
What is a phishing email? How to spot an email scam
A phishing email is a fraudulent message crafted to trick recipients into revealing sensitive information like passwords or credit card numbers. These emails often imitate legitimate sources, like banks or popular websites, to appear credible. They aim to exploit a person’s trust in these institutions, persuading them to provide personal information, clicking on malicious links, or download attachments containing malware.
Key indicators of phishing emails include generic greetings, spelling and grammar mistakes (although not always), and urgent or threatening language that pressures the recipient to act quickly.
Suspicious links or attachments and sender email addresses that don’t match the legitimate organization they claim to represent are also telltale signs. Additionally, requests for sensitive information, which legitimate organizations typically won’t ask for via email, are a red flag.
Phishing email examples: what not to fall for
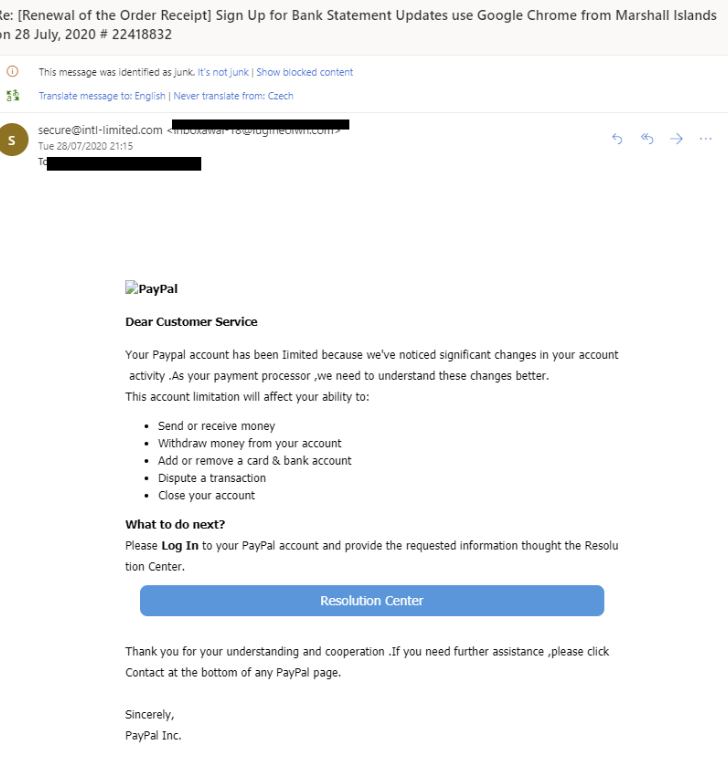
PayPal scams
This scam involves emails that appear to come from PayPal, often with convincing logos and formatting. The emails usually claim there’s an issue with the recipient’s account and asks them to click a link to verify or update their account information. The link leads to a fake PayPal website designed to look authentic, where victims unknowingly enter their login credentials, which are then stolen by the scammers. It may look like the following example, for other examples, visit this post.
Re: [Important] – Your account was temporary limited. Your account has been limited until we hear from you. While your account is limited, some options in your account won’t be available.
IRS / tax refund scams
In this phishing attack, individuals receive emails that seemingly come from the IRS. The emails often create a sense of urgency, claiming that there’s an issue with the recipient’s taxes or tax return. We wrote about IRS scams delivering the Emotet malware recently but it is just one example. The common theme for the IRS phishing scam emails is that these emails typically ask for personal and financial information, under the guise of resolving the issue. However, the IRS does not initiate contact with taxpayers via email to request personal or financial information.
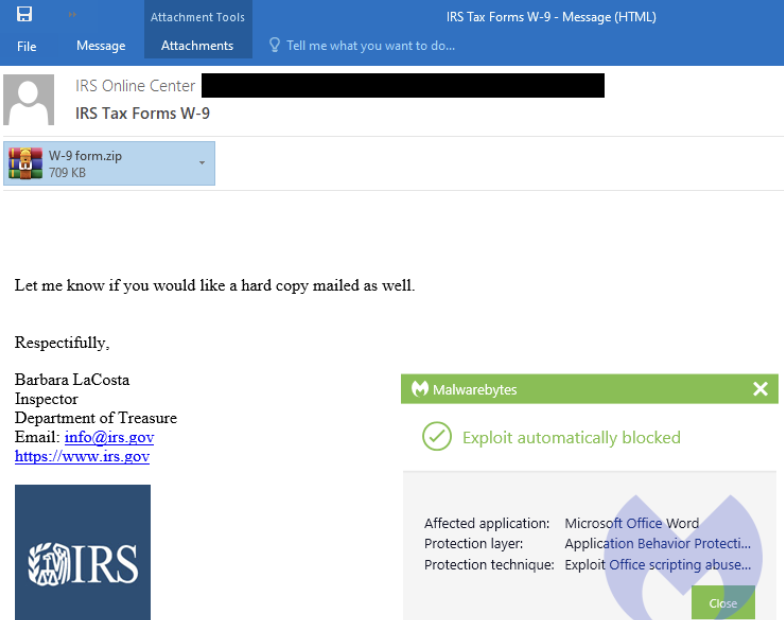
IRS Online Center – IRS Tax Forms W-9: Let me know if you would like a hard copy mailed as well. Respectifully, [SIC] Barbara LaCosta, Inspector, Department of Treasure
Google Docs scams
This scam involves emails that invite recipients to view a document on Google Docs. The email might appear to come from someone the person knows, which is part of the deception. Clicking the link in the email does not lead to a real Google Docs page but rather to a malicious website which may be designed to steal Google account credentials or install malware on the victim’s computer. We wrote about Google doc infostealer attack. The email would typically look like someone is trying to collaborate with you, but if you didn’t expect such an email, the best advice is to avoid clicking on it.

Tech Support scams
These phishing emails may try to get you click on a pop-up window that looks like an error message, example from FTC.gov, such as this one:

Threats Detected: Click or call immediately as suspicious activity has been detected.
Social media scams
Social media is a never ending source for scammers to phish users and get their personal data. One in four people who reported losing money to fraud since 2021 said it started on social media. Reported losses to scams on social media during the same period hit a staggering $2.7 billion, far higher than any other method of contact.
Hackers can easily clone real users profiles or hack into your profile, pretend to be you, and scam your contacts. Scammers can pretend to send an official email from the platform urging you to login to activate a feature or to reset your profile. On LinkedIn, users often report receiving suspicious emails from potential employers:
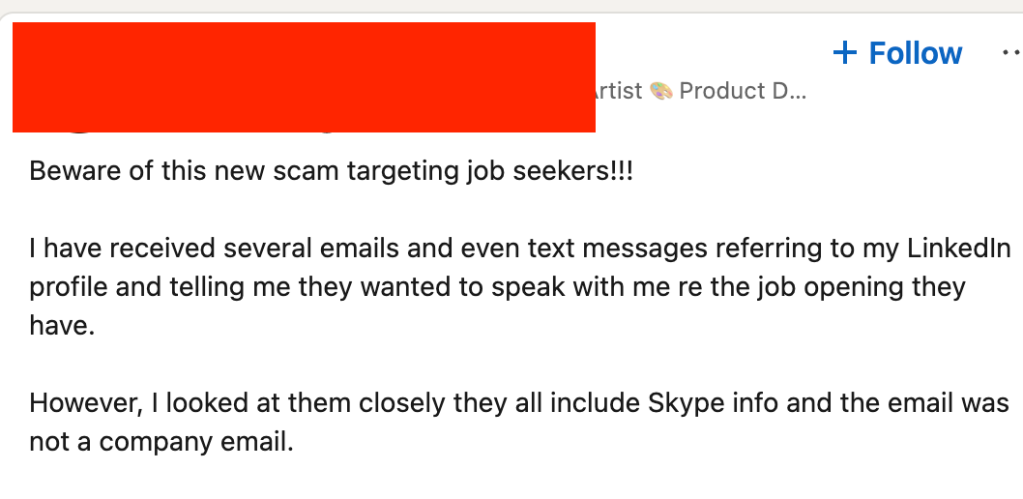
These are extremely tricky to identify, so keep an eye on any red flags such as typos, unusual requests and contact information, as well as urgent requests to click on attachments and / or links.
Bank phishing scams
These messages look like official notes from your financial institutions. However, you can easily spot a scam if they site nonexistent transactions or ask for your personal information. Do not click on these links to fill out these fraudulent forms. When in doubt, contact your bank to confirm the issue described in the email. We described bank scams more in-depth here.

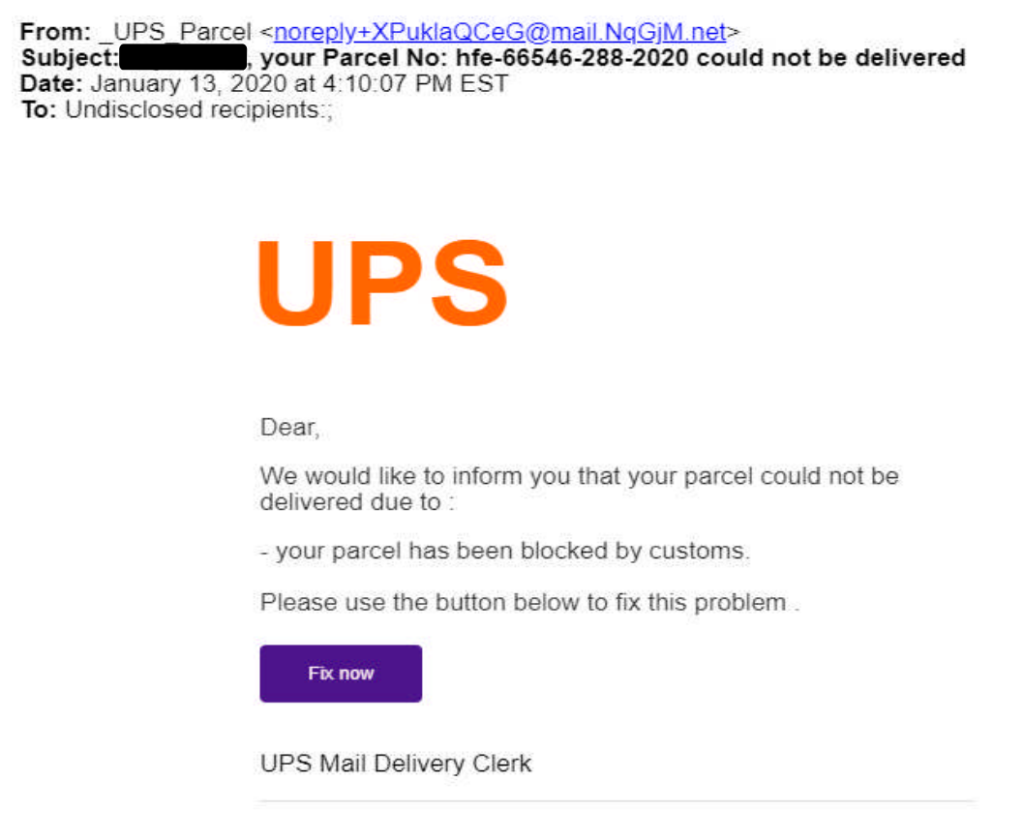
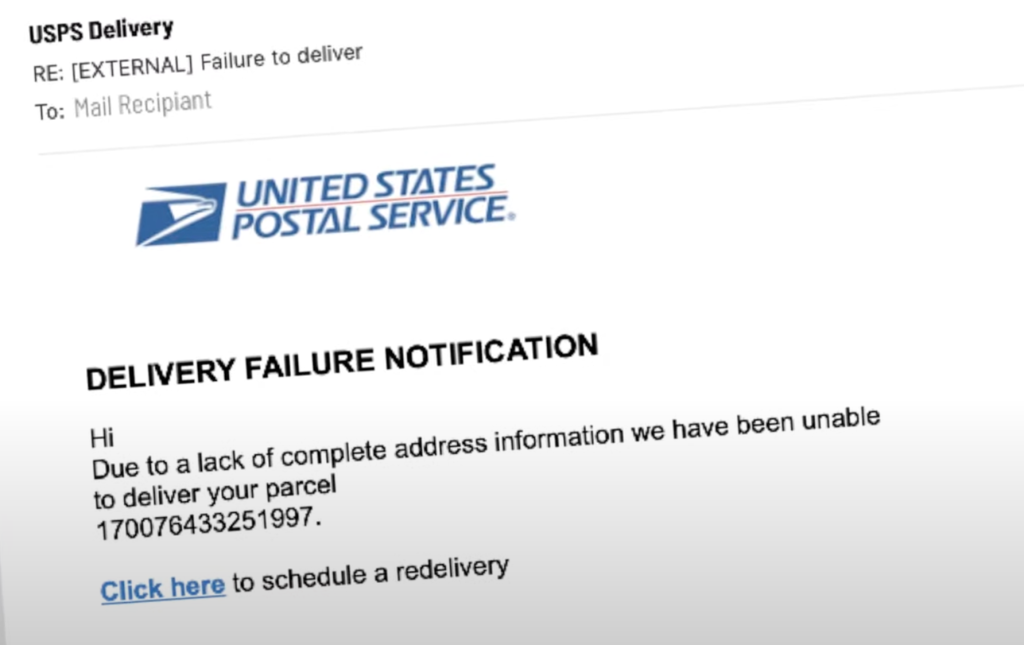
USPS or UPS phishing emails – i.e. “package couldn’t be delivered“
These emails look as though they came from the mail delivery service, such as USPS or UPS. They’re asking you to submit a personal information as the “package couldn’t be delivered.” Resist clicking on any links and login into the fraudulent sites to submit your personal information. Look out for typos and other red flags. Check out some of these phishing email examples from UPS (source: https://www.ups.com/assets/resources/webcontent/en_US/fraud_email_examples.pdf):
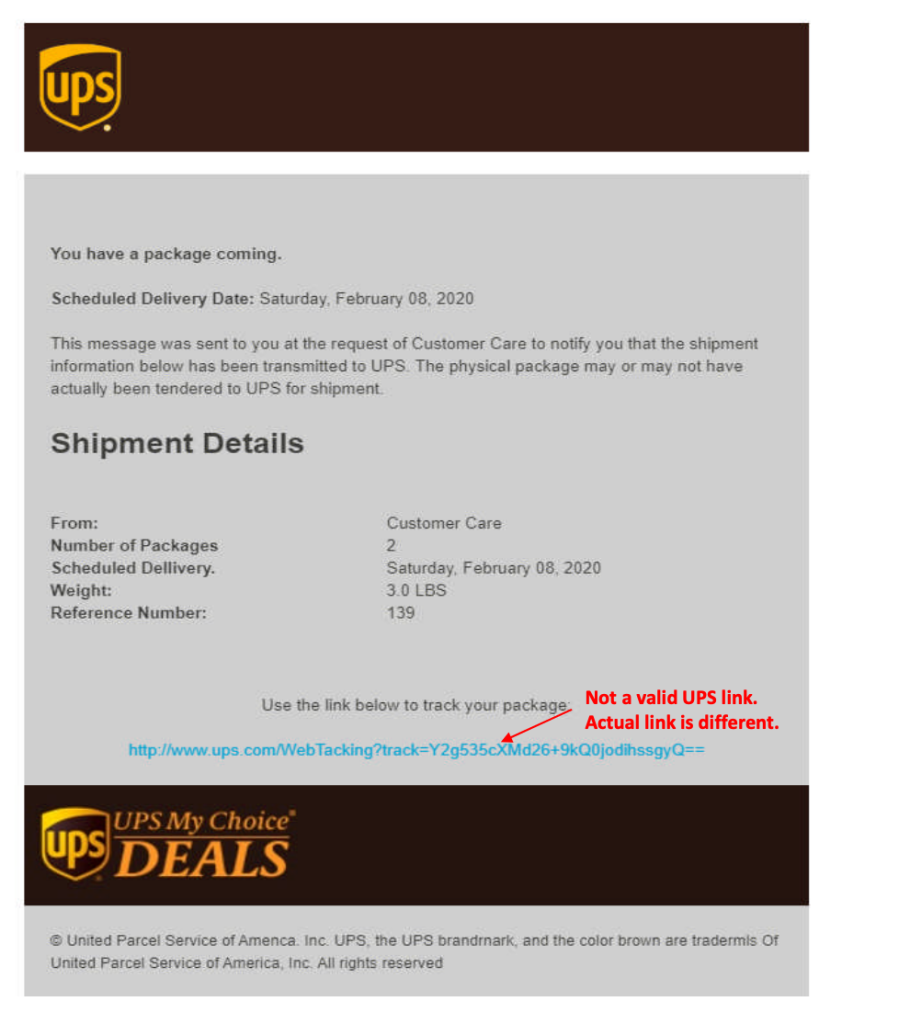
USPS shared some videos on how to spot a phishing USPS email here: https://www.uspis.gov/news/scam-article/fake-usps-emails
Common phishing emails themes
Phishing emails, designed to trick recipients into divulging sensitive information, often share common themes:
- Urgency: Many phishing emails create a sense of urgency, pressing you to act quickly. This might be a claim that your account will be closed, a threat of legal action, or a limited-time offer.
- Requests for personal information: These emails frequently ask for personal details like passwords, social security numbers, bank account information, or credit card numbers.
- Suspicious links or attachments: Phishing emails often contain links or attachments that the sender urges you to click on or open. These can lead to malicious websites or download malware onto your device.
- Spoofed sender information: Phishing emails might appear to be from legitimate sources, such as banks, government agencies, or well-known companies. They often mimic the look and feel of official communications.
- Grammatical and spelling errors: While not always the case, many phishing emails contain noticeable spelling and grammar mistakes.
- Threatening or alarming messages: Some phishing attempts use intimidation, like the threat of a fine or accusing you of illegal activities, to provoke a response.
- Offers that are too good to be true: They may promise unexpected windfalls, like winning a lottery or receiving an inheritance from a distant relative.
- Unsolicited requests: Phishing emails often come unbidden and may pertain to a service or a product you never used or an account you never opened.
Recognizing these themes can help you identify and avoid falling victim to phishing scams.
Why are phishing emails dangerous?
The dangers of phishing emails are significant. They can lead to identity theft, financial loss, and malware infections. Victims may face unauthorized transactions, loss of control over personal accounts, and long-term damage to their credit score. The personal impact of these threats includes stress, loss of privacy, and potential legal issues if one’s identity is used for illegal activities.
What happens if you open a phishing email?
Opening a phishing email itself is generally not enough to compromise your computer with viruses or malware. These malicious elements are usually triggered when you download an attachment or click on a link within the email. However, opening the email can alert the sender that your email address is active, potentially leading to more phishing attempts. It’s crucial to remain vigilant and avoid interacting with any suspicious content within such emails.
Clicked on a phishing link? Here’s what to do
Stay Calm: Don’t panic, but take immediate action.
- Disconnect: Disconnect your device from the internet to prevent further damage or data theft
- Scan for viruses and malware: Run a free virus scan here.
- Change all your account passwords: Email, social media, banking apps – any logins you can think about. If you need tips about a strong password – check out our password generator.
- Monitor your dark web exposure: here’s a great tool – digital footprint scan.
What happens if you respond a phishing email?
Responding to phishing emails is risky for several clear reasons. Even if you know it’s a fake email, replying can lead to more trouble. Most phishing attacks are run automatically, and when you respond, it puts you on the scammer’s radar. Remember, these cybercriminals are often involved in illegal activities and can be harmful.
Firstly, if you reply to a phishing email, you accidentally give the scammer your personal or your company’s email signature. This signature usually includes phone numbers and other details, which the scammer can use to make more convincing fake emails to trick you and others.
Secondly, when you reply, it tells the scammer that your email is in use. This makes you a bigger target for future scams. Your email address might even be sold to other cybercriminals.
Lastly, your email’s technical details can give away your location. This means scammers can figure out where you are, which adds to the risk.
Report a phishing email
Reporting phishing attempts is a critical step in protecting yourself and others from online scams. The Federal Trade Commission, a US government agency responsible for consumer protection, offers a platform for individuals to report phishing. This helps in tracking and mitigating such scams.
To report a phishing incident:
- If you’ve received a phishing email, you can forward it to the Anti-Phishing Working Group at their email address, reportphishing@apwg.org.
- In the case of phishing via text message, forward the message to the number 7726, which corresponds to ‘SPAM’ on most phone keypads.
- Lastly, you can also report the phishing attempt directly to the FTC. This can be done through their website, ReportFraud.ftc.gov.
Each report contributes to the fight against these fraudulent activities, helping the FTC and other organizations to track and stop scammers.
Are there legal consequences for the senders of phishing mails?
The senders of phishing emails face legal consequences under various consumer protection laws. In many countries phishing is considered a criminal offense, and perpetrators can be prosecuted for fraud, identity theft, and cybercrimes. The exact penalties vary by jurisdiction but can include substantial fines and imprisonment.