Ransomware attacks are becoming more frequent and costlier—breaches caused by ransomware grew 41 percent in the last year, the average cost of a destructive attack rising to $5.12 milllion. What’s more, a good chunk of the cyber criminals doing these attacks operate on a ransomware-as-a-service (RaaS) model.
RaaS is not much different, in theory, from the software-as-a-service (SaaS) business model, where cloud providers “rent out” their technology to you on a subscription basis—just swap out ‘cloud providers’ with ‘ransomware gangs’ and ‘technology’ with ransomware (and the related crimes involved).
In this post, we’ll talk more about how RaaS works, why it poses a unique threat to businesses, and how small-and-medium-sized (SMBs) businesses can prepare for the next generation of RaaS attacks.
How does ransomware-as-a-service work?
How ransomware-as-a-service changed the game
Why ransomware-as-a-service attacks are so dangerous
Is ransomware here to stay? The evolution of RaaS attacks
How SMBs can protect themselves against next-gen RaaS
The perfect one-two combo for fighting RaaS
How does ransomware-as-a-service work?
Don’t get it twisted: RaaS gangs aren’t your run-of-the-mill hackers looking to score a few hundred bucks. We’re talking big, sophisticated businesses with up to a hundred employees—LockBit, BlackBasta, and AvosLocker are just a few of the RaaS gangs we cover in our monthly ransomware review.
“This is run as a business,” says Mark Stockley, Security Evangelist at Malwarebytes. “You’ve got developers, you’ve got managers, you’ve got maybe a couple of levels of people doing the negotiations, things like that. And these gangs have made hundreds of millions of dollars each year in the last few years.”
RaaS gangs like LockBit make money by selling “RaaS kits” and other services to groups called affiliates who actually launch the ransomware attacks. In other words, affiliates don’t need crazy technical skills or knowledge to carry out attacks. By working closely with “Initial Access Brokers” (IABs), some RaaS gangs can even offer affiliates direct access into a company’s network.
How ransomware-as-a-service changed the game
Let’s jump back to the year 2015. These were the “good ol’ days” where ransomware attacks were automated and carried out on a much smaller scale.
Here’s how it went: somebody would send you an email with an attachment, you double-clicked on it, and ransomware ran on your machine. You’d be locked out of your machine and would have to pay about $300 in Bitcoin to get it unlocked. Attackers would send out loads of these emails, lots of people would get encrypted, and lots of people would pay them a few hundred bucks. That was the business model in a nutshell.
But then ransomware gangs sniffed out a golden opportunity.
Rather than attacking individual endpoints for chump change, they realized they could target organizations for big money. Gangs switched from automated campaigns to human-operated ones, where the attack is controlled by an operator. In human-operated attacks, attackers try hard to wedge themselves into a network so that they can move laterally throughout an organization.
At the forefront of this evolution from automated ransomware to human-operated ransomware attacks are ransomware-as-a-service gangs—and their new business model seems to be paying off: in 2021, ransomware gangs made at least $350 million in ransom payments.
Why ransomware-as-a-service attacks are so dangerous
The fact that RaaS attacks are human-operated means that ransomware attacks are more targeted than they used to be—and targeted attacks are far more dangerous than un-targeted ones.
In targeted attacks, attackers spend more time, resources, and effort to infiltrate a businesses network and steal information. Such attacks often take advantage of well-known security weaknesses to gain access, with attackers spending days to even months burrowing themselves in your network.
The human-operated element of RaaS attacks also means that RaaS affiliates can control precisely when to launch an attack—including during times where organizations are more vulnerable, such as on holidays or weekends.
“Famously, RaaS affiliates love long weekends,” Stockley said. “They want to run the ransomware when you’re not going to notice to give themselves however much time they need in order for the encryption to complete. So they like to do it at nighttime, they love to do it during holidays.”
“You’re dealing with a person,” Stockley continued. “It’s not about software running trying to figure everything out; it’s a person trying to figure everything out. And they’re trying to figure out what’s the best way to attack you.”
Is ransomware here to stay? The evolution of RaaS attacks
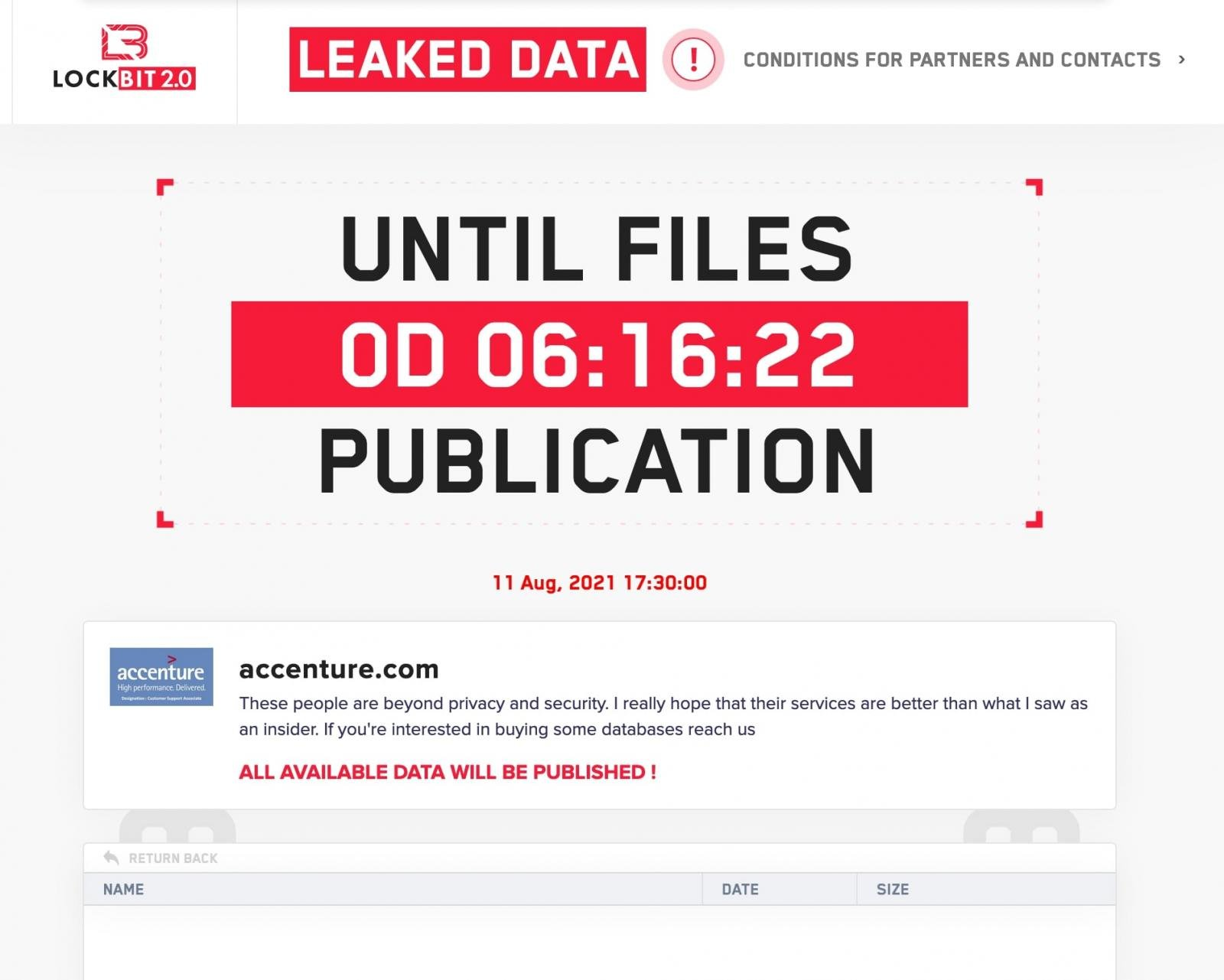
One of the biggest innovations in the RaaS space in recent years has been the use of double extortion schemes, where attackers steal data before encryption and threaten to leak it if the ransom isn’t paid.
Companies have gotten more aware of ransomware and better prepared in terms of things like backups, for example. But if affiliates have already broken into your environment, they can simply use stolen data as extra leverage, leaking bits of it to get your attention, to speed up negotiations, or prove what kind of access they have.
All of the RaaS gangs these days do double extortion, leaking data on dedicated leak websites on the dark web. Many RaaS programs even feature a suite of extortion support offerings, including leak site hosting. Not only is this trend growing, but there’s chatter about whether or not stand-alone data leaking is the next stage in evolution for RaaS.
“There are now gangs that only do data leaking, and they don’t bother doing the encryption at all,” Stockley said. “Because it’s sufficiently successful. And you don’t have to worry about software, you don’t have to worry about software being detected, you don’t have to worry about it running.”
In other words, the evolution from “ransomware-focused” RaaS to “leaking-focused” RaaS means that businesses need to rethink the nature of the problem: It’s not about ransomware per se, it’s about an intruder on your network. The really dangerous thing is turning out to be the access, not the ransomware software itself.
How SMBs can protect themselves against next-gen RaaS
Preparing for RaaS attacks isn’t any different from preparing for ransomware attacks in general, and advice isn’t going to vary all that much across different sized businesses or industries. Because next-gen RaaS is so focused on intrusion, however, SMBs have their own unique challenges in combating it.
Monitoring a network 24/7 for signs of a RaaS intrusion is tough work, period, let alone for organizations with shoe-string budgets and barely any security staff. Consider the fact that, when a threat actor breaches a target network, they don’t attack right away. The median number of days between system compromise and detection is 21 days.
By that time, it’s often too late. Data has been harvested or ransomware has been deployed. In fact, 23 percent of intrusions lead to ransomware, 29 percent to data theft, and 30 percent to exploit activity—when adversaries use vulnerabilities to initiate further intrusions.
Even with tools such as EDR, SIEM, and XDR, sifting through alerts and recognizing Indicators of Compromise (IOCs) is the work of seasoned cyber threat hunters—talent that SMBs just can’t afford. That’s why investing in Managed Detection and Response (MDR) is hugely beneficial for SMBs looking to get a leg-up against RaaS attacks.
“Obviously, the most cost effective thing is to not let people in in the first place. And this is why things like patching, two-factor authentication, and multi-vector Endpoint Protection (EP) are so important,” Stockley said. “But at the point where they’ve broken in, then you want to detect them before they do anything bad. That’s where MDR comes in.”
The perfect one-two combo for fighting RaaS
Human-operated, targeted, and easy to execute, RaaS attacks are a dangerous evolution in the history of ransomware.
Double-extortion tactics, where attackers threaten to leak stolen data to the dark web, are another important evolutionary stage of RaaS campaigns today—to the point where ransomware itself might become obsolete in the future. As a result, SMBs should focus their anti-RaaS efforts on intruder detection with MDR, in addition to implementing ransomware prevention and resilience best practices.
Have a burning question or want to learn more about our cyberprotection? Get a free business trial below.
More resources
Get the eBook: Is MDR right for my business?
Top 5 ransomware detection techniques: Pros and cons of each
Cyber threat hunting for SMBs: How MDR can help
A threat hunter talks about what he’s learned in his 16+ year cybersecurity career












