Social engineering attacks have been a longstanding concern for both individuals and organizations alike. The trend, as we know it, is that fraudsters conducting spear phishing attacks—specifically, business email compromise (BEC)—are likely to target employees either in the finance or executive teams of a company as they have authority over financial matters.
This has now changed.
According to Barracuda’s latest report entitled “Spear Phishing: Top Threats and Trends” [PDF], 77 percent of employees who are in roles considered as “low profile” are now favorite spear phishing targets. Some of these employees are members of IT, who receive an average of 40 phishing emails per year, and the sales department, who receive 1 in every 5 BEC phishing emails sent the company’s way.
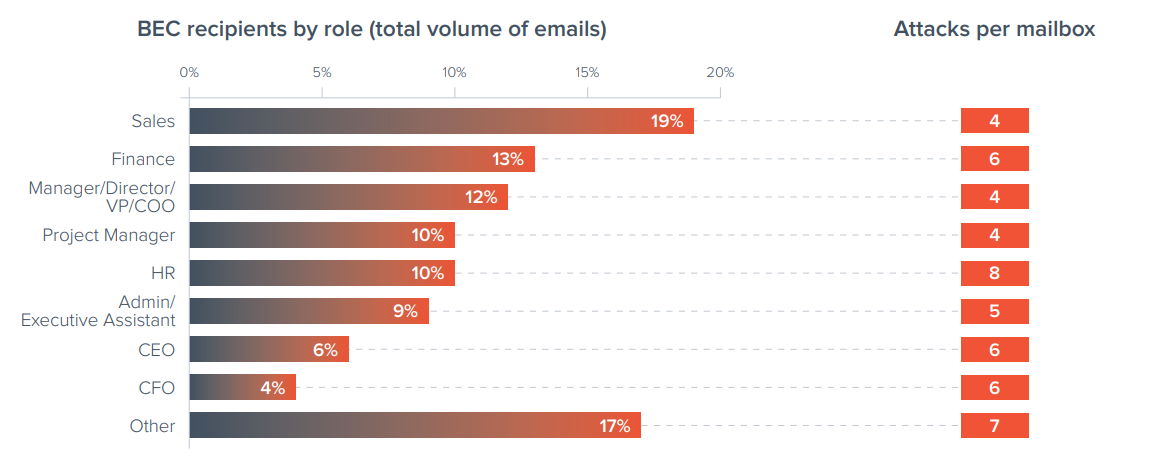
“Due to the nature of their role, sales reps are used to getting external messages from senders they haven’t communicated with before. At the same time, they are all connected with payments and with other departments including finance,” says the report. “For hackers, these individuals could be a perfect entry point to get into an organization and launch other attacks.”
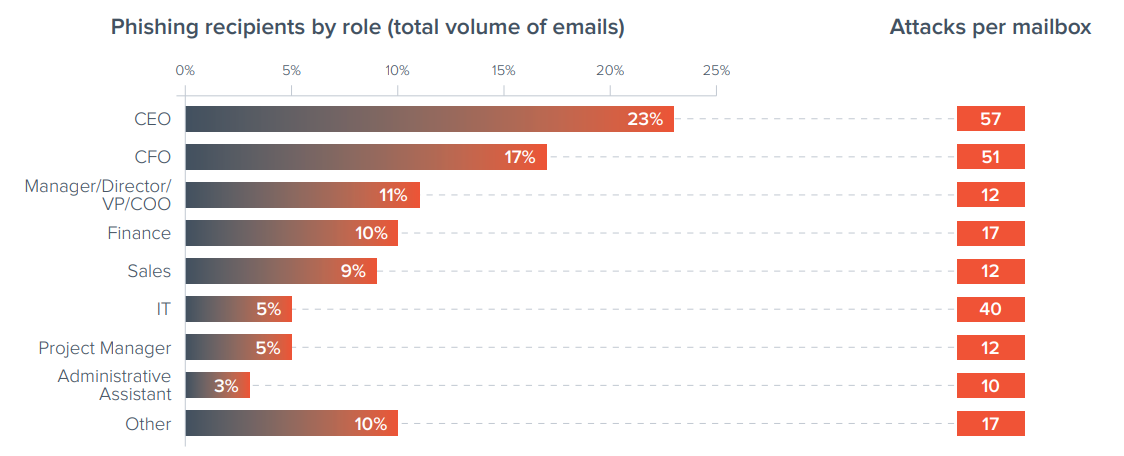
Although other employees are being targeted more in BEC attacks, this doesn’t mean that executives and those in finance are off the hook entirely. As you can see in the graph below, an average CEO receives 57 phishing emails on average per year.
Whether online criminals change who they target or not, one fact remains: They continue to look for the weakest link in your company, and all they need is that one click from an employee who falls for their schemes. This further highlights the importance of education and awareness efforts any company should be focusing and investing on.
Whether or not you’re part of an organization, it’s important to teach yourself to recognize the red flags of phishing attempts, both on your computer and mobile device. We got just what you need here:
Stay safe!