Results for 'cerber'
A week in security (October 21 – 27)
October 28, 2019 - Last week on Malwarebytes Labs, we explored a link between Magecart Group 5 and the Carbanak APT, we discussed the growing...
Helping survivors of domestic abuse: What to do when you find stalkerware
July 1, 2019 - We’re going to talk about something different today. We’re going to talk about domestic abuse. Earlier this year, cybersecurity company Kaspersky...
Magniber ransomware improves, expands within Asia
July 16, 2018 - This blog post was authored by @hasherezade and Jérôme Segura. The Magnitude exploit kit is one of the longest-serving browser exploitation...
Magnitude exploit kit switches to GandCrab ransomware
April 17, 2018 - The GandCrab ransomware is reaching far and wide via malspam, social engineering schemes, and exploit kit campaigns. On April 16, we...
Napoleon: a new version of Blind ransomware
December 8, 2017 - The ransomware previously known as Blind has been spotted recently with a .napoleon extension and some additional changes. In this post,...
A week in security (October 16 – October 22)
October 23, 2017 - Last week was an eventful one in security, keeping our research and intel teams on their toes. Multiple security researchers homed...
Magniber ransomware: exclusively for South Koreans
October 18, 2017 - The Magnitude exploit kit has been pretty consistent over the last few months, dropping the same payload—namely, the Cerber ransomware—and targeting...
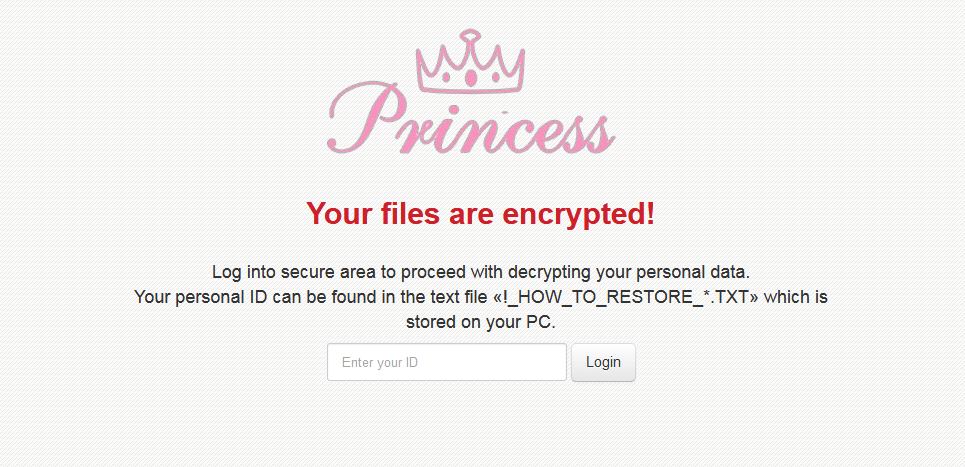
RIG exploit kit distributes Princess ransomware
August 31, 2017 - We have identified a new drive-by download campaign that distributes the Princess ransomware (AKA PrincessLocker), leveraging compromised websites and the RIG...
Malware vaccination tricks: blue pills or red pills
August 30, 2017 - First, let me explain what I mean by malware vaccination tricks. Most of you will have heard about some of these....
Week in Security (August 7 – August 13)
August 14, 2017 - Last week, we explained how security certificates work and how malware authors have used them to block security software from being...