The year is 2023 and there still are some people using Internet Explorer on planet Earth. More shocking perhaps, is the fact there are still threat actors maintaining exploit kit infrastructure and dropping new malware.
In this quick blog post, we review two well-known toolkits from the past, namely RIG EK and PurpleFox EK with the latest traffic captures we were able to collect.
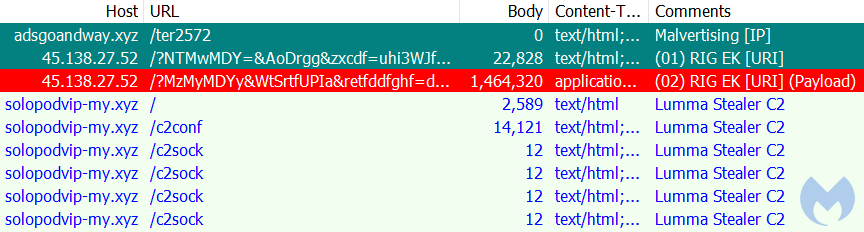
RIG EK
The RIG exploit kit continues to be used by a single threat actor that leverages adult traffic schemes. In this latest instance, it dropped the Lumma Stealer.
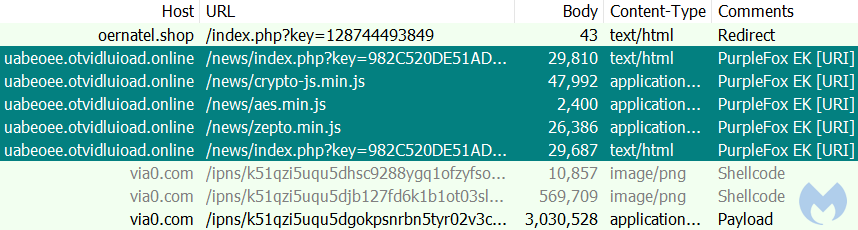
PurpleFox EK
PurpleFox is more than just an exploit kit, it is a complete framework with rootkit capabilities. The exploit kit is one of the delivery mechanisms for the PurpleFox malware.
Thank you to researchers at First Watch Security for providing information on this attack chain.
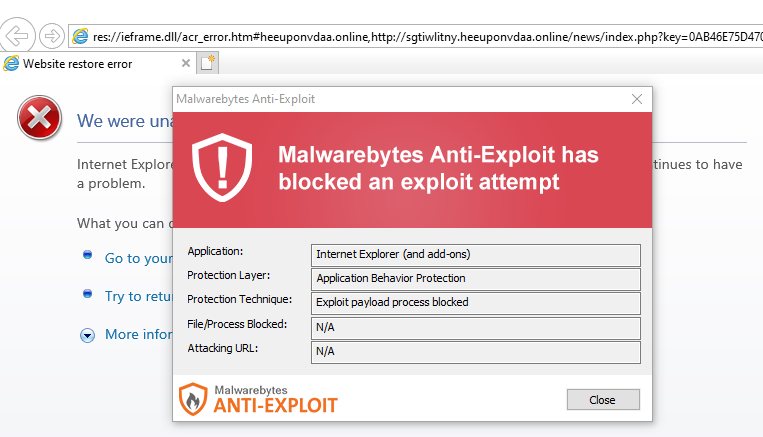
Protection
Even after all these years, Malwarebytes continues to protect agains these exploit kits targeting vulnerabilities in Internet Explorer, the browser no longer supported by Microsoft.
Indicators of Compromise
RIG EK
adsgoandway[.]xyz
45.138.27[.]52
Lumma Stealer payloadd
07e06e8277980a60e595da9cd9e03a4ecd2e8f8bdbd3cf5c930ab878ac5b0836
Lumma Stealer C2
solopodvip-my[.]xyz
PurpleFox EK
oernatel[.]shop
uabeoee.otvidluioad[.]online
via0[.]com
Payload
f627070c4cbb03556896601870cf575b1c8f47b062fdfef5c3516ff5a07db40c










