In the April 2023 Android security bulletin, Google announced security updates which include fixes for two critical remote code execution (RCE) vulnerabilities and one vulnerability that has been exploited in the wild. The vulnerabilities are impacting Android systems running versions 11, 12, 12L, and 13. Users should update as soon as they can.
What needs to be done
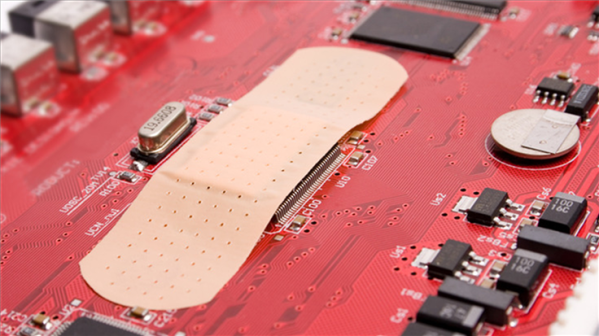
If your Android is on security patch level 2023-04-05 or later, this will address all of these issues. Android partners are notified of all issues at least a month before publication, however this doesn’t always mean that the patches are available for devices from all vendors.
You can find your Android’s version number, security update level, and Google Play system level in your Settings app. You should get notifications when updates are available for you, but you can also check for updates.
For most phones it works like this: Under About phone or About device you can tap on Software updates to check if there are new updates available for your device, although there may be slight differences based on the brand, type, and Android version of your device.
Two critical vulnerabilities
Google never discloses a lot of details about these vulnerabilities. Access to bug details and links are usually restricted until the majority of users are updated with a fix. Here’s what we know so far:
CVE-2023-21085: A vulnerability in the System component which allows a remote attacker to execute arbitrary code. The vulnerability exists due to improper input validation within the System component. A remote attacker can trick the victim to open a specially crafted file and execute arbitrary code.
When a program is unable to perform a proper verification of input, using unintended input can influence program data flow handling. Attackers can abuse this by creating input data that can cause changes of control flow, arbitrary control of a resource, or arbitrary code execution.
CVE-2023-21096: Another vulnerability in the System component which allows a remote attacker to execute arbitrary code. The vulnerability exists due to improper input validation within the System component. A remote attacker can trick the victim to open a specially crafted file and execute arbitrary code.
One vulnerability exploited in the wild
CVE-2022-38181: A vulnerability in the Arm Mali GPU kernel driver allows unprivileged users to access freed memory because GPU memory operations are mishandled. This use-after-free (UAF) vulnerability allows a local application to escalate privileges on the system. A local application can trigger memory corruption and execute arbitrary code with elevated privileges. This vulnerability is known to be exploited in targeted attacks and was first spotted in November 2022.
UAF is a type of vulnerability that is the result of the incorrect use of dynamic memory during a program’s operation. If, after freeing a memory location, a program does not clear the pointer to that memory, an attacker can use the error to manipulate the program. Referencing memory after it has been freed can cause a program to crash, use unexpected values, or execute code. By using dynamic memory allocated to a program with higher privileges, the attacker can use those privileges to execute his code.
We don’t just report on vulnerabilities—we identify them, and prioritize action.
Cybersecurity risks should never spread beyond a headline. Keep vulnerabilities in tow by using Malwarebytes Vulnerability and Patch Management.