In this series of posts, we will be using the flowchart below to follow the process of determining which adware we are dealing with. Our objective is to give you an idea of how many different types of adware are around for Windows systems. Though most are classified as PUPs, you will also see the occasional Trojan or rootkit, especially for the types that are more difficult to detect and remove.
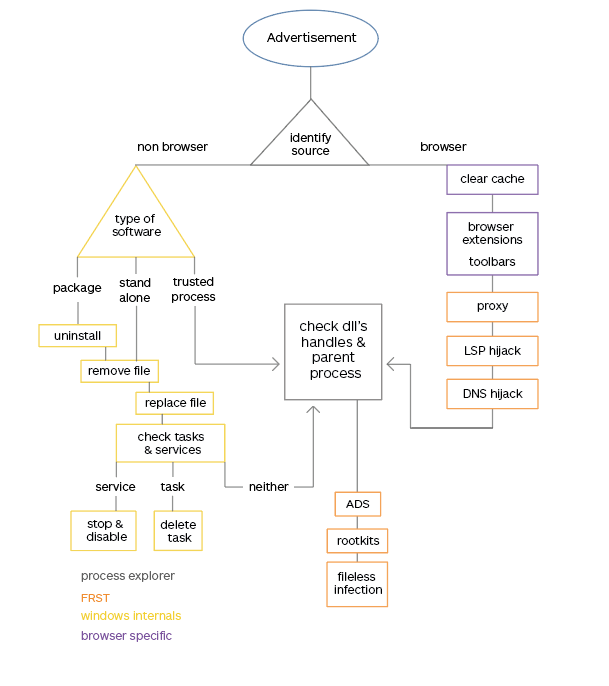
Getting rid of files
In this post, we will discuss several methods to remove the files responsible for showing you the offending advertisements in those cases where the identified process is not a browser.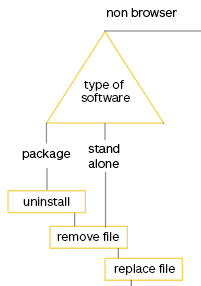
Uninstall
With many PUPs and sometimes even more intrusive adware, uninstalling the program that is showing you the advertisements will be enough. If this works it’s often the cleanest and easiest method to get rid of the advertisements. Identifying which program to uninstall from your list of installed software and features is sometimes the hardest step in this process. Here are a few tips that might help you to do so:- Use your favorite search engine to look for the process name we found to be responsible for the advertisement window. Sometimes this will reveal the name of the software it belongs to and how it’s listed in your list of installed programs and features.
- Sort the list of installed programs and features by date of install. Although this date can easily be spoofed, most software packages in this category won’t. Compare that date to the date when the advertisements first started appearing.
- Warning: in cases where you used a bundler there might be several entries with the same date.
- Use your favorite search engine to look for the entries in your list of installed programs and features that you don’t recognize or remember installing.
Once you have identified the entries you want to remove, select them by clicking on the line in the list, and click on Uninstall. “>
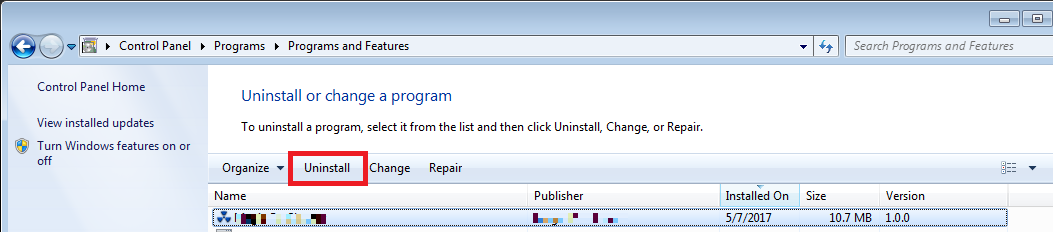
It may be necessary to reboot the system for the changes to take effect. If this solves the problem, great. If not, keep reading.
Delete the file
If the advertisements don’t stop after trying the user-friendly approach outlined earlier, your next step is to delete the file which is responsible for the advertisements. This is much less a clean solution as it might leave more clutter behind. There are several methods that can be used and I will try to list them according to stubbornness. But first, we need to find the file. Since we already used Process Explorer to identify the process, we will also use it to locate the file. Right-click on the selected process and choose Properties and look at the Image tab to see the full path to the file.
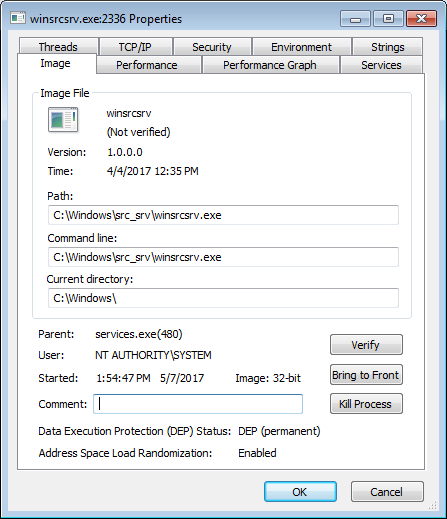
Make a note of the path as we will need that later on. Then close the properties window and right-click the selected process once more. This time use the Kill Process Tree option and confirm that you want to kill this process (and if applicable the ones under it). If the process respawns immediately or Process Explorer (running elevated) is unable to kill it, you will have to wait for other parts in this series. If the process dies you can proceed with the deletion methods below.
- Easy: navigate to the file path you made a note of earlier, right-click the file and choose Delete.
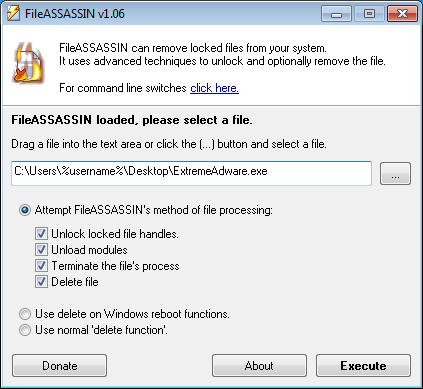
- If that doesn’t work, there is always FileASSASSIN, but you will have to be 100% sure about the file you are going to remove.
- Download and install FileASSASSIN following the prompts.
Browse to the file you want to delete, check all the upper boxes as shown below and click Execute.
Note that the last part just is the destination folder, there is no need to specify the filename and extension again.”>
If all of the above do not work for you, you may have to wait for the post that deals with rootkits. See you later. And stay safe out there.
Index
Part 1
- Identify the process
- Clear browser caches
- Remove browser extensions
Part 2
- Proxies
- Winsock hijackers
- DNS hijackers
Part 3
- Type of software
- Uninstall
- Remove file
- Replace file
Up next, part 4
- Scheduled tasks
- Services
Pieter Arntz











