Short bio
Angler was one of the leading exploit kits used by cybercriminals to distribute malware ranging from ransomware and banking Trojans to ad fraud. Like most other exploit kits, it focused on web-based vulnerabilities in the browsers and their plugins. Angler was one of the few exploit kits during its time that offered fileless infections, where malware never touches the disk and only resides in memory to avoid detection. Angler has been inactive since June 2016.
History
When Blackhole, the “king of exploit kits,” disappeared in late 2013, it left a void in the criminal undergrounds. Not longer after, a newcomer called Angler started to generate some buzz. It didn’t take long to become the de facto exploit kit, thanks to its overall effectiveness and ability to add zero-day vulnerabilities into its arsenal.
Angler used vulnerabilities in Internet Explorer, Silverlight, Flash Player, Adobe Reader, Java, Internet Explorer and Flash.
It’s noteworthy that Angler also used the ActiveX XLMDOM vulnerability (CVE-2013-7331) to fingerprint systems. This technique is used to detect virtual machines, sandboxes, and security tools that indicate the presence of a security researcher and not a genuine end user.
Angler also utilized a Diffie-Hellman encryption key exchange to make each attack unique to a particular victim and to thwart attempts at replaying packet captures.
For the reasons described above, Angler was one of the most technically complex exploit kits. In addition, the developers behind Angler have shown great skill when it came to integrating the latest patched vulnerabilities, in a matter of days, sometimes hours, after they were fixed by the respective software vendors.
Finally, Angler was very adept at introducing brand-new exploits for unpatched vulnerabilities, the so-called zero-days. This represented a real menace to consumers and businesses because it shows that even patching is not enough these days. Patching is already problematic, so the emergence of zero-days puts things into perspective and requires a different strategy to combat them.
Common infection method
Traffic to the Angler exploit kit came from malvertising and compromised web sites. Traffic redirection is an essential part of the entire exploit kit ecosystem, and there are close ties between operators of these exploit kits and people (traffers) in charge to driving leads to them.
The infection happened via a process known as drive-by download, where a user browsing a legitimate site (or compromised one) is redirected to the exploit kit page without any sort of action on their part. Sometimes the redirection happens in the background via an iframe, for example, making the infection process almost invisible from the end user.
If the user’s machine was vulnerable (or even if it wasn’t, in the case of a zero-day), a piece of malware is dropped to disk or injected directly into memory. Exploit kits can be seen as a delivery method, a vehicle for any type of malware infection.
Associated families
There have been similarities between Angler EK and Hanjuan EK, another more elusive exploit kit. For example, the use of similar encryption keys and the fileless payloads.
Remediation
One cannot remove the exploit kit itself, since it’s really just a tool to infect a PC at a particular time. For this reason, remediation depends on the actual malware that was dropped, which in many cases is actually a combination of various pieces of malware.
Aftermath
The signs of an infection via an exploit kit are not always obvious if the piece of malware is meant to be stealthy (i.e. banking Trojan). In other cases, the user will quickly realize that something has gone wrong when their desktop is hijacked with a message demanding a ransom to decrypt their personal files.
Avoidance
There is no real way of avoiding exploit kits because they are brought upon via malvertising even on popular websites. Given this, we all have been exposed to exploit kits at one point or another, but whether we were infected or not depends on the type of exploit that was pushed, and if we were using any type of exploit mitigation software.
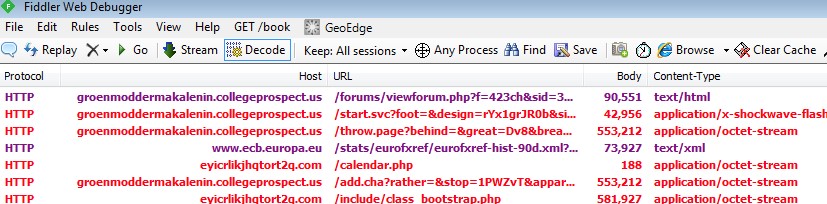
Screenshots