Nobelium is a synthetic chemical element with the symbol No and atomic number 102. It is named in honor of Alfred Nobel. But it is also the name given to the threat actor that is behind the attacks against SolarWinds, the Sunburst backdoor, TEARDROP malware, GoldMax malware, other related components.
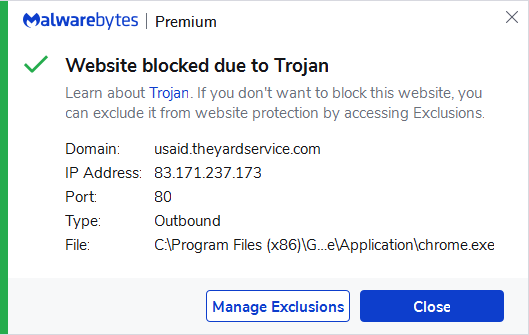
Microsoft Threat Intelligence Center (MSTIC) has issued a warning stating that it has uncovered a wide-scale malicious email campaign operated by NOBELIUM. In this campaign NOBELIUM leveraged the legitimate mass-mailing service Constant Contact. This allowed the threat actor to masquerade as a US-based development organization to distribute malicious URLs to a wide variety of organizations and industry verticals.
The campaign
This new wide-scale email campaign leverages the legitimate service Constant Contact to send malicious links that are disguised since they are obscured behind the mailing service’s URL. Many similar services use this type of mechanism to simplify the sharing of files while providing insights into by who and when links are clicked.
Finding the most effective delivery method
The early beginnings of these campaigns were first noticed January 28, 2021, when the actor was seemingly performing early reconnaissance by only sending the tracking portion of the email, leveraging Firebase URLs to record targets who clicked. Malicious payloads were not observed during this early activity.
In the next evolution of the campaign, MSTIC says it observed NOBELIUM attempting to compromise systems through an HTML file attached to a spear-phishing email. If a receiver opened the HTML attachment, embedded JavaScript code in the HTML wrote an ISO file to disc and encouraged the target to open it.
Similar spear-phishing campaigns were detected throughout March, which included the NOBELIUM actor making several alterations to the HTML document based on the intended target. MSTIC says it observed the actor encoding the ISO within the HTML document itself; redirecting from the HTML document to an ISO, which contained an RTF document, with the malicious Cobalt Strike Beacon DLL encoded within it; and replacing the HTML with a URL that led to a website that spoofed the targeted organization and hosted the ISO file.
The ISO payload
As we noted above, the payload is delivered via an ISO file. When ISO files are opened they are mounted much like an external or network drive. Threat actors may deploy a container into an environment to facilitate execution or evade defenses. And sometimes they will deploy a new container to execute processes associated with a particular image or deployment, such as processes that execute or download malware. In others, a threat actor may deploy a new container configured without network rules, user limitations, etc. to bypass existing defenses within the environment. In this case, a shortcut file (.lnk) would execute an accompanying DLL, which would result in a Cobalt Strike Beacon executing on the host. It is worth noting that the DLL is a hidden file. Cobalt Strike Beacons call out to the attacker’s infrastructure via port 443.
Experimenting with the payload
The delivery method was not the only evolving factor in the campaign. In one of the more targeted waves, no ISO payload was delivered, but additional profiling of the target device was performed by an actor-controlled web server after a user clicked the link. If the device targeted was an Apple iOS device, the user was redirected to another server under NOBELIUM control, where the since-patched zero-day exploit for CVE-2021-1879 was served.
During the waves in April, the threat actor stopped using Firebase, and no longer tracked users. Their techniques shifted to encoding the ISO inside the HTML document. Target host details were now stored by the payload on a remote server via the use of the api.ipify.org service. The threat actor would sometimes employ checks for specific internal Active Directory domains that would terminate execution of the malicious process if it identified an unintended environment.
The latest surge
On May 25, the NOBELIUM campaign was noticed to escalate significantly, attempting to target around 3,000 individual accounts across more than 150 organizations. Due to the high volume of emails distributed in this campaign, many automated email threat detection systems blocked most of the malicious emails and marked them as spam. However, some automated threat detection systems may have successfully delivered some of the earlier emails to recipients either due to configuration and policy settings or prior to detections being in place.
The goal
The successful deployment of the payload enables NOBELIUM to gain persistent access to the compromised machines. The successful execution of these malicious payloads would also enable NOBELIUM to conduct further malicious activity, such as lateral movement, data exfiltration, and delivery of additional malware.
Indiciators of compromise (IOCs)
In its warning, MSTIC provides a list of indicators of compromise from the large-scale campaign that launched on May 25, 2021. The organization notes that the attack is still active, these indicators should not be considered exhaustive for this observed activity.

Stay safe, everyone!