On Friday, December 2, Google rolled out an out-of-band patch for an actively exploited zero-day vulnerability in its V8 JavaScript engine. The flaw could allow attackers to cause a system crash or execute potentially malicious code.
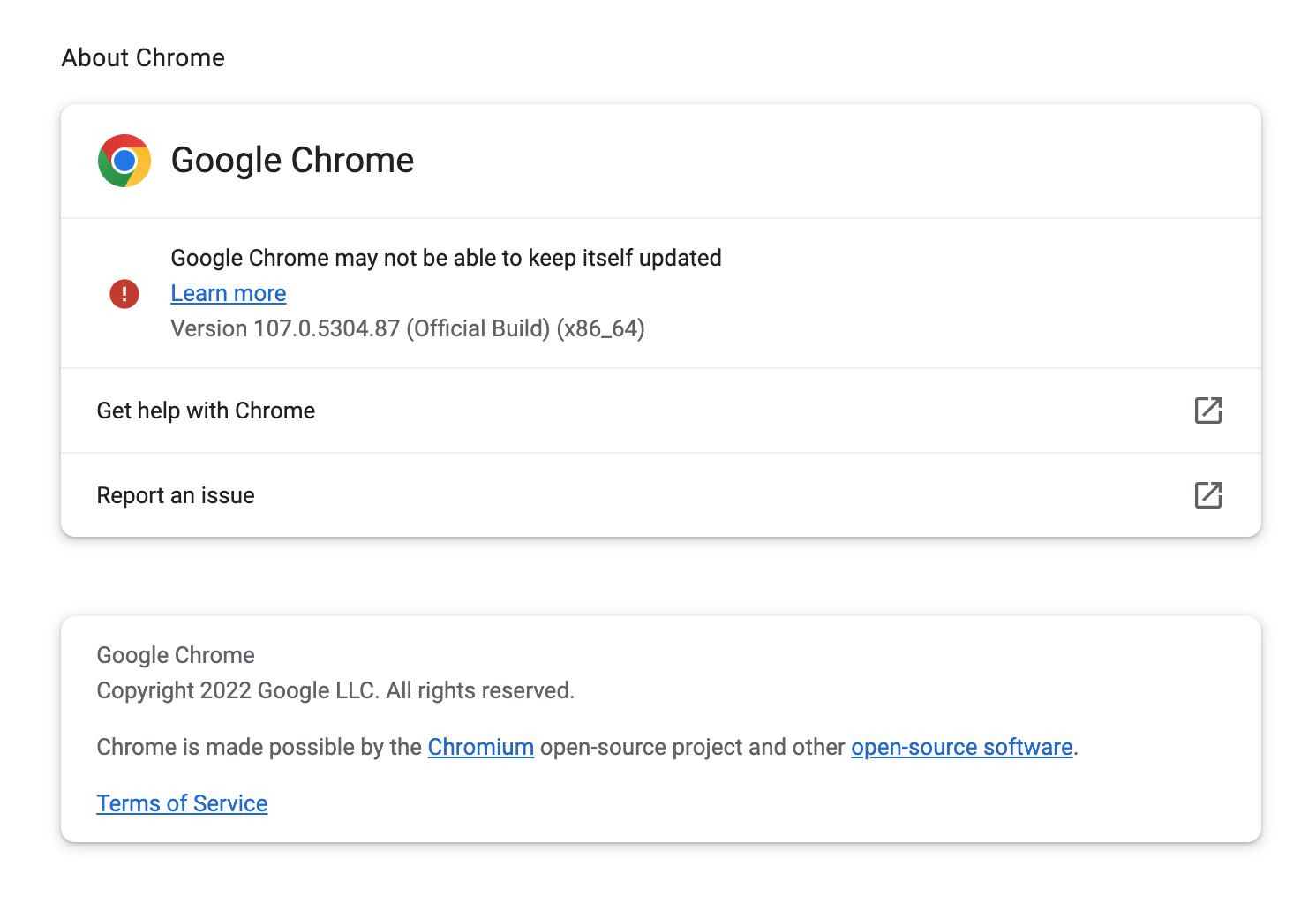
That means you’ll want to update Chrome to patch against this vulnerability as soon as you can. Do this by navigating to the “About Chrome” page on your browser’s menu.
If your Chrome version is 108.0.5359.94 (Mac and Linux) or 108.0.5359.94/.95 (Windows), then you have the latest version. If it, click Update Google Chrome.
Note: if you don’t have the update option, such as in the case below, some files may be missing from your computer, so it’s best to uninstall and reinstall Chrome.
Also, if you have other Chromium-based browsers you’re using, you may need to update them.
Vulnerability details
The flaw, tracked as CVE-2022-4262, has a severity rating of “High” and is a type confusion bug. Once exploited, remote attackers could exploit a memory corruption (also called heap corruption) using a specially crafted HTML page.
A type confusion bug happens when code doesn’t verify the object type passed to it, and then uses the object without type-checking. Unfortunately, this bug occurs on the V8 JavaScript engine, Google’s open-source JavaScript engine. Attacks on the V8 are not common; however, it’s considered one of the most dangerous.
CVE-2022-4262 is the 4th type confusion bug found this year and the 9th actively exploited zero-day to date.
As with any zero-day vulnerabilities Google patches, very little technical detail is provided about the vulnerability. You will also find that online pages for this vulnerability either contain incomplete details or are there as placeholders to be updated with new information in the future. The National Vulnerability Database is currently analyzing this flaw.
We don’t just report on threats—we remove them
Cybersecurity risks should never spread beyond a headline. Keep threats off your devices by downloading Malwarebytes today.










