Our spam traps recently caught a phishing scam that neatly illustrates some of the tactics scammers use routinely to avoid both human intuition, and automatic detection.
The scam starts with an unsolicited email, of course…
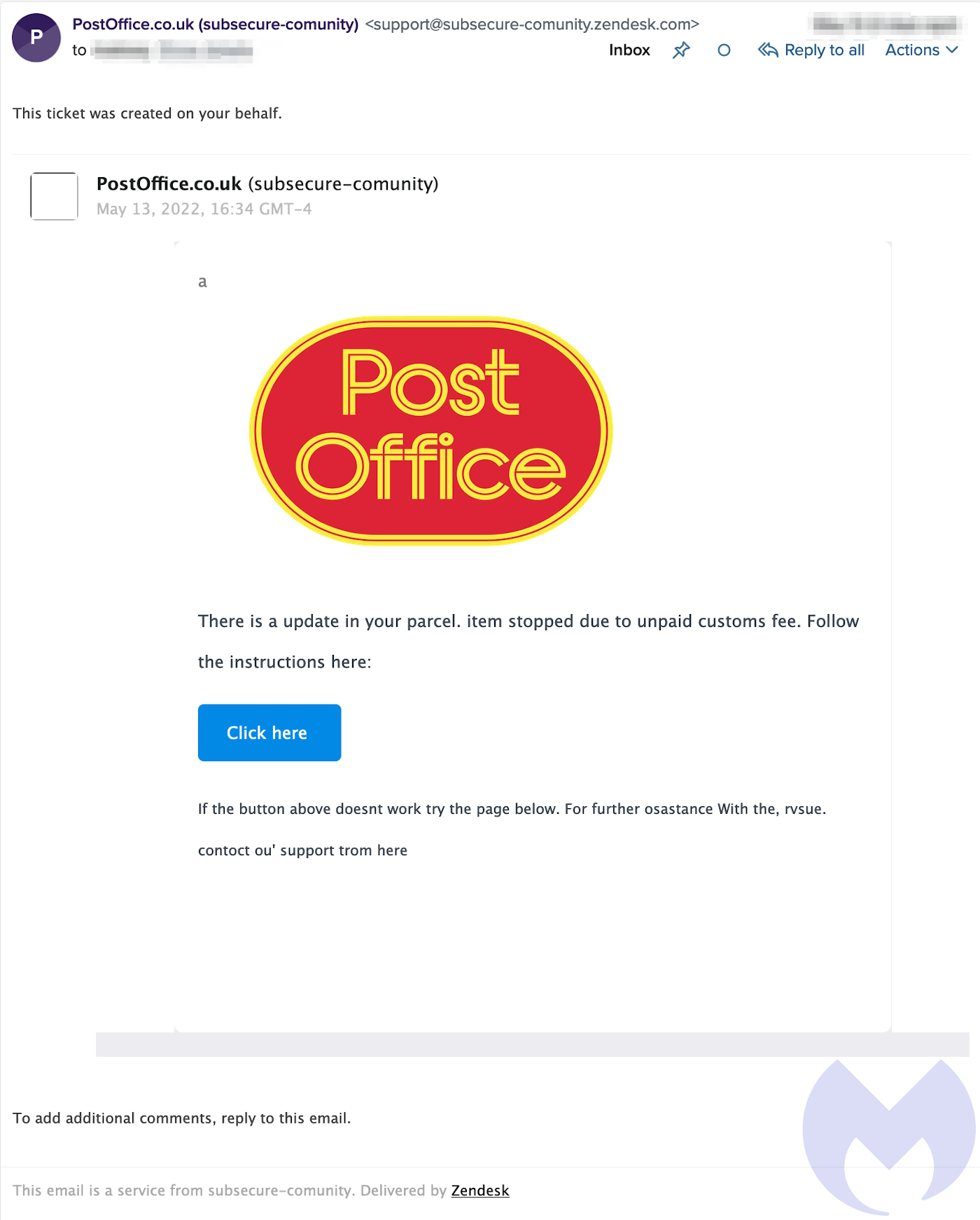
The scam email is ostensibly from the Post Office, an instantly recognisable postal service brand in the UK, and it tells recipients “There is a update in your parcel. item stopped due to unpaid customs fee.” [sic] This is an echo of an extremely popular SMS scam from 2021 that told recipients they had to pay a small postage fee to release a parcel waiting for delivery.
The spelling and grammar in the email is predictably awful, and a little weird—it looks like a bad scan by an optical character reader (OCR). However, despite decades of security advice highlighting poor spelling and grammar as an enormous red flag, the fact is it doesn’t seem to hurt the scammers. So while other tactics have evolved, poor English has persisted.
As simple as it is, and as bad as it seems, the message includes a number of features that help to avoid raising suspicions:
It’s a familiar message from a trusted brand
Half the email is taken up by a giant logo for an organisation that is instantly recognisable to anyone in the UK. The scammers are building trust in the sender and telling users this is about a postal delivery, without writing a word.
They are also piggybacking on a very familiar form of email communication. Delivery companies like DHL and Royal Mail regularly bombard us with email and SMS updates about deliveries, recipients are often asked to click through to websites to track parcels, and occasionally they have to pay postage or customs fees.
The address looks good
The from address starts “PostOffice.co.uk”, suggesting it’s come from the postoffice.co.uk domain. However, that’s the Display Name, a user-friendly name that can be anything the sender wants. The address is the part in angle brackets: support@subsecure-community.zendesk.com.
Some sharp-eyed users may spot that it’s actually a zendesk.com email address, but Zendesk itself is a trusted system that’s used by big brands, and getting an email from Zendesk isn’t unusual either.
Because Zendesk is an online business, it makes setting up new accounts very easy. And because it relies heavily on email, it uses features like DKIMto minimise the chances of its emails being forged or flagged by anti-spam tools. By setting up genuine Zendesk accounts, the scammers are able to benefit from those security features, and the trustworthiness of the zendesk.com domain.
Of course criminals don’t expect their accounts to last long, and this one was quickly shut down.
The links don’t look bad
Users who hover their pointer over the email’s links, hoping to see if they look nefarious, will be disappointed, as they’ll just see an impenetrably-complicated URL. A lot of emails use odd-looking and convoluted URLs, so it’s rare to see links that are obviously good or obviously bad, and these are unlikely to ring alarm bells.
The only oddity that might tip off knowledgeable users is that links go to Google. They look like this:
https://www.google.com/url?sa=t&rct=j&q=&esrc=s&source=web&cd=&cad=rja&uact=8&ved=2ahUKEwi2z4al48_3AhUDgf0HHQYWA-sQFnoECAkQAQ&url=https%3A%2F%2Fexample.org%2Fbaby-music%2F&usg=AOvVaw2RWSxL7fWRChaS7EhY5OuA
This URL in the email is borrowed from a Google search results page. Why? Because the links in Google search results pages are open redirectsthat can be used by anyone to create a google.com URL that will redirect to a web page of their choice. Many companies regard open redirects as a security vulnerability, but Google does not.
The web page you end up on if you click the link in the phishing email is highlighted below, although we’ve replaced the name of the compromised website with example.org:
https://www.google.com/url?sa=t&rct=j&q=&esrc=s&source=web&cd=&cad=rja&uact=8&ved=2ahUKEwi2z4al48_3AhUDgf0HHQYWA-sQFnoECAkQAQ&url=https%3A%2F%2Fexample.org%2Fbaby-music%2F&usg=AOvVaw2RWSxL7fWRChaS7EhY5OuA
The Google open redirect helps to hide the real URL from curious users, but it may help to hide it from automatic detection too. The open redirect on google.com uses JavaScript rather than HTTP, so automated tools that follow chains of HTTP redirects won’t reach the scammer’s website, they’ll simply stop at google.com, which returns a status of 200 OKrather than
301 RedirectSo where does it end up? Right now, nowhere. Whatever was waiting for victims on the compromised website—malware, malvertising, a payment form, or some other equally unpleasant thing—has been removed by the site owner. All that’s left is an empty directory.
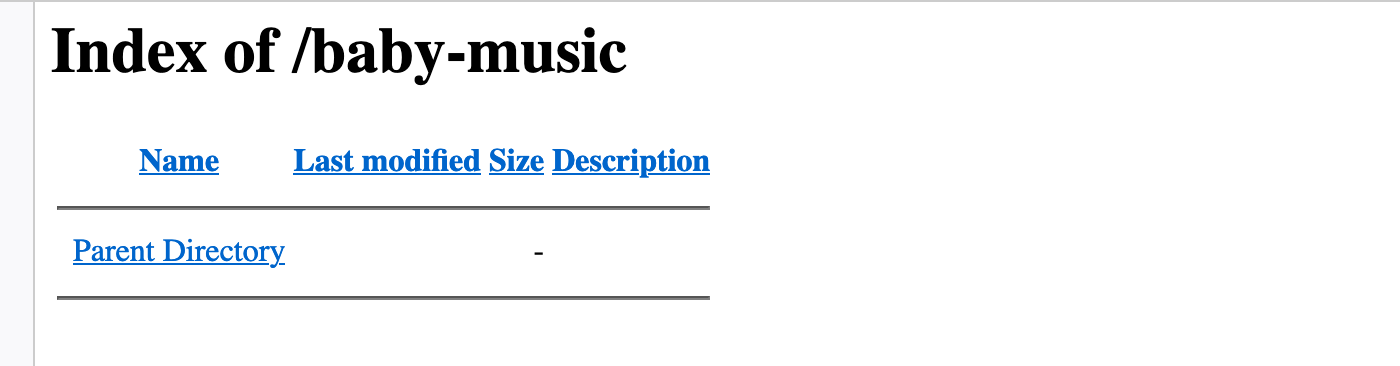
The scammers, no doubt, have already moved on to a new compromised website, a new “burner” Zendesk account, and a different Google URL.










