In traditional software development, programmers code an application in one computing environment before deploying it to a similar, but often slightly different environment. This leads to bugs or errors that only show up when the software is deployed—exactly when you need them least. To solve for this, modern developers often bundle their applications together with all of the configuration files, libraries, and other pieces of software required to run in it in “containers” hosted in the cloud. This method, called containerization, allows them to create and deploy the entire computing environment, so there are no unexpected surprises.
Because a lot of projects rely on many of the same dependencies, developers can get their projects off to a flying start by building on top of pre-configured container images, which can be downloaded from online image repositories like Docker Hub. Those images may in turn be built on top of other images, and so on. So, for example, developer building a plugin for the WordPress content management system might base their project on a container image containing WordPress, and that container might be built on top of another image that includes a web server and database, which may be built on a container image for a popular operating system, like Ubuntu.
Container images provide a simple way to distribute software at the expense of transparency.
Now imagine if a malicious actor could hide a crypto-jacker in a popular source image, one that might get used and reused thousands of times. They could end up with a huge number of systems mining cryptocurrency for them for free.
Docker images
Docker Hub is the world’s largest library and community for container images and therefore a very attractive target for attackers. Luckily, tampering with containers is not easy and Docker has a strong focus on “Trusted Delivery” which is supposed to guarantee an untampered app. But there is a lot more to be found in container images than just the app.
Uncovered by researchers
In the last several years, Unit 42 researchers have uncovered cloud-based crypto-jacking attacks in which miners are deployed using an image in Docker Hub. Containerization is almost always conducted in a cloud environment, because that contributes to its scalability—behind the scenes popular web applications or services often rely on huge numbers of identical containers. This has some advantages for the crypto-jackers:
- There are many instances for each target.
- It is hard to monitor, so miners can run undetected for a long time.
The researchers uncovered 30 images from 10 different Docker Hub accounts that accounted for over 20 million “pulls” (downloads).
The favorite cryptocurrency
The most popular cryptocurrency for attackers to mine is Monero. Monero is a cryptocurrency designed for privacy, promising:
“all the benefits of a decentralized cryptocurrency, without any of the typical privacy concessions”.
No cryptocurrency is anonymous, as many people think, but there are other reasons why the crypto-jackers favor Monero:
- Many crypto-mining algorithms run significantly better on ASICs or GPUs, but Monero mining algorithms run better on CPUs, which matches what the crypto-jacker can expect to find in a containerized environment.
- Besides Bitcoin, Monero is one of the better known cryptocurrencies and therefore is expected to hold its value.
Cryptocurrencies are pseudonymous at best, which means that users hide behind a pseudonym, like one or more wallet IDs. Their activities can be tracked—forever—so keeping their identity secret depends on how well they can separate their real identity from their wallet IDs.
XMRig
In most of the recorded attacks that mined Monero, the attackers used XMRig. XMRig is a popular Monero miner and is preferred by attackers because it is easy to use, efficient, and, most importantly, open source, which allows attackers to modify its code. In some images, the researchers found different types of cryptominers. Possibly to enable the attacker to choose the best crypto-miner for the victim’s hardware.
The consequences
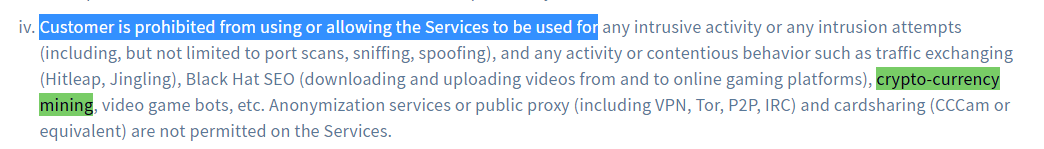
Not only will having a crypto-miner in your container lead to either a higher bill or lower performance, there could be other consequences too, because many cloud service providers explicitly forbid mining for cryptocurrencies.
Mitigation
Stopping crypto-jackers from taking advantage of popular images can be done at a few levels:
Image providers needs to perform regular checks against tampering, container repositories should monitor for irregularities, and cloud service providers can check outgoing connections for mining-related activity
Container users should avoid downloading containers from untrusted sources, scan images for malware at the build stage, check the integrity of images before and after copying them, and monitor runtime activity and network communication.
Since containers are just another way of arrange software stacks—including operating systems, applications and libraries—all the usual precautions apply too, such as patching vulnerabilities promptly.
Stay safe, everyone!











