Since late last year, our researchers have been monitoring new methods being deployed by cybercriminals to potentially abuse browser push notifications. Now, an adware family detected by Malwarebytes as Adware.Adposhel is doing just that, taking control of push notifications in Chrome at the administrator level.
What does Adposhel adware do?
The adware uses Chrome policies to ensure that notification prompts will be shown to users ands add some of its own domains to the list of sites that are allowed to push browser notifications. So far nothing new. The recent twist, however, is that Adposhel enforces these settings as an administrator, meaning a regular Chrome user will not be able to change the settings in the notifications menu.
It seems the adware family has now decided to fully deploy this tactic, as we are seeing complaints about it emerging on forums, such as Reddit.
Victims have complained about being unable to remove domains from the list of domains that are allowed to show push notifications, and being unable to change the setting that control whether websites can ask you to allow notifications.

Disabling that setting would stop a user from seeing prompts like these:
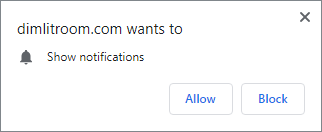
If a user were to click Allow on that prompt, this domain would be added to their allowed list of URLs, with the understanding that it could be removed manually in the notifications menu.
Adposhel uses the NotificationsAllowedForUrls policy to block users from removing their entries from the Allow list.
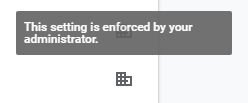
Where you would normally see the three dots (ellipsis) menu icon representing the settings menu, entries submitted to a policy by Adposhel will see an icon telling you the setting is enforced by an administrator.
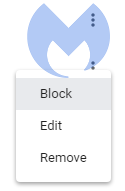
If you hover over the icon, the accompanying text confirms it.
How do I undo the changes made by Adposhel adware?
This does not mean that you can change that setting just because you are the administrator of the system you are working on, by the way. But if you are the system administrator, you can fix the notification changes made by the Adposhel installer by applying a simple registry fix:
Windows Registry Editor Version 5.00 [HKEY_LOCAL_MACHINESOFTWAREPoliciesGoogleChrome] "DefaultNotificationsSetting"=dword:00000001 [-HKEY_LOCAL_MACHINESOFTWAREPoliciesGoogleChromeNotificationsAllowedForUrls] This is safe to do unless there were legitimate URLs in the list of URLs that were allowed to show notifications by policy, which I doubt. But we always advise to create a backup of the registry before making any changes.
Backing up Registry with ERUNT
Modifying the registry may create unforeseen results, so we always recommend creating a backup prior to doing that.
Please download ERUNT and save the file to the desktop.
- Install ERUNT by following the prompts, but say No to the portion that asks you to add ERUNT to the startup folder.
- Right-click on the icon and select Run as Administrator to start the tool.
- Leave the default location (C:WINDOWSERDNT) as a place for your backup.
- Make sure that System registry and Current user registry are ticked.
- The third option Other open users registries is optional.
- Press OK to backup and then press YES to create the folder.
This tool won’t generate a report. You may uninstall it after you’re done cleaning.
Protection and detection
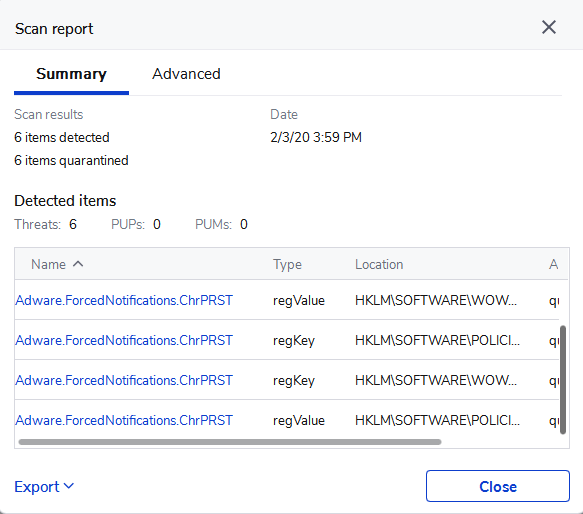
Malwarebytes detects the installers as Adware.Adposhel.
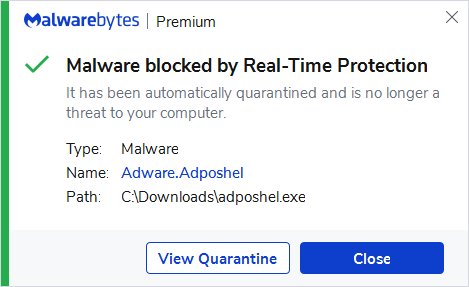
The URLs enforced by this Adpohel-induced Chrome policy are detected as Adware.ForcedNotifications.ChrPRST.
IOCs
Domains:
aclassigned.info chainthorn.com cityskyscraper.com concreasun.info dimlitroom.com durington.info efishedo.info enclosely.info insupposity.info nineteducer.info oncreasun.info parliery.info qareaste.info stilysee.info suggedin.info Stay safe, everyone!











