GitLab has issued several critical security updates, with users of the version control software urged to upgrade their installations as soon as possible. One of the fixes is for a hard coded password issue.
What is distributed version control?
Distributed version control is a way for an organisation’s codebase to be mirrored on the devicesof anyone who needs access. Where people occasionally become confused is when they see a number of services using the word “Git” in their name. They’re not all the same thing, and we shouldn’t unnecessarily worry that one issue affects lots of different services due to naming conventions.
Are GitHub and GitLab the same thing?
They are not! If you’re reading about this update, you’re reading about an update for users of GitLab specifically. GitHub isn’taffected by this, and so users shouldn’t worry about missing security updates for hard-coded passwords. Hub and Lab are similar, but most definitely not the same.
What’s happened with GitLab?
There’s been a critical security release, addressing multiple issues. No fewer than 17 elements have been addressed, with one rated critical, two rated high, and nine rated medium. Here’s the rundown of the issue rated critical from their release page:
Static passwords inadvertently set during OmniAuth-based registration
A hardcoded password was set for accounts registered using an OmniAuth provider (e.g. OAuth, LDAP, SAML) in GitLab CE/EE versions 14.7 prior to 14.7.7, 14.8 prior to 14.8.5, and 14.9 prior to 14.9.2 allowing attackers to potentially take over accounts. This is a critical severity issue (CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:N, 9.1). It is now mitigated in the latest release and is assigned CVE-2022-1162.
This vulnerability has been discovered internally by the GitLab team.
Note: We executed a reset of GitLab.com passwords for a selected set of users as of 15:38 UTC. Our investigation shows no indication that users or accounts have been compromised but we’re taking precautionary measures for our users’ security.
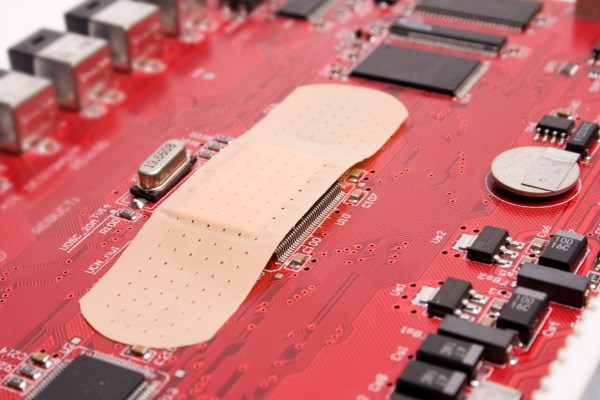
What are hardcoded passwords, and why are they bad?
Hardcoded passwords, also known as embedded credentials, make using the software or device they’re attached to a risky business. If your cheap, off the shelf router has the same single password in use for every single device, that’s bad. Someone who owns one of these devices now knows the password for all of those devices. If your forum software has a single, unchangeable password buried in the code, that’s bad. Somebody with dubious intentions may well have the keys to the kingdom for all versions of that forum.
It’s a similar story here – with a few caveats. According to The Register, accounts created through OmniAuthusing fewer than 21 characters for the password were vulnerable to the default password. A script has also been releasedwhich, in GitLab’s words, “…can be used by self-managed instance admins to identify user accounts potentially impacted by CVE-2022-1162”.
Time to update
If you think you may be impacted by this, make haste and check out the list of updates. You don’t want to leave an easy way in for attackers to exploit your business.