On New Year’s Eve, Seif Elsallamy (@0x21SAFE on Twitter), a bug bounty hunter and security researcher, pointed out a phish-worthy security flaw he found on Uber’s email system. The flaw allowed anyone to send emails on behalf of Uber, meaning they would end with “@uber.com“, just like the one below:
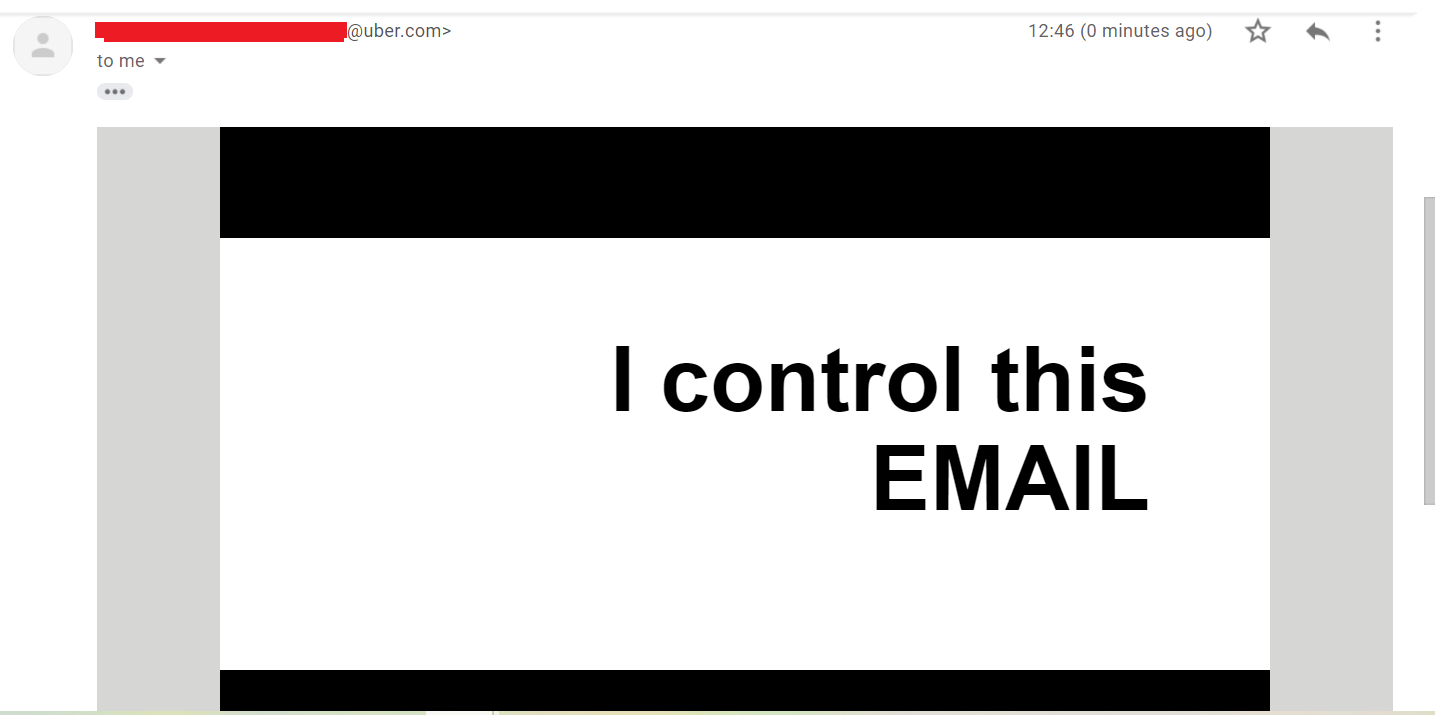
An email address with “@uber.com” legitimately sent from one of Uber’s email servers will no doubt pass through email spam filters and reach their intended recipients. Knowing that this can be done by anyone opens multiple phishing opportunities for the would-be scammer.
They could start sending out a fake email marketing campaign to Uber clients, potentially using a list from the 57 million user data breach in 2017. The email could contain a link to click on that leads to an external site that was made to look like it’s from Uber, too. Suffice to say, there is a lot of scamming potential here.
And this is not a case of email spoofing—which makes an email appear to come from somewhere legitimate but actually comes from somewhere entirely different—but a case of a successful HTML injection into a vulnerable email endpoint on Uber’s side.
As BleepingComputer said, it’s similar to the flaw disclosed by Youssef Sammouda in 2019 which allowed anyone to send an email on behalf of Facebook using an “@fb.com” email address. But the similarities end there, because while Facebook fixed the issue and awarded Sammouda a bounty, Uber has not done the same.
Falling on deaf ears
It often comes as a surprise when companies ignore bug reports that may actually have a huge impact on their business. Elsallamy’s finding has not only brought to light an old bug once more, but also unearthed a history of Uber not taking the issue seriously and, in turn, not doing anything about it.
Elsallamy tweeted: “Bring your [calculator] and tell me what would be the result if this vulnerability has been used with the 57 million email address that has been leaked from the last data breach? If you know the result then tell your employees in the bug bounty triage team.”
Soufiane el Habti (@wld_basha on Twitter), another bug bounty hunter, hopped on the original tweet thread, saying he raised the same issue to Uber last year but the triage team “closed it as informative”. Shiva Maharaj (@ShivaSMaharaj on Twitter) claimed that he reported this bug in 2015/2016, but said “they don’t care.”
When BleepingComputer asked what Uber should do to address this concern, Elsallamy said: “They need to sanitize the users’ input in the vulnerable undisclosed form. Since the HTML is being rendered, they might use a security encoding library to do HTML entity encoding so any HTML appears as text.”
Given how easy it is to perform HTML injections, clients and employees in Uber should keep a close eye on potential phishing and/or scam attacks.










