In an extensive report about a phishing campaign, the Microsoft 365 Defender Threat Intelligence Team describes a number of encoding techniques that were deployed by the phishers. And one of them was Morse code.
While Morse code may seem like ancient communication technology to some, it does have a few practical uses in the modern world. We just didn’t realize that phishing campaigns was one of them!
Let’s look at the campaign, and then we’ll get into the novel use of an old technology.
The campaign
Microsoft reports that this phishing campaign has been ongoing for at least a year. It’s being referred to as the XLS.HTML phishing campaign, because it uses an HTML file email attachment of that name, although the name and file extension are modified in variations like these:
- xls.HTML
- xslx.HTML
- Xls.html
- .XLS.html
- xls.htML
- xls.HtMl
- xls.htM
- xsl_x.h_T_M_L
- .xls.html
- ._xslx.hTML
- ._xsl_x.hTML
The phishers are using variations of XLS in the filename in the hope the receiver will expect an Excel file if they open the attachment. When they open the file, a fake Microsoft Office password dialog box prompts the recipient to re-enter their password, because their access to the Excel document has supposedly timed out. This dialog box is placed on a blurred background that will display parts of the “expected” content.
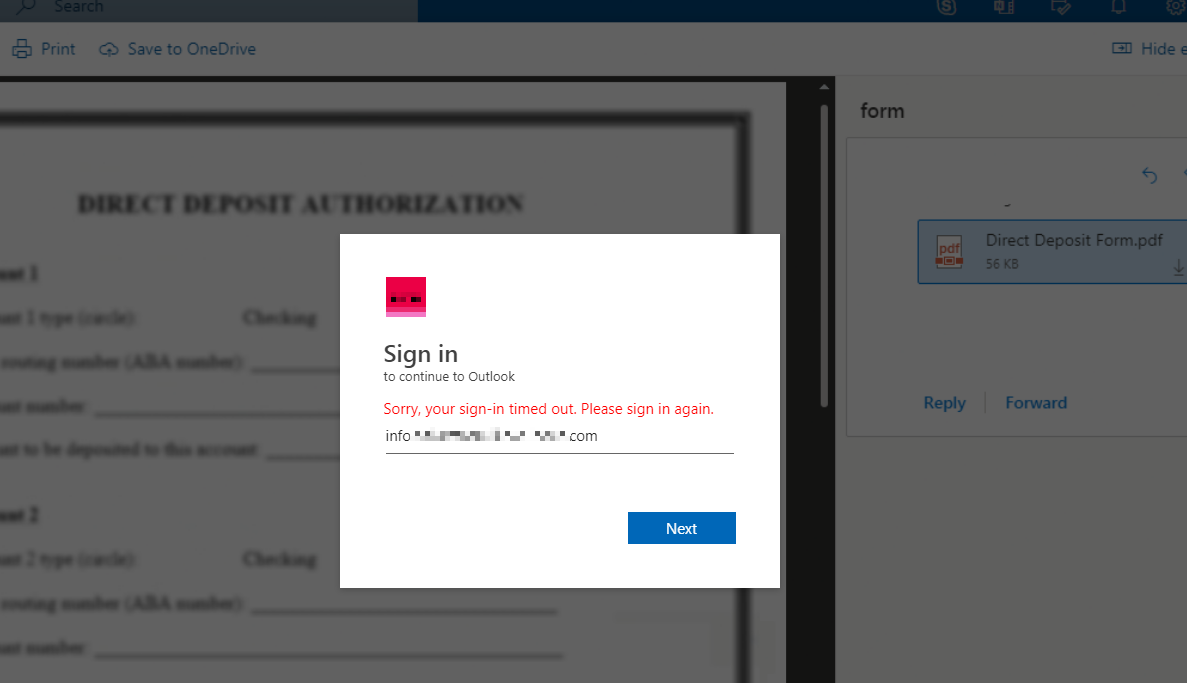
The script in the attachment fetches the logo of the target user’s organization and displays their user name, so all the victim has to do is enter the password. Which will then be sent to the attacker’s phishing kit running in the background.
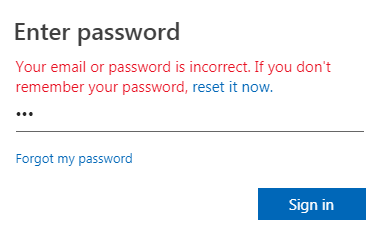
After trying to log in the victim will see a fake page with an error message and be prompted to try again.
It is easy to tell from the information about the target used by the phishers, like the email address and company logo, that these phishing mails are part of a targeted campaign that needed some preparation to reach this step.
And this phishing campaign is another step to gather more data about a victim. In the latest campaigns the phishers fetch the user’s IP address and country data, and send that data to a command and control (C2) server along with the usernames and passwords.
Encoding
The phishing campaign has been seen using different types of encoding, and combinations of encodings. For example, in one of the waves the user mail ID was encoded in Base64. Meanwhile, the links to the JavaScript files were encoded in ASCII before being encoded again, with the rest of the HTML code, in Escape.
Encodings seen in the campaign included:
- ASCII, a basic character encoding standard for electronic communication. ASCII codes represent text in computers, telecommunications equipment, and other devices.
- Base64, a group of binary-to-text encoding schemes that represent binary data in an ASCII string format. By using only ASCII characters, base64 strings are generally URL-safe, and allow binary data to be included in URLs.
- Escape or URL-encoding, originally designed to translate special characters into some different but equivalent form that is no longer dangerous in the target interpreter.
- Morse code, more about that below.
Not that encoding is different from encryption. Encoding turns data from one format into another, with no expectation of security or secrecy. Encryption transforms data in a way that only be reversed by somebody with specific knowledge, such as a password or key.
So, encoding methods won’t hide anything from a security researcher, so why bother? Changing the encoding methods around is designed to make it harder for spam filters trained on earlier versions of the campaign to spot the later versions.
Morse code
Morse code is a communication system developed by Samuel Morse, an American inventor, in the late 1830s. The code uses a combination of short and long pulses, which can be represented by dots and dashes that correspond to letters of the alphabet.
Famously, the Morse code for “SOS” is . . . - - - . . ., for example.
The International Morse Code encodes the 26 letters of the English alphabet, so the phishers had to come up with their own encoding for numbers. Morse code also doesn’t include special characters and can also not be used to distinguish between upper and lower case, which makes it harder to use than other types of encoding.
So, technically they didn’t use Morse code but an encoding system that used some base elements from Morse code using dashes and dots to represent characters.
This is how the javascript section for the morse code decoding looked.
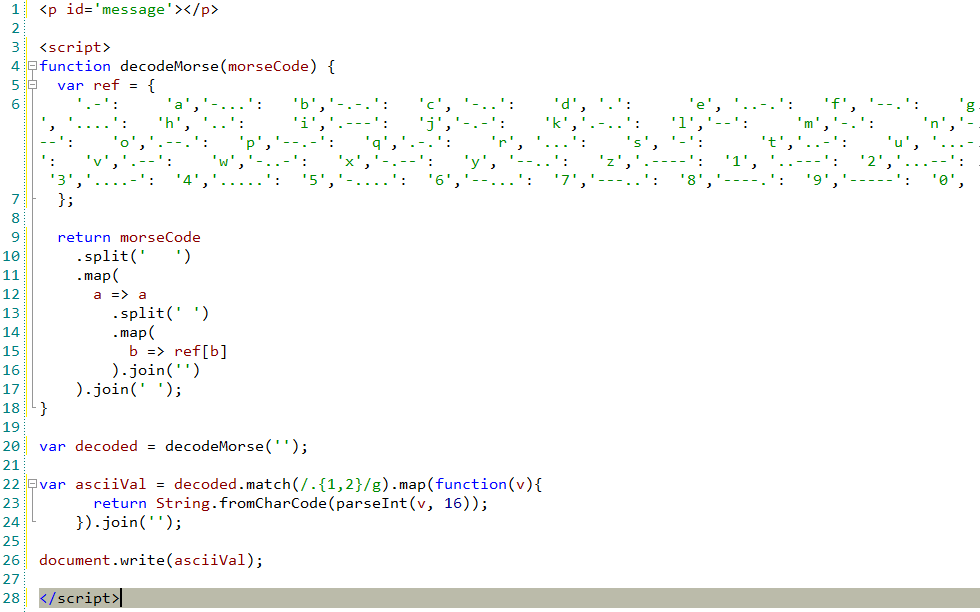
In one wave, links to the JavaScript files were encoded using ASCII, then Morse code. In other cases, the domain name of the phishing kit URL was encoded in Escape before the entire HTML code was encoded using Morse code.
Addendum
During our own research for this article we also came across files that used the pdf.html filename and similar variations on the theme we saw with the xls.html extension. These html files produced the same prompt to log into Outlook because the sign-in timed out.
These samples were named using the format: {company}-payroll-{date}-pdf.HtmL
For more information about phishing and how to protect yourself and your company please have a look at our page about phishing. For a full description of the phishing campaign, take a look a the Microsoft blog.
… – .- -.– / … .- ..-. . –..– / . …- . .-. -.– — -. . -.-.–











