In what might be conceived as one of Microsoft’s new year resolutions, it has disclosed that it’s turned off the ms-appinstaller protocol handler by default. The change is designed to make installing apps easier, but it also makes installing malware easier.
Typically, an app needs to be on a device before it can be installed, which normally means that a user has to download it first. To save time and disk space, Microsoft introduced the ability to install applications directly from a web server, without downloading it first. It relies on links that use the ms-appinstaller URI (Uniform Resource Identifier) scheme, which are handled by App Installer rather than a web browser. When software is installed this way users don’t see SmartScreen or browser warnings about downloaded executables.
Microsoft reports that it observed malicious activity where criminals tricked users into installing malware using ms-appinstaller links, allowing them to bypass mechanisms like SmartScreen that are designed to keep users safe.
Several cybercriminals were found selling a malware kit as a service that abuses the MSIX file format and ms-appinstaller protocol handler. They distribute signed malicious MSIX application packages using websites accessed through malicious advertisements for legitimate popular software.
The abuse was first noticed in November 2023. Several known groups were using it in different scenarios, all of which lead users to landing pages that mimicked legitimate software vendor sites, where the malware was available via ms-appinstaller links or malicious MSIX installers.
Cybercriminals used four different techniques to spread their malware:
- SEO poisoning. Users who searched for legitimate software applications on Bing or Google were presented with search results for malicious landing pages.
- Malvertising. Users searching for software were directed to malicious landing pages via search ads mimicking legitimate vendors.
- Teams messages. Users were sent messages over Microsoft teams linking to malicious landing pages.
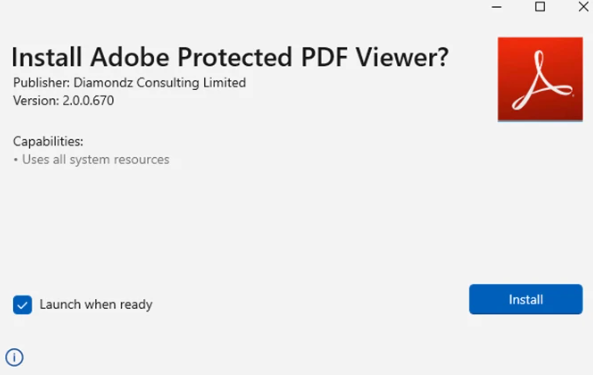
- Social engineering. Microsoft showed an example of an employement opportunity site that tricked visitors into installing malware by saying it was a new PDF reader version that was required in order to view a document.
The criminal groups identified as using these methods were all initial access brokers (IABs). IABs are individuals or organizations that specialise in providing ransomware gangs with access to company networks.
Malicious installers can be spotted by looking at the publisher information in the ms-appinstaller prompt.
To manually disable ms-appinstaller on your network, set the Group Policy EnableMSAppInstallerProtocol to disabled.
How to avoid ransomware
- Block common forms of entry. Create a plan for patching vulnerabilities in internet-facing systems quickly; and disable or harden remote access like RDP and VPNs.
- Prevent intrusions. Stop threats early before they can even infiltrate or infect your endpoints. Use endpoint security software that can prevent exploits and malware used to deliver ransomware.
- Detect intrusions. Make it harder for intruders to operate inside your organization by segmenting networks and assigning access rights prudently. Use EDR or MDR to detect unusual activity before an attack occurs.
- Stop malicious encryption. Deploy Endpoint Detection and Response software like ThreatDown EDR that uses multiple different detection techniques to identify ransomware, and ransomware rollback to restore damaged system files.
- Create offsite, offline backups. Keep backups offsite and offline, beyond the reach of attackers. Test them regularly to make sure you can restore essential business functions swiftly.
- Don’t get attacked twice. Once you’ve isolated the outbreak and stopped the first attack, you must remove every trace of the attackers, their malware, their tools, and their methods of entry, to avoid being attacked again.
Our business solutions remove all remnants of ransomware and prevent you from getting reinfected. Want to learn more about how we can help protect your business? Get a free trial below.