The Cybersecurity and Infrastructure Security Agency (CISA) has added a critical unauthenticated remote code execution (RCE) vulnerability in Citrix NetScaler ADC and Citrix NetScaler Gateway to its Known Exploited Vulnerabilities Catalog, based on evidence of active exploitation. This means that Federal Civilian Executive Branch (FCEB) agencies need to remediate this vulnerability by August 9, 2023 to protect their networks against active threats. We urge everyone else to take it seriously too.
The recommended actions are to apply mitigations per vendor instructions or discontinue use of the product if mitigations are unavailable. Given the active exploitation, we would advise to do this as soon as possible.
The Common Vulnerabilities and Exposures (CVE) database lists publicly disclosed computer security flaws. The actively exploited CVE patched in this update is CVE-2023-3519 a Citrix NetScaler ADC and NetScaler Gateway code injection vulnerability with a CVSS score of 9.8 out of 10. The vulnerability can lead to unauthenticated RCE. It affects appliances configured as a Gateway (VPN virtual server, ICA Proxy, CVPN, RDP Proxy) or as an authentication, authorization and accounting (AAA) virtual server.
Little information has been made available about the campaign that is exploiting this vulnerability. What we do know is that the criminals use web shells—a script that can be used by an attacker to run remote commands and maintain persistent access on an already compromised system. CISA has released a cybersecurity advisory about the tactics, techniques, and procedures (TTPs) of the currently active campaign.
Reportedly, there are around 38,000 Citrix Gateway appliances exposed to the public Internet and exploits against Citrix ADC have been discussed, including the sale of a Remote Code Execution (RCE) exploit, on a cybercrime forum.
Citrix acknowledges the urgency by stating:
“Exploits of CVE-2023-3519 on unmitigated appliances have been observed. Cloud Software Group strongly urges affected customers of NetScaler ADC and NetScaler Gateway to install the relevant updated versions as soon as possible.”
The security bulletin by Citrix about this vulnerability includes two more vulnerabilities. The following supported versions of NetScaler ADC and NetScaler Gateway are affected by the vulnerabilities:
- NetScaler ADC and NetScaler Gateway 13.1 before 13.1-49.13
- NetScaler ADC and NetScaler Gateway 13.0 before 13.0-91.13
- NetScaler ADC 13.1-FIPS before 13.1-37.159
- NetScaler ADC 12.1-FIPS before 12.1-55.297
- NetScaler ADC 12.1-NDcPP before 12.1-55.297
Citrix notes that NetScaler ADC and NetScaler Gateway version 12.1 have reached the end-of-life stage and customers should upgrade to a newer variant of the product.
Customers using Citrix-managed cloud services or Citrix-managed Adaptive Authentication do not need to take any action.
Malwarebytes blocks the IP addresses that are known indicators of compromise (IoCs) for the active campaign exploiting this vulnerability.
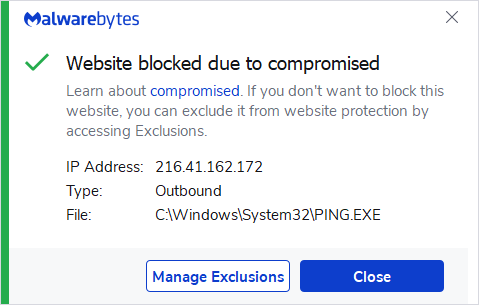
216.41.162.172
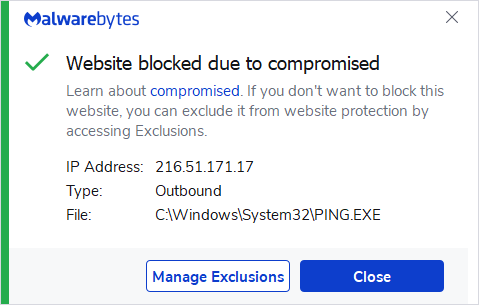
216.51.171.17
For administrators that would like to see whether their instance has been compromised and what they should do about it, I found this checklist.
We don’t just report on vulnerabilities—we identify them, and prioritize action.
Cybersecurity risks should never spread beyond a headline. Keep vulnerabilities in tow by using Malwarebytes Vulnerability and Patch Management.











