QBot, an infostealer-turned-dropper malware, is being successfully dropped onto affected systems, thanks to a zero-day bypass once used by cybercriminals in Magniber ransomware campaigns last month.
In a new phishing campaign discovered by security researcher proxylife (@pr0xylife), campaign operators have switched from using password-protected ZIP files to install the malware to exploiting a Mark of the Web (MotW) zero-day flaw to run a JavaScript (JS) that executes QBot.
This JS file is a standalone file signed with a malformed signature, the exploit. Though the file is downloaded from the internet, it (or other file types) is allowed to run without resistance from the OS, bypassing Microsoft SmartScreen, a security component of Windows Defender, and preventing the MotW security warnings from displaying.
MotW is a Windows technology that warns users of potential harm when downloading and opening a file from the internet or an email attachment. In other words, it’s a safety precaution in the form of a reminder that the user is about to unleash a risky file that might harm their computer.
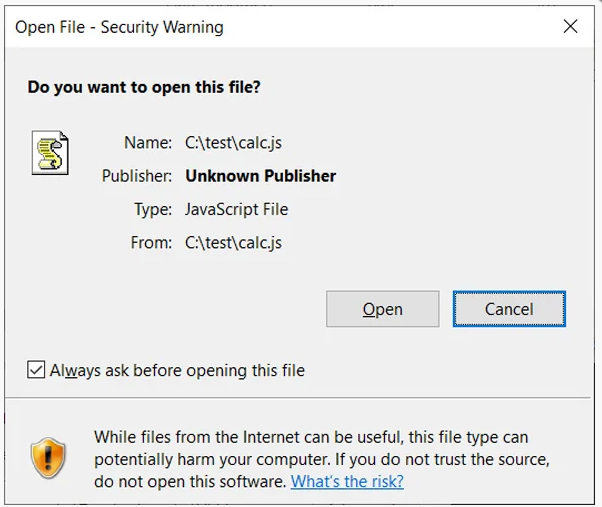
In this sample, the MotW reads:
While files from the internet can be useful, this file type can potentially harm your computer. If you do not trust the source, do not open this software.
According to Bleeping Computer, this QBot phishing campaign starts with an email containing a link to a purported password-protected file.
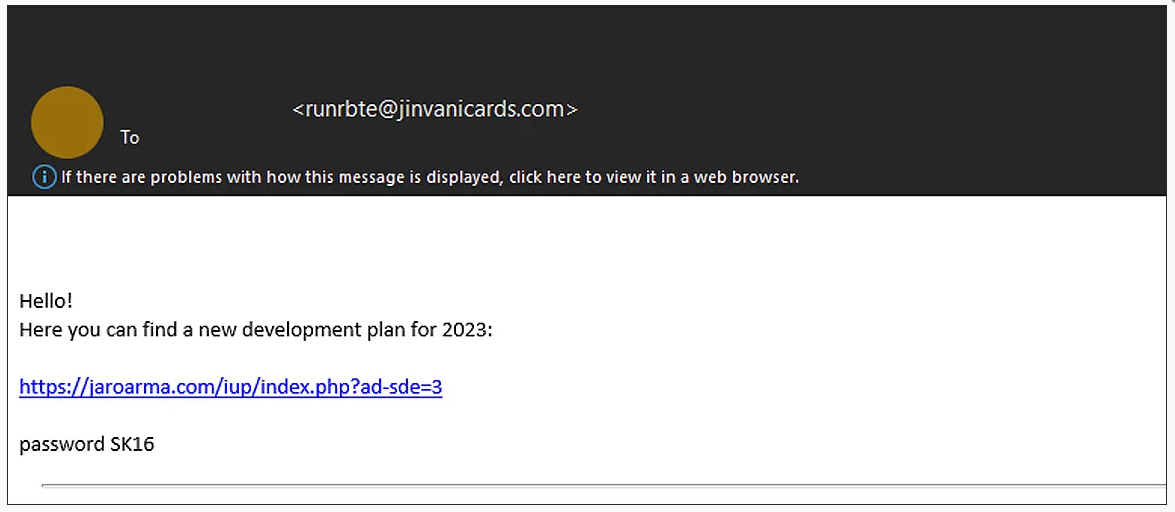
Clicking the link downloads a protected ZIP file containing another ZIP file, which houses a disk image (IMG) file. If you’re using Windows 10 or later, running the file tells the operating system (OS) to mount it as a new drive letter. For example, if the last drive letter on your computer is D, double-clicking the IMG file creates a drive E.
Inside this new drive are a JS file, a text file, and a folder containing a TMP file, which is actually a DLL renamed to a temp file. This is QBot. The JS file contains a script to read the text file and append its contents to a shellexecute command to load the temp file. This will launch QBot with no security warnings.
QBot then injects itself into legitimate Windows processes to evade detection.
As of this writing, Microsoft has yet to release a patch to address the zero-day flaw they’ve known about since October. Hopefully, as cybercriminals take advantage of this MotW exploit, the software giant will have a patch available in the December 2022 Patch Tuesday release.
For now, users need to be picky about where they can download safe and clean files. We also advise caution in downloading and opening files from emails.
Stay safe!
We don’t just report on threats—we remove them
Cybersecurity risks should never spread beyond a headline. Keep threats off your devices by downloading Malwarebytes today.