A new macOS malware—called OSX.MacStealer—that is capable of stealing various files, cryptocurrency wallets, and details stored in specific browsers like Firefox, Chrome, and Brave, was discovered by security researchers from Uptycs, a cybersecurity company specializing in cloud security. It can also extract the base64-encoded form of the database of Keychain, Apple’s password manager. Users of macOS Catalina (10.5) and versions dependent on Intel, Apple M1, and Apple M2 are affected by this malware.
And while MacStealer appears to be the mac malware to watch, it is pretty rudimentary, according to Thomas Reed, Malwarebytes’ director of core technology. “There is no persistence method, and it relies on the user opening the app,” he adds, considering the foreseeable features the developer wants to add to MacStealer in the future.
MacStealer uses channels in Telegram as its command-and-control (C2) center. The malware has been promoted on a dark web forum since the beginning of March. According to the developers, it’s still in the early beta stage, thus lacking a builder and panel. These are also why the developers distribute MacStealer as a malware-as-a-service (MaaS), selling at a low price of $100 and promising more advanced features in the future.
MacStealer arrives to target macOS systems as an unsigned disk image (.DMG) file. Users are manipulated to download and execute this file onto their systems. Once achieved, a bogus password prompts users in an attempt to steal their real password. MacStealer then saves the password in the affected system’s temporary folder (TMP).
The malware then proceeds to collect and save the following also within the TMP folder:
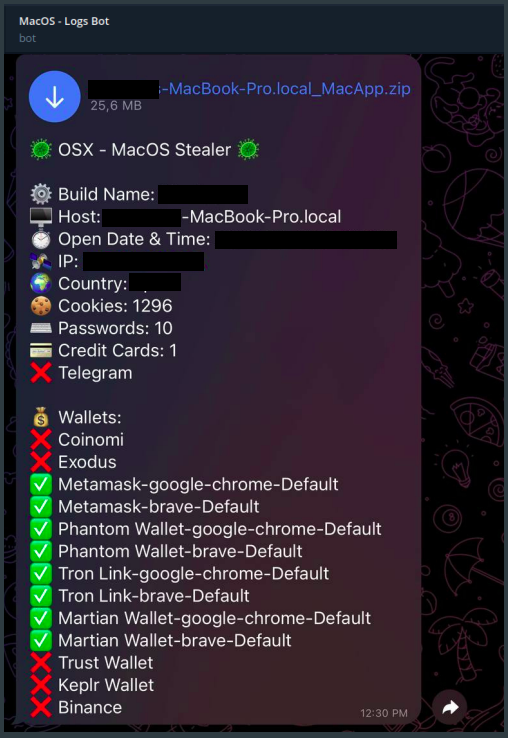
- Account passwords, browser cookies, and stored credit card details in Firefox, Chrome, and Brave
- Cryptocurrency wallets (Binance, Coinomi, Exodus, Keplr Wallet, Martian Wallet, MetaMask, Phantom, Tron, Trust Wallet)
- Keychain database in its encoded (base64)form
- Keychain password in text format
- Various files (.TXT, .DOC, .DOCX, .PDF, .XLS, .XLSX, .PPT, .PPTX, .JPG, .PNG, .CVS, .BMP, .MP3, .ZIP, .RAR, .PY, .DB)
- System information in text form
MacStealer also compresses everything it stole in a ZIP file and sends it to remote C&C servers for the threat actor to collect later. At the same time, a summary version of the information it stole is sent to pre-configured Telegram channels, alerting the threat actor that new stolen data is available for download.
MacStealer being an unsigned DMG file is also a barrier for anyone, especially beginners, attempting to run the program on a modern mac, said Malwarebytes’ Reed. “Its attempt at phishing for login passwords is not very convincing and would probably only fool a novice user. But such a user is exactly the type who would have trouble opening it.”
We don’t just report on threats—we remove them
Cybersecurity risks should never spread beyond a headline. Keep threats off your devices by downloading Malwarebytes today.










