The Cisco Product Security Incident Response Team (PSIRT) has posted a blog about Akira ransomware targeting VPNs without Multi-Factor Authentication (MFA).
The Cisco team states that it is aware of reports of the Akira ransomware group going specifically after Cisco VPNs that are not configured for MFA. And they have observed instances where cybercriminals appear to be targeting organizations that do not configure MFA for their VPN users.
One of the reports the team may be aware of was tweeted weeks ago by security researcher and incident responder Aura:
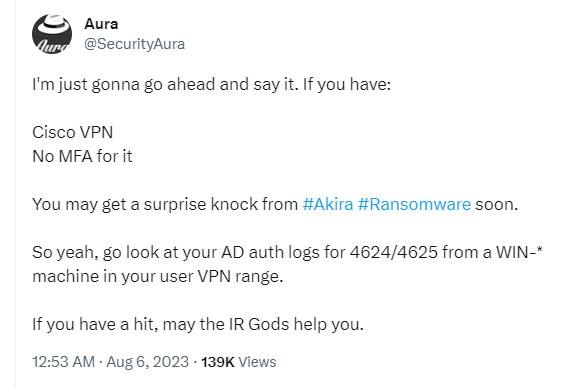
“I’m just gonna go ahead and say it. If you have:
Cisco VPN
No MFA for it
You may get a surprise knock from #Akira #Ransomware soon.”
Cisco VPN solutions are widely used to provide secure, encrypted data transmission between users and corporate networks, often used by remote employees. Gaining access could allow attackers to extract credentials through LSASS (Local Security Authority Subsystem Service) dumps to facilitate further movement within the network and elevate privileges if needed.
What the researchers haven’t been able to determine is how the ransomware operators gained access to Cisco VPN’s account login credentials in the first place, also hindered by the fact that Cisco ASA (Adaptive Security Appliance) doesn’t feature a logging function for successful logins. Only login attempts with invalid username/password combinations can be found in the logs if logging is configured in the affected Cisco’s ASAs.
It is possible that the criminals acquired valid credentials by purchasing them on the dark web, that they are using a zero-day exploit, or that they are using brute-force or credential stuffing attacks. Credential stuffing is a popular tactic of attempting to access online accounts using username-password combinations acquired from already-breached data dumps. In a brute force attack, attackers typically try a lot of common passwords, or a few common passwords across many usernames which is called password spraying. Password spraying focuses on trying a few passwords across many accounts, often to avoid account lockouts and detection.
Cisco says it has seen evidence of brute force and password spraying attempts. Other researchers say they have found evidence of Akira using Cisco VPN gateways in leaked data posted on the group’s extortion page and seem to be leaning towards the vulnerability scenario.
Whichever way was used to gain access, it has become even more apparent that adding MFA is an important factor in fighting off these attacks.
How to avoid ransomware
- Block common forms of entry. Create a plan for patching vulnerabilities in internet-facing systems quickly; and disable or harden remote access like RDP and VPNs.
- Prevent intrusions. Stop threats early before they can even infiltrate or infect your endpoints. Use endpoint security software that can prevent exploits and malware used to deliver ransomware.
- Detect intrusions. Make it harder for intruders to operate inside your organization by segmenting networks and assigning access rights prudently. Use EDR or MDR to detect unusual activity before an attack occurs.
- Stop malicious encryption. Deploy Endpoint Detection and Response software like Malwarebytes EDR that uses multiple different detection techniques to identify ransomware, and ransomware rollback to restore damaged system files.
- Create offsite, offline backups. Keep backups offsite and offline, beyond the reach of attackers. Test them regularly to make sure you can restore essential business functions swiftly.
- Don’t get attacked twice. Once you’ve isolated the outbreak and stopped the first attack, you must remove every trace of the attackers, their malware, their tools, and their methods of entry, to avoid being attacked again.
Malwarebytes EDR and MDR remove all remnants of ransomware and prevents you from getting reinfected. Want to learn more about how we can help protect your business? Get a free trial below.











