With rising energy costs and increased volatility in the value of cryptocurrencies, we were bound to see a rise in malicious cryptomining, aka cryptojacking. If you don’t know whether you will ever see a return on your investments in mining equipment, one will look for other opportunities. But if you are a threat actor, you can use other people’s resources to mine your cryptocurrency. No investment, and if the number of mining bots is high enough, there might be some worthwhile profit.
Detection
Keeping the number of bots that are secretly being used for mining means that cybercriminals will have to maintain a low profile on the affected machines. Rendering a device useless for the owner will cause that user to investigate, which could result in that user removing the sneaky miner from their machine.
File detections, whether based on running executables or browser extensions, will have the same effect. Once a miner is detected by one or more popular anti-malware programs, a cyberthief will quickly see their army of miners diminish. Looking at our top 10 malware of last month, you will notice that RiskWare.BitCoinMiner and Trojan.BitCoinMiner are regulars in the top 10 of (Windows) malware that we blocked.
Fileless
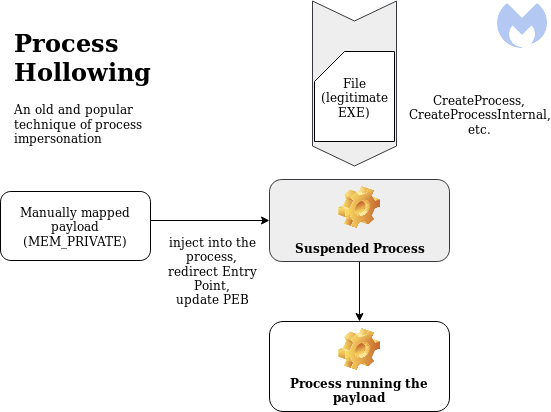
The workaround that some cybercriminals find for averting file detection is to make their malware fileless. Unlike traditional malware, which relies on a file being written to a disk, fileless malware is intended to be memory resident only. In a recent blog post, Microsoft differentiates between crypto miners that use legitimate tools and LOLBins.
LOLBins is the abbreviated term for Living Off the Land Binaries. Living Off the Land Binaries are binaries of a non-malicious nature, local to the operating system, that are utilized and exploited by cybercriminals to camouflage their malicious activity.
Notepad
One of the most abused tools for cryptomining is notepad.exe. Using techniques like process hollowing to inject malicious code into legitimate processes like notepad.exe, the cryptomining malware tries to stay below the radar. The malware will create a scheduled task or use other recurring events to start the process hollowing routine.
Detecting fileless malware
There are several ways to detect fileless malware. In their blog post, Microsoft proposes using a hardware-based threat defense, which applies machine learning to low-level CPU telemetry to detect threats. Cryptojackers will typically cause spikes in CPU usage, a phenomenon that will typically cause a user to start an investigation because it slows the system down.
Using behavioral detection methods certainly makes sense, especially in the case of cryptojacking where the behavior of the malware is predictable based on its end goal. But other typical malware behavior like code injection, process hollowing, and creating scheduled tasks will raise warning flags as well.
Other warning signs can be found in the connections that certain processes make, like reaching out to known C2 servers and mining pools. And we can block the connection to websites that use their visitor’s systems for cryptomining without their explicit consent.
Mitigation
Noticing that something is amiss is an important step. Don’t discard constant high CPU usages as a nuisance. It can do some costly damage to your system. It was not built to constantly perform at peak levels.
Cryptojacking can be done locally on the system or in the browser. Knowing the difference can help you remediate the problem, as both methods require different forms of protection.
Any decent anti-malware solution, like Malwarebytes, will provide protection against both methods. You will need to use active protection though. Just scanning your computer’s file system can miss the fileless variants.