This article is based on research by Marcelo Rivero, Malwarebytes’ ransomware specialist, who monitors information published by ransomware gangs on their Dark Web sites. In this report, “known attacks” are those where the victim did not pay a ransom. This provides the best overall picture of ransomware activity, but the true number of attacks is far higher.
Following a three-month lull of activity, Cl0p returned with a vengeance in June and beat out LockBit as the month’s most active ransomware gang. The group’s 91 attacks come not long after their extensive GoAnywhere campaign in March, when they hit over 100 organizations using a nasty zero-day.
June also witnessed a staggering increase in attacks from relatively new gangs such as Akira (26) and 8Base (41), enough to propel both of them into the top five—a designation usually reserved for more familiar names like ALPHV, who was conspicuously silent in June.
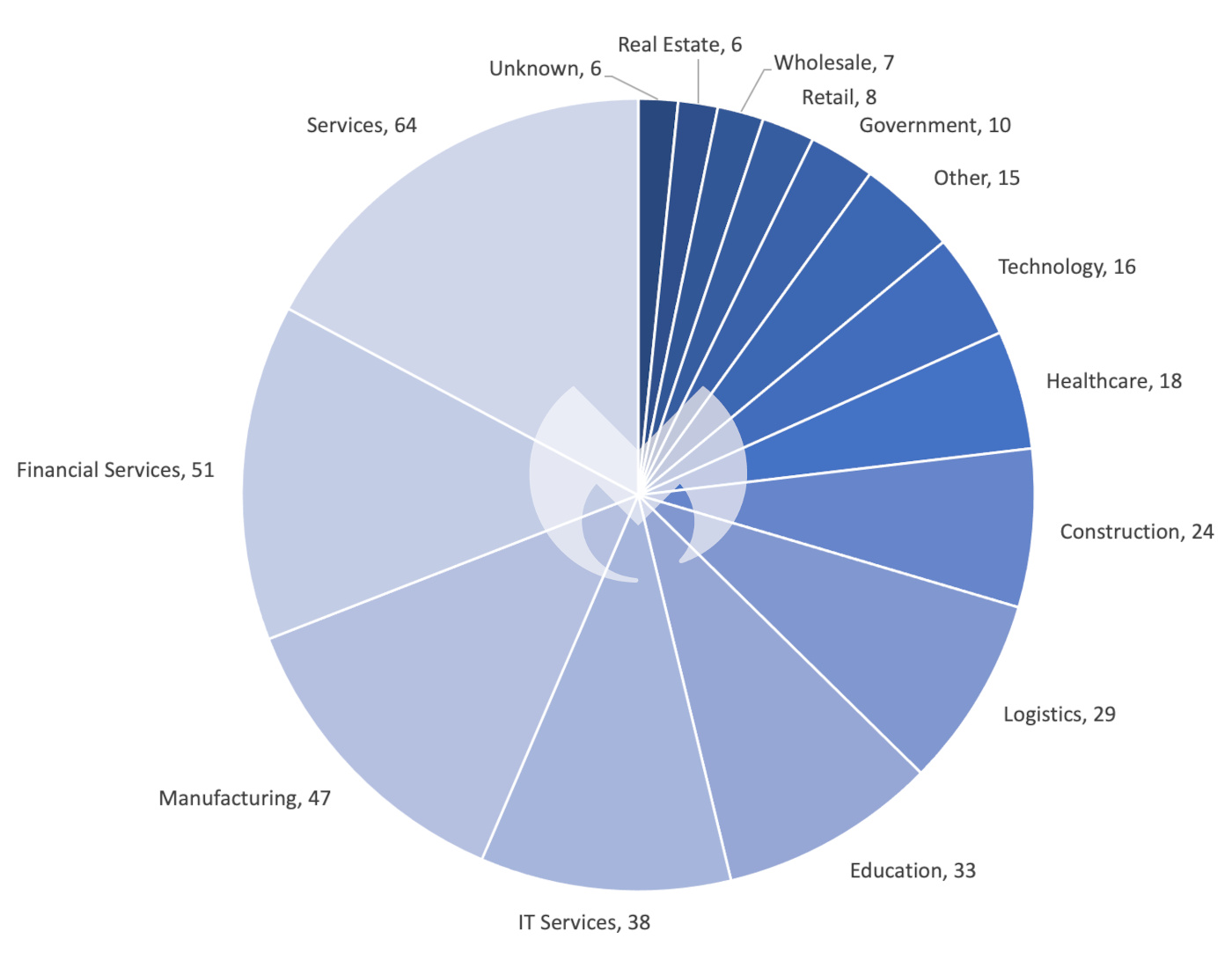
Other big stories in June include a suspected LockBit affiliate arrest, the Royal ransomware gang toying with a new encryptor, and a notable increase in attacks on the Manufacturing sector.
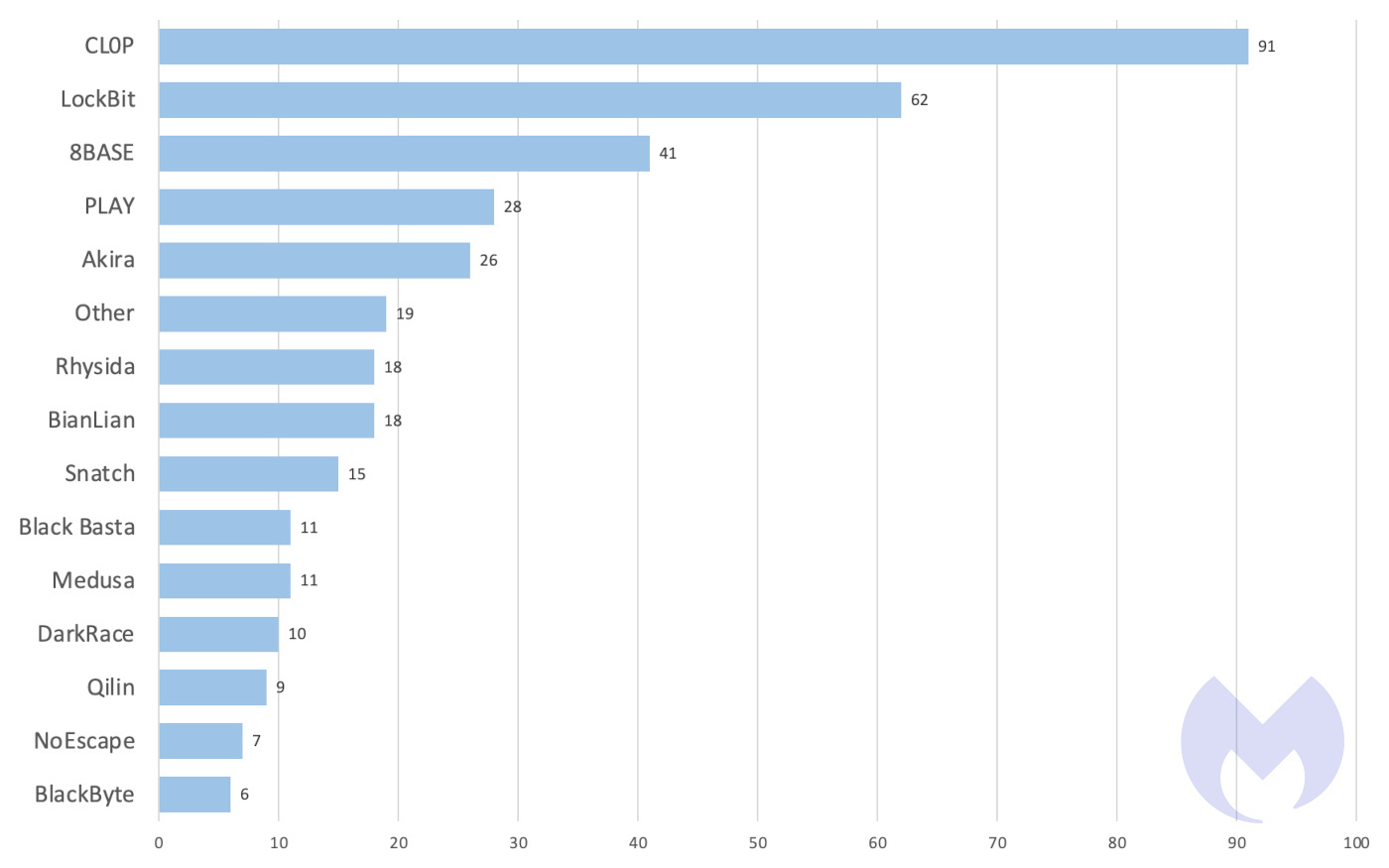
Comparing June to the earlier months of the year, we notice several shifts in ransomware activity. There was a massive decrease in the activity from Royal, for example, which normally dominates the monthly rankings—often cracking into the top five—with an average of roughly 30 attacks a month in that period. But last month, they posted just two victims.
While a sudden dip in attacks isn’t too unusual for top ransomware gangs, it’s worth mentioning that in last month’s review we speculated that Royal might be going through a rebrand. That’s because a new ransomware called BlackSuit had appeared which shared 98 percent of its code with the infamous Royal ransomware.
Considering that both Royal and BlackSuit were active last month, however, a rebrand probably isn’t happening any time soon. Instead, it’s likely that Royal is simply testing a new encryptor—especially considering that BlackSuit was used in just two attacks last month—and that this lull can be explained as more or less of a research period for them.
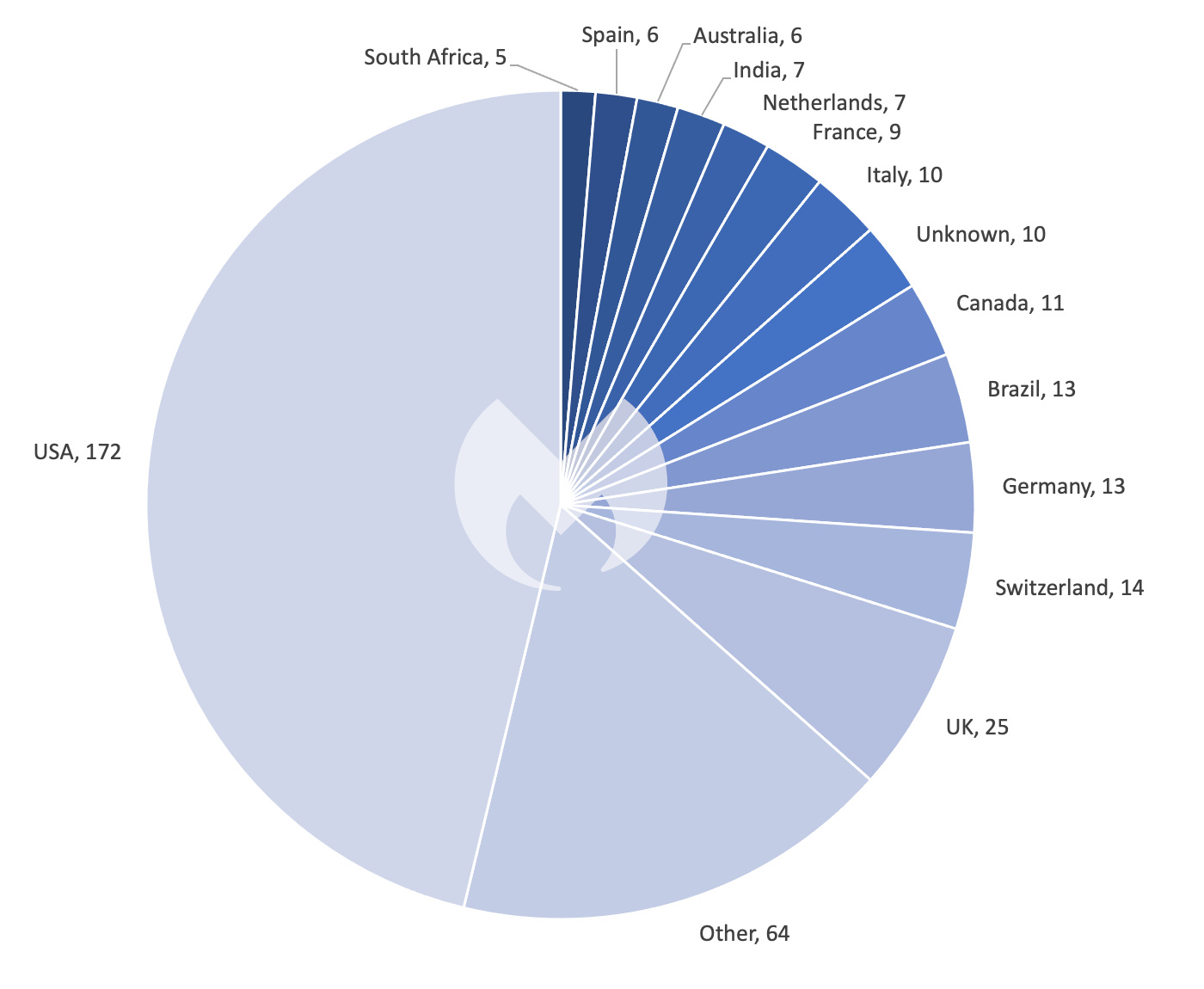
Other interesting anomalies in June include 47 attacks on the Manufacturing industry (which usually averages around 20 attacks a month) and notable increases in attacks on Switzerland (14) and Brazil (13), both of which are normally attacked only two or three times a month. Part of this can be explained by the fact that 8BASE disproportionately attacked Brazil with 11 attacks last month, while PLAY focused on Switzerland (5).
Cl0p’s precipitous rise to the top of the charts this month, on the other hand, can be explained by their exploitation of a zero-day in MOVEit Transfer, a widely used file transfer software.
The vulnerability, which could allow attackers to gain escalated privileges and unauthorized access to an environment, was first disclosed on May 31st in a security bulletin released by Progress. But while it was clear earlier on that attackers were actively exploiting CVE-2023-34362, it was only a few days later that it became clear that Cl0p was behind the attacks. A Cl0p representative confirmed that they had been testing the vulnerability since July 2021 and that they had decided to deploy it over the Memorial Day weekend. What’s more, two other vulnerabilities in MOVEit were found while new victims were still coming forward.
In terms of the fallout, it’s tough to overstate the havoc Cl0p was able to wreck thanks to the zero-day.
The MOVEit data breaches had widespread impacts, affecting everything from the Oregon DMV and Louisiana OMV (Office of Motor Vehicles)—including the leak of nearly 10 million drivers’ licenses—to the University of Rochester and multiple corporations. PBI Research Services also reported a data breach that exposed information for 4.75 million people. The government even offered a reward of up to $10 million for information on Cl0p after several federal agencies in the US fell victim to the gang.
LockBit
LockBit reportedly squeezed about $91 million out of US organizations with around 1,700 attacks since 2020, according to a June report by CISA. As confirmed by our own research data, CISA also found LockBit took the top spot as the biggest global ransomware threat in 2022.
As for who was hit the hardest, around 16 percent of ransomware incidents affecting State, Local, Tribal, and Tribunal (SLTT) governments were from LockBit, says the MS-ISAC.
In other news, a suspected LockBit affiliate named Ruslan Magomedovich Astamirov, a 20-year-old from the Chechen Republic, was arrested in Arizona last month. The US Justice Department thinks he’s been deploying LockBit ransomware on victim networks both in the States and overseas, with the investigation having run from August 2020 through March 2023.
Astamirov is now facing charges of wire fraud and of intentionally damaging protected computers, plus he’s accused of making ransom demands through deploying ransomware. The arrest makes him the third LockBit affiliate charged in the US since November.
Newcomers
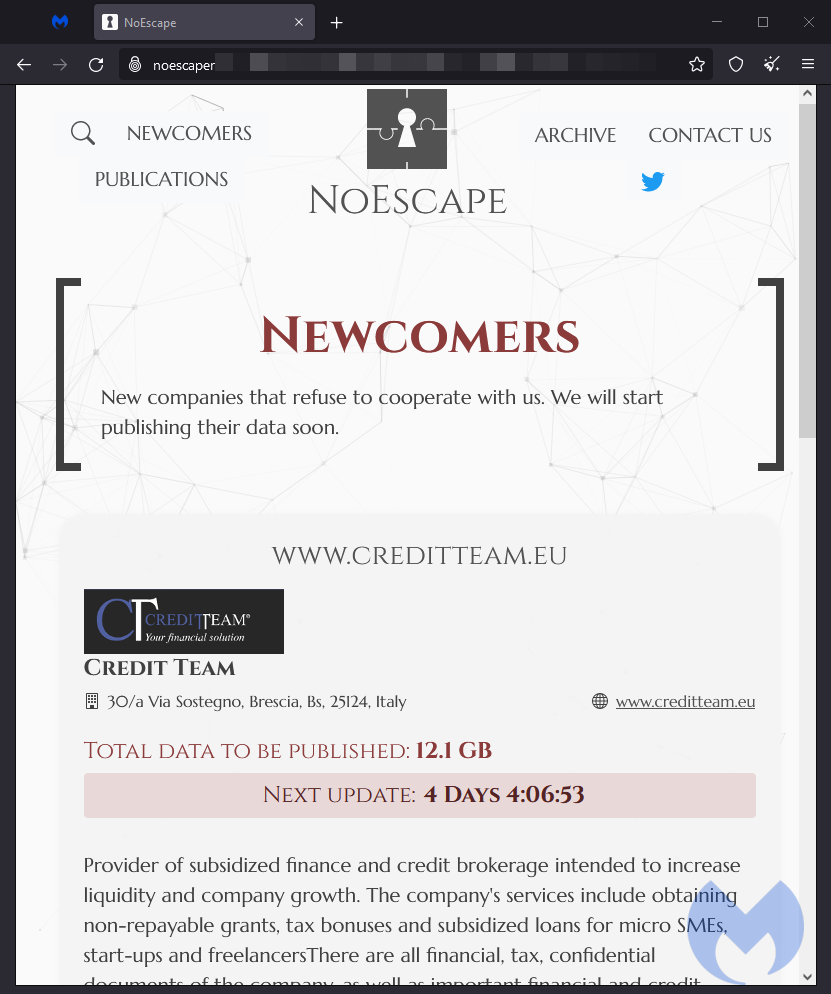
NoEscape
NoEscape is a new ransomware which been doing the rounds in underground forums since May 2023. Developed in-house using C++, the NoEscape ransomware uses a hybrid approach to encryption, combining ChaCha20 and RSA encryption algorithms for file encryption and key protection.
Last month, NoEscape posted 7 victims on their leak site.
Darkrace
DarkRace is a new ransomware group first discovered by researcher S!Ri. Darkrace specifically targets Windows operating systems and has several similarities to LockBit.
The gang attacked 10 victims last month, the majority of them being from the Information and Communications Technology (ICT) sectors. Geographically, most victims are located in Europe, specifically Italy.
Rhysida
Rhysida, a new ransomware gang claiming to be a “cybersecurity team,” has been in operation since May 17, 2023, making headlines for their high-profile attack against the Chilean Army.
The gang published a whopping eighteen victims on their leak site in June, making it one of the most prolific newcomers in our month reviews to-date.










