Results for 'Amazon'
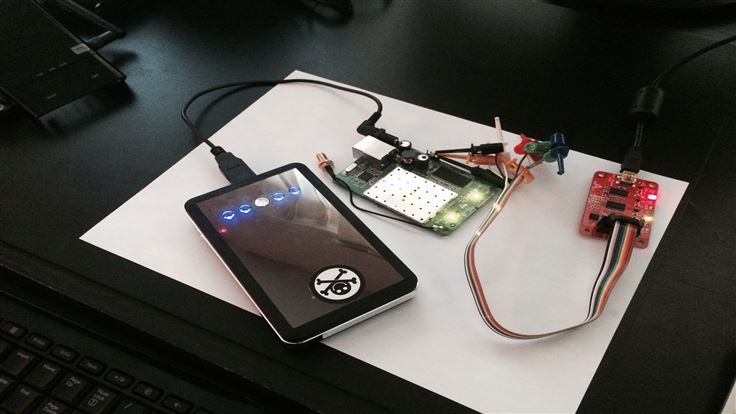
UART, Root Shell On Commercial Devices
February 21, 2014 - Many embedded devices run a stripped down version of Linux and have poorly documented diagnostic interfaces. In order to find potential...
Kindle Apps: Look Before You Leap
February 20, 2014 - With school holidays in the UK slowly winding down (most likely with a cry of “Are they going back in yet”...
Ad2Store redirections: the latest annoyance for mobile users
February 10, 2014 - Online ads can be very aggressive and disruptive, not to mention they often carry malicious payloads aka malvertising. You may have come...
FBI Takes Down Poorly Secured Carders
January 24, 2014 - Operational Security, or OPSEC, is the very core of running any kind of clandestine operations, be it a government or a...
Potentially Unwanted Miners – Toolbar Peddlers Use Your System To Make BTC
November 29, 2013 - Potentially Unwanted Programs or PUPs as we like to call them, are things like Toolbars, Search Agents, etc. Unnecessary junk for...
Hacked and Unpacked: The Piratebox
November 6, 2013 - Some time ago I showcased the Wi-Fi pineapple, a small portable Wi-Fi access point modified with a custom firmware to be used as...
Chrome’s Solution to the Unsavvy Poses A Potential Risk
October 24, 2013 - Don’t get me wrong, I love Chrome, I think it’s a fantastic browser and has a great track record of protecting...
79 percent of mobile malware is directed at Android
September 5, 2013 - In a recent study, the Department of Home Land Security (DHS) and the FBI reported 79 percent of all malware targeting mobile...
Keeping Secure in an Android World
May 25, 2013 - Most of us have moved to mobile computing and use it daily, but we often take security for granted. After all,...
This Christmas time the bad guys will be shopping too
December 17, 2012 - While most folks want a new gaming system, TV, or the latest computer gadget, there is another group of people that...