Which of the myriad, extant cyberthreats should your business be paying the most attention to in 2023?
That’s the question we set out to answer in this year’s annual State of Malware report, and the answers might surprise you. To understand why, you need to know what makes this year’s report so different from previous ones.
Unquestionably, over the last five years, the most serious cybersecurity task facing businesses has changed from defending against waves of malicious, email-borne malware to stopping seasoned criminals armed with Ransomware-as-a-Service (RaaS).
RaaS attacks can be extraordinarily severe. They can bring entire organizations to a halt, come with ruinous ransoms, and may take months of dedicated effort to recover from. They represent an existential threat to businesses.
The worst-of-the-worst is LockBit, the first on our list of the most dangerous threats you face. LockBit’s largest known ransom demand in 2022 was $50 million, although multiple sources report even higher demands were made. Its victims included businesses of all sizes, from local law firms with a handful of employees to multi-national enterprises.
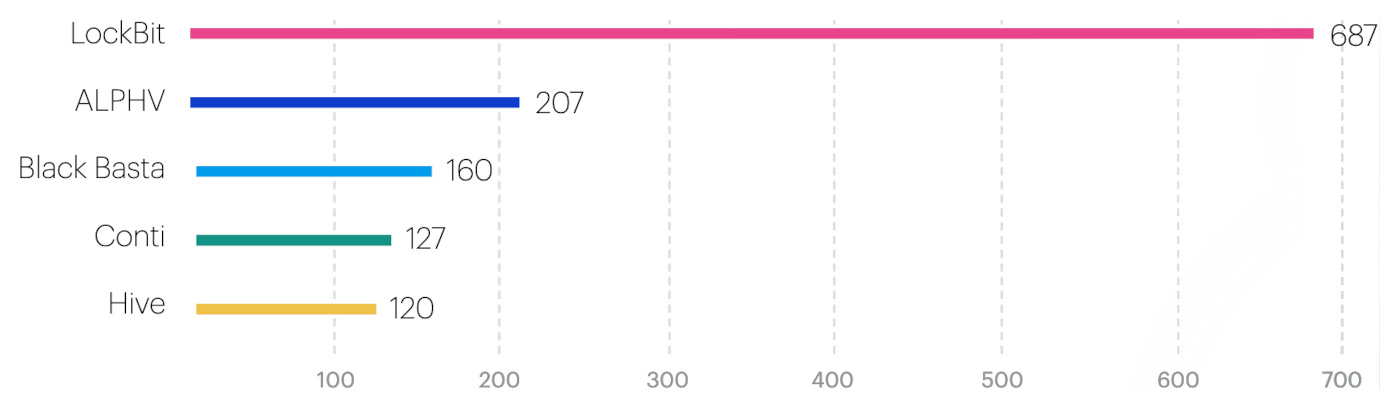
LockBit was the most widely used RaaS in 2022, by far. It accounted for almost a third of all known RaaS attacks, and more than three times as many as its closest competitor, ALPHV.
And yet, if you were to create a list of the most detected malware from last year, you wouldn’t see LockBit on it. In fact, you wouldn’t see any RaaS on it. In cybersecurity, what’s common and what’s serious have diverged markedly.
For that reason, lists of the most detected malware are gone from this year’s report. In their place, we asked our experts—our threat intelligence analysts, and the threat hunters in our Managed Detection and Response (MDR) team: What essential information do resource-constrained organizations need to know?
They came up with a list of the five worst-in-class malware threats spanning Windows, Android and macOS. The report explains what these threats do and why, what it takes to detect them, and what it takes to recover from an attack. Each of our five is an archetype, so if you prepare to stop them, you’re well prepared for anything, on any of your devices.
Compiling our report like this also led us to an important insight: The most dangerous attacks you will face are not from the strangest new malware, the most sophisticated, the most eye-catching, or the most prevalent.
Instead, the most dangerous threats come from a set of known, mature tools and tactics that an entire ecosystem of cybercriminals rely upon to take in billions of dollars a year. Criminals have come to rely upon these attack types and their vectors because they work, and they work because they are hard to defend against and difficult to remove.
The 2023 State of Malware report explains what they are, how they find their victims, and how to avoid becoming one of them.
To learn more about LockBit and how to defend against it, and to discover the four other threats you should prepare for this year, download the 2023 State of Malware report. In it you will also learn:
- What it takes to stop what Europol called the “world’s most dangerous malware.”
- Why there was a 300% increase in some new malware delivery methods.
- How to catch the emerging, hard-to-detect attacks that don’t rely on malware.
- Why security people are as important as security software.










