Note: The developers of NITE Team 4 granted the blog author access to the game plus DLC content.
A little while ago, an online acquaintance of mine asked if a new video game based on hacking called NITE Team 4 was in any way realistic, or “doable” in terms of the types of hacking it portrayed (accounting for the necessary divergences from how things would work outside of a scripted, plot-goes-here environment).
The developers, AliceandSmith, generously gave me a key for the game, so I’ve spent the last month or so slowly working my way through the content. I’ve not completed it yet, but what I’ve explored is enough to feel confident in making several observations. This isn’t a review; I’m primarily interested in the question: “How realistic is this?”
What is it?
NITE Team 4 is an attempt at making a grounded game focused on a variety of hacking techniques—some of which researchers of various coloured hats may (or may not!) experience daily. It does this by allowing you full use of the so-called “Stinger OS,” their portrayal of a dedicated hacking system able to run queries and operate advanced hacking tools as you take the role of a computer expert in a government-driven secret organisation.
Is it like other hacking games?
Surprisingly, it isn’t. I’ve played a lot of hacking games through the years. They generally fall into two camps. The first are terrible mini-games jammed into unrelated titles that don’t have any resemblance to “hacking” in any way whatsoever. You know what I’m talking about: They’re the bits flagged as “worst part of the game” whenever you talk to a friend about any form of digital entertainment.
The second camp is the full-fledged hacking game, the type based entirely around some sort of stab at a hacking title. The quality is variable, but often they have a specific look and act a certain way.
Put simply, the developers usually emigrate to cyberpunk dystopia land and never come back. Every hacker cliché in the book is wheeled out, and as for the actual hacking content, it usually comes down to abstractions of what the developer assumes hacking might be like, rather than something that it actually resembles.
In other words: You’re not really hacking or doing something resembling hacking. It’s really just numbers replacing health bars. Your in-game computer is essentially just another role-playing character, only instead of a magic pool you have a “hacking strength meter” or something similar. Your modem is your stamina bar, your health bar is replaced by something to do with GPU strength, and so on.
They’re fun, but it’s a little samey after a while.
Meanwhile, in NITE Team 4: I compromised Wi-Fi enabled billboards to track the path of the potentially kidnapped owner of a mobile phone.
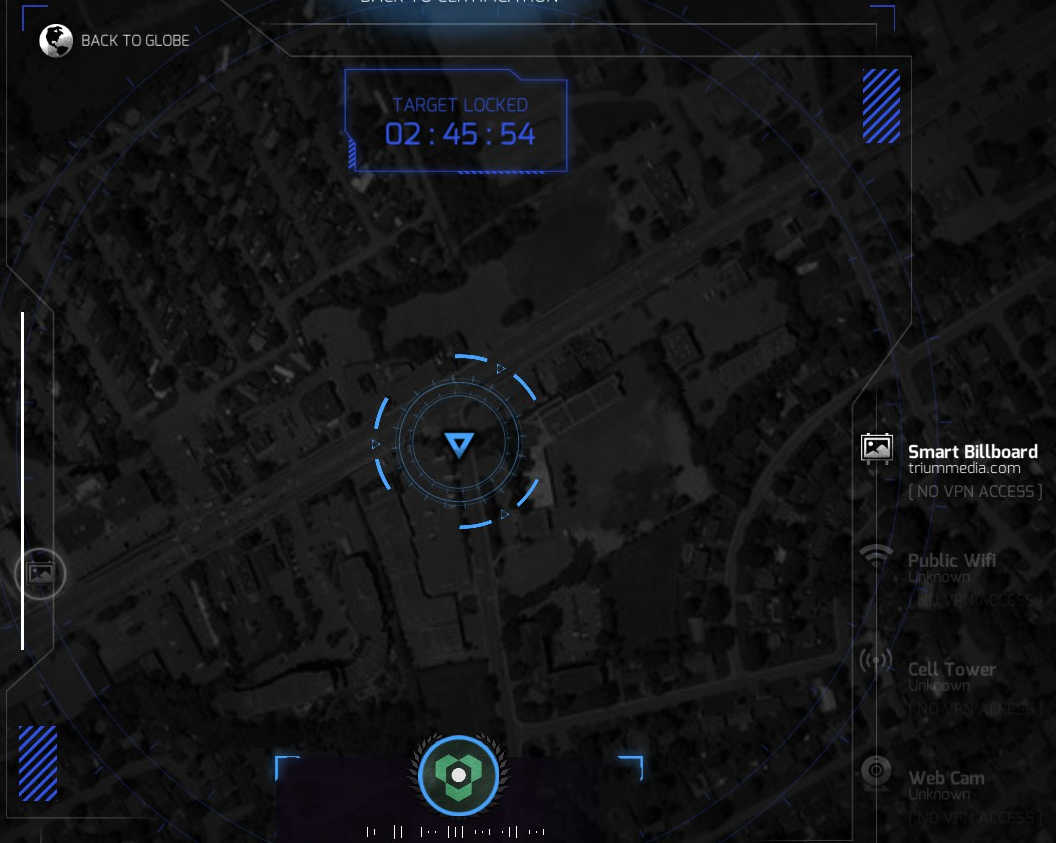
Click to enlarge
I used government tools to figure out the connection between supposedly random individuals by cross referencing taxi records and payment stubs. I figured out which mobile phone a suspect owns by using nearby Wi-Fi points to build a picture of their daily routine.
Click to enlarge
I made use of misconfigured server settings to view ID cards belonging to multiple companies looking for an insider threat.
I performed a Man-in-the-Middle attack to sniff network traffic and made use of the Internet of Things to flag a high-level criminal suspect on a heatmap.

Click to enlarge
If it sounds a little different, that’s because it is. We’re way beyond the old “Press H to Hack” here.
Logging on
Even the title screen forced me to weigh up some serious security choices: Do I allow the terminal to store my account username and password? Will there be in game repercussions for this down the line? Or do I store my fictitious not-real video game login in a text file on my very-real desktop?

Click to enlarge
All important decisions. (If you must know, I wrote the password on a post-it note. I figure if someone breaks in, I have more pressing concerns than a video game login. You’re not hacking my Gibson, fictitious nation state attackers).
Getting this show on the road
Your introduction to digital shenanigans isn’t for the faint of heart. As with many games of this nature, there’s a tutorial—and what a tutorial.
Spread across three sections covering basic terminal operations, digital forensics, and network intrusion, there’s no fewer than 15 specific tutorials, and each of those contains multiple components.
I can’t think of any other hacking-themed game where, before I could even consider touching the first mission, I had to tackle:
Basic command line tools, basic and advanced OSINT (open source intelligence), mobile forensics, Wi-Fi compromise, social engineering via the art of phishing toolkits, MiTM (Man in the Middle), making use of exploit databases, and even a gamified version of the infamous NSA tool Xkeyscore.
When you take part in a game tutorial that suggests users of Kali and Metasploit may be familiar with some aspects of the interface, or happily links to real-world examples of tools and incidents, you know you’re dealing with something that has a solid grounding in “how this stuff actually works.”

Click to enlarge
In fact, a large portion of my time was spent happily cycling through the tutorial sections and figuring out how to complete each mini objective. If you’d told me the entire game was those tutorials, I’d probably have been happy with that.
What play styles are available?
The game is fairly aligned to certain types of Red Team actions, primarily reconnaissance and enumeration. You could honestly just read an article such as this and have a good idea of how the game is expected to pan out. Now, a lot of other titles do this to some degree. What’s novel here is the variety of approaches on offer to the budding hacker.
There are several primary mission types: The (so far) four chapter long main mission story, which seems to shape at least certain aspects based on choices made earlier on. This is where the most…Hollywood?…aspects of the story surrounding the hacking seem to reside. In fairness, they do assign a “real life” rating to each scenario and most of them tend to err on the side of “probably not happening,” which is fair enough.
The second type of mission is the daily bounties, where various government agencies offer you rewards for hacking various systems or gathering intel on specific targets. I won’t lie: The interface has defeated me here, and I can’t figure out how to start one. It’s probably something incredibly obvious. They’ll probably make me turn in my hacker badge and hacker gun.
Last of all—and most interesting—are the real world scenarios. These roughly resemble the main missions, but with the added spice of having to leave the game to go fact finding. You may have to hunt around in Google, or look for clues scattered across the Internet by the game developers.
Each mission comes with a briefing document explaining what you have to do, and from there on in, it’s time to grab what information you can lying around online (for real) and pop your findings back into the game.
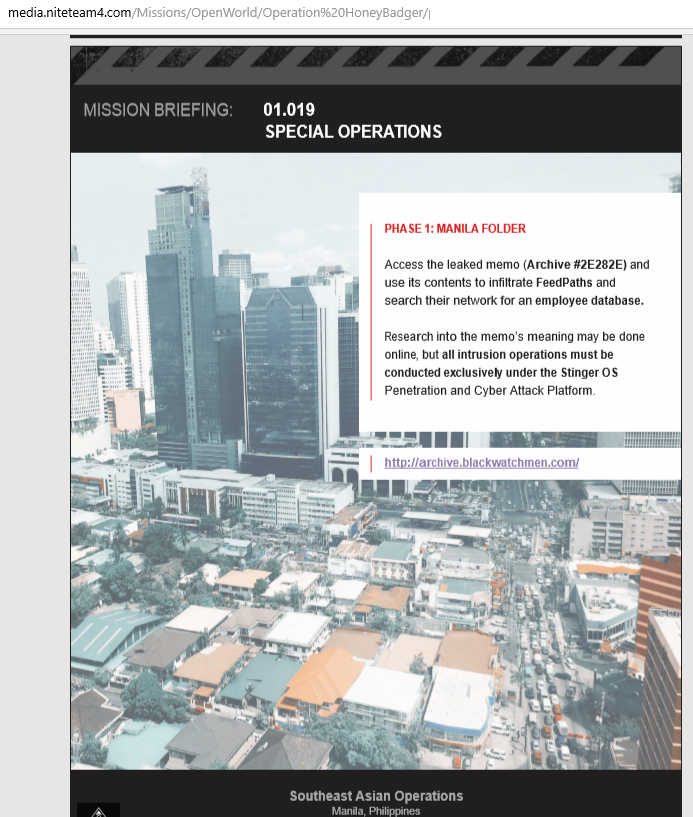
Click to enlarge
In keeping with the somewhat less Hollywood approach, the tasks and mission backgrounds are surprisingly serious and the monthly releases seem to follow “what if” stories about current events.
They deal with everything from infiltrating Emannuel Macron’s files (topical!) to tackling methamphetamine shipments in South Korea, and helping to extract missing journalists investigating the internment of religious minorities in China. As I said…surprisingly serious.
Getting your gameface on
Most tasks begin by doing what you’d expect—poking around on the Internet for clues. When hackers want to compromise websites or servers, they often go Google Dorking. This is essentially hunting round in search engines for telltale signs of passwords, or exposed databases, or other things a website or server should keep hidden, but the admin hasn’t been paying enough attention.
The idea in NITE Team 4 is to rummage around for subdomains and other points of interest that should’ve been hidden from sight and then exploit them ruthlessly. Different combinations of search and different tools provided by Stinger OS produce different results.
Once you have half a dozen subdomains, then you begin to fingerprint each one and check for vulnerabilities. As is common throughout the game, you don’t get any sort of step-by-step walkthrough on how to break into servers for real. Many key tasks are missed out because it probably wouldn’t make for an interesting game, and frankly there’s already more than enough here to try and figure out while keeping it accessible to newcomers.
Should you find a vulnerable subdomain, it’s then time to run the custom-made vulnerability database provided by Stinger OS, and then fire up the compromise tool (possibly the most “gamey” part of the process) that involves dragging and dropping aspects of the described vulnerability into the hacking tool and breaking into the computer/server/mobile phone.
From there, the mission usually diverges into aspects of security not typically covered in games. If anything, the nuts and bolts terminal stuff is less of a focus than working out how to exploit the fictitious targets away from your Stinger terminal. It feels a lot more realistic to me as a result.
What else can you do?
Before long, you’ll be trying various combinations of data about targets, and their day-to-day life, in the game’s XKeyscore tool to figure out patterns and reveal more information.

Click to enlarge
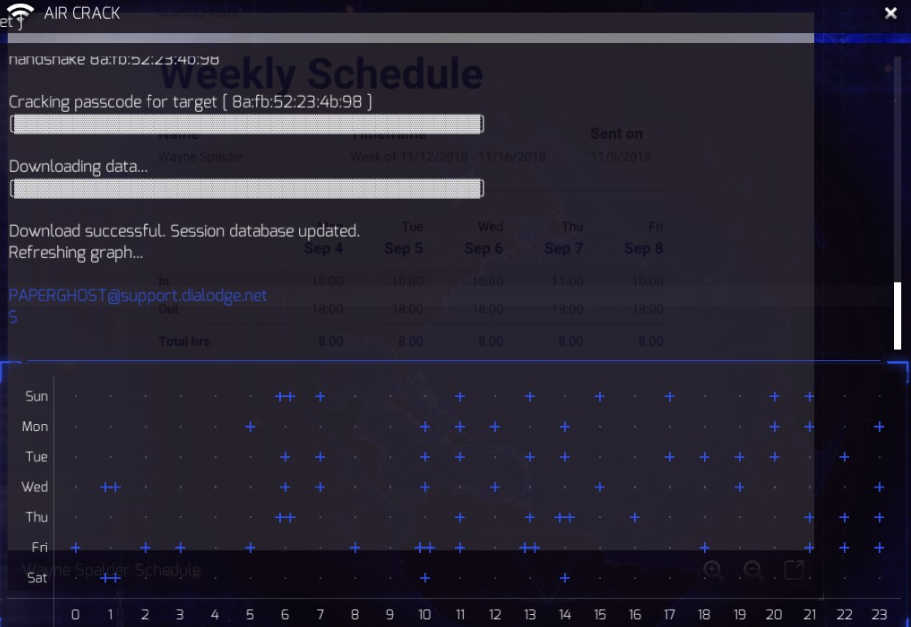
You’ll be using one of your VPNs to access a compromised network and use several techniques to crack a password. Maybe you won’t need to do that at all, because the target’s phone you just compromised has the
password in plaintext in an SMS they sent their boss. What will you do if the password isn’t a password, but a clue to the password?
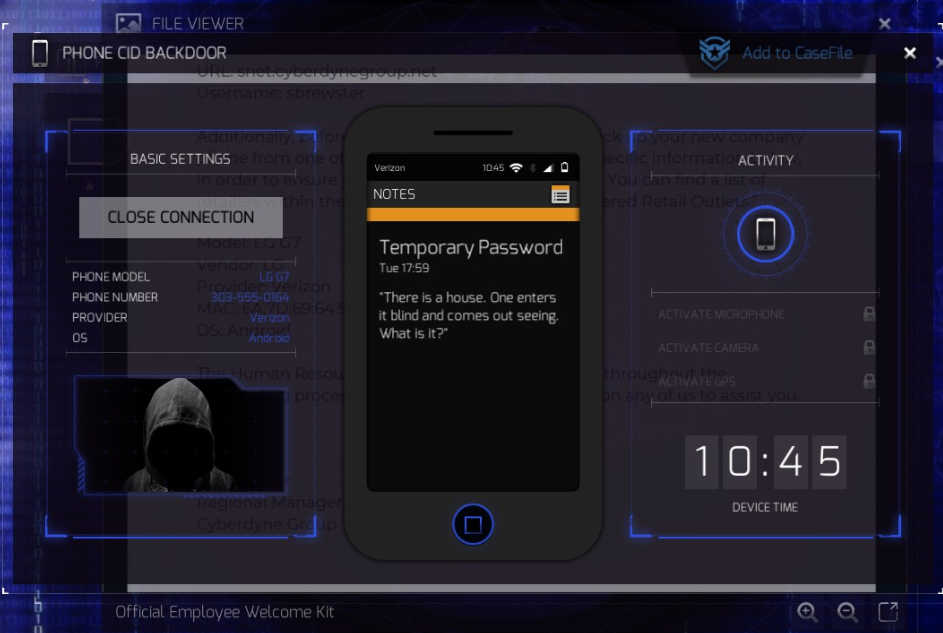
Click to enlarge
Once obtained, it might help reveal the location of a rogue business helping an insider threat hijack legitimate networks. How will you take them down? Will you try and break into their server? Could that be a trap? Perhaps you grabbed an email from the business card you downloaded. Is it worth firing up the phishing toolkit and trying to craft a boobytrapped email?

Click to enlarge
Would they be more likely to fall for a Word document or a Flash file? Should the body text resemble an accounting missive, or would a legal threat be more effective?
I hear those IoT smart homes are somewhat vulnerable these days. Anyone for BBQ?

Click to enlarge
…and so on.
I don’t want to give too much away, as it’s really worth discovering these things for yourself.
Hack the planet?
I mentioned earlier that I’d have been happy with just the tutorials to play around in. You’re not going to pop a shell or steal millions from a bank account by playing this game because ultimately it’s just that—a game. You’re dropped into specific scenarios, told to get from X to Y, and then you’re left to your own devices inside the hacker sandbox. If you genuinely want to try and tackle some of the basics of the trade, you should talk to security pros, ask for advice, go to conferences, take up a few courses, or try and grab the regular Humble Hacking Bundles.
Occasionally I got stuck and couldn’t figure out if I was doing something wrong, or the game was. Sometimes it expected you to input something as it presented it to you but didn’t mention you’d need to leave off the “/” at the end. Elsewhere, I was supposed to crack a password but despite following the instructions to the letter, it simply wouldn’t work—until it did.
Despite this, I don’t think I’ve played a game based on hacking with so many diverse aspects to it.
Bottom line: Is it realistic?
The various storyline scenarios are by necessity a little “out there.” You’re probably not going to see someone blowing up a house in Germany via remote controlled Hellfire missile strike anytime soon. But in terms of illustrating how many tools people working in this area use, how they use lateral thinking and clever connections to solve a puzzle and get something done, it’s fantastic. There are multiple aspects of this—particularly where dealing with OSINT, making connections, figuring out who did what and where are concerned—that I recognise.
While I was tying up this blog post, I discovered the developers are producing special versions of it for training. This doesn’t surprise me; I could imagine this has many applications, including making in-house custom security policy training a lot more fun and interesting for non infosec employees.
Is this the best hacking game ever made? I couldn’t possibly say. Is it the most fleshed out? I would say so, and anyone looking for an occasionally tricky gamified introduction to digital jousting should give it a look. I’d have loved something like this when I was growing up, and if it helps encourage teenagers (or anyone else, for that matter) to look at security as a career option, then that can only be a bonus.










