WordPress is an immensely popular content management system (CMS) powering over 43% of all websites. Many webmasters will monetize their sites by running ads and need to draw particular attention to search engine optimization (SEO) techniques to maximize their revenues.
But some people will take a shortcut to gaining traffic by engaging in legal but sometimes fraudulent practices. In this instance, we identified someone buying popunder traffic to promote their websites. A popunder is a very common occurrence online and consists of launching a secondary page under the current one. In itself, it could be considered simply an annoyance and is not malicious except when the website that is being launched uses various techniques to defraud advertisers.
We discovered a few dozen WordPress blogs using the same plugin that mimics human activity by automatically scrolling a page and following links within it, all the while a number of ads were being loaded and refreshed. The blogs would only exhibit this invalid traffic behavior when launched from a specific URL created by this plugin, otherwise they appeared completely legitimate.
In this post, we share the technical details behind this ad fraud scheme and any clues pointing to the developer of this WordPress plugin.
Key findings
- About 50 WordPress blogs have been backdoored with a plugin called fuser-master
- One of the blogs performing this ad fraud had 3.8 M visits in January, with an average visit duration of 24:55 minutes and 17.50 pages per visit
- This plugin is being triggered via popunder traffic from a large ad network
- The WordPress sites are being loaded in a separate page underneath and display a number of ads
- The plugin contains JavaScript code that mimics the activity of a real visitor: scrolls the page, clicks on links, etc.
- The code also monitors for real human activity (mouse movement) and will immediately stop the fake scrolling when that happens
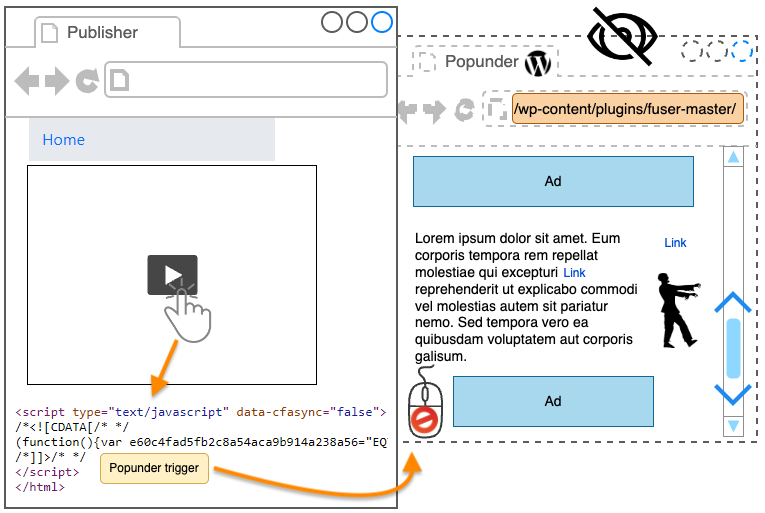
Figure 1: Diagram summarizing ad fraud case
Fuser-master WordPress plugin
Recently we blogged about ad fraud involving a popunder as well, except in that case it was using an iframe to hide the ads. Here, there is nothing hidden at all and the ad fraud can only be deduced when the page is being scrolled down, and back up at random intervals. Because it is a popunder, anyone becomes an unwitting accomplice and does not see any of the fraudulent behavior.
In this investigation, we won’t be spending time on the ad network facilitating these popunders but we have a fairly good idea of which one it might be based on anti-debugging code that they used. What makes popunders particularly enticing for ad fraud is the fact they allow content to be loaded and remain until further action. Unlike the main browser window where a user can easily navigate away from the current website they are visiting, the popunder will remain open for several minutes or even hours, until it is closed.
We were able to trigger the popunder several times and noticed that the fraudsters were using several different blogs that all had the same thing in common, namely they used a plugin called ‘fuser-master’. There aren’t many references for this plugin such as where to download it or who its author might be. We were only able to find one mention from themesinfo.com which is a WordPress theme detector.
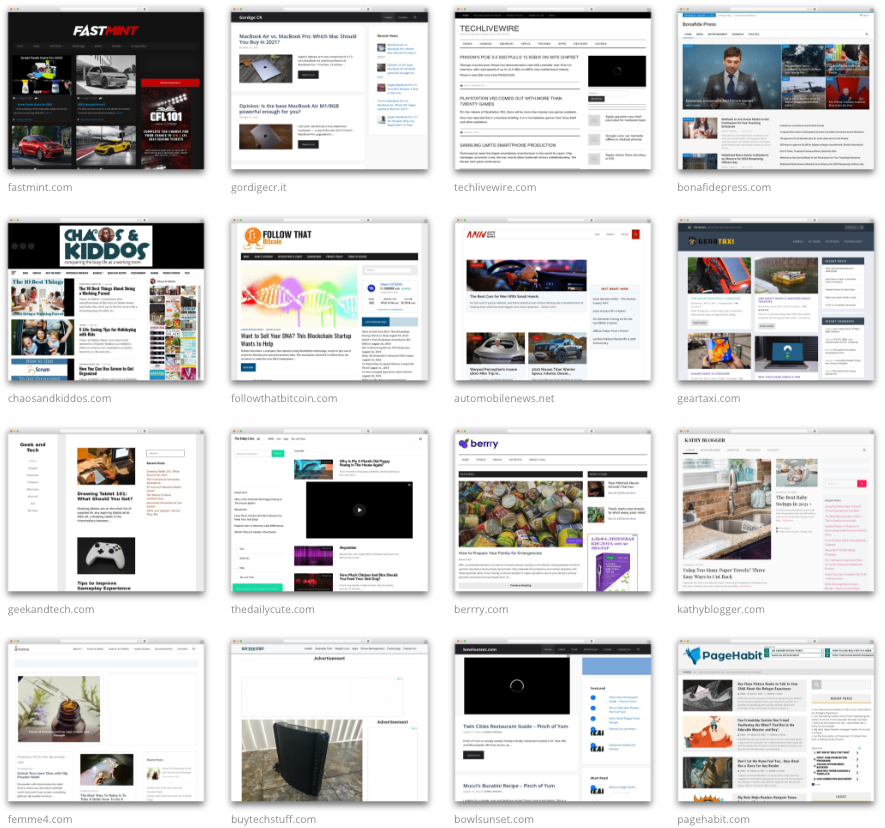
Figure 2: A list of websites using the fuser-master plugin
Not all the sites listed in the gallery still exist or are fully functional, but that still gave us a good indication of what was being used to turn standard blogs into ad fraud robots. It’s worth mentioning again that when visited at their homepage, all these blogs are static in nature, meaning we don’t see this kind of zombie activity where the page is scrolling by itself. In the next section, we will look at the URL entry point that triggers that specific behavior.
User check and redirect
All of these blogs appear typical when visited directly, so they would likely pass both a manual and human verification. However, when a special URL (the entry point) is entered with the corresponding parameters, they turn into ad fraud. Below you can see the URL path and its parameters that are being used on all the blogs where that plugin has been installed:
/wp-content/plugins/fuser-master/entrypoint.php?
- e
- Iptoken
- websiteid
- geo
First, the current user is checked to determine if they should be allowed to enter into the ad fraud scheme or not:
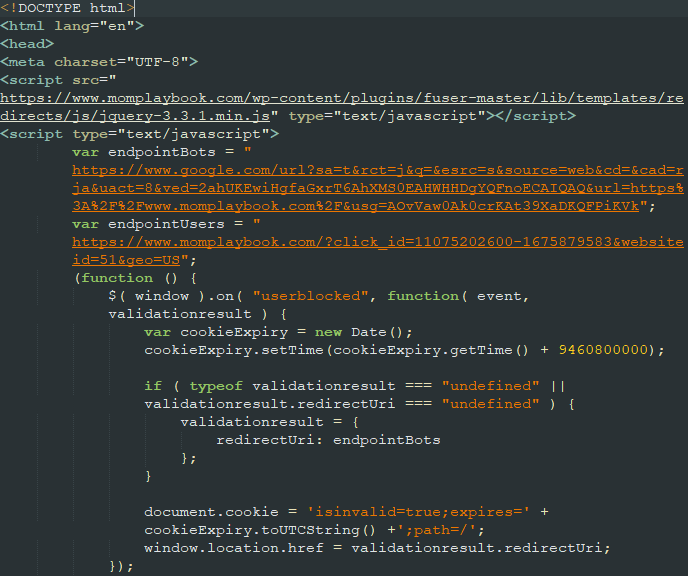
Figure 3: Pre-check for cookies
The fraudsters are using open redirects from Google and Twitter in an interesting way. A keyword from an array corresponding to related Google search terms is picked and added to a Google search URL:
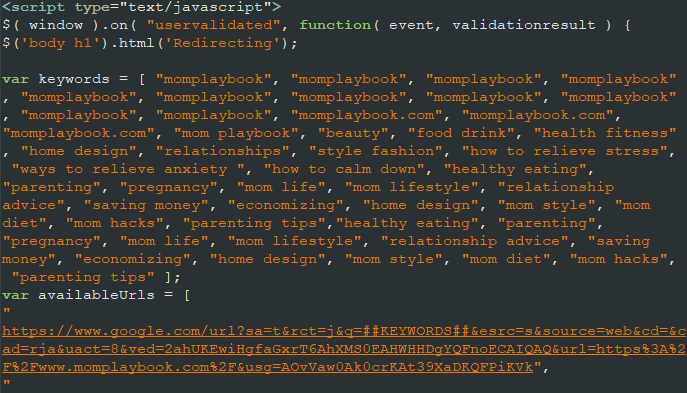
Figure 4: SEO trick
That keyword is chosen randomly and makes up the dynamic redirect URL:
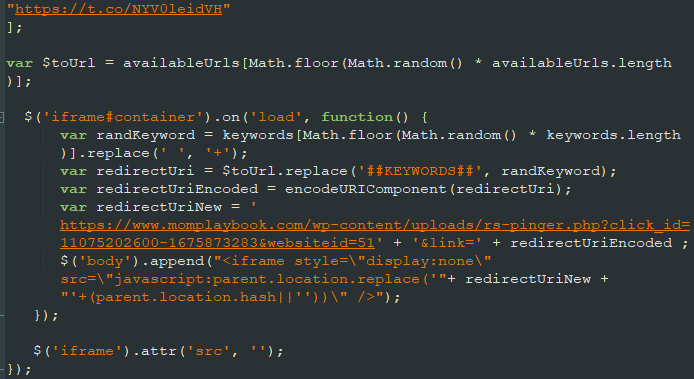
Figure 5: Keyword used in redirect
The next web request is the actual redirect code which also drops some cookies. The URL and code for the redirect will vary based on the different options set up previously:
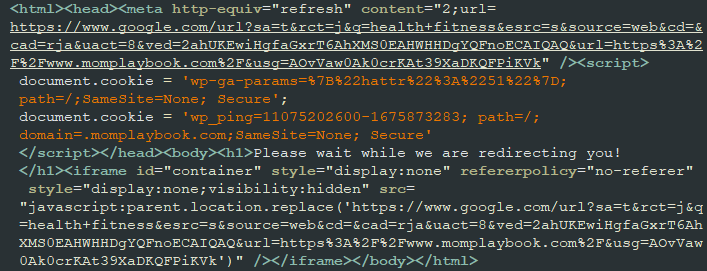
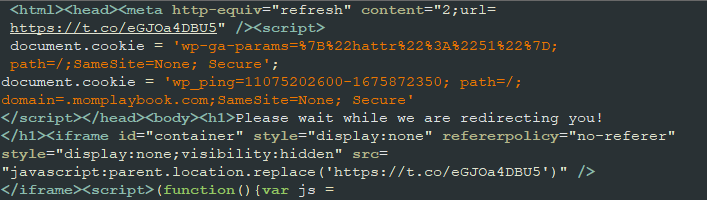
The popunder will effectively load the blog via the entrypoint, then immediately leave it to re-enter via a Google open redirect as if someone had clicked on one of the search results. This is what it looks like:
Figure 8: Animation showing open redirect mechanism
Faking user activity
As mentioned previously, the blogs will only exhibit their ad fraud nature when visited via the fuser-master plugin’s entry point. We know that this happens when a user was browsing the web, clicked on a page and a popunder was launched. The blog will open up in a new window behind the current window, which means the user is completely unaware of what is happening.
It becomes quickly obvious that there is something odd when the popunder is exposed. We notice some scrolling back and forth and somewhat randomly which truly mimics what a human would do when reading an article. When looking at the code we can see that it checks for user activity (more on that later) and only performs this scrolling activity if it has not detected real mouse movements on the page:
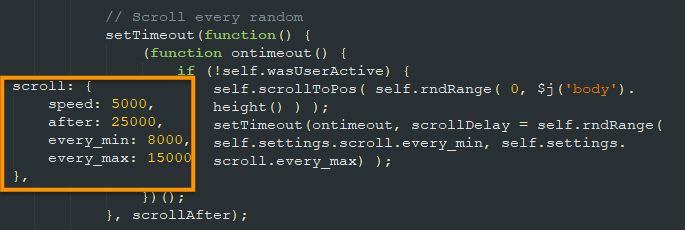
Figure 9: Code for automated scrolling
Had the popunder been the same blog without this fake scrolling there would be no reason to suspect mischief. Of course the fraudsters aren’t interested in a static page without any kind of user interaction as their goal is monetization via ads. This invalid traffic needs to look as valid as possible in order to not get flagged by anti ad fraud solutions:
Figure 10: Animation showing automated scrolling
Another interesting aspect of this fraud is how at regular intervals, a new article is being viewed. This makes sense in the context of a standard visitor to a blog continuing on the site by following other articles that they might be interested in reading. Looking at the fuser-master’s code, we see that it tries to get all internal URLs from the currently loaded page and places these links into an array. If we observe what’s happening, see that after a certain number of scrolling up and down, a different article gets loaded and the scrolling resumes. This fake activity could last from minutes to hours, until it is interrupted by the real human who’s currently at their computer.
Freeze game
At some point, the real user will close their browser or the page that was in front of the popunder. When that happens, all fake activity suddenly stops and the blog becomes static. This is a clever trick to avoid suspicion and reminds us of the ‘freeze’ game kids play. The fraudsters are able to detect when the mouse is being placed over the current page and can quickly stop the code from running.
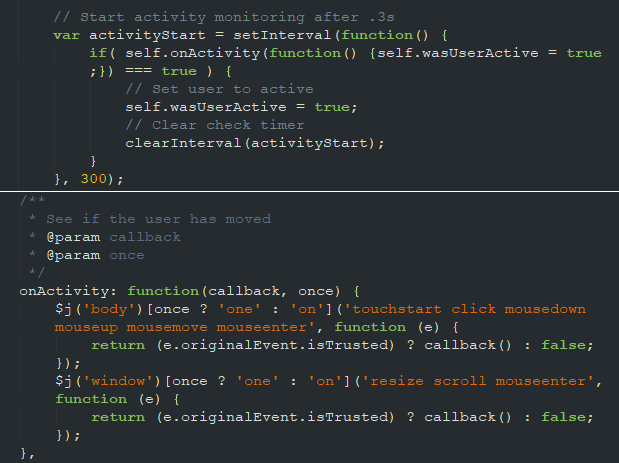
Figure 11: Monitoring for real user activity
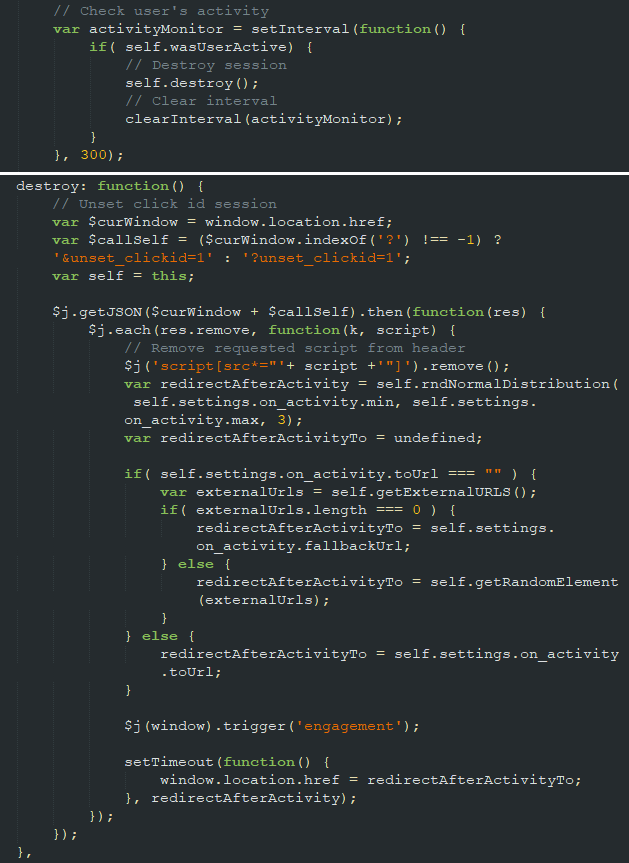
Figure 12: Stopping fake activity after real user is detected
Same web developer built those blogs
Looking through the Internet Archive, we identified an Indian web developer behind several of these sites. Some of the older posts were written by him and the layout such as the scroll bar style and test ads are also identical. There is nothing that definitely proves that this web developer created the ad fraud plugin although he had the technical skills to do so and based on his community WordPress identity was involved in a number of posts about various SEO plugins.
Figure 13: Demo blog using a similar template reused elsewhere
In addition, his own business website also features those blogs in his portfolio and while hovering over the thumbnails we can’t help but notice a scrolling technique very similar to what we saw previously with the ad fraud.
Figure 14: Portfolio showcasing some of the blogs
We contacted one of his supposed customers to let them know about the fuser-mater plugin running on their site. While we did not hear back from them, within about an hour the plugin had been removed from their WordPress installation.

Figure 15: Fuser-master plugin was deleted shortly after our notification
If the web developer wanted to earn from this ad fraud scheme, he would need to have his own publisher IDs and overwrite the ones used by his customers, however we could not immediately verify that this was the case. It’s also possible that the plugin is sold as an “add-on” and that some of his customers are fully aware of it, but we could not prove that either.
Contrary to the previous ad fraud case we looked at, this one does not simply use Google ads. Instead they are going through a number of ad platforms which makes their publisher ID and potential revenue more difficult to figure out. We do know that one of the websites featured in this investigation (momplaybook[.]com) had 3.8 million visitors in January, spending an average of 24 minutes and looking at 17 pages on the site (stats by SimilarWeb).
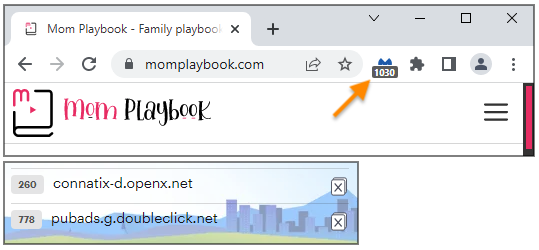
Figure 16: Malwarebytes Browser Guard
Visiting that same website, Malwarebytes Browser Guard blocked over a thousand ad trackers after a few minutes of sitting idle on the main page. The majority of requests came from Google’s DoubleClick and OpenX which we have informed.
Conclusion
Popunders are an ad format that is highly susceptible to abuse. For ad fraud in particular, popunders allow websites to be loaded and serve ads that will never be viewed by real humans.
The plugin we identified during this investigation is relatively simple and allows anyone with an ordinary WordPress blog to increase their earnings dramatically. Because regular visitors will come to the blog via a different flow (standard search or referral link), none of the fraudulent behaviors will be shown. All that is needed is to purchase ad space via a large popunder distributor and use the special entry point URL that triggers the fuser-master plugin.
We have shared details about this invalid traffic case with other partners in the industry.
Indicators of Compromise
momplaybook[.]com geekextreme[.]com femme4[.]com mealplays[.]com dorkfuel[.]com automobilenews[.]net thedailycute[.]com beingexpat[.]com klinkeltown[.]com tidbitsofexperience[.]com lostmeals[.]org bakedoccasions[.]com bakedoccasions[.]com brightsidebeauty[.]com cookbooksandkids[.]com bowlsunset[.]com thereporterz[.]com basicguru[.]com bonafidepress[.]com geeksdigest[.]com hairstylesideashub[.]com techlivewire[.]com thecryptosyndicate[.]com theframeloop[.]com thegamershub[.]co[.]uk fastmint[.]com gordigecr[.]it techlivewire[.]com bonafidepress[.]com chaosandkiddos[.]com geekandtech[.]com geeksdigest[.]com rec-canada[.]com madassgamers[.]com cravecanada[.]com travelnicer[.]com geartaxi[.]com berrry[.]com buytechstuff[.]com pagehabit[.]com techcola[.]com techdeed[.]com rebelgamejam[.]com leftrightpolitics[.]com followthatbitcoin[.]com










