Ever since the Mandiant APT1 report landed like a bomb in private sector security reporting, threat intelligence has been a hot buzzword many companies have been chasing over. But what is threat intelligence? What do you need to execute it well? And how many new tools do you need to buy? The ambiguity around these questions leaves many people wondering “How on earth do I start a threat intel program?”
Maybe don’t?
Threat intelligence is a very new, very popular buzzword in the security industry. But as a capability, it’s both very expensive, and meant to sit on top of a mature security program. Do you have mitigations in place against the OWASP top 10? Have you vetted your existing vendors for efficacy? Do you have a fully staffed and trained SOC, or are your analysts working double shifts? If you don’t have clear answers to those questions, your security program probably is not mature, and would not really benefit from an additional costly function.
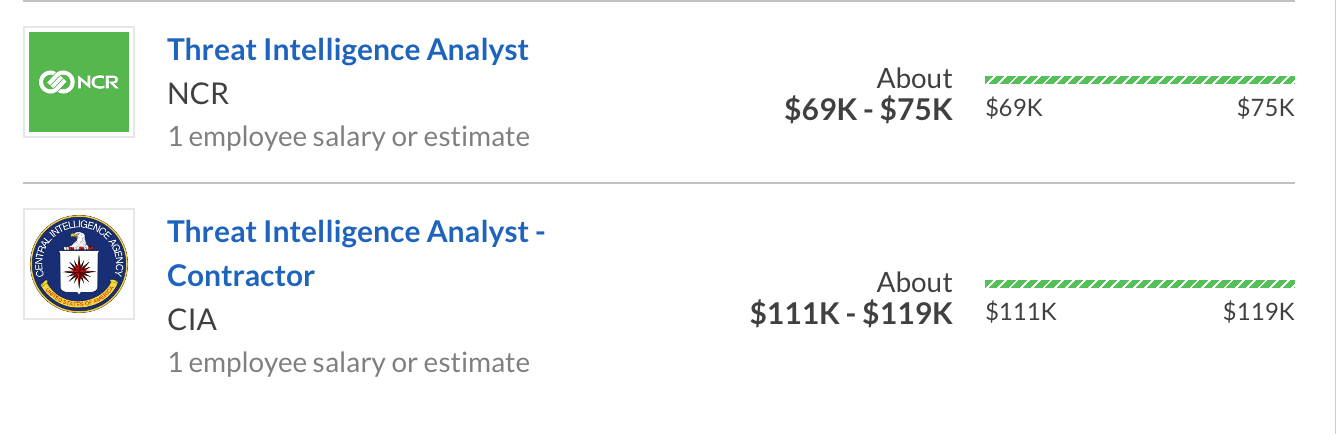
Cost can be a serious concern. While SOC analysts have a fairly wide spread for salary range, threat intelligence analysts with government training are not that common, resulting in a salary premium. Below you can see a relatively common private sector intelligence analyst salary as contrasted with a salary for a government trained analyst.
A well-trained threat intel analyst embedded in a mature security team can be an outstanding force multiplier, but without a well-oiled environment to place them into, they can inflate staffing budgets without providing a significant return on investment.
But I have to
If you must start a threat intel program, the first step is to look for the components you already have. Spending on threat intel vendors or employees with highly specific experience can lead to astronomical costs, and raises the odds that enterprise leadership won’t find value in the team. So start small: almost every Tier II SOC has senior members with a wealth of experience in the threat landscape, and an itch for more responsibility. Rather than casting a line into a very tight market for new staff, it’s much more cost effective to send those SOC members to intelligence training, then task them with creating training for everyone else. Some companies have accomplished this via transitioning SOC staff from monitoring to threat hunting.
Threat hunting – intel you should already be doing
Per Wikipedia, “Cyber threat hunting is the process of proactively and iteratively searching through networks to detect and isolate advanced threats that evade existing security solutions.” In practice, what this amounts to is training analysts to tell the entire story of a threat: where did it start, what TTPs were employed in the attack, what systems were touched, and what corroborating information can be gained from public data. When a responder is trained to tell the full story of a threat in this manner, organizations can not only respond to a threat, but can also learn from it and adjust mitigations accordingly.
Tools you need and tools you don’t
First and foremost, you do not need a third party threat intelligence feed. It’s a nice to have, but the reality is that external vendors cannot provide data specific to your company, and frequently struggle to offer relevant data filtered by industry vertical. Vastly more important is to make appropriate use of the data you have. Here’s a non-comprehensive list of data that many companies collect, but don’t exploit effectively:
- Malicious spam can be used to pinpoint types of threats specific to the organization, as well as relative popularity of exploits used
- Log review is commonly done as part of after action reports associated with a breach. But they can also be used proactively to review patterns of activity, and adjust mitigations accordingly.
- Password failures. If a threat actor is attempting to brute force an account, is it a dictionary attack or have the credentials previously been valid on the system? Looking at use of outdated passwords can pinpoint a past data leak, or give visibility into how stolen company data is disseminated out to threat actors.
Reviewing internal data for threat intelligence can be much more effective than a third party feed because all internal data is by definition tailored to your company’s specific threat profile. It also costs nothing, which doesn’t hurt.
Where to go next
Threat intelligence is a relatively new field in private sector infosec, but a few researchers have produced valuable resources for getting people on the right path.
Securosis provides both a threat intel blog, and a library of papers offering deep dives into security principles and best practices.
The SANS reading room has a great white paper on identifying what threat intel is, and what it can do in best cases. Very useful in communicating with executives who might be unclear on these ideas.
And if you’ve already started a threat intel program, check out the SANS paper on evaluating information security controls. The scope is a bit broader than a single cyber security function, but should provide valuable input on how to judge if your program is working for you at a reasonable cost.
Threat intelligence is still a very new idea that doesn’t yet have widely agreed upon best practice. So while there are some good resources to get started, the best resource for you is most likely other people in the same position. Talking to peers, reading current blogs, and keeping tabs on productive teams can position you well for success. Good luck, and stay safe.










