The IT security researchers at AdaptiveMobile have called out what looks like an important vulnerability in the architecture of 5G network slicing and virtualized network functions. They warn that the risks, if this fundamental vulnerability in the design of 5G standards had gone undiscovered, are significant.
What is 5G?
5G is the 5th generation mobile network. It is the fifth new global wireless standard after (you’ll never guess) 1G, 2G, 3G, and 4G. 5G enables a new kind of network that is designed to connect virtually everyone and everything together, including machines, objects, and devices. 5G is based on OFDM (Orthogonal frequency-division multiplexing), a method of modulating a digital signal across several different channels to reduce interference.
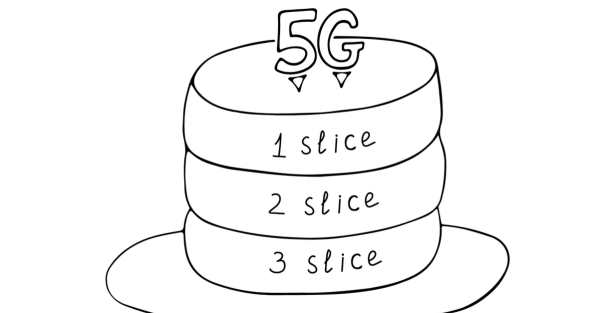
What is 5G network slicing?
5G network slicing is a network architecture that enables the multiplexing of virtualized and independent logical networks on the same physical network. Basically, the actual 5G network is compartmentalized into multiple virtual networks that function independently.
This allows the infrastructure providers to divide their network up into several independent ones for separate mobile network operators. A mobile operator can create specific virtual networks that cater to different clients and use cases.
The vulnerability
Network functions are services available within a network, and in 5G they can be dedicated to single slice, or shared between multiple slices. AdaptiveMobile Security looked at 5G networks that contain both shared and dedicated network functions.
What it learned was that when a network has network functions that support several slices there is a lack of mapping between the application and transport layers identities, which allows rogue slices to do more than they are allowed. The separate networks were not as separate as they should be.
The fundamental vulnerability has the potential to allow data access and denial of service attacks between different network slices on a mobile operator’s network.
5G networks are complex, and so are the attacks. AdaptiveMobile sets out a few examples in its report, but the easiest to explain is an example of a Denial of Service (DoS) attack.
Imagine a network carved into two slices that can both have access to the same shared network function (“the shared service”). We’ll call the slices “Victim” and “Aggressor”, just to make it really obvious! In our example, the Aggressor network slice is under the control of a rogue operator who wants to run a DoS attack against the Victim network slice.
In simple terms, the Aggressor slice sends a message to the shared service, claiming that it is the Victim slice, and that it’s overloaded and does not want to receive any communication from the shared service, thereby denying that service to Victim.
The attack works because although the shared service checks that the Aggressor slice is permitted to speak to it (correctly), it does not have to check that the messages it sends actually relate to it and not a different one.
Or, as the report puts it:
Currently, there is no requirement in the 3GPP specifications to validate if the slice identity in the 3GPP-Sbi-Oci header matches the slice identity in the token for the service API usage.
How can this be abused?
According to AdaptiveMobile, an attacker could gain access to data and launch denial of service attacks across multiple slices if they have access to the 5G Service Based Architecture.
- The operator and their customers would be exposed and risk the loss of sensitive location data.
- Denial of service against another network function on the same network.
- Access to a network function and related information of another vertical customer.
Is there any real danger?
To pull off a successful attack you would have to get accepted as a mobile operator and get assigned a “slice” of the 5G network. Which would set you back by a significant amount. Probably a lot more than you could ever hope to gain by successfully exploiting the flaw. The only real and current danger would be if two competitors on the same network decided to spy on one another. Given the limited amount of network operators and the cost involved in becoming one, the danger to customers seems non-existent.
But, once a flaw has been found, there is a good chance more will follow, and it is better to expose these flaws than to discard them just because they are harmless now. Because, as the head of 5G Security Research at AdaptiveMobile Security, Dr. Silke Holtmanns, put it:
“Having brought this to the industry’s attention through the appropriate forums and processes, we are glad to be working with the operator and standards communities to highlight this issue and promote best practice going forward.”
In short, it’s good to be aware of existing vulnerabilities, but we have seen much more effective DoS attacks against 5G.