Google has released an update to Chrome which includes seven security fixes including one for a vulnerability which is known to have already been exploited.
If you’re a Chrome user on Windows, Mac, or Linux, you should update as soon as possible.
The easiest way to update Chrome is to set it to update automatically, but you have to make sure to close your browser for the update to finish. You can also end up on an older, vulnerable version if something goes wrong—such as an extension stopping you from updating the browser.
So, it doesn’t hurt to check now and then. And now would be a good time, given the severity of the vulnerabilities in this batch. My preferred method is to have Chrome open the page chrome://settings/help which you can also find by clicking Settings > About Chrome (on Windows) or Google Chrome > About Google Chrome (on Mac).
If there is an update available, Chrome will start downloading it. Then all you have to do is relaunch the browser in order for the update to complete.
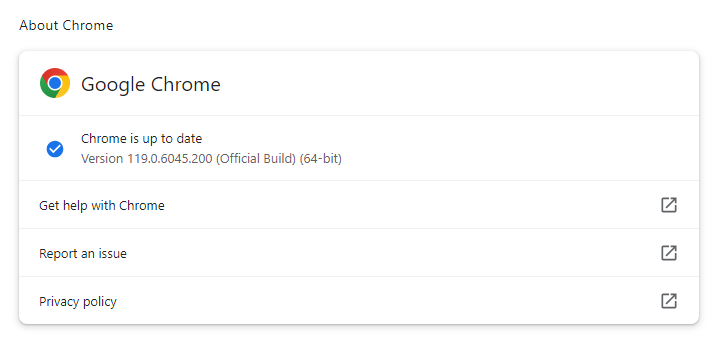
Google Chrome is up to date
After the update, the version should be listed as 119.0.6045.199 for Mac and Linux, and 119.0.6045.199/.200 for Windows, or later.
The technical details
The Common Vulnerabilities and Exposures (CVE) database lists publicly disclosed computer security flaws. The CVE assigned to the actively expoited zero-day is:
CVE-2023-6345: Integer overflow in Skia. Google notes it is aware that an exploit for CVE-2023-6345 exists in the wild. This vulnerability could lead to a range of risks, from crashes to the execution of arbitrary code.
Google never gives out a lot of information about vulnerabilities, for obvious reasons. Access to bug details and links may be kept restricted until a majority of users are updated with a fix, so that interested criminals remain none the wiser.
The fact that the vulnerability is listed with a severity rating of High, indicates that the scope of the flaw is limited to the browser, but this could mean successful exploitation could provide the attacker with information about visited websites and so on.
Skia is an open source 2D graphic library for drawing Text, Geometries, and Images. Skia works across a variety of hardware and software platforms. It serves as the graphics engine for Google Chrome and ChromeOS, Android, Flutter, and many other products.
That’s why users of other Chromium based browsers and software that uses Skia should keep their eyes open for similar updates.
We don’t just report on threats—we remove them
Cybersecurity risks should never spread beyond a headline. Keep threats off your devices by downloading Malwarebytes today.











