Passwords are a hot topic on social media at the moment, due to the re-emergence of a discussion about good password management practices.
There’s a wealth of password management options available, some more desirable than others. The primary recommendation online is usually a software-based management tool. Some include online syncing alongside web browser extensions. Others involve syncing passwords with services such as Dropbox.
That’s before we get to the notepad on desktop aficionados, or the time-honoured tradition of the Post-It note on the office monitor. Today, we’re here to talk about perhaps the most controversial method of password storage though.
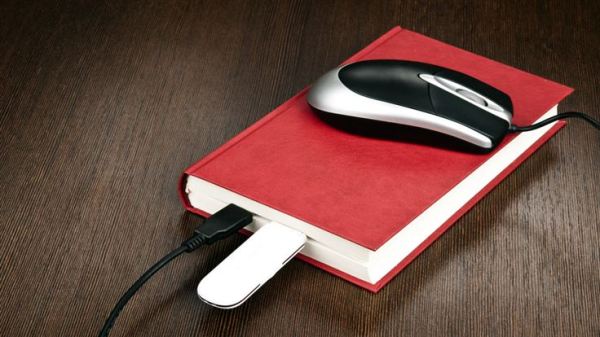
The big book of passwords
There’s one password management tool which experiences more than its fair share of derision—the oft-maligned Internet password book. These are, as you may expect, physical books which are little more than empty notepads with “Internet password book” written on the front. Some allow owners to group logins by category, or add additional notes as they see fit.
For various reasons, you’ll usually see them being rubbished on social media as the worst thing around for password management. It’s a passionate debate, and one which comes back to life every 6 months or so. The most recent bi-annual flurry of excitement was kicked off by BBC technology reporter Zoe Kleinman:
One important aspect of whether these books should be used at all is something called a threat model. If you’re hoping for a brief run down of what a threat model is, then great news…that’s exactly what we’re going to do.
Threat models
The best description I’ve seen of what threat modelling consists of, is in an article by Katie Nickels who says it’s “the process of figuring out what you have that adversaries care about”.
We don’t all face the same risks, and we don’t all need to take the same precautions as a result. When you see the latest sophisticated nation state attack in the news, it’s bad. But, like most people, you can probably go on as if nothing has happened. That clever spearphishing attack targeting a dozen or so individuals worldwide?
It’s targeting a dozen or so individuals worldwide.
You’ll never see it, and you almost certainly won’t receive messages from Google about it. It’s not in your threat model.
My personal security concerns are based around what’s important to me, what I want to secure, which bits I’m not bothered about, and what is absolutely mission critical at all costs. That’s my threat model.
Sizing up your adversary
You may not need to worry about nation state attacks, but you’ll almost certainly have something in place for the 600th fake tax return invoice landing in your mailbox. That’s an aspect of your threat model you know your business is up against, you know what they’re after, and you’ve put solutions in place to ward it off. It may or may not be the single most important threat your organisation faces…or it might be mid-tier. It will differ from place to place, and that’s fine.
What tends to happen when we see the infamous password book on display, is we apply a one-size-fits-all approach and dismiss it as silly or bad practice.
Well, it could definitely be sub-optimal for someone working with sensitive data. There’s far better ways for those individuals to secure their digital demands, in ways that scale up to the likely threats they face. On the other hand, there’s many people out there who the books will be a perfect fit for:
- People who are simply unfamiliar or uncomfortable with computers. This isn’t uncommon.
- Those with accessibility or cognitive issues.
- Folks who feel a lack of control at placing all their password eggs in one (digital) basket.
Password managers
The two pillars of bad password practices are reuse, and poor password selection. Software-based password managers are excellent tools for dealing with both problems, which is why they are so widely recommended. They are great for creating increasingly complex passwords all gated behind a variety of secure login methods. Everything from 2FA, to regional login lockouts are yours for the taking. That’s great! The more choice, the better.
Even so, many people won’t ever bother with password managers.
Maybe they’re overwhelmed for choice, or the tools they know of don’t meet specific operational requirements. Perhaps the tool they really want to use has no browser extension, or it’s offline only instead of syncing online. It’s also possible they may just find the whole thing too fiddly or complicated, or simply not know they exist.
Depending on OS, type of device, and feature set, something that should be easy can very easily become a chore. From there, bad habits can start to set in, including the eventual removal of the password manager. It’s then a short hop back to Password123.
Password management books: what works and what doesn’t
Some common objections to password books are as follows:
- If you lose the book while out and about, you’ve lost access to everything.
- Having to type in your passwords while reading them from a book, instead of having a password manager do it for you, could encourage people to use simple passwords instead of complex ones.
- Books become a form of abandonware over time, with missing entries, torn pages, logins which have been changed online and not updated, and other logins which never end up in the book at all.
The counters to these points are lengthy, so they get their own sections:
Loss or theft of a password book
Losing the book while outside the home isn’t that different from losing access to a password vault because of technical problems, forgotten master passwords, or other unforeseen happenings. In both cases, something has gone wrong. At least in the case of the book, it’s likely to be kept at home and is reliant on multiple real-world layers of physical security.
That’s much more reliable than “password management tool has their database broken into by anonymous criminals, and there’s nothing you can do about it”. If your home is burgled, you have bigger fish to fry than worrying about your logins. Also, realistically, burglars are looking for expensive items they can take and then sell on. They do not care about the password book in your clothes draw.
Password books: encouraging simple passwords?
Could books encourage simple passwords? It’s quite possible. Some may find it rather aggravating to hammer out dozens of complicated passwords from page to screen whenever they log in. In my experience, people writing passwords down tend to take more of an interest in making everything unique. After all, nobody is filling 30 pages of a password book with “password123”. What’s the point? Sure, we could end up with a variety of password1234/5/6 instead, but it’s still a bit more varied than the alternative.
I’ve also seen people write passwords only – not usernames or service / website on the pages. What they do instead, is associate certain pages with certain services. This is a great defence against theft or loss, but I’d be worried about forgetting the order. This is also a major negative if the book owner dies and family members need to attempt some form of data recovery. Where would you even begin?
Abandonware in paper format?
Abandonware books, what a concept. I think there’s some merit to this one, but I also think it offers a glimmer of hope. I know someone who did this, and what was happening was a slow transition to software password managers. If filling in some passwords in a book is the stepping-stone someone needs to feel more confident about moving logins to the PC, more power to them. It’s also possible some folks have typed out passwords from books so many times that they can remember the important ones anyway.
This concludes my lengthy counterpoint section.
Maybe they’re not the worst idea after all
The takeaway here is we’re dealing with an imperfect, messy solution for a messy, imperfect requirement to use our accounts. In situations where friends or relatives simply won’t entertain a password manager, it could be a decent (if not the only!) alternative. It really depends on the individual, and how safe it’ll be to drag their logins from screen to page. The password book won’t work for everybody, but it will definitely work for somebody and I think that’s perfectly fine.