Results for 'hasherezade'
Look Into Locky Ransomware
March 1, 2016 - Locky is a new ransomware that has been released (most probably) by the Dridex gang (source). Not surprisingly, it is well...
LeChiffre, Ransomware Ran Manually
January 22, 2016 - LeChiffre is yet another ransomware that recently has been observed to cause some major damage (in Mumbai – read more here)....
Ransom32 – look at the malicious package
January 11, 2016 - Ransom32 is a new ransomware implemented in a very atypical style. Emisoft provides a good description of its functionality here. In our post,...
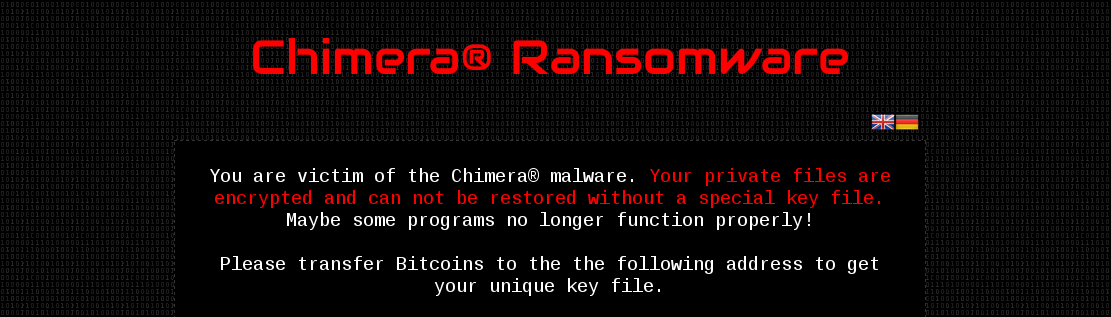
Inside Chimera Ransomware – the first ‘doxingware’ in wild
December 9, 2015 - Ransomware have proven to be a good source of money for cybercriminals. Not surprisingly, we are nowadays facing various families of...
Malware Crypters – the Deceptive First Layer
December 2, 2015 - Recently, two suspects were arrested for selling Cryptex Reborn and other FUD tools (helping to install malware in a Fully UnDetectable way)....
No money, but Pony! From a mail to a trojan horse
November 19, 2015 - In this post, we will take a high and low-level look at the Pony Trojan, delivered through a recent spam campaign. During our...
A Technical Look At Dyreza
November 4, 2015 - In a previous post we presented unpacking 2 payloads delivered in a spam campaign. A malicious duet – Upatre (malware downloader)...
A Week in Security (Aug 02 – Aug 08)
August 11, 2015 - Last week, we saw a fake Android alert that blames Chinese hackers, a peculiar Facebook phishing campaign that is after your...
Rainbows, Steganography and Malware in a new .NET cryptor
August 7, 2015 - This post describes the process of unpacking a malicious payload delivered in a new spam campaign. I often observe malicious samples, distributed...
“Payment Confirmation Slip” Spam Offers Up Malware
August 6, 2015 - Update: We now have an in-depth analysis of this Malware on the blog. There’s a piece of email spam currently in circulation,...