The San Francisco 49ers has confirmed that it has been hit by a ransomware attack. The announcement came just hours before the biggest football game of the year, Sunday’s Super Bowl between the Cincinnati Bengals and the Los Angeles Rams.
In a boilerplate statement to BleepingComputer, the 49ers revealed that the attack has caused temporary disruption to its IT network. As of this writing, it is in the process of recovering affected systems.
The San Francisco 49ers recently became aware of a network security incident that resulted in temporary disruption to certain systems on our corporate IT network. Upon learning of the incident, we immediately initiated an investigation and took steps to contain the incident.
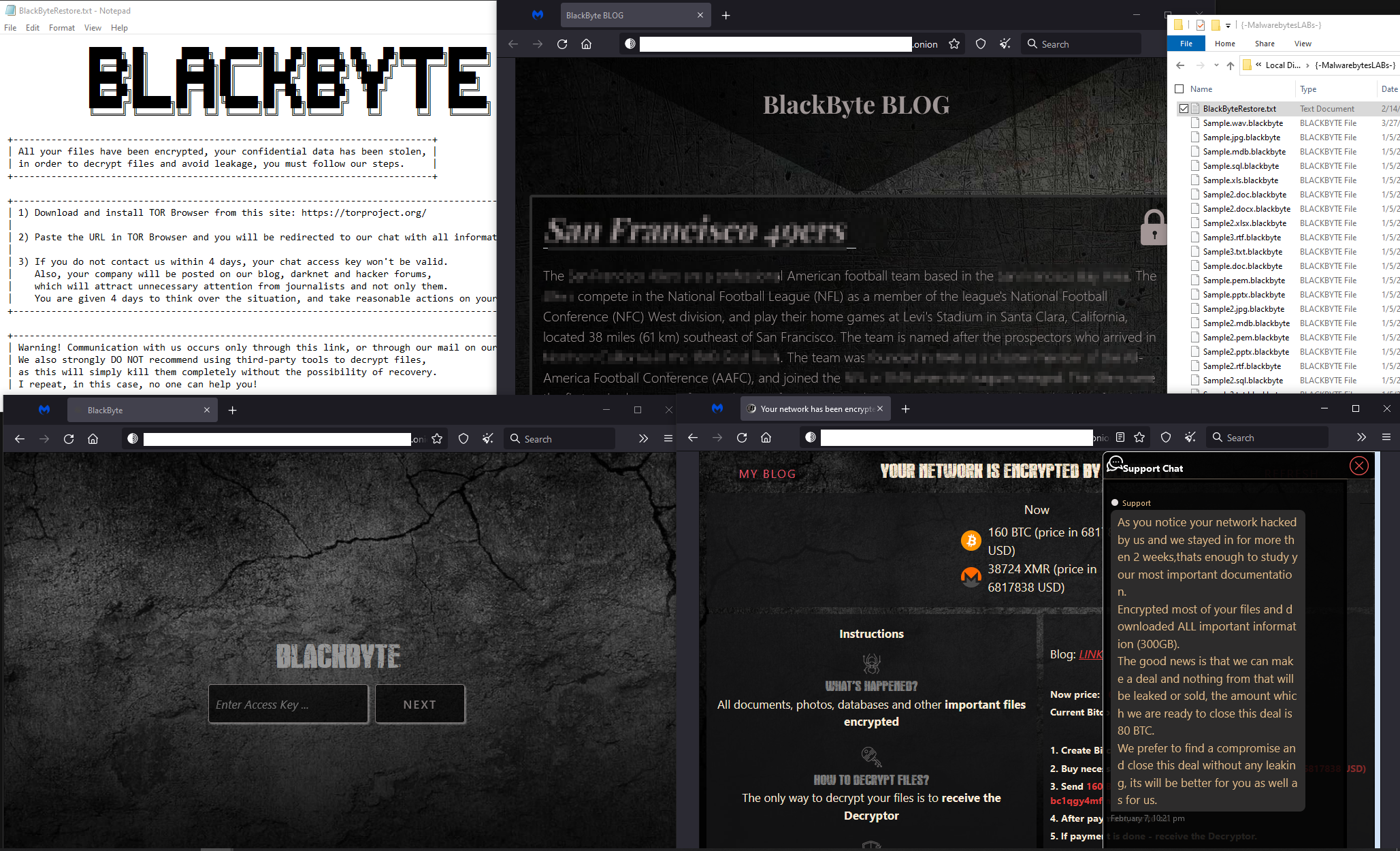
The BlackByte ransomware gang has already claimed responsibility for the attack by leaking a small number of files it claims to have been stolen.
Malwarebytes detects BlackByte as Ransom.BlackByte.
BlackByte
BlackByte ransomware is a relatively new ransomware-as-a-service (RaaS)tool, that has been around since July 2021. It is used by affiliates who breach organizations, steal valuable information, and then use ransomware to encrypt the organizations’ files—rendering them unusable. They then demand a ransom to decrypt the files, and threaten to leak the stolen data if it’s not paid.
Like other ransomware groups, the threat actors using Blackbyte have been known to use software exploits to breach victims’ networks, such as Microsoft’s well-publicised ProxyShell vulnerability. This only highlights the importance of applying software patches whenever they have been made available.
Our friends at Trustwave published a two-part [1] [2], in-depth analysis of the first version of BlackByte in October 2021. The analyses revealed a flaw in its code: The decryption/encryption key had been reused in multiple attacks. This allowed Trustwave researchers to create a free decyptor tool to help victims in the recovery of their files without paying the ransom.
Version two of BlackByte does not have this flaw, so the 49ers will likely have to rely on backups to recover its affected systems.
A timely FBI advisory
Just a couple of days before the attack, on Friday 11 February, the FBI released an advisorywarning about the dangers of BlackByte ransomware:
As of November 2021, BlackByte ransomware had compromised multiple US and foreign businesses, including entities in at least three US critical infrastructure sectors (government facilities, financial, and food & agriculture). BlackByte is a Ransomware as a Service (RaaS) group that encrypts files on compromised Windows host systems, including physical and virtual servers.
The advisort includes a number of BlackByte indicators of compromise (IOCs)—digital clues such as files, hashes, file modifications, and registry changes—associated with BlackByte activity. These help IT and security professionals determine if it is on, or has been on, their systems.
Lastly the FBI has advised organizations to keep regular backups of their data. That’s good advice, but there are other things you should consider too: Network segmentation to limit an attacker’s ability to move through your network; patching all systems to to prevent breaches; using two-factor authenticationand rate limitingto prevent brute force password guessing; and regular account audits to beef up account security.
Backups are a vitally important last line of defence against ransomware, but they often fail when people need them most. In a recent Malwarebytes Lock and Code podcast, host David Ruiz spoke with Matt Crape, technical account manager for VMware, about why backups are so hard to get right, and what the most basic missteps are when companies roll out a backup plan.
This post has been updated to include a new screenshot and Malwarebyte’s detection of the ransomware.










