This time we will have a look at another payload from recent RIG EK campaign. It is Smoke Loader (Dofoil), a…
Tag: hasherezade
Unpacking yet another .NET crypter
In this post, we will study one of the malicious executables recently delivered by RIG Exploit Kit. It is packed in a…
From Locky with love – reading malicious attachments
The common way of malware distribution, used i.e. by Locky ransomware are downloader scripts. They are spread in massive spam campaigns…
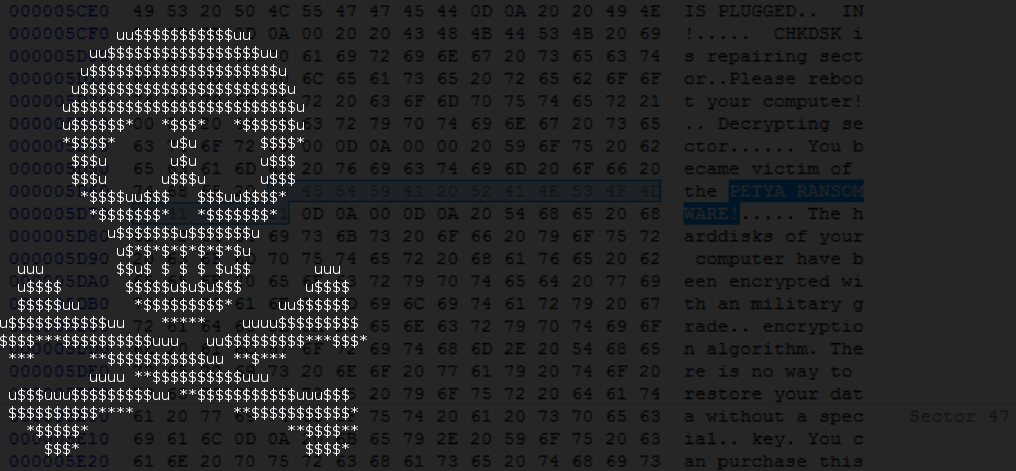
Third time (un)lucky – improved Petya is out
So far we dedicated several articles to the interesting, low-level ransomware called Petya, hijacking the boot sector. You can read about…
Untangling Kovter’s persistence methods
Kovter is a click-fraud malware famous from the unconventional tricks used for persistence. It hides malicious modules in PowerShell scripts as…
Satana ransomware – threat coming soon?
Petya ransomware is quickly becoming a household name and in typical cyber-criminal fashion, copycat families are starting to emerge. In this post, we have…
Petya and Mischa – Ransomware Duet (Part 1)
After being defeated about a month ago, Petya comes back with new tricks. Now, not as a single ransomware, but in…
Petya – Taking Ransomware To The Low Level
Petya is different from the other popular ransomware these days. Instead of encrypting files one by one, it denies access to…
A Technical Look At Dyreza
In a previous post we presented unpacking 2 payloads delivered in a spam campaign. A malicious duet – Upatre (malware downloader)…
Unpacking Fraudulent “Fax”: Dyreza Malware from Spam
This post describes the process of unpacking a malware delivered in a spam campaign. The described sample has been delivered on…