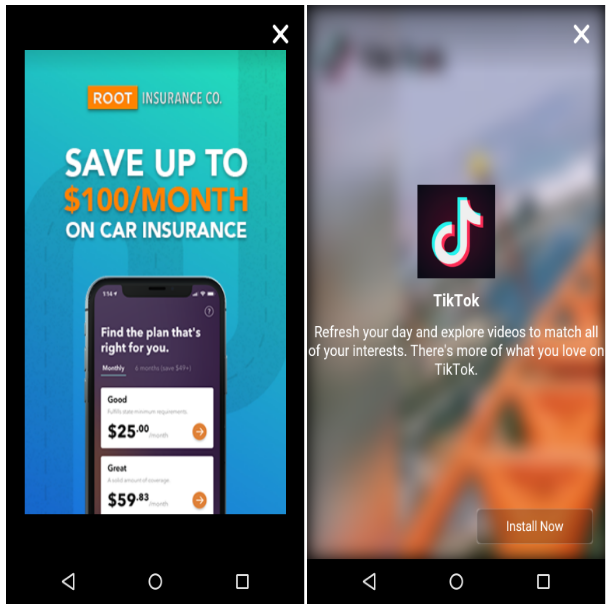
Unsurprisingly, we found a web of malicious redirects via malvertising campaigns with a strong focus on mobile users who are tricked into installing rogue apps. The end goal is to monetize via fullscreen adverts that pop up on your phone at regular intervals.
Looking for a clue
Our search begins by looking up some of the domains mentioned on Twitter by @Placebo52510486. There are thousands of sites listed by PublicWWW that have been injected with malicious jquery lookalikes.
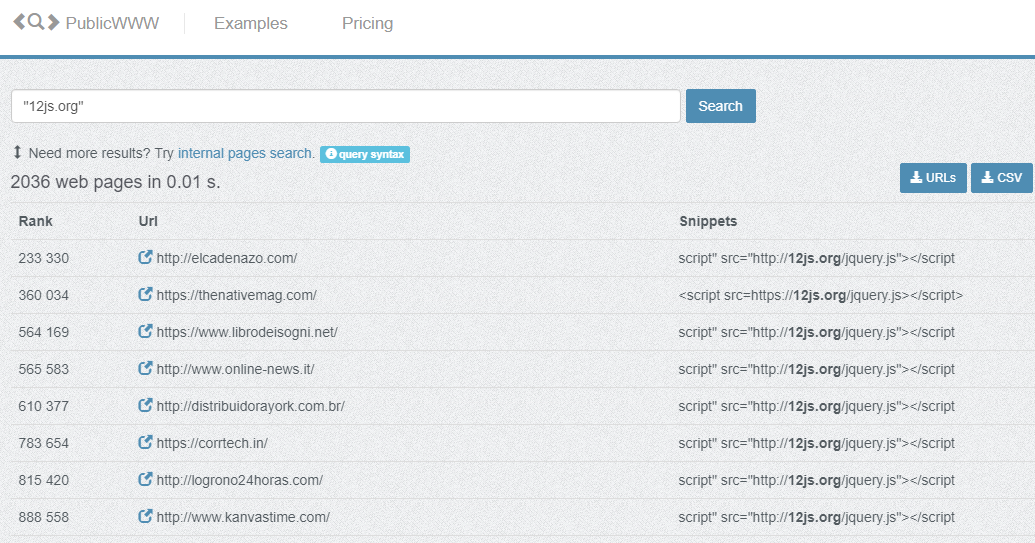
While we do not know the exact infection vector, many of these websites are running an outdated Content Management System (CMS).
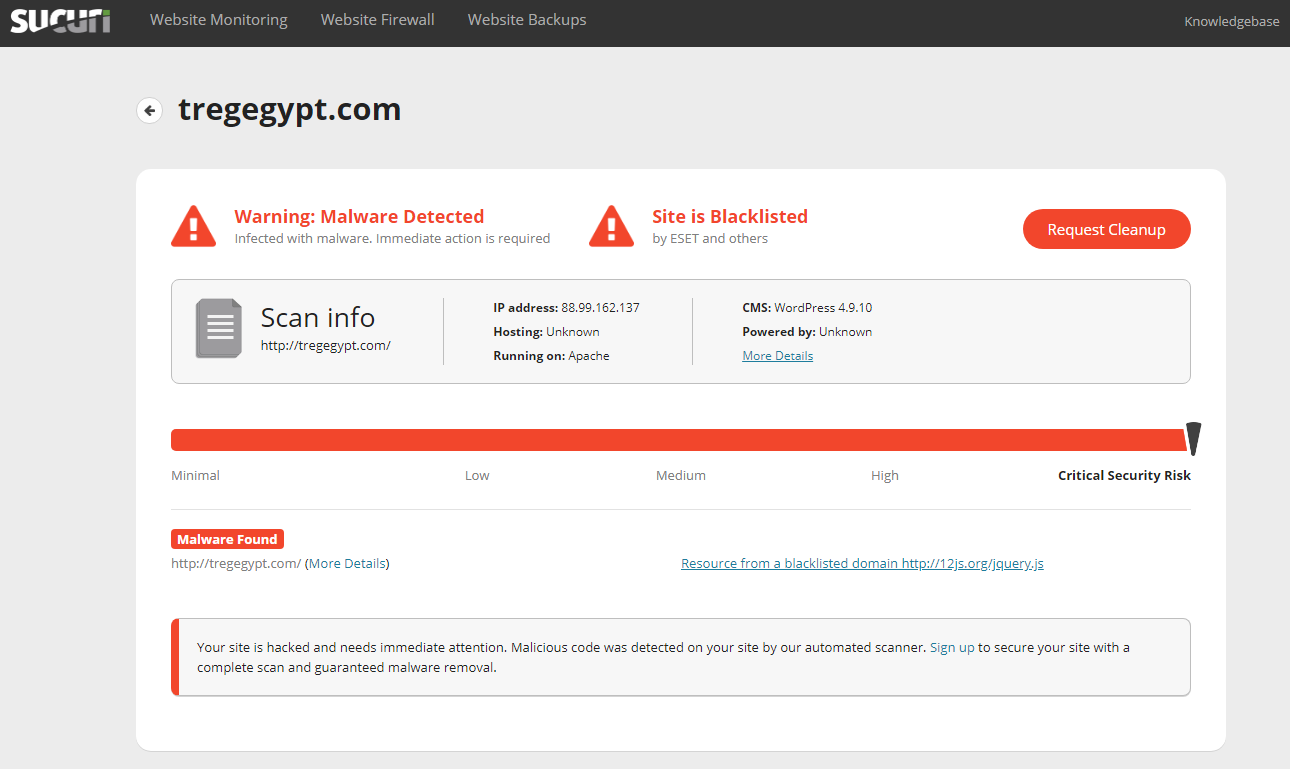
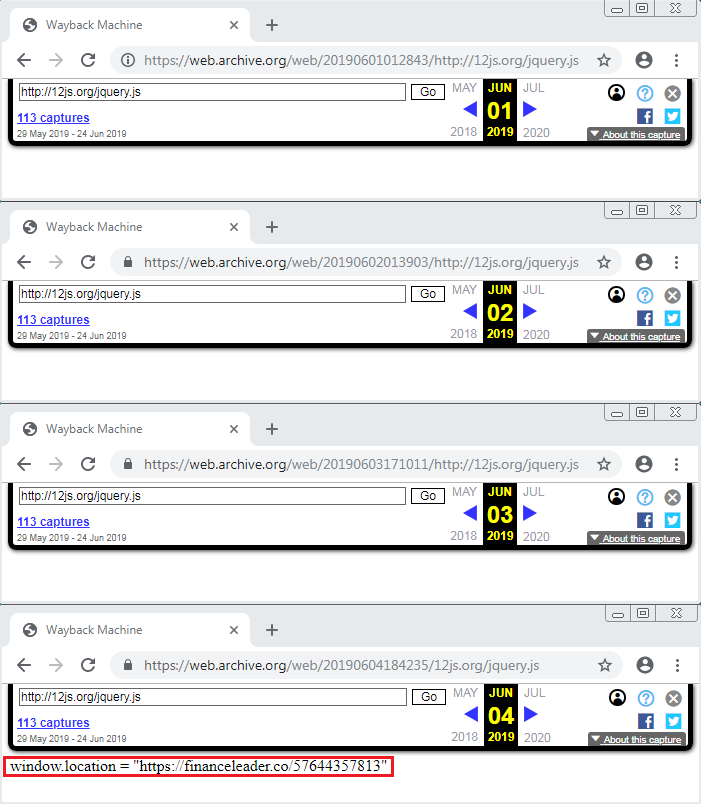
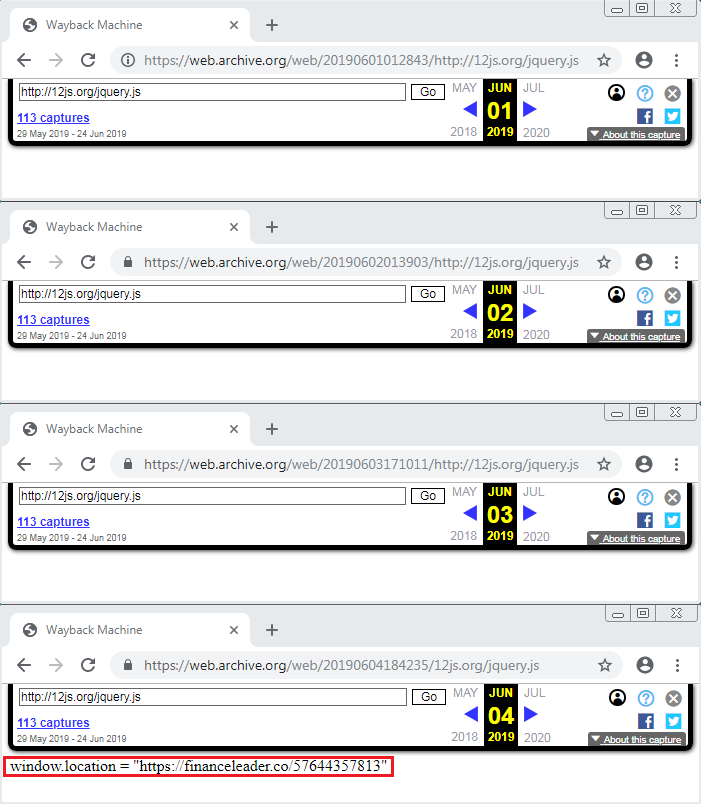
Like other researchers before, when we replayed traffic the supposedly malicious JavaScript was once again empty.
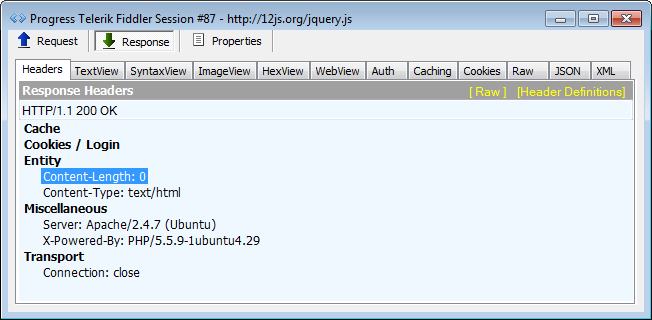
However, with some persistence and luck, we were able to find an archive of this script when it was not empty.
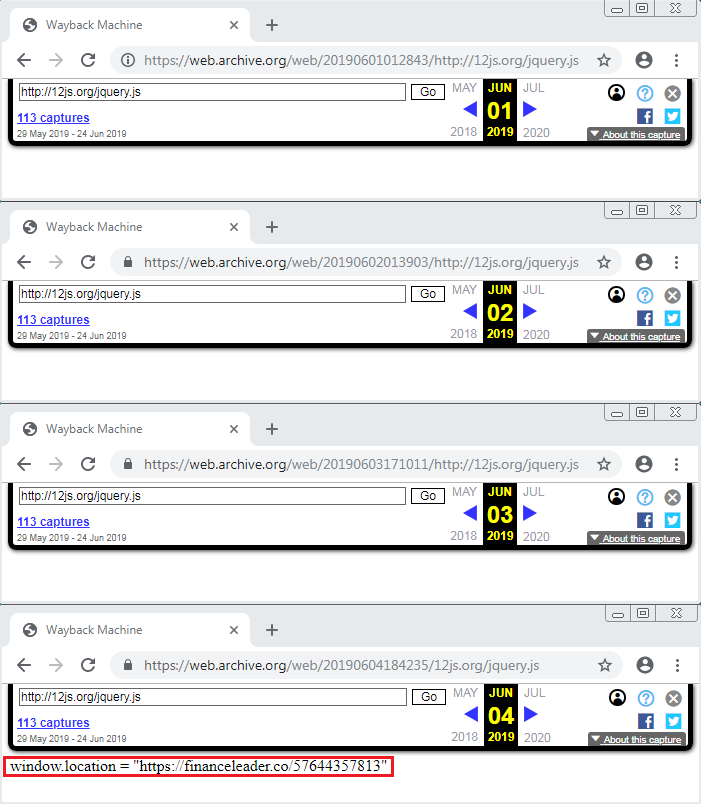
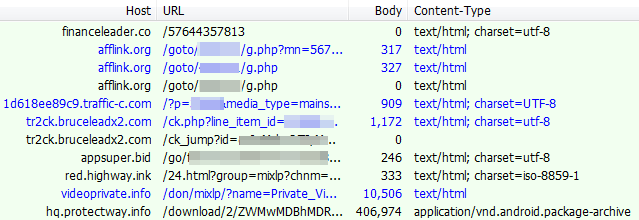
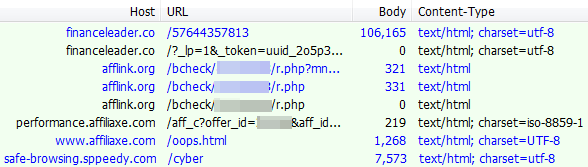
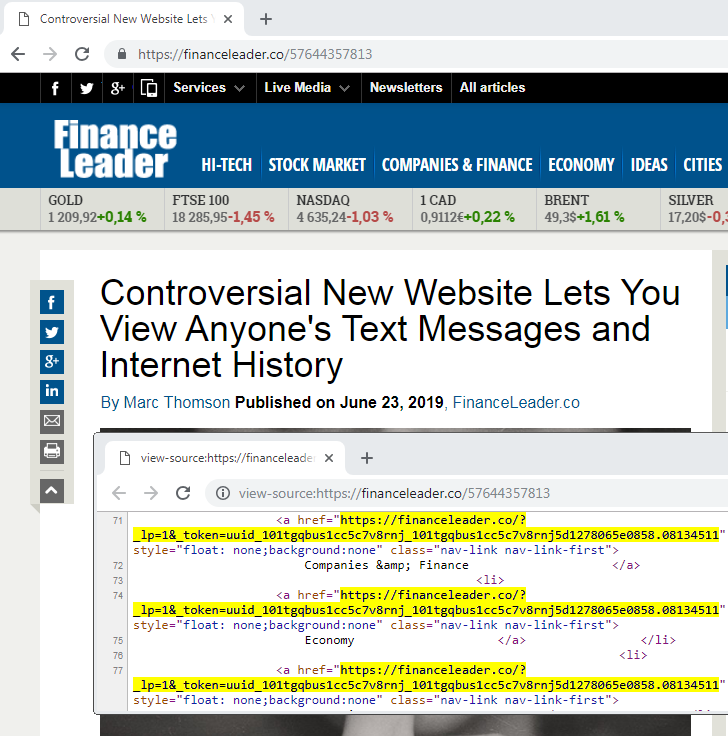
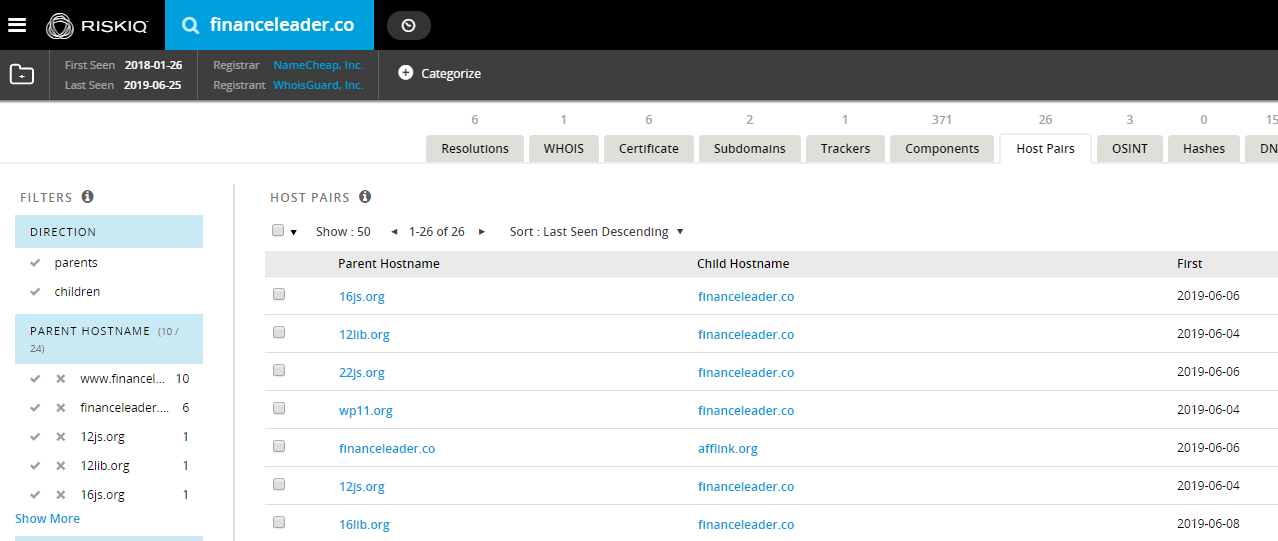
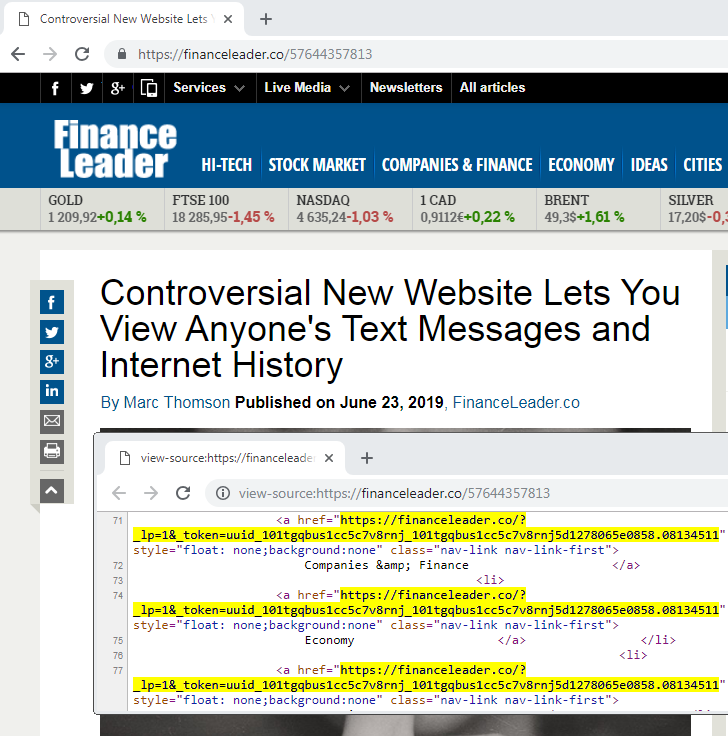
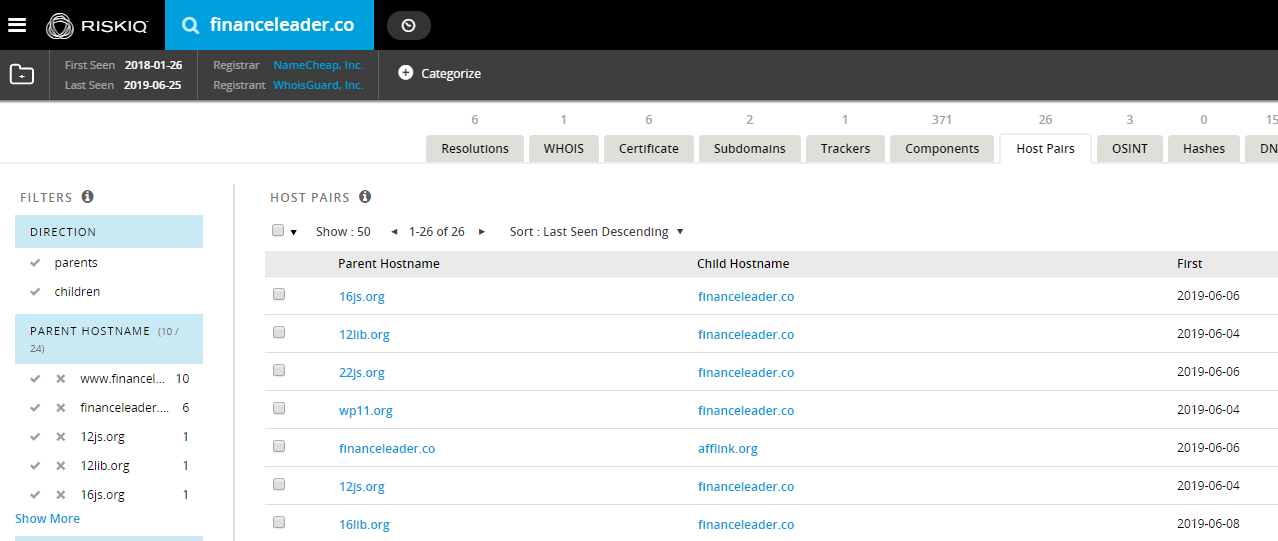
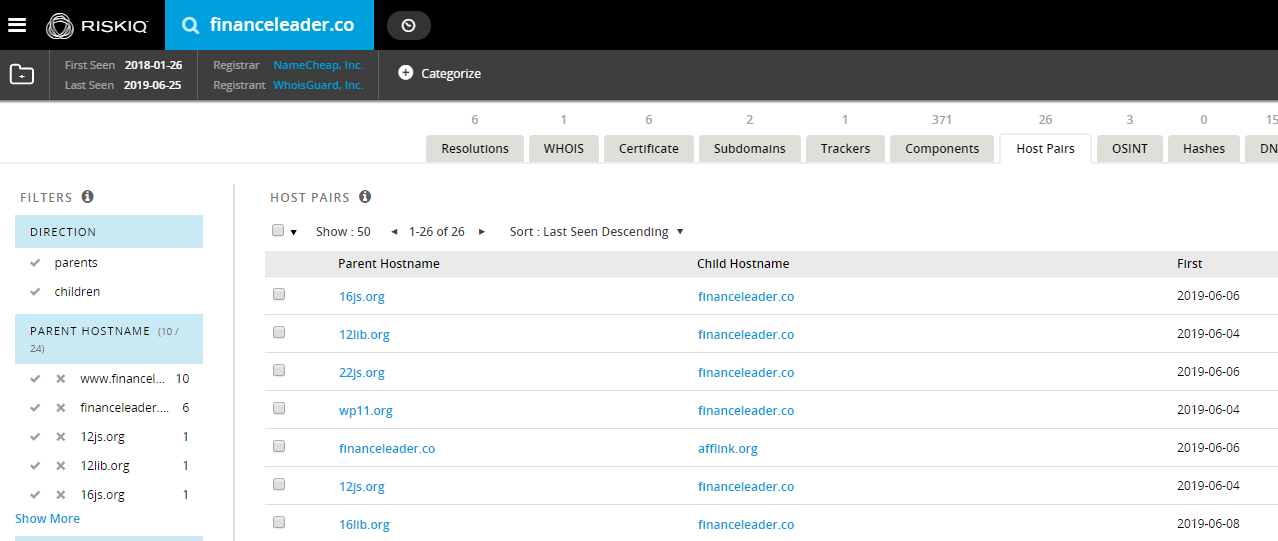
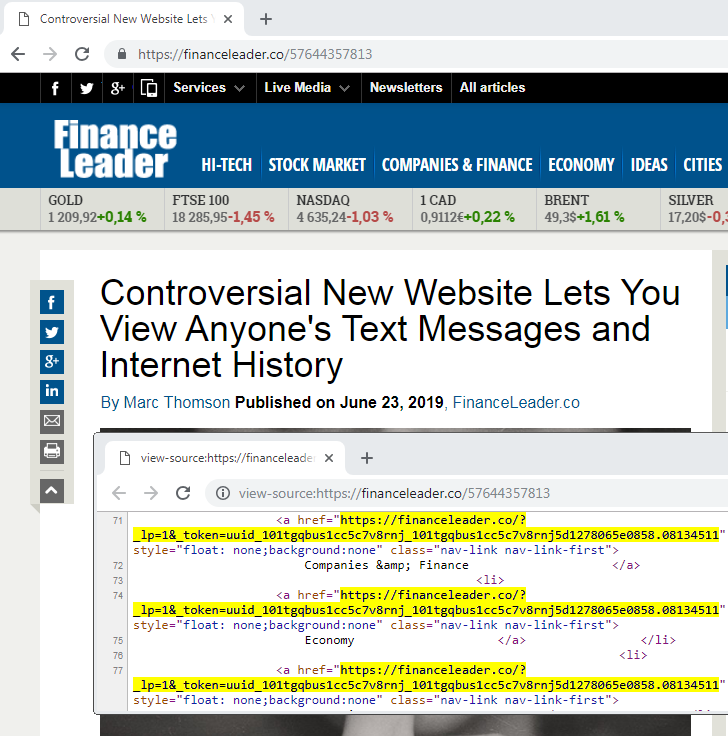
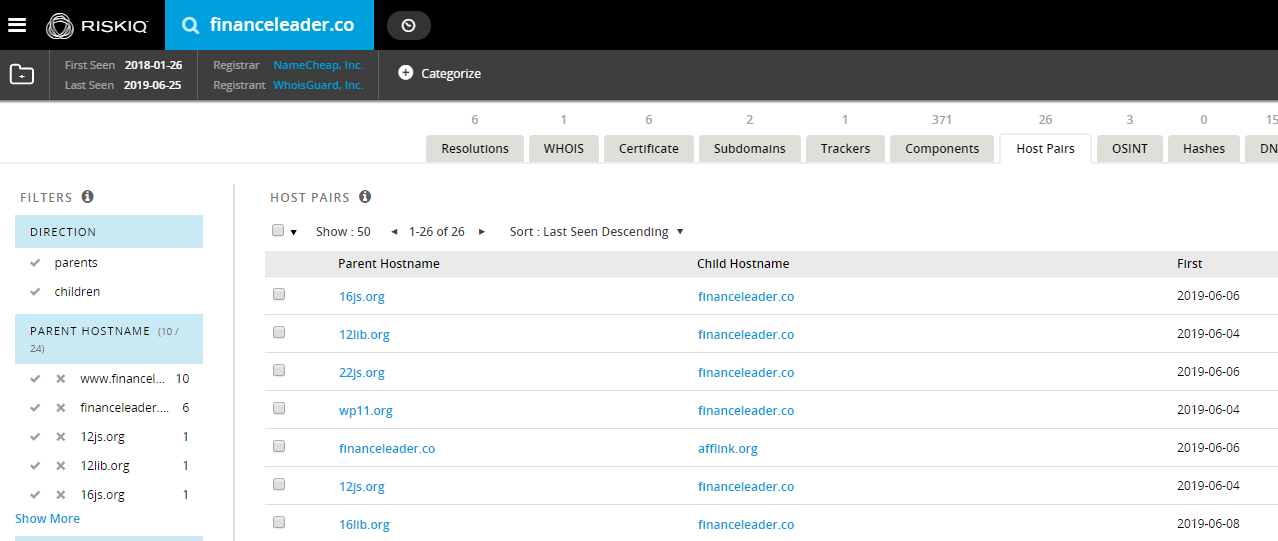
We can see that it contains a redirect to: financeleader[.]co. A cursory check on this domain confirms the host pairs corresponding to those fake jquery domains. It’s worth noting that browsing to the root domain without the special identifier will redirect to google.com.
Desktop web traffic
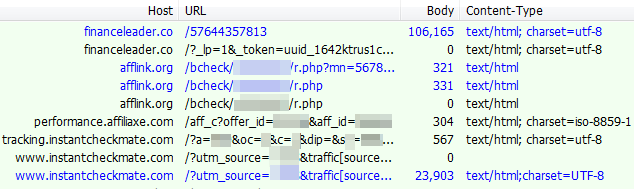
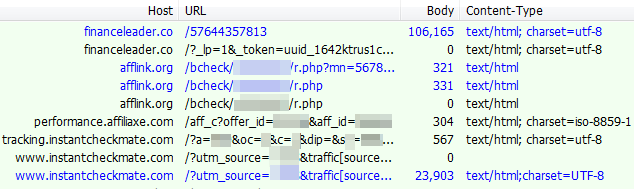
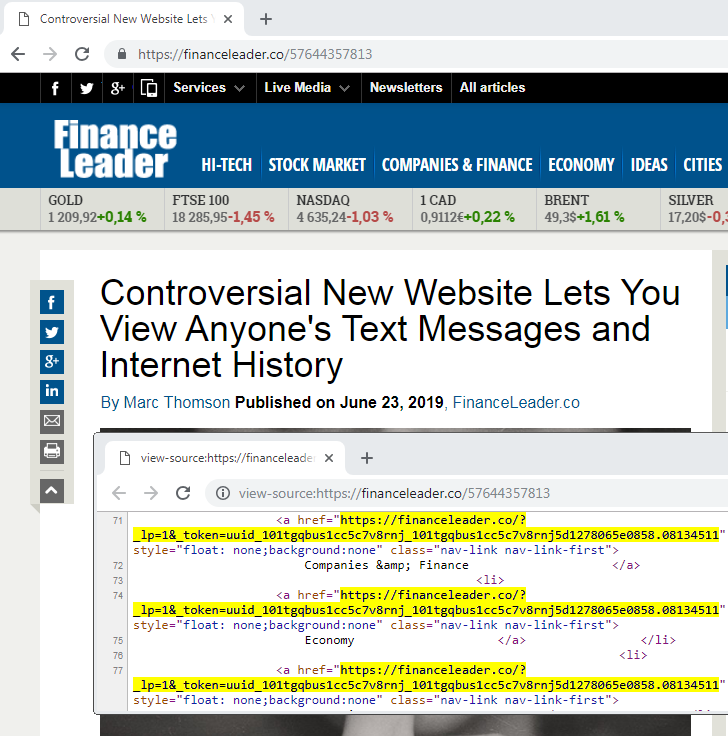
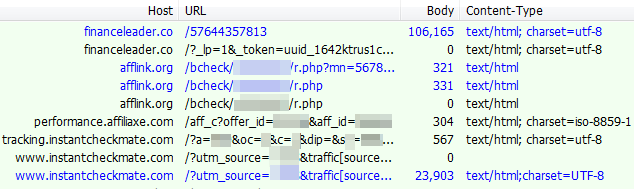
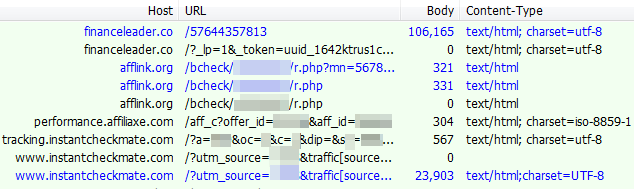
There is some geo-targeting involved for the redirections and clearly desktop users do not appear to be the primary focus here. From a US IP address, you are presented with a bogus site where all items point to the same link that redirect you to instantcheckmate[.]com.
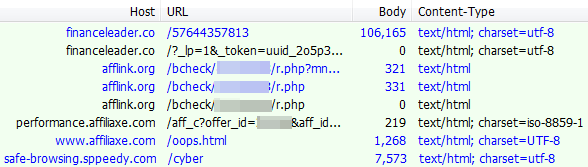
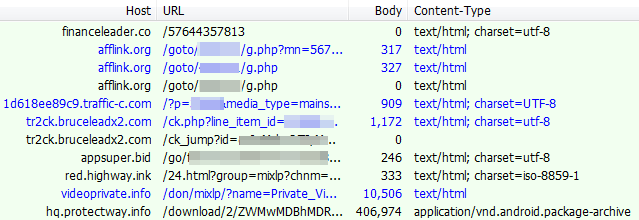
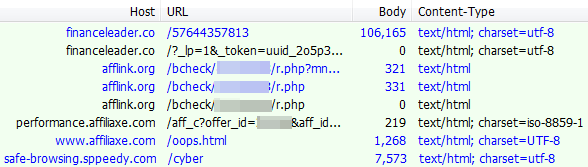
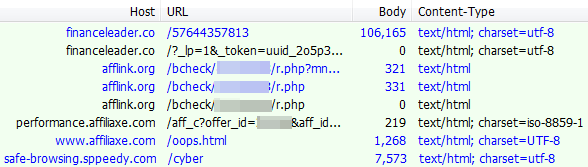
Associated web traffic:
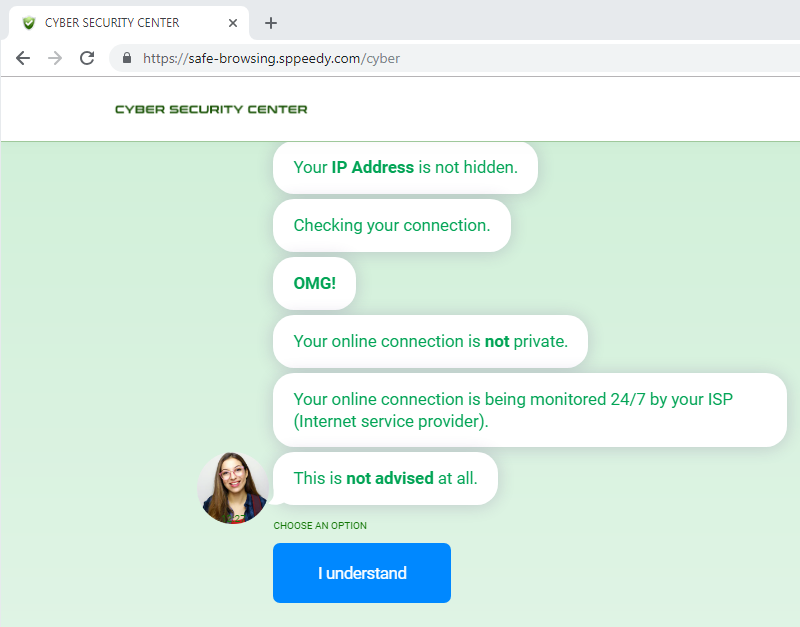
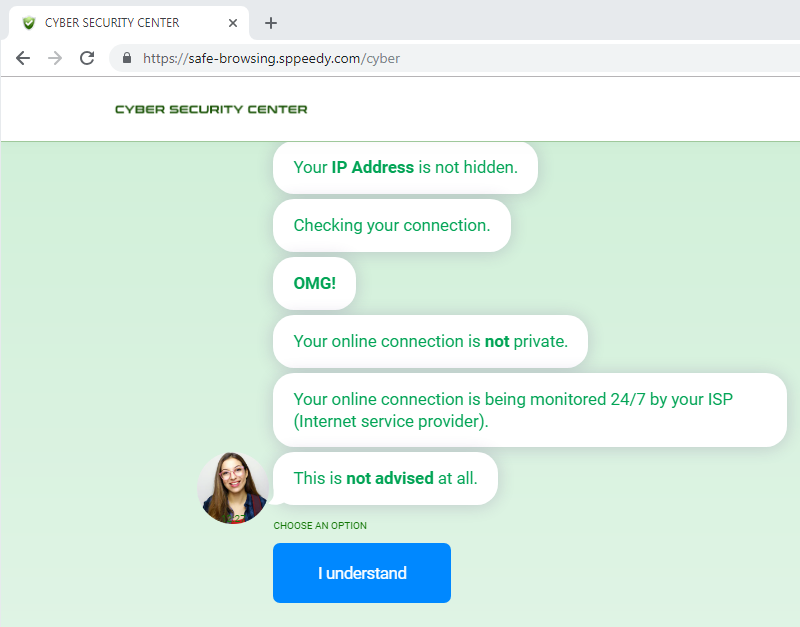
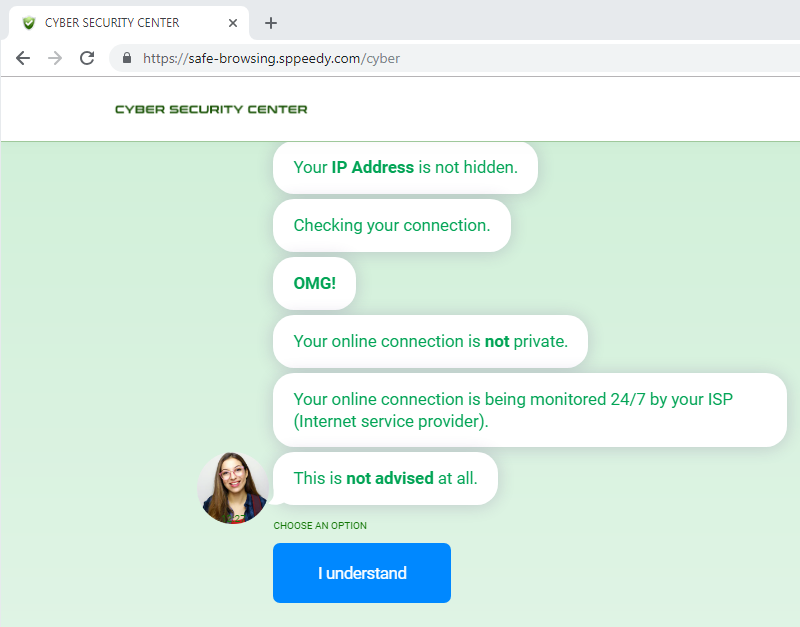
From a non US IP, you are redirected to a page that aggressively advertises VPNs:
Associated web traffic:
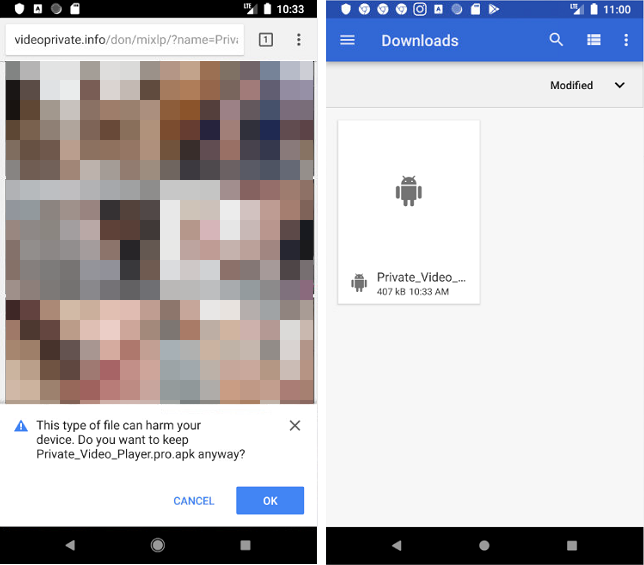
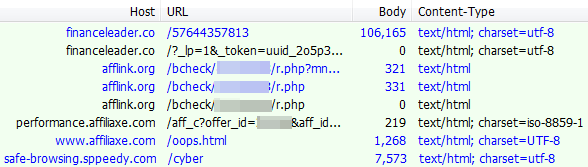
Mobile web traffic
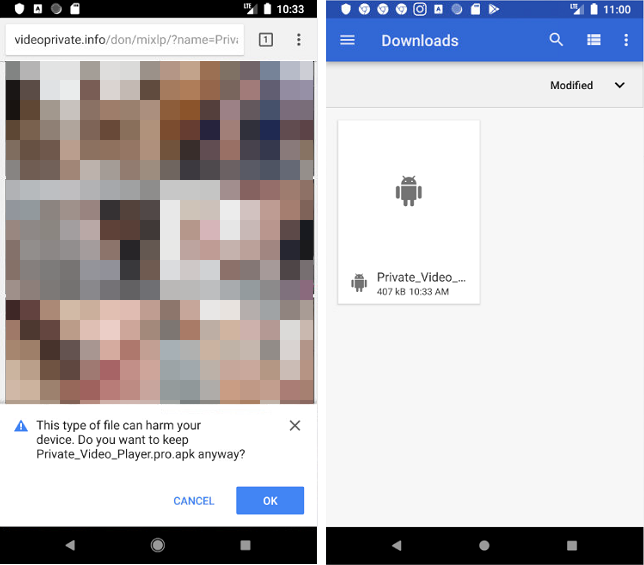
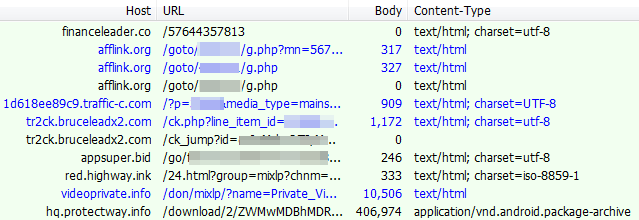
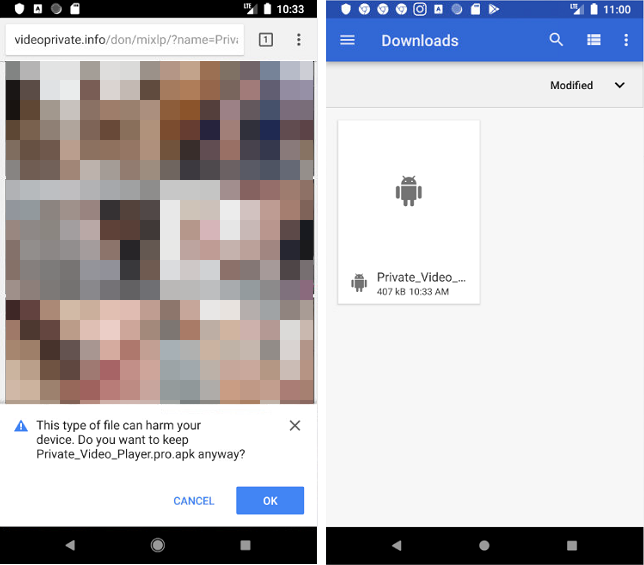
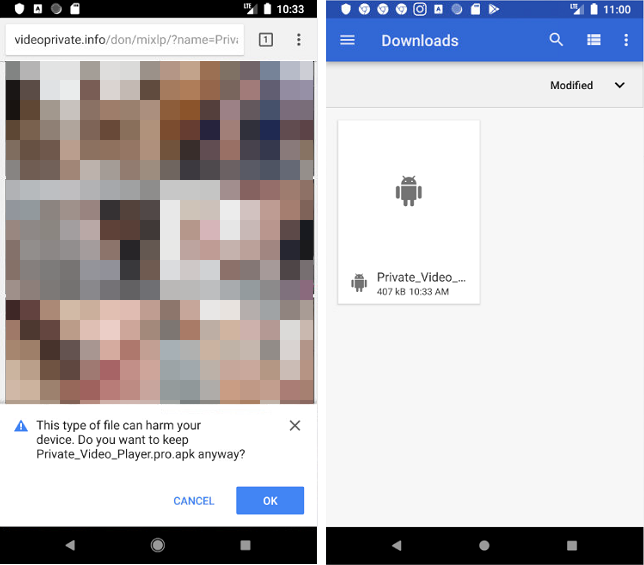
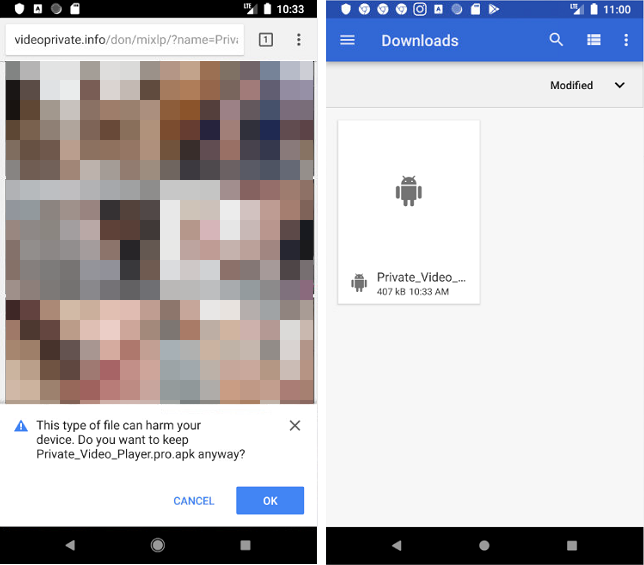
Once we switch to a mobile User-Agent and Android in particular, we can see a lot more activity and a variety of redirects. For example in one case, we were served a bogus adult site that requires users to download an app in order to play the videos:
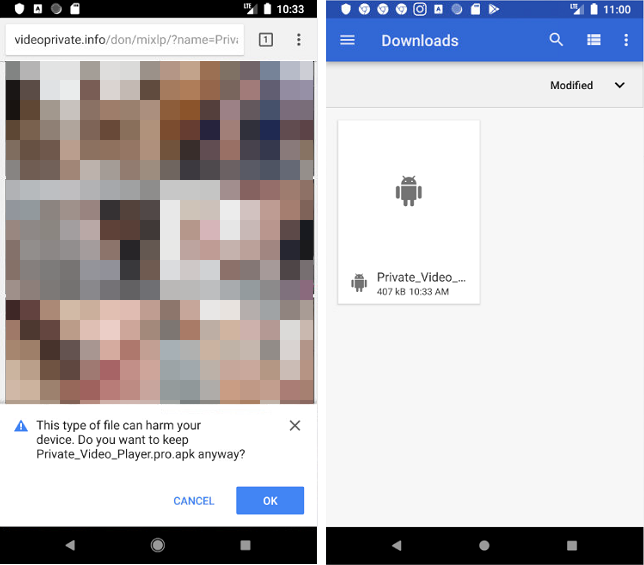
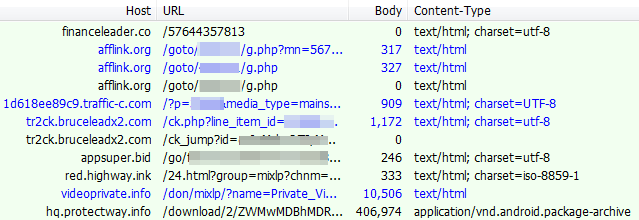
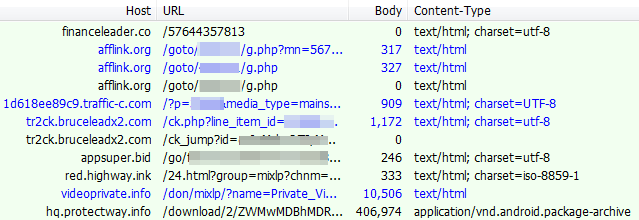
Associated web traffic:
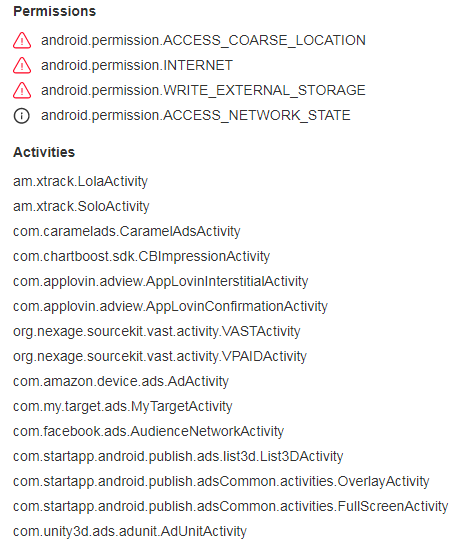
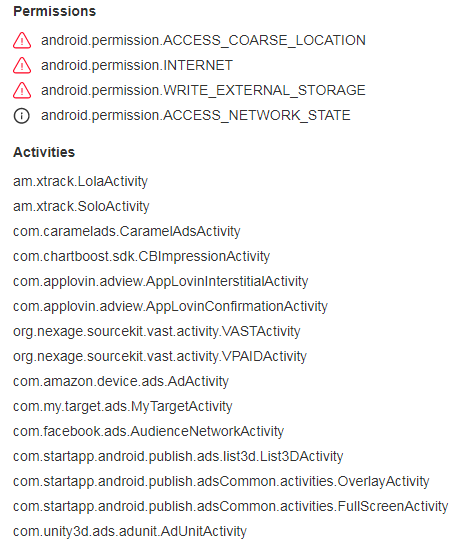
This app is malicious (detected as Android/Trojan.HiddenAds.xt by Malwarebytes) and will generate full screen ads at regular intervals.
Traffic monetization and ad fraud
While we encountered some desktop traffic, we believe the primary goal of the fake jquery campaign is to monetize from mobile users. This would explain the level of filtering involved to hide non-qualified traffic.
We weren’t able to get an idea of the scale at play, especially considering that the domain initiating the redirects really only became active in late May. However, given the number of websites that have been compromised, this campaign is quite likely funneling a significant amount of traffic leading to ad fraud.
Malwarebytes users are protected against this campaign both on desktop and mobile.
Indicators of Compromise
Fake jquery domains:
12js[.]org
16js[.]org
22js[.]org
lib0[.]org
16lib[.]org
12lib[.]org
wp11[.]org
Redirects:
financeleader[.]co
afflink[.]org
Malicious APKs:
0e67fd9fc535e0f9cf955444d81b0e84882aa73a317d7c8b79af48d91b79ef19 a210c9960edc5362b23e0a73b92b4ce4597911b00e91e7d3ca82632485c5e68d










