This malware came in a phishing e-mail – disguised as a Bitcoin wallet. After clicking the link, user receives a JAR…
Tag: hasherezade
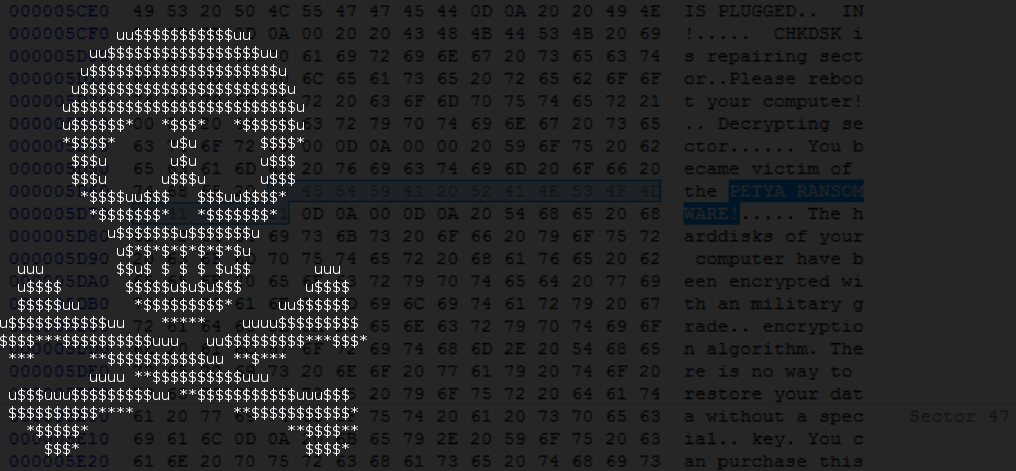
Goldeneye Ransomware – the Petya/Mischa combo rebranded
From March 2016 we’ve observed the evolution of an interesting low-level ransomware, Petya – you can read about it here. The second…
Simple userland rootkit – a case study
Rootkits are tools and techniques used to hide (potentially malicious) modules from being noticed by system monitoring. Many people, hearing the…
PrincessLocker – ransomware with not so royal encryption
PrincessLocker ransomware has appeared some time ago and has drawn out attention by using the same template of the site for…
Floki Bot and the stealthy dropper
Floki Bot, described recently by Dr. Peter Stephenson from SC Magazine, is yet another bot based on the leaked Zeus code. However,…
Introducing TrickBot, Dyreza’s successor
Recently, our analyst Jérôme Segura captured an interesting payload in the wild. It turned out to be a new bot that,…
Lesser known tricks of spoofing extensions
It is a well-known fact that malware using social engineering tricks is designed to hide itself from being an obvious executable….
Unpacking the spyware disguised as antivirus
Recently we got access to several elements of the espionage toolkit that has been captured attacking Vietnamese institutions. During the operation,…
Shakti Trojan: Technical Analysis
Recently, we took a look at the interesting Trojan found by Bleeping Computer. Our small investigation on its background and possible…
Decrypting Chimera ransomware
We’ve recently wrote about the leak of keys for Chimera ransomware. In this, more technical post, we will describe how to utilize…