MegaCortex is a relatively new ransomware family that continues the 2019 trend of threat actors developing ransomware specifically for targeted attacks on enterprises. While GandCrab apparently shut its doors, several other bespoke, artisanal ransomware families have taken its place, including RobinHood, which shut down the city of Baltimore, Troldesh, and CrySIS/Dharma.
Detected by Malwarebytes as Ransom.MegaCortex, MegaCortex saw a spike in business detections in late May and has since slowed down to a trickle, following a similar trend as its Troldesh and CrySIS forebearers.
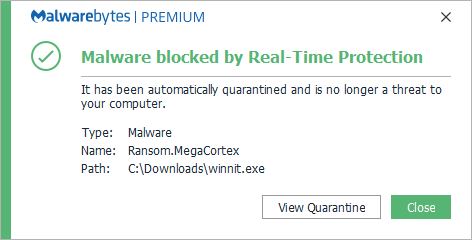
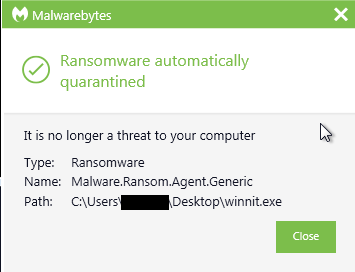
Our anti-ransomware technology detected Ransom.MegaCortex even before defintions were added.
Distribution
The methods of distribution for MegaCortex are still not completely clear, but there are indications that the ransomware is dropped on compromised computers by using Trojan downloaders. Once a corporate network has been compromised, the attackers try to gain access to a domain controller and spread across the entire network from there.
Suspected Trojans that might be responsible for the distribution of MegaCortex are Qakbot aka Qbot, Emotet, and Rietspoof. Rietspoof is a multi-stage malware that spreads through instant messaging programs.
Execution
Before the actual ransomware process starts, several tools and scripts are deployed to disable certain security processes and attempt to gain access to the domain controller so the ransomware can be distributed across the network.
Once the ransomware process is activated, it creates these files:
- ********.log
- ********.tsv
- ********.dll
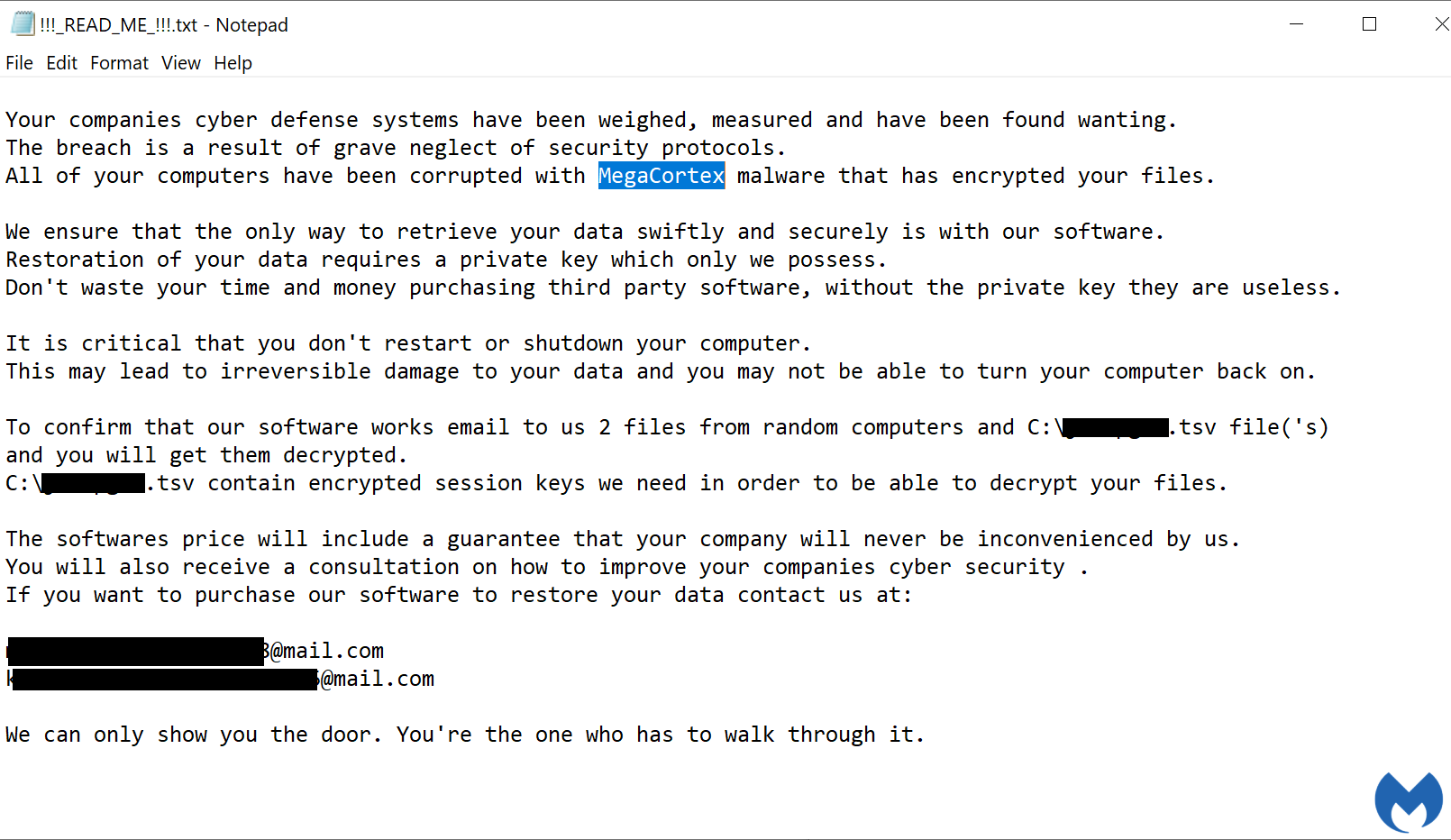
The ******** are eight random characters that are identical for the three files on the affected system. These names are also mentioned in the ransom note called !!!_READ_ME_!!!.txt.
The ransom note, the log file, and the tsv file are all located in the root drive. The dll, on the other hand, can be found in the %temp% folder.
The encrypted files are given the extension .aes128ctr. The encryption routine skips files with the extensions:
- .aes128ctr
- .bat
- .cmd
- .config
- .dll
- .exe
- .lnk
- .manifext
- .mui
- .olb
- .ps1
- .sys
- .tlb
- .tmp
The routine also skips the files:
- desktop.ini
- ********.tsv
- ********.log
It also skips all the files and subfolders under %windir%, with the exception of %windir%temp. In addition, MegaCortex deletes all the shadow copies on the affected system.
After the encryption routine is complete, MegaCortex displays this rather theatrical ransom note, high on drama and low on grammatical correctness.
Remarkable ransom note quotes
Some notable quotes from the ransom note:
- “All of your computers have been corrupted with MegaCortex malware that has encrypted your files.” So the name MegaCortex comes from the threat actors themselves, as opposed to the security researchers who discovered it. (That is one way to help the industry to use a unified detection name.)
- “It is critical that you don’t restart or shutdown your computer.” This implies that one of the seeds for the encryption routine will be made irretrievable if the computer gets rebooted.
- “The software price will include a guarantee that your company will never be inconvenienced by us.” Is this a tell-tale sign about how much granular control the threat actors have over the malware attacks, or just another empty promise made by criminals?
- “We can only show you the door. You’re the one who has to walk through it.” A reference to The Matrix or a failed fiction writer?
The ransom note also makes clear that the information necessary for the decryption routine is contained in the randomly named tsv file. So, if all the information except the private key is on the infected computer, does that mean there will be a free decryptor soon? That depends on many other factors, but if the cybercriminals used the same private key for each infection, there could be a possible escape on the horizon.
Undoubtedly it will take some reverse engineering to get definitive answers to these questions, but it certainly gives us some clues.
Countermeasures
Given that the exact infection vector is as of yet unknown, it is hard to give specific protection advice for this ransomware family. But there are some countermeasures that always apply to ransomware attacks, and they might be useful to repeat here:
- Scan emails with attachments. Suspicious mails with attachments should not reach the end user without being checked first.
- User education. Users should be taught to refrain from downloading attachments sent to them via mail or instant messaging without close scrutinization.
- Blacklisting. Most endpoints do not need to be able to run scripts. In those cases, you can blacklist wscript.exe and maybe other scripting options like Powershell.
- Update software and systems. Updating your systems and your software can plug up vulnerabilities and keep known exploits at bay.
- Back up files. Reliable and easy-to-deploy backups can shorten the recovery time.
We are far from knowing everything there is to know about this ransomware, but as we discover new information, we will keep our blog readers updated. In the meantime, it is imperative for enterprises to employ best practices for protecting against all ransomware.
After all, we can only show you the door. You’re the one who has to walk through it.
Stay safe, everyone!