This article is based on research by Marcelo Rivero, Malwarebytes’ ransomware specialist, who monitors information published by ransomware gangs on their Dark Web sites. In this report, “known attacks” are attacks where the victim opted not to pay a ransom. This provides the best overall picture of ransomware activity, but the true number of attacks is far higher.
Between April 2022 and March 2023, Germany was a globally significant target for ransomware gangs. During that period:
- It was the fourth most attacked country in the world, and the most attacked in the EU
- The construction sector was harder hit than in the USA, UK, or France
- LockBit and Black Basta accounted for 54% of known attacks
- Black Basta attacked targets in Germany far more often than in the UK or France
In August 2022, German power semiconductor manufacturer Semikron disclosed a ransomware attack that had partially encrypted its network, with the attackers claiming to have stolen 2TB of documents.
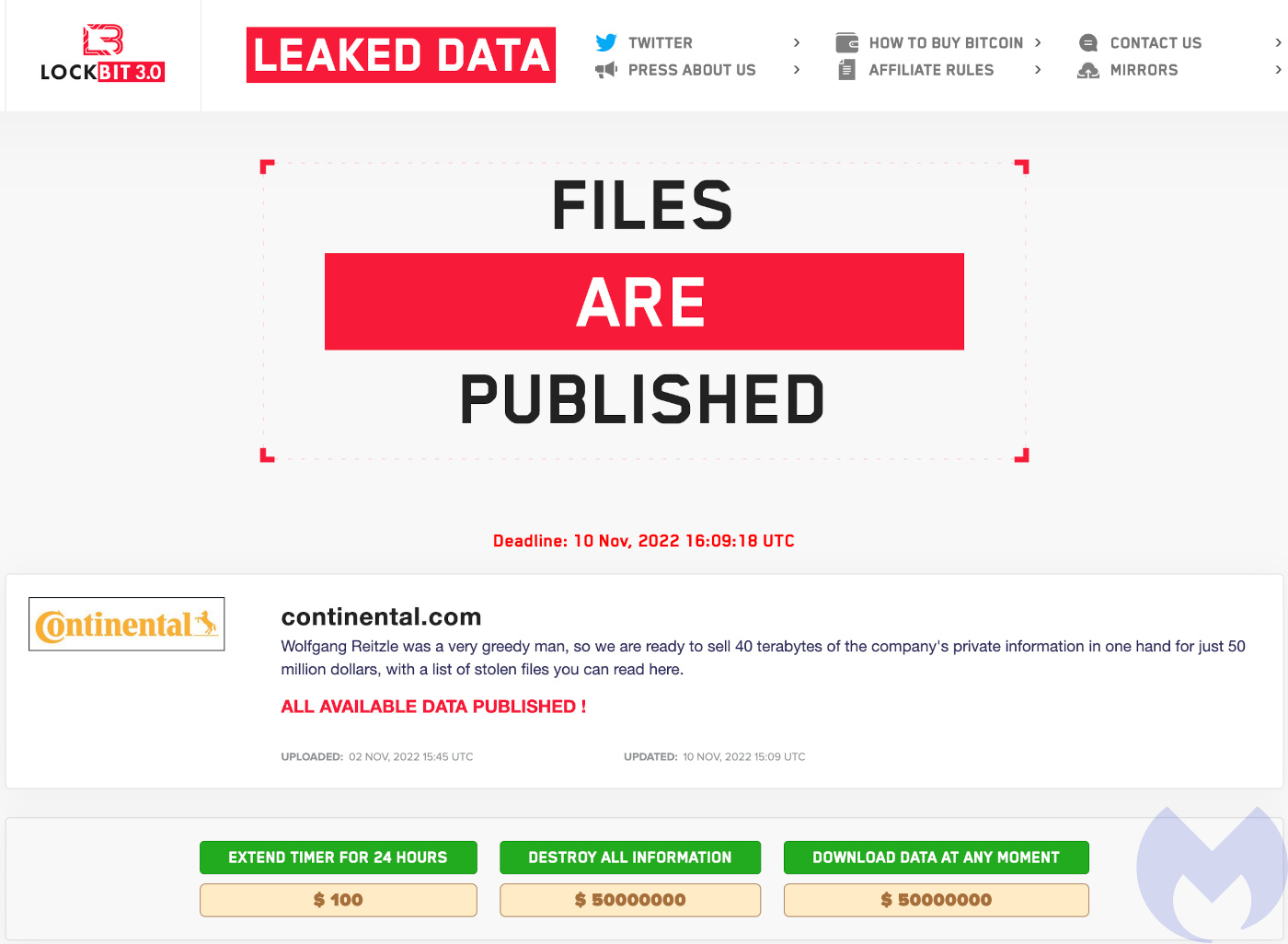
In the same month, German automotive parts powerhouse Continental was attacked by LockBit, which claimed to have stolen 40TB of files. The company broke off negotiations in late October, and the ransomware gang offered the data for sale or destruction for $50 million, the biggest known ransom of 2022, and the largest this author had seen until LockBIt’s equally outlandish request for $80 million from Royal Mail in early 2023.
A ransomware attack on German newspaper Heilbronner Stimme in October 2022 disrupted its printing systems, forcing the publication of a six-page emergency edition. The attack affected the entire Stimme Mediengruppe, including companies Pressedruck, Echo, and RegioMail, with Echo’s website and e-paper accessibility also compromised. Editor-in-chief Uwe Ralf Heer reported that a well-known cybercriminal group encrypted its systems and left ransom demands, but did not specify further.
In November 2022, the Vice Society ransomware gang claimed responsibility for a cyberattack on the University of Duisburg-Essen (UDE). The attackers leaked files including backup archives, financial documents, research papers, and student spreadsheets. On January 9, 2023, the university announced that due to extensive and complex damage caused by the attack, its entire IT infrastructure would need to be reconstructed.
Germany is a prime target
In the 12 months from April 2022 to March 2023, Germany was a globally significant target for ransomware, ranking as the fourth most attacked country by known attacks. It was the most attacked country in the EU, and the most attacked country where English isn’t the principle language.
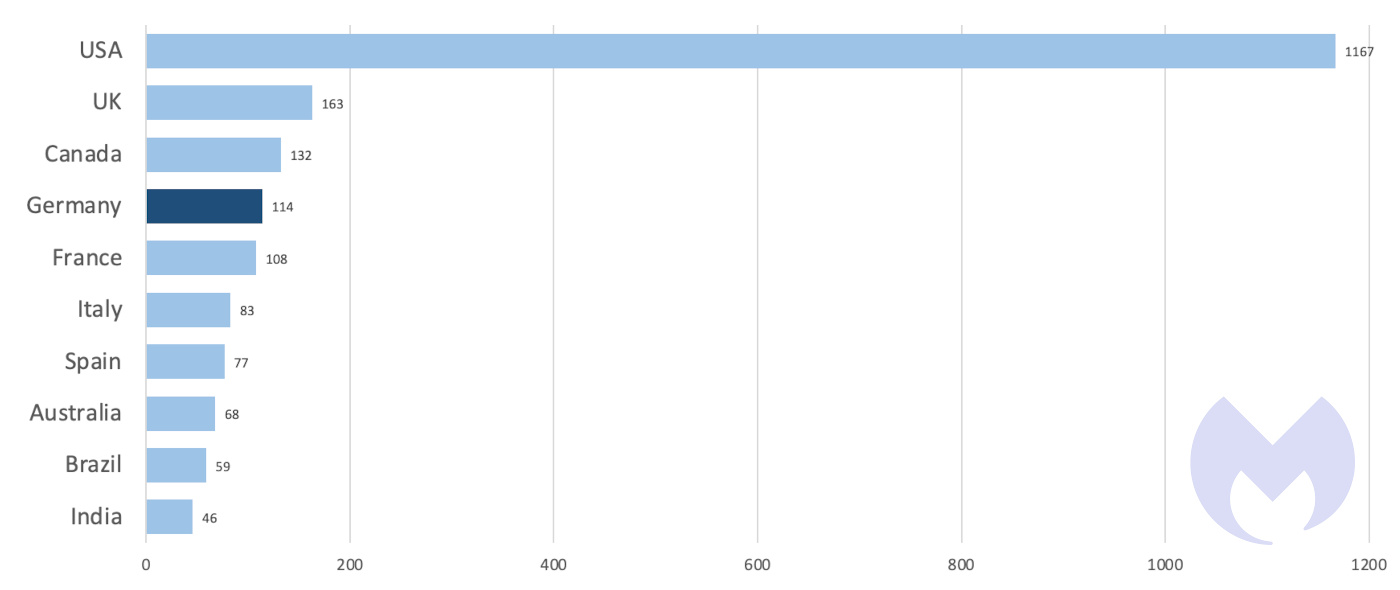
Given the disparity between the USA and the rest of the world in terms of number of attacks, it would be easy to conclude that ransomware is, first-and-foremost, a USA problem. It is not. The size and nature of the US economy means that it has many more targets for ransomware gangs than other countries in the top ten.
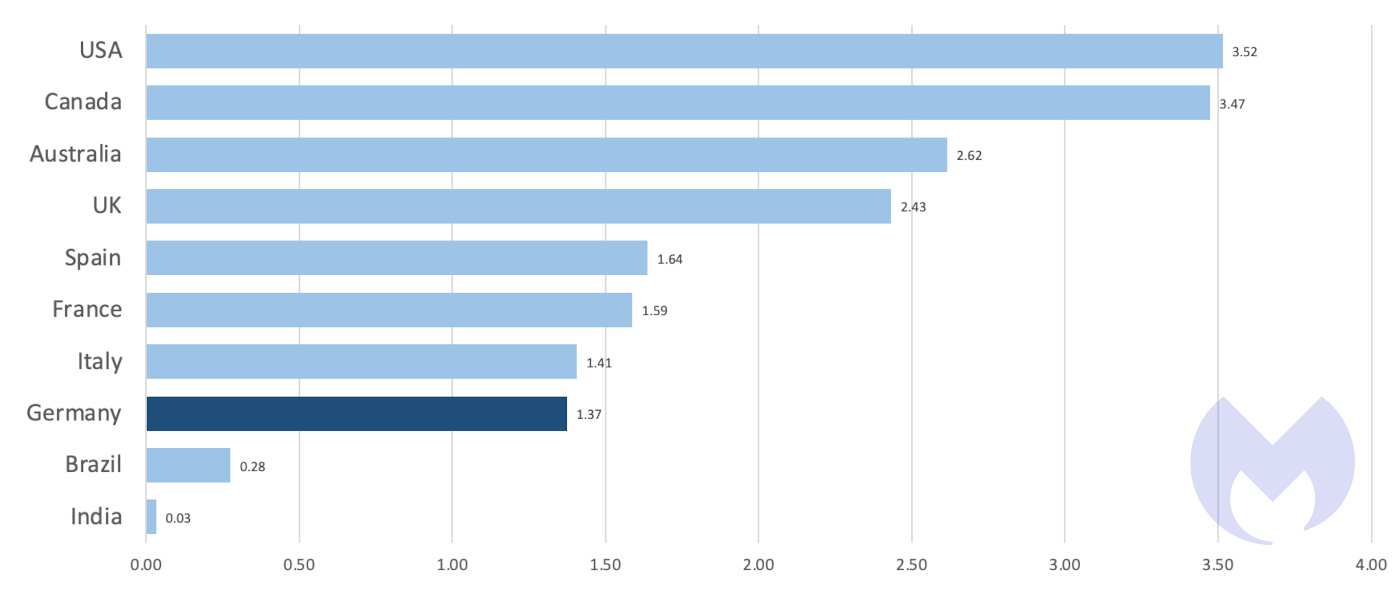
We can account for the difference in the size of countries’ economies by dividing the number of known ransomware attacks by a country’s nominal GDP, which gives us an approximate rate of attacks per $1T of economic output. On that basis, the difference between the countries in the top ten is far smaller than the total number of known attacks would suggest. The top ten most attacked countries all suffered between 15 and 66 known attacks per $1T of economic output.
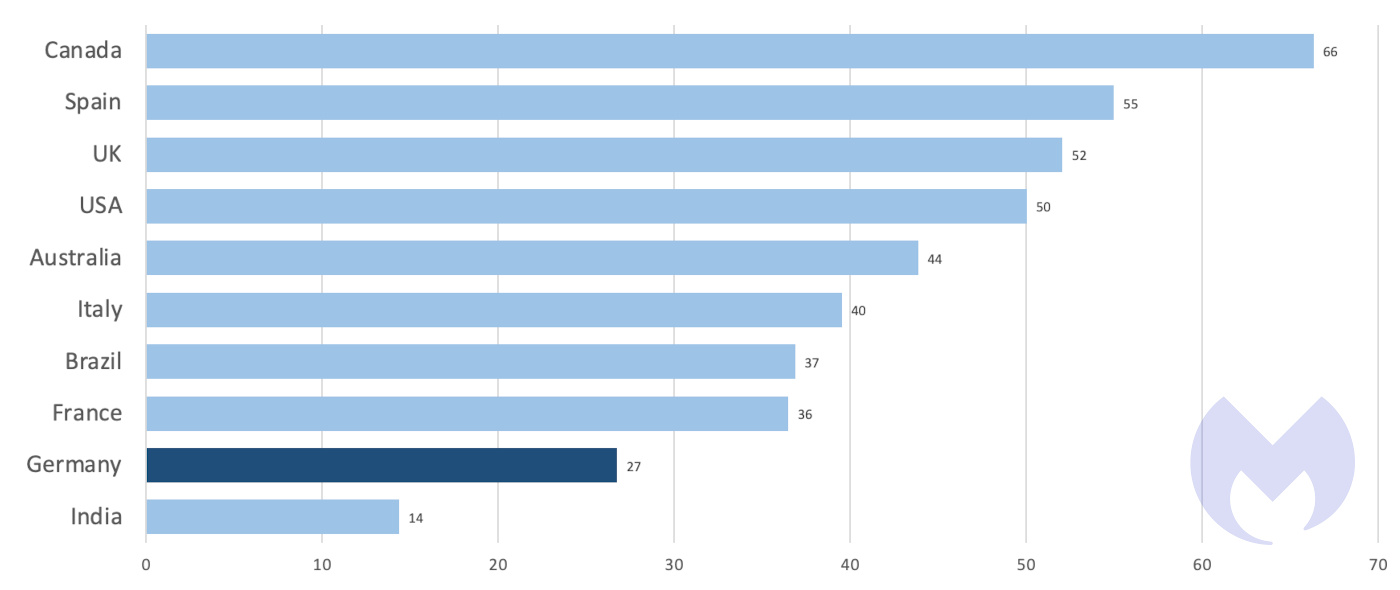
The size of the countries in the top ten also vary enormously, and we can try to account for that by dividing known attacks by the size of each country’s population. On that measure, again, the differences between countries are much smaller than a simple count of known attacks suggests.
On a known attacks per capita basis, Germany sits in a cluster of four advanced European economies with nearly identical rates of attack. In all the variations of our top ten, English-speaking countries occupy at least three of the top five positions, and English-speaking countries with smaller populations and economies, like Canada and Australia, seem to suffer disproportionately.
The situation in Germany is far from good, it just isn’t quite as bad as in the very worst countries. By any measure, Germany is one of the most attacked countries in the world, and its organisations are prime targets for ransomware gangs.
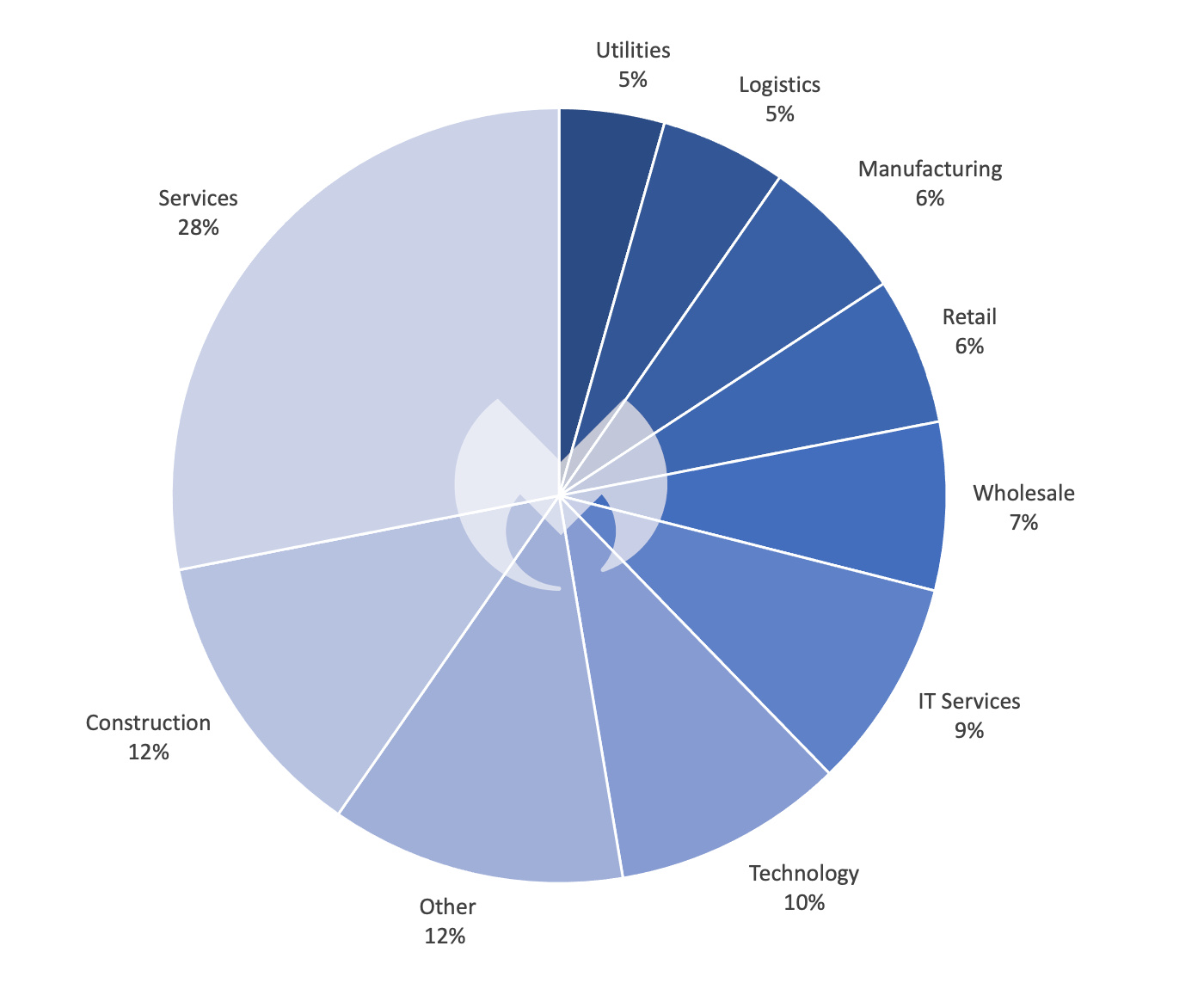
As in most countries, the German services sector is the most hard hit, accounting for 28% of attacks in the last 12 months, just slightly above the global average of 25%. In most respects, German industry sectors are attacked in roughly the proportions as they are in the UK and France, with some notable exceptions. There were no known attacks on German healthcare in the last 12 months (which, again, does not include unknown attacks), the country suffered fewer attacks on its legal services than either the UK or France, and it does not seem to have suffered the same problems France has had protecting its government sector, or the UK its education sector.
Where Germany suffers more than its neighbours is construction. Its 12% share of known attacks is double the global average, and notably higher than the USA (7%), UK (7%), and France (5%).
Black Basta’s hunting ground
In the UK, no individual ransomware was used in more than two known attacks on construction. In France one gang, LockBit, recorded three. In Germany, two different gangs recorded five known attacks against construction, accounting for a little over two thirds of the total. One of those gangs was LockBit, which is unsurprising given its position as by far the most used ransomware globally. The other was Black Basta, which recorded more attacks against German construction targets in 12 months than it did in the whole of France in the same period.
It seems Black Basta has an appetite for German targets. In the last 12 months it was the second most used ransomware in Germany, with 27 known attacks. In the same period it was busy in the UK with 10 attacks—but overshadowed by LockBit, Vice Society and others—it recorded just three attacks in France, where LockBit absolutely dominated.
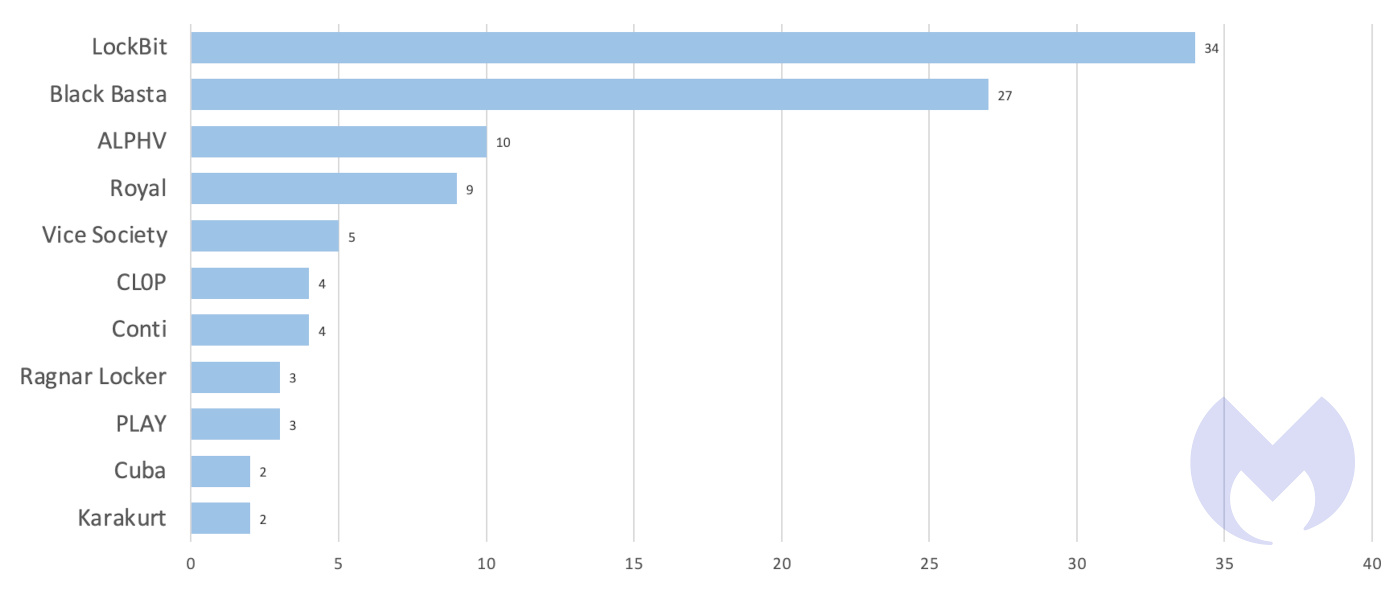
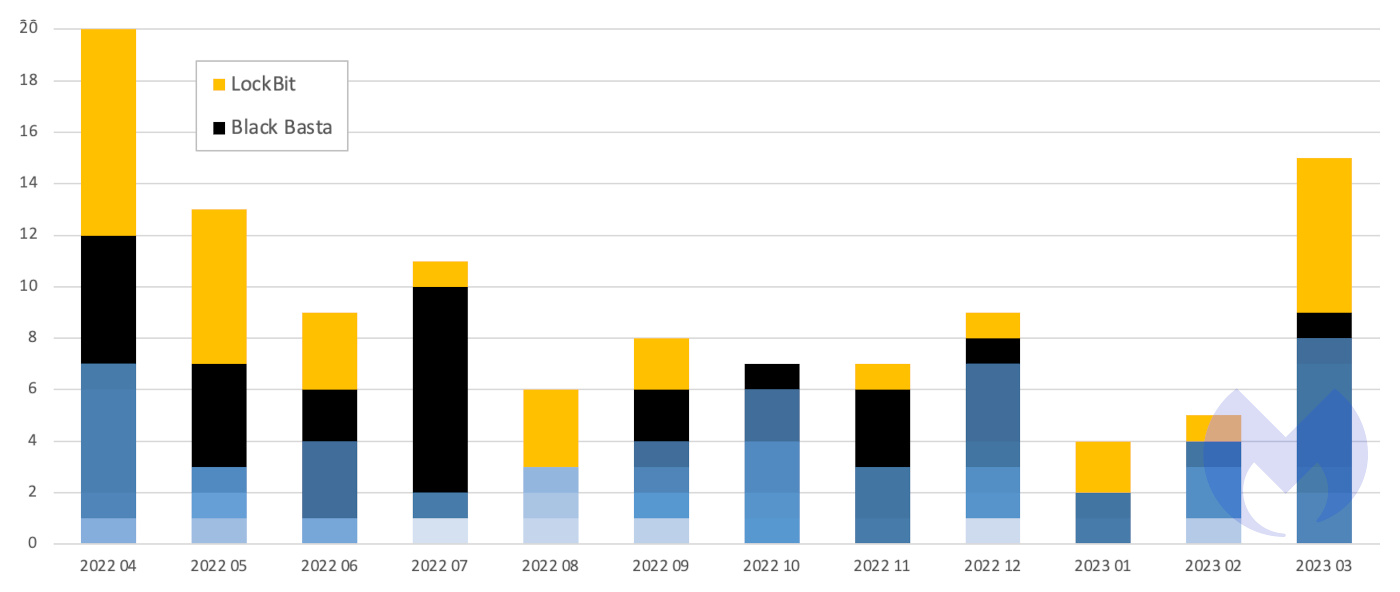
In the last year, Black Basta and LockBit were the only ransomware that registered more than four known attacks in a month, with both going as high as eight. Between them, the two groups accounted for 54% of known attacks in Germany and largely determined whether the country would have a bad month at the hands of ransomware gangs or a terrible one.
Black Basta does not reinvent the wheel in the way it operates. Similar to other ransomware groups, attacks frequently begin with initial access gained through phishing attacks. A typical attack might start with an email containing a malicious document in a zip file. Upon extraction, the document installs the Qakbot banking trojan to create backdoor access and deploy SystemBC, which sets up an encrypted connection to a command and control server. From there, CobaltStrike is installed for network reconnaissance and to distribute additional tools.
As is the overarching trend for ransomware groups these days, Black Basta’s primary goal is to steal data so that it can hold the threat of leaked data over its victims. The data is generally stolen using Rclone, which filters and copies specific files to a cloud service. After the data is exfiltratrated, the ransomware encrypts files with the “.basta” extension, erases volume shadow copies, and presents a ransom note named readme.txt on affected devices. Attackers using Black Basta may be active on a victim’s network for two to three days before running their ransomware.
Conclusions
In the last 12 months, Germany was a globally significant hunting ground for ransomware gangs, and the country with the fourth highest total of known attacks. Across the various industry sectors, construction was over represented, suffering a higher proportion of known attacks than the construction sectors in the USA, France, and the UK. Much like the education sector in the UK and the government sector in France, it should be alarming that, with an entire world of targets to choose from, it has attracted a disproportionate amount of attention.
In particular, the German construction sector suffered at the hands of LockBit and Black Basta, which displayed a liking for German targets of all kinds and was the second most used ransomware. Black Basta recorded considerably more attacks in Germany in the last year than in either the UK or France. In fact, the only country in the world to suffer more Black Basta attacks in the last twelve months than Germany was the USA.
How to avoid ransomware
- Block common forms of entry. Create a plan for patching vulnerabilities in internet-facing systems quickly; disable or harden remote access like RDP and VPNs; use endpoint security software that can detect exploits and malware used to deliver ransomware.
- Detect intrusions. Make it harder for intruders to operate inside your organization by segmenting networks and assigning access rights prudently. Use EDR or MDR to detect unusual activity before an attack occurs.
- Stop malicious encryption. Deploy Endpoint Detection and Response software like Malwarebytes EDR that uses multiple different detection techniques to identify ransomware, and ransomware rollback to restore damaged system files.
- Create offsite, offline backups. Keep backups offsite and offline, beyond the reach of attackers. Test them regularly to make sure you can restore essential business functions swiftly.
- Don’t get attacked twice. Once you’ve isolated the outbreak and stopped the first attack, you must remove every trace of the attackers, their malware, their tools, and their methods of entry, to avoid being attacked again.
Malwarebytes removes all remnants of ransomware and prevents you from getting reinfected. Want to learn more about how we can help protect your business? Get a free trial below.










