PUP.Optional.FakeFlash
Short bio
PUP.Optional.FakeFlash is Malwarebytes’ generic detection name for a large family of browser extensions that are installed by websites offering fake Flash updates.
Symptoms
This extension requires permission to show notifications
Type and source of the infection
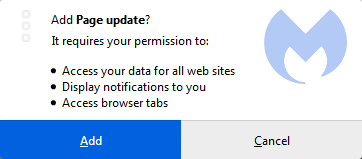
PUP.Optional.FakeFlash extensions are installed by websites where users will be confronted with screens similar to these:
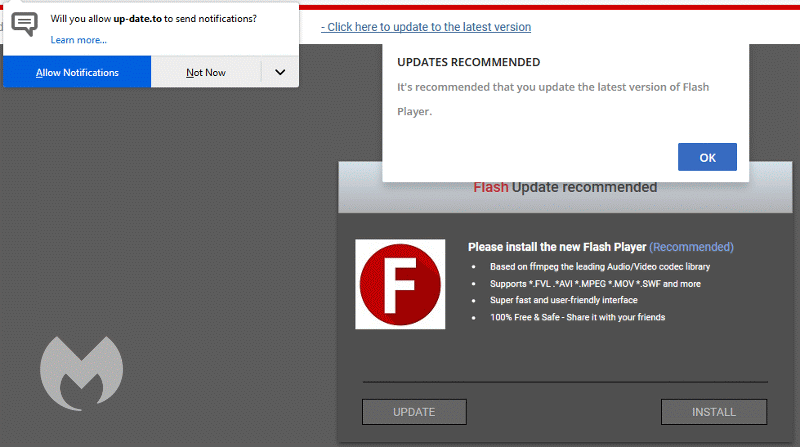
Urging you to allow notifications and/or install a browser extension:

Aftermath
Some of these extensions change your permissions for Push Notifications. Users will have to remove the permissions manually. You can find more information about this procedure in our blogpost called Browser push notifications: a feature asking to be abused.
Protection
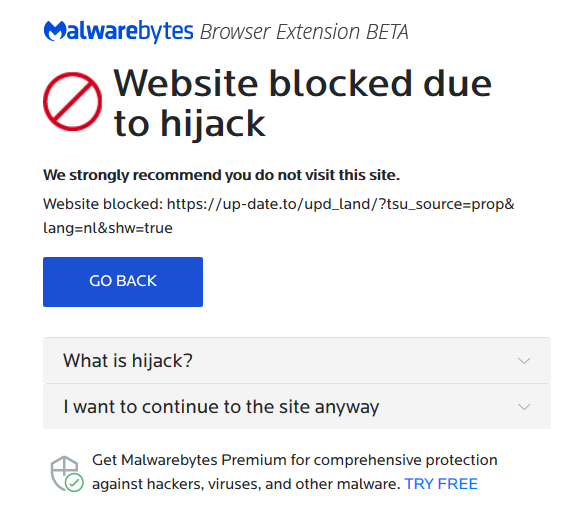
Malwarebytes blocks the malicious website that are known to push PUP.Optional.FakeFlash:
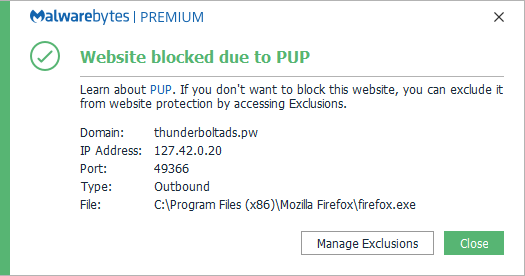
Users of the Malwarebytes browser extensions are protected even before we add the malicious domains to our blocklist.
Remediation
Malwarebytes can detect and remove PUP.Optional.FakeFlash without further user interaction.
- Please download Malwarebytes to your desktop.
- Double-click MBSetup.exe and follow the prompts to install the program.
- When your Malwarebytes for Windows installation completes, the program opens to the Welcome to Malwarebytes screen.
- Click on the Get started button.
- Click Scan to start a Threat Scan.
- Click Quarantine to remove the found threats.
- Reboot the system if prompted to complete the removal process.
Malwarebytes removal log
A Malwarebytes log of removal will look similar to this:
Malwarebytes www.malwarebytes.com
-Log Details- Scan Date: 5/22/19 Scan Time: 8:44 AM Log File: 17980360-7c5d-11e9-857e-00ffdcc6fdfc.json
-Software Information- Version: 3.7.1.2839 Components Version: 1.0.586 Update Package Version: 1.0.10706 License: Premium
-System Information- OS: Windows 7 Service Pack 1 CPU: x64 File System: NTFS User: {computername}\{username}
-Scan Summary- Scan Type: Threat Scan Scan Initiated By: Manual Result: Completed Objects Scanned: 236322 Threats Detected: 1 Threats Quarantined: 1 Time Elapsed: 5 min, 30 sec
-Scan Options- Memory: Enabled Startup: Enabled Filesystem: Enabled Archives: Enabled Rootkits: Enabled Heuristics: Enabled PUP: Detect PUM: Detect
-Scan Details- Process: 0 (No malicious items detected)
Module: 0 (No malicious items detected)
Registry Key: 0 (No malicious items detected)
Registry Value: 0 (No malicious items detected)
Registry Data: 0 (No malicious items detected)
Data Stream: 0 (No malicious items detected)
Folder: 0 (No malicious items detected)
File: 1 PUP.Optional.FakeFlash, C:\USERS\{username}\APPDATA\ROAMING\MOZILLA\FIREFOX\PROFILES\{PROFILE}.DEFAULT\EXTENSIONS\LN_VSOAJKXXXZZ@UDPPPADK.XPI, Quarantined, [1752], [686156],1.0.10706
Physical Sector: 0 (No malicious items detected)
WMI: 0 (No malicious items detected)
(end)
Add an exclusion
Should users wish to keep this program and exclude it from being detected in future scans, they can add the program to the exclusions list. Here’s how to do it.
- Open Malwarebytes for Windows.
- Click the Detection History
- Click the Allow List
- To add an item to the Allow List, click Add.
- Select the exclusion type Allow a file or folder and use the Select a folder button to select the main folder for the software that you wish to keep.
- Repeat this for any secondary files or folder(s) that belong to the software.





