Apple has announced a new feature of iOS 16 called Lockdown Mode. This new feature is designed to provide a safer environment on iOS for people at high risk of what Apple refers to as “mercenary spyware.” This includes people like journalists and human rights advocates, who are often targeted by oppressive regimes using malware like NSO Groups’ Pegasus spyware.
NSO is an Israeli software firm known for developing the Pegasus spyware. Pegasus has been in the spotlight frequently in recent years, and although NSO claims to limit who is allowed to have access to its spyware, each new finding shows it is used by authoritarian nations bent on monitoring and controlling critics. In one of the more infamous cases, and a classic example of how Pegasus has been used, journalist Jamal Khashoggi’s murder has been traced to the use of Pegasus by the United Arab Emirates.
How is this possible? iPhones don’t get viruses!
Contrary to popular belief, it is, in fact, possible for an iPhone to become infected with malware. However, this usually involves a fair bit of effort, usually the use of one or more vulnerabilities in iOS, the operating system for the iPhone. Such vulnerabilities have been known to sell for prices in the million dollar range, which puts such malware out of the reach of common criminals.
However, companies like NSO can purchase – or pay expert iOS reverse engineers to find – these vulnerabilities and incorporate them into a deployment system for their malware. They then sell access to this malware to make money.
Deploying the malware typically happens via something like a malicious text message, phone call, website, etc. For example, NSO has been known to use one-click vulnerabilities in Apple’s Messages app to infect a phone if a user taps a link. It’s also used more powerful zero-click vulnerabilities, capable of infecting a phone just by sending it a text. Because of this, Apple made changes in iOS 14 to harden Messages.
Messages is not the only possible avenue of attack, however, and it’s impossible to build a wall for the “walled garden” that doesn’t have some holes in it. Every bug is a potential avenue of attack, and all software has bugs. Thus, Apple has taken things to a new level by providing Lockdown Mode to high-risk individuals.
What is Lockdown Mode?
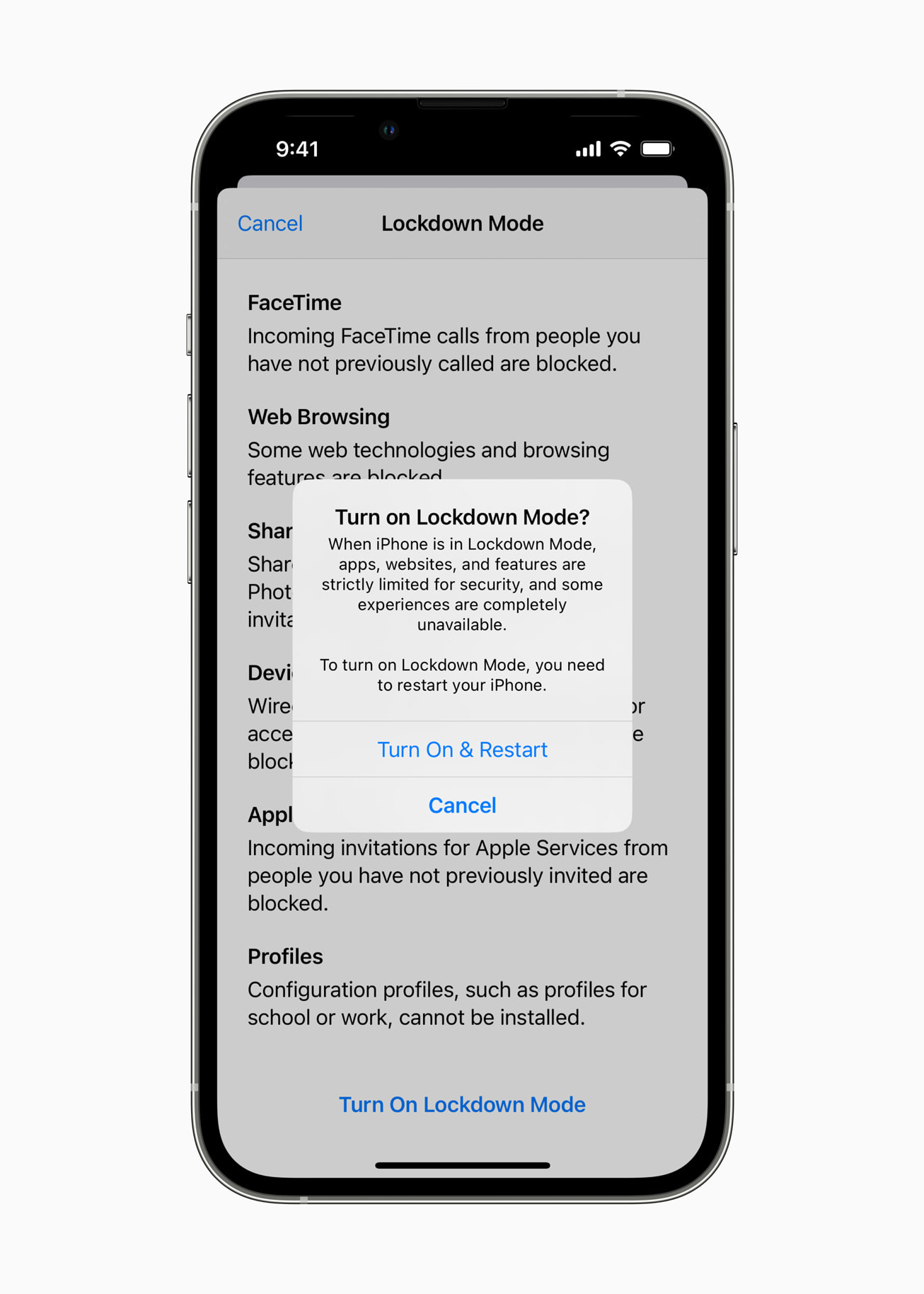
Lockdown Mode puts the iPhone into a state where it is more difficult to attack. This is done by limiting what is allowed in certain aspects of usage of the phone, to block potential avenues of attack. The improvements, per Apple’s press release, include:
- Messages: Most message attachment types other than images are blocked. Some features, like link previews, are disabled.
- Web browsing: Certain complex web technologies, like just-in-time (JIT) JavaScript compilation, are disabled unless the user excludes a trusted site from Lockdown Mode.
- Apple services: Incoming invitations and service requests, including FaceTime calls, are blocked if the user has not previously sent the initiator a call or request.
- Wired connections with a computer or accessory are blocked when iPhone is locked.
- Configuration profiles cannot be installed, and the device cannot enrol into mobile device management (MDM), while Lockdown Mode is turned on.
Although Apple refers to Lockdown Mode as “an extreme, optional protection,” the limitations don’t actually sound particularly difficult to live with. Most users probably won’t turn this on, but these restrictions sound like something that the average user could adapt to fairly easily.
Backing it up with big bucks
To further bolster the security of Lockdown Mode, Apple is offering an unprecedented $2 million bug bounty to anyone who can find a qualifying vulnerability that can be exploited while an iPhone is in Lockdown Mode. Vulnerability hunters everywhere will be pounding on Lockdown Mode, looking for a bug that will score them the big payout. However, this bounty will also help to ensure that the vulnerability gets disclosed to Apple rather than being sold to a company like NSO. It’s easy to do the right thing when it also earns you $2 million!
Should I use Lockdown Mode?
If you’re a journalist and you cover topics that may put a target on your back, absolutely! If you’re a defender of human rights and a critic of countries that trample on those rights, don’t think twice.
Average people, though, will have little chance of ever encountering “mercenary spyware.” However, the extra security definitely wouldn’t hurt, and it looks like it won’t cost you a lot in terms of lost functionality.










