Quishing is the contraction used by some security vendors for QR code based phishing. Since QR (Quick Response) codes are basically two-dimensional barcodes that hold encoded data, they can be used to work as a link.
But using QR codes has a few advantages for phishers. They are harder to recognize, both by email filters and by the person on the receiving end.
The use of QR codes in malicious campaigns is not new, and because they can provide contactless access to a product or service they grew in popularity during the pandemic.
In August, 2023 we wrote about a campaign that used QR codes to phish for Micrososft credentials. The links in the QR codes used open redirects from legitimate domains associated with Bing, Salesforce, and Cloudflare to send the targets to phishing sites that were after Microsoft credentials. Since the subject of the emails were often spoofed Microsoft security notifications the Bing URLs would not have looked out of place to any victims who looked at them.
So, even upon a quick inspection these links would have looked legitimate to someone inspecting the link before actually visiting the destination. Lately, an increase in the number of this type of phishing emails has been noticed. Both to bring victims to malware infested sites as well as sites phishing for credentials.
The QR codes in these mails can both be embedded or sent as an attachment.
The usual methods are used to make the emails look convincing. The email will pretend to come from a bank or another organization you trust. Some will look like internal mails from your organization, coming for example from HR or the IT-department.
Most of the email contained little to no text. The message is displayed in an image, which helps the email get through email filters.
Example
I personally received a quishing mail pretending to be from the KVK (the Dutch Chamber of Commerce), telling me I had to request a digital key within the next 3 days or my company would be registered as inactive.
As you can see, a lot of the normal signs by which we can recognize a phishing mail are there:
- Urgency
- A link eading to a site to fill out personal information
- Sloppy lay-out of the mail
I was also able to recognize it as false because the sender address didn’t belong to the organization it claimed to be from.
The QR code contained a link to the lihi1.com URL shortener which pointed me to a clone of the KVK site.
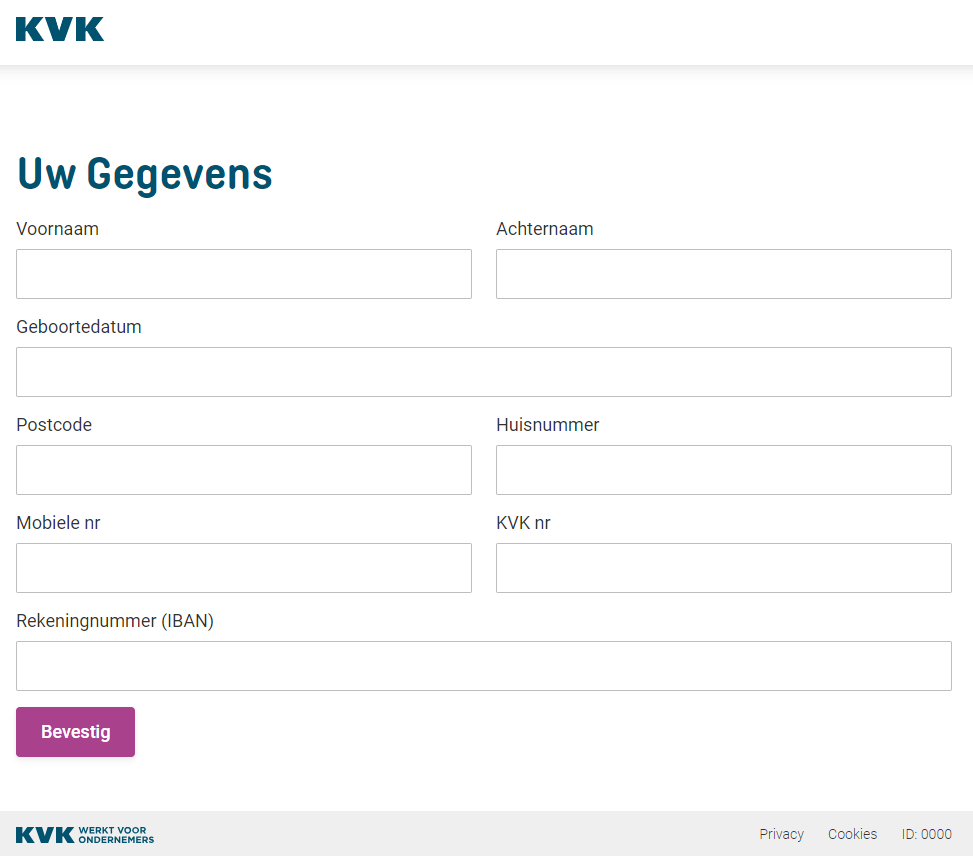
It asked for my name, birth date, address, mobile phone number, my KVK registration number and my bank account number. I’m sure a succesfull phisher can sell such a set of data for a few bucks on the dark web.
To stay safe from quishing, you can follow the same advice we provide for phishing, because that’s what it is. Only the method to obfuscate the URL is a bit more sophisticated, which also makes the use of it more suspicious.
One extra measure you can take is to install a QR code scanner that doesn’t take you to the destination in the URL, but displays it for you, so you can decide whether you want to proceed.
Stay alert for hallmarks of phishing campaigns, such as a sense of urgency and appeals to your emotions. Be extremely wary if a QR code takes you to a site that asks for personal information, login credentials or payment.
We don’t just report on threats—we remove them
Cybersecurity risks should never spread beyond a headline. Keep threats off your devices by downloading Malwarebytes today.











