What is phishing?
Phishing is when tricksters pretend to be real companies to fool people into sharing private information like personal details, bank account info, and passwords. Once they get this info, they can steal the person’s identity or money.
How does phishing work?
Phishing can happen through emails, phone calls, or text messages. The tricksters send messages that look real and urgent, asking the person to take action. For instance, an email might look like it’s from a trustworthy bank, telling the person to update their account info to avoid problems. Because the message seems urgent and real, people might share sensitive info like passwords and credit card numbers, which the tricksters can then misuse.
Posing as a legitimate entity, the attacker lures victims to a counterfeit website where they are persuaded to enter confidential information. This well-crafted façade, coupled with a sense of urgency, enables the phishing scam to successfully harvest valuable personal data, leaving the unsuspecting victim vulnerable to identity theft and financial loss.
The sender: In a phishing attack, the sender imitates (or “spoofs”) someone trustworthy that the recipient would likely know. Depending on the type of phishing attack, it could be an individual, like a family member of the recipient, the CEO of the company they work for, or even someone famous who is supposedly giving something away. Often phishing messages mimic emails from large companies like PayPal, Amazon, or Microsoft, and banks or government offices.
The message: Under the guise of someone trusted, the attacker will ask the recipient to click a link, download an attachment, or to send money. When the victim opens the message, they find a scary message meant to overcome their better judgement by filling them with fear. The message may demand that the victim go to a website and take immediate action or risk some sort of consequence.
The destination: If users take the bait and click the link, they’re sent to an imitation of a legitimate website. From here, they’re asked to log in with their username and password credentials. If they are gullible enough to comply, the login credentials go to the attacker, who uses it to steal identities, pilfer bank accounts, and sell personal information on the black market. The destination URL in the phishing email often looks very similar to the legitimate URL, which can further deceive the victim.
How to recognize phishing?
Phishing attempts are fraudulent activities where scammers use email or text messages aiming to trick individuals into revealing sensitive information like passwords, bank account numbers, or Social Security numbers. Recognizing phishing can be achieved by being alert to certain red flags.
Typically, phishing messages may appear to come from reputable sources such as banks, credit card companies, or familiar online platforms. They often create a sense of urgency, suggesting suspicious activity or issues with your account, urging you to act swiftly.
Some common indicators of phishing include unexpected communications requesting personal or financial information, unfamiliar sender email addresses, generic greetings, spelling and grammar mistakes, and deceptive URLs. By being cautious and verifying any suspicious communications directly with the institutions involved before responding, individuals can better protect themselves against phishing attempts. Now we want to go into more detail about the signs of phishing and help you spot them.
Signs of phishing
Spotting phishing attempts can be a challenge, but with some vigilance, basic guidelines, and a dose of common sense, you can significantly reduce the risks. Look for irregularities or peculiarities in the email. Use the “smell test” to determine if something doesn’t sit right with you. Trust your instincts, but stay away from fear, as phishing scams often exploit fear to impair your judgment.
Here are additional signs of phishing attempts:
Sign 1: The email presents an offer that seems too good to be true.
It might claim you’ve hit the jackpot, won an extravagant prize, or other improbable rewards.
Sign 2: The sender is recognizable, but not someone you usually interact with.
Even if you recognize the sender’s name, exercise caution if it’s not someone you regularly communicate with, particularly if the email’s content is unrelated to your usual job tasks. Similarly, be wary if you’re cc’d on an email alongside unfamiliar individuals or colleagues from unrelated departments.
Sign 3: The message induces fear.
Be cautious if the email utilizes charged or alarming language to instill a sense of urgency, urging you to click and “act immediately” to prevent account termination. Remember, legitimate organizations won’t request personal information via email.
Sign 4: The message includes unexpected or odd attachments.
These attachments may harbor malware, ransomware or other online threats.
Sign 5: The message incorporates links that seem dubious.
Even if the above indicators don’t raise suspicion, never trust embedded hyperlinks blindly. Hover your cursor over the link to reveal the actual URL. Pay special attention to subtle misspellings in a seemingly familiar website URL, as it’s a red flag for deceit. It’s always safer to manually enter the URL into your browser instead of clicking on the embedded link.
Who is targeted by phishing?
Phishing is a threat to everyone, targeting various individuals and industries, from corporate executives to everyday social media users and online banking customers. The wide scope of phishing makes it crucial to exercise caution online and adopt preventive measures. Being vigilant and proactive can significantly reduce the risk of falling victim to phishing scams, ensuring a safer online experience for all.
How to protect yourself against phishing attacks
As stated previously, phishing is an equal opportunity threat, capable of showing up on desktops, laptops, tablets, and smartphones. Most Internet browsers have ways to check if a link is safe, but the first line of defense against phishing is your judgement. Train yourself to recognize the signs of phishing and try to practice safe computing whenever you check your email, read Facebook posts, or play your favorite online game.
Malwarebytes Labs shared some of the key practices to protect yourself against phishing attacks:
- Don’t open e-mails from senders you are not familiar with.
- Don’t ever click on a link inside of an e-mail unless you know exactly where it is going.
- If you are asked to provide sensitive information, check that the URL of the page starts with “HTTPS” instead of just “HTTP.” The “S” stands for “secure.” It’s not a guarantee that a site is legitimate, but most legitimate sites use HTTPS because it’s more secure. HTTP sites, even legitimate ones, are vulnerable to hackers.
- Enable Multi-Factor Authentication (MFA): Utilize MFA wherever possible to add an extra layer of security. Even if phishers obtain your password, they’ll need to bypass additional verification steps to access your account.
- Lookout for the digital certificate of a website.
- To layer that protection, if you get an e-mail from a source, you are unsure of, navigate to the provided link manually by entering the legitimate website address into your browser.
- Mouseover the link to see if it’s a legitimate link.
- If you suspect an e-mail isn’t legitimate, take a name or some text from the message and put it into a search engine to see if any known phishing attacks exist using the same methods.
We strongly recommend the use of trusted antivirus/anti-malware solutions like Malwarebytes Premium to enhance your digital security. Most modern cybersecurity tools, equipped with smart algorithms, can identify malicious links or attachments, providing a vigilant shield even against clever phishing attempts.
If a phishing tactic slips past your notice, our robust security software keeps your information securely in your control. We offer a complimentary trial of Malwarebytes, allowing you to experience its superior protection before making a purchase.
Different types of phishing attacks
Phishing attacks use deceptive methods to illegally gather sensitive information, and they come in various forms, each with its own unique features. These are specific ways phishing attackers aim to deceive their targets:
Spear Phishing
Spear phishing is a targeted form of phishing where attackers tailor messages to specific individuals or organizations, using collected data to make the deceit more convincing. It requires pre-attack reconnaissance to uncover names, job titles, email addresses, and the like.
The hackers scour the Internet to match up this information with other researched knowledge about the target’s colleagues, along with the names and professional relationships of key employees in their organizations. With this, the phisher crafts a believable email.
Example: Fraudsters may impersonate executives to trick employees into authorizing fraudulent payments.
Whale Phishing
Whale phishing targets high-profile individuals, such as executives, celebrities, or C-level businesspeople. It attempts to trick them into revealing personal information or professional details.
Understanding and identifying the diverse forms of phishing attacks is crucial to implementing effective protective measures, ensuring the security and integrity of personal and organizational assets.
Email Phishing
Commonly seen since email’s inception, phishing emails involve deceptive emails appearing to come from reputable sources (e.g., banks, online retailers) urging recipients to click on links or download attachments.
Examples:
- Business email compromise (BEC): A business email compromise (BEC) attack targets someone in the finance department of an organization, often the CFO, and attempts to deceive them into sending large sums of money. Attackers often use social engineering tactics to convince the recipient that sending the money is urgent and necessary.
- Clone phishing: In this attack, criminals make a copy—or clone—of previously delivered but legitimate emails that contain either a link or an attachment. Then, the phisher replaces the links or attached files with malicious substitutions disguised as the real thing. Unsuspecting users either click the link or open the attachment, which often allows their systems to be commandeered. Then the phisher can counterfeit the victim’s identity in order to masquerade as a trusted sender to other victims in the same organization.
- 419/Nigerian scams: A verbose phishing email from someone claiming to be a Nigerian prince is one of the Internet’s earliest and longest-running scams. This “prince” either offers you money, but says you need to send him a small amount first, to claim it, or he says he is in trouble, and needs funds to resolve it. The number “419” is associated with this scam. It refers to the section of the Nigerian Criminal Code dealing with fraud, the charges, and penalties for offenders.
Vishing (Voice Phishing)
Attackers impersonate authority figures (e.g., bank officials, law enforcement) over the phone to scare individuals into sharing sensitive information or transferring funds.
Smishing (SMS Phishing)
Similar to vishing, but conducted via SMS, smishing sends fraudulent messages urging recipients to click on malicious links or share personal details.
Catphishing
A deceptive tactic where attackers create fake online personas to lure individuals into romantic relationships for monetary exploitation or personal information access.
Examples of phishing attacks
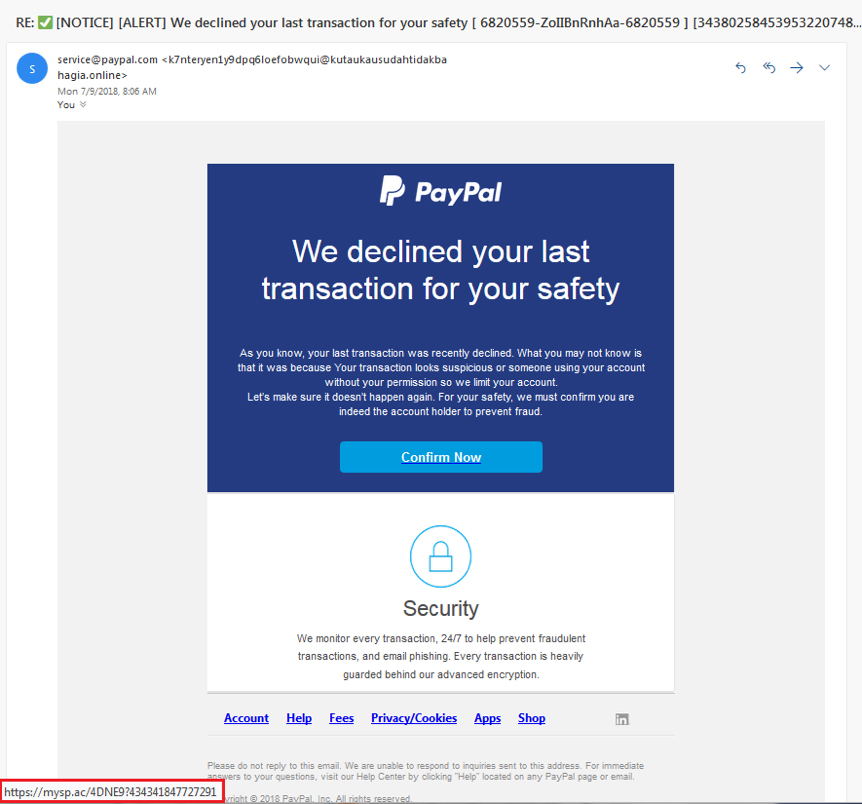
Here’s an example of a phishing attempt that spoofs a notice from PayPal, asking the recipient to click on the “Confirm Now” button. Mousing over the button reveals the true URL destination in the red rectangle.
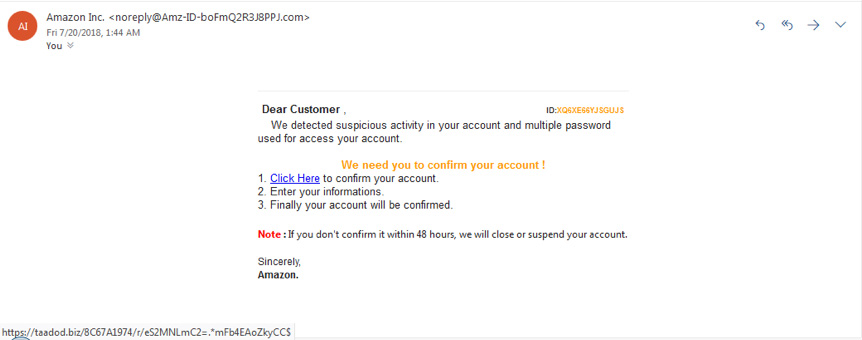
Here’s another phishing attack image, this time claiming to be from Amazon. Note the threat to close the account if there’s no response within 48 hours.
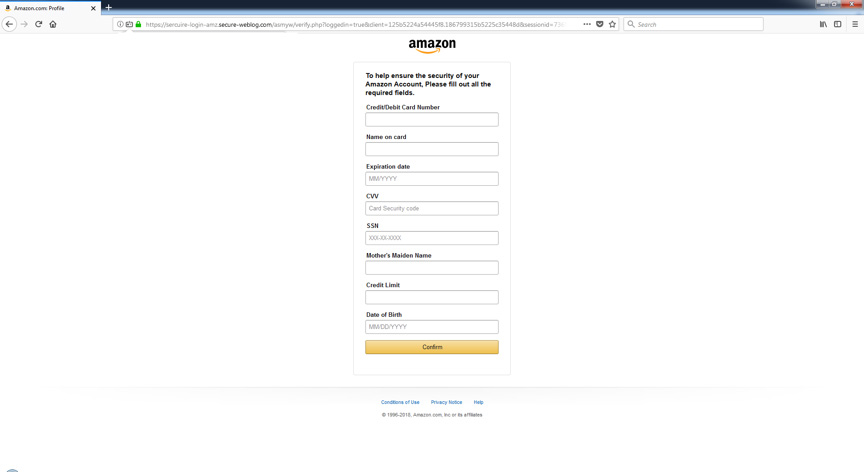
Clicking on the link leads you to this form, inviting you to give away what the phisher needs to plunder your valuables:
Why is phishing effective?
Phishing is notably effective due to its exploitation of human psychology rather than relying on advanced technical tactics. Often masquerading as urgent communications from authoritative figures, phishing scams prey on individuals’ trust and fear.
Adam Kujawa, formerly of Malwarebytes Labs, sums it up: “Phishing stands out as the simplest yet most potent cyber-attack, chiefly targeting the most susceptible yet powerful element: the human mind.” The lack of technical sophistication and the potential to evoke immediate reactions, highlight why phishing remains a widespread and serious online threat.
“Phishing is the simplest kind of cyberattack, and at the same time, the most dangerous and effective.”
Phishers are not trying to exploit a technical vulnerability in your device’s operation system—they’re using social engineering. From Windows and iPhones to Macs and Androids, no operating system is completely safe from phishing, no matter how strong its security is. In fact, attackers often resort to phishing because they can’t find any technical vulnerabilities.
Why waste time cracking through layers of security when you can trick someone into handing you the key? Often, the weakest link in a security system isn’t a glitch buried in computer code, it’s a human being who doesn’t double check where an email came from.
Now that we’ve explored what phishing is and how it works, let’s take a look at where it all started, going back to the 1970s with phone system hacking, also known as ‘phreaking’.
The history of phishing
The term “phishing” likens scam attempts to fishing, where bait is used to lure victims. It’s believed to have originated from the ’70s “phreaking” culture, which involved hacking phone systems. Before the term “phishi
ng” was coined, a similar technique was presented in a 1987 tech conference. The term’s first known use traces back to 1996, associated with hacker Khan C Smith, amid a scam on America Online (AOL) users, exploiting AOL’s popularity by impersonating AOL staff to collect user information.
Entering the 2000s, phishers shifted focus to online payment systems, banking, and social media platforms. They created convincing fake domains, especially spoofing eBay and PayPal, tricking users into sharing sensitive information. The first bank-targeted phishing attack was reported in 2003. By the mid-2000s, phishing had become a major cyber threat with sophisticated, organized campaigns, causing significant financial losses.
The damage escalated over the years, with notable incidents including a state-sponsored campaign in 2011, the massive Target data breach in 2013, and high-profile political phishing attempts in 2016. The trend continued into 2017, with a scam leading to over $100 million being misdirected from tech giants like Google and Facebook.